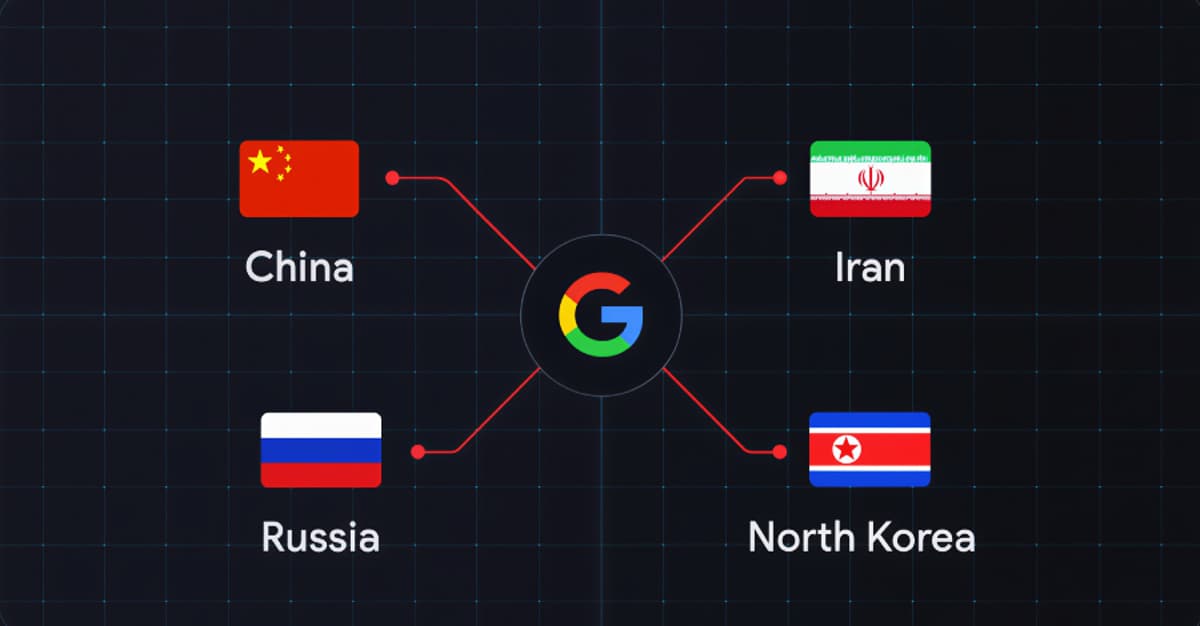
Google Links China, Iran, Russia, North Korea to Coordinated Defense Sector Cyber Operations
•February 13, 2026
0
Why It Matters
The findings reveal an escalating, multi‑vector espionage threat that could undermine critical defense technologies and supply‑chain resilience, prompting firms to accelerate cyber‑defense investments.
Key Takeaways
- •China, Iran, Russia, North Korea target defense sector simultaneously
- •Threats focus on drones, autonomous vehicles, and battlefield tech
- •Actors exploit hiring processes and edge devices for initial access
- •Supply‑chain breaches use malware via manufacturing and ORB networks
- •Google identifies over a dozen APT groups employing novel tools
Pulse Analysis
The defense industrial base is now a primary battlefield for state‑backed cyber actors, as Google’s Threat Intelligence Group reports a surge in coordinated intrusions from China, Iran, Russia and North Korea. Unlike traditional espionage that focused on static networks, these campaigns are driven by the rapid adoption of autonomous weapons, drones and AI‑enhanced systems in the Ukraine conflict. By weaponizing everyday tools—messaging platforms, recruitment portals and edge devices—adversaries gain footholds that bypass conventional perimeter defenses, creating a persistent, multi‑vector siege on defense contractors.
Technical analysis shows attackers leveraging a blend of custom and off‑the‑shelf malware, from Windows batch scripts that decrypt Signal messages to Android trojans masquerading as firmware updates for battlefield control systems. The use of operational relay box (ORB) networks allows threat groups to route traffic through benign home or commercial connections, effectively evading geofencing and complicating attribution. Supply‑chain infiltration remains a critical vector, with malicious code injected into manufacturing software upgrades and edge‑device firmware, granting long‑term persistence and credential theft across the ecosystem.
For industry leaders, the report underscores the urgency of adopting zero‑trust architectures, continuous monitoring, and robust vendor risk management. Traditional endpoint detection and response (EDR) tools are increasingly circumvented, demanding behavior‑based analytics and threat‑hunting capabilities. Moreover, the convergence of espionage and financially motivated extortion amplifies the potential operational and reputational damage. Companies must prioritize hardened hiring pipelines, secure firmware supply chains, and collaborative intelligence sharing to mitigate the evolving threat landscape.
Google Links China, Iran, Russia, North Korea to Coordinated Defense Sector Cyber Operations
0
Comments
Want to join the conversation?
Loading comments...