.webp?ssl=1)
How Security Teams Use IP Location and DNS History In Cybercrime Investigation
•January 18, 2026
0
Why It Matters
Integrating IP and DNS intelligence accelerates detection, improves attribution, and reduces false positives, directly strengthening an organization’s incident response and risk management.
Key Takeaways
- •IP location reveals geographic and hosting anomalies.
- •DNS history links domains to shared malicious infrastructure.
- •Combined pivots reduce false positives and improve attribution.
- •Automation supplies data; analysts provide contextual judgment.
- •Insider threats surface through unusual external DNS connections.
Pulse Analysis
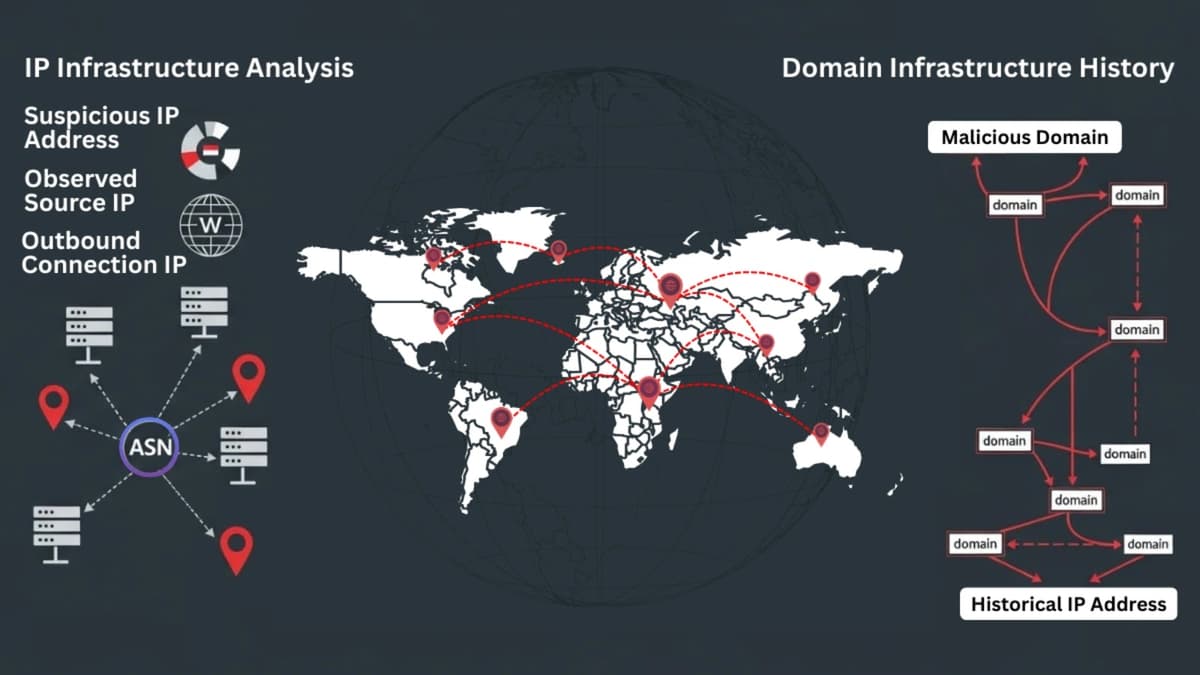
Understanding attacker infrastructure begins with the simplest indicator: an IP address. When a security alert fires, IP location data supplies immediate clues about geography, autonomous system numbers, and hosting environments. Analysts can spot VPNs, data‑center IPs, or low‑reputation providers that suggest compromise. However, IPs alone are volatile—cloud services recycle addresses and malicious actors rotate servers—so relying solely on geolocation can produce misleading conclusions.
The real power emerges when IP insights are paired with DNS history. Historical DNS records expose how a domain has migrated across IPs, revealing persistent backend servers that survive takedowns. By mapping these shifts, investigators can connect seemingly unrelated phishing sites, ransomware portals, or botnet command‑and‑control nodes to a common infrastructure cluster. This longitudinal view uncovers campaign‑level patterns, enabling defenders to preemptively block entire networks rather than isolated domains.
While many Security Operations Centers automate enrichment, human judgment remains essential. Analysts must weigh automated signals against behavioral evidence, timing, and threat‑intel feeds to avoid false attribution—especially when legitimate cloud services share infrastructure with adversaries. The combined workflow—suspicious IP, associated domain, DNS chronology, and pivot analysis—creates a layered, evidence‑based case that satisfies compliance, supports legal actions, and enhances overall cyber resilience.
How Security Teams Use IP Location and DNS History In Cybercrime Investigation
0
Comments
Want to join the conversation?
Loading comments...