Greater Pittsburgh Orthopaedic Associates Disclosed a 2025 Breach, but Was There Also One in 2024?
•February 24, 2026
0
Why It Matters
The dual‑year breach saga highlights gaps in healthcare cyber‑risk reporting and the potential exposure of sensitive patient data, underscoring regulatory and reputational stakes for medical providers.
Key Takeaways
- •2025 breach potentially encrypted data of 56,954 patients.
- •Notification letters mailed to patients in February 2026.
- •RansomHouse claimed encryption; no ransomware demand disclosed.
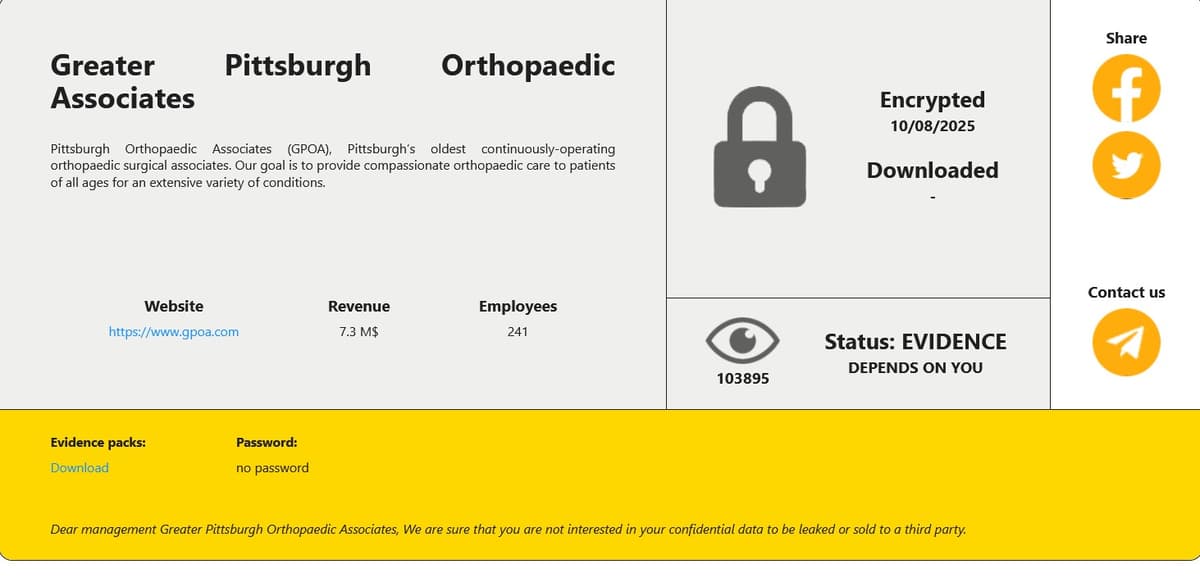
- •Possible 2024 attack by DonutLeaks remains unverified.
- •Discrepancies exist between HHS and Maine AG reports.
Pulse Analysis
The healthcare sector continues to be a prime target for cybercriminals, and the Greater Pittsburgh Orthopaedic Associates (GPOA) case illustrates how quickly a breach can evolve from a localized incident to a multi‑state regulatory headache. The August 2025 attack, allegedly executed by the ransomware group RansomHouse, reportedly encrypted patient records containing names, addresses, Social Security numbers, and provider details. While the breach notification arrived months later, the organization’s decision to provide credit‑monitoring via Cyberscout reflects a growing industry practice to mitigate post‑breach financial risk for patients.
Regulatory compliance adds another layer of complexity. GPOA initially reported 35,000 affected individuals to the U.S. Department of Health and Human Services, yet a subsequent filing to the Maine Attorney General listed nearly 57,000 records. Such discrepancies can trigger investigations, fines, and heightened scrutiny from oversight bodies, emphasizing the importance of accurate, timely breach reporting under HIPAA and state data‑privacy laws. The lag between discovery, reporting, and patient notification also raises questions about the adequacy of existing breach‑response frameworks within smaller medical groups.
The alleged 2024 incident involving the DonutLeaks collective, though never confirmed, serves as a cautionary tale about the shadowy nature of dark‑web disclosures. Even when a breach does not surface on official tools, the mere presence of a leak listing can erode patient trust and invite further attacks. Healthcare providers must therefore adopt proactive security measures—such as continuous network monitoring, robust encryption, and regular third‑party audits—to stay ahead of threat actors. As the GPOA saga demonstrates, transparent communication, swift remediation, and alignment with evolving privacy regulations are essential to protect both patient data and organizational reputation.
Greater Pittsburgh Orthopaedic Associates disclosed a 2025 breach, but was there also one in 2024?
0
Comments
Want to join the conversation?
Loading comments...