Hackers Exfiltrate NTDS.dit File, Gain Full Control of Active Directory Environments
•February 4, 2026
0
Why It Matters
The loss of NTDS.dit equates to total compromise of an enterprise’s identity fabric, enabling attackers to impersonate any user and move laterally unchecked. Prompt detection and remediation are essential to prevent prolonged data exfiltration and preserve trust in Windows domain environments.
Key Takeaways
- •NTDS.dit contains all domain credentials and policies.
- •Attackers use volume shadow copies to bypass file locks.
- •APT28, APT41, FIN6 known for NTDS extraction.
- •Trellix Helix correlates telemetry to detect exfiltration.
- •Response: reset KRBTGT, enforce MFA, isolate systems.
Pulse Analysis
Active Directory remains the backbone of enterprise identity management, and the NTDS.dit file is its most sensitive component. It stores every user’s password hash, privileged account credentials, group memberships, and trust relationships. When this database is exfiltrated, attackers obtain a master key to the entire network, bypassing the need for phishing or brute‑force attacks and dramatically accelerating the breach timeline.
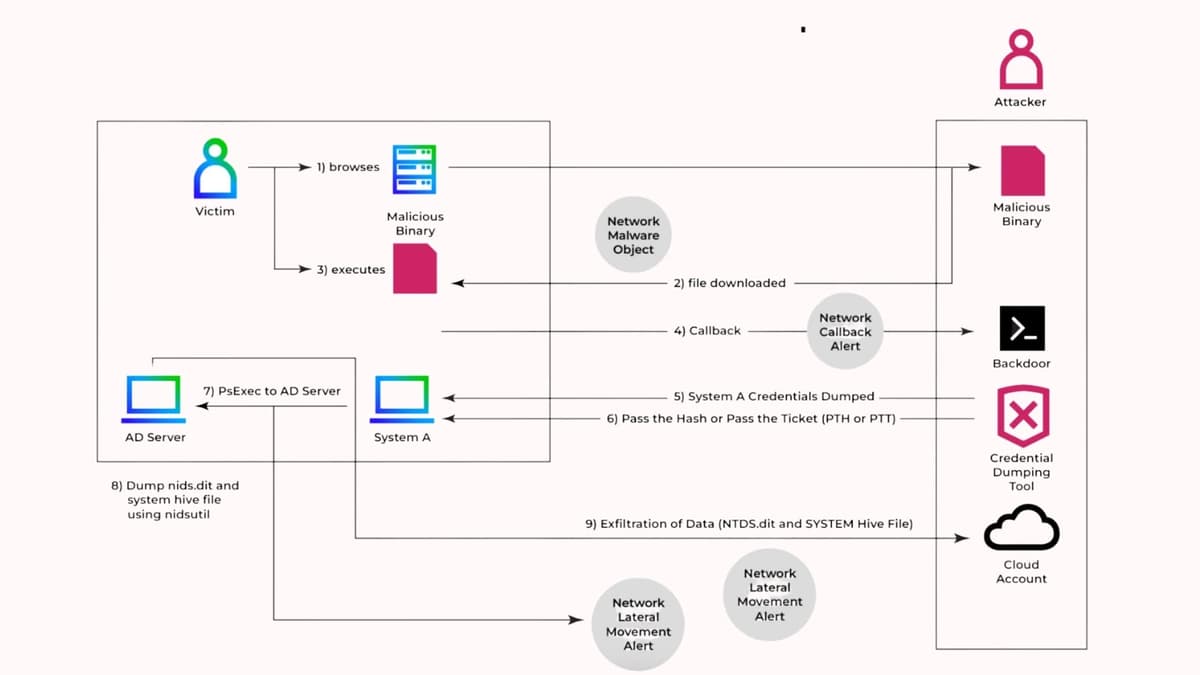
The extraction technique relies on Windows’ native Volume Shadow Copy Service, which creates a read‑only snapshot of the system volume. By invoking tools like vssadmin, ntdsutil, or third‑party utilities such as SecretsDump and Mimikatz, threat actors can copy the locked NTDS.dit file, combine it with the SYSTEM hive, and decrypt the hashes offline. APT‑linked groups—including APT28, APT41, and FIN6—have refined this low‑noise approach, making detection difficult for isolated endpoint or network sensors. Integrated platforms like Trellix Helix address the gap by correlating endpoint, network, and cloud telemetry, flagging suspicious shadow‑copy creation, PsExec usage, and anomalous SMB traffic.
Mitigation requires a layered response: immediate isolation of affected domain controllers, disabling compromised accounts, and rotating the KRBTGT password twice to invalidate existing Kerberos tickets. Organizations should enforce MFA for all privileged users, restrict administrative share access, and deploy Credential Guard alongside application whitelisting to block unauthorized tooling. Continuous monitoring of shadow‑copy operations and automated playbooks that trigger on MITRE ATT&CK T1003.003 indicators can dramatically reduce dwell time and protect the integrity of the Active Directory ecosystem.
Hackers Exfiltrate NTDS.dit File, Gain Full Control of Active Directory Environments
0
Comments
Want to join the conversation?
Loading comments...