Global GoBruteforcer Botnet Campaign Threatens 50,000 Linux Servers
•January 8, 2026
0
Companies Mentioned
Why It Matters
The campaign highlights how automated credential‑spraying on exposed services can translate into direct financial loss, underscoring the urgent need for stronger authentication and exposure reduction across cloud and on‑premise environments.
Key Takeaways
- •Over 50,000 Linux servers vulnerable to GoBruteforcer attacks.
- •Botnet targets FTP, MySQL, PostgreSQL, phpMyAdmin services.
- •AI‑generated deployment scripts spread default credentials, fueling attacks.
- •Cryptocurrency projects hit, draining funds via TRON and BSC scanners.
- •2025 variant uses random IP generation, 95 threads per host.
Pulse Analysis
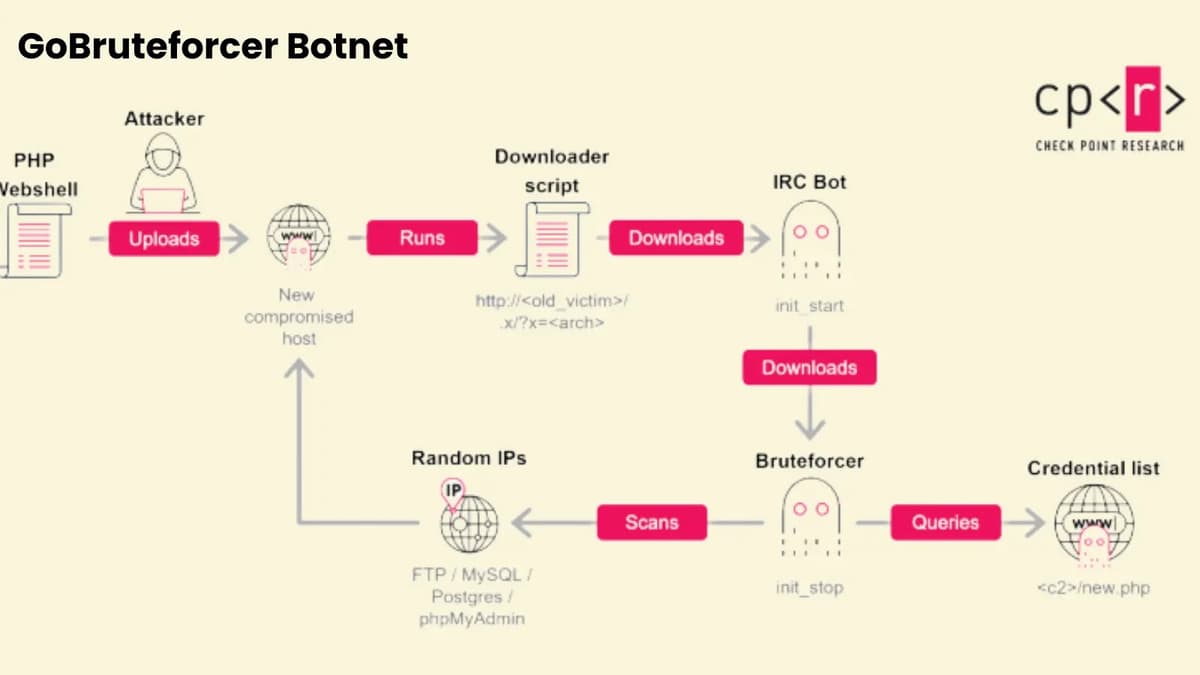
The resurgence of GoBruteforcer illustrates a broader shift in threat actors toward exploiting the sheer volume of publicly exposed services. Shodan data shows millions of FTP, MySQL and PostgreSQL instances remain reachable on default ports, providing a fertile hunting ground for automated credential‑spraying tools. Unlike opportunistic malware, GoBruteforcer’s modular architecture—combining web shells, downloaders and Go‑based IRC bots—enables rapid scaling across heterogeneous Linux environments, making it a potent vector for initial access.
A surprising catalyst for the current wave is the mass adoption of AI‑generated server deployment guides. Large‑language models frequently emit boilerplate configurations that embed generic usernames such as "appuser" or "myuser" with weak passwords. When organizations copy these snippets into production, they unintentionally create uniform attack surfaces that the botnet can exploit en masse. Legacy stacks like XAMPP further compound the problem by shipping with pre‑installed FTP services and default credentials, effectively acting as backdoors for malicious actors targeting high‑value sectors, notably cryptocurrency and blockchain projects.
Technical evolution in the mid‑2025 variant raises the stakes for defenders. The botnet now employs an infinite‑dice‑roll IP generation algorithm to bypass blacklist ranges, while obfuscated Go code masks malicious processes as legitimate services. With up to 95 concurrent brute‑force threads per 64‑bit host, the threat can exhaust authentication limits and evade rate‑limiting controls. Mitigation requires a layered approach: immediate audit of internet‑facing services, enforcement of MFA and complex passwords, decommissioning of default accounts, and network segmentation to isolate critical databases. Failure to act could see continued credential‑based compromises and direct financial theft, reinforcing the imperative for proactive credential hygiene across the enterprise.
Global GoBruteforcer Botnet Campaign Threatens 50,000 Linux Servers
0
Comments
Want to join the conversation?
Loading comments...