How to Use Cyber-Deception in Your Security Strategy
•February 24, 2026
0
Why It Matters
Deception provides early, high‑confidence alerts that reduce dwell time and complement traditional controls, making it a strategic asset for organizations facing sophisticated threats.
Key Takeaways
- •Decoys generate early breach signals, reducing dwell time
- •Proper tuning prevents false positives and attacker fingerprinting
- •Low‑cost canary tokens enable quick deployment for most firms
- •Integration with mature security programs maximizes deception effectiveness
- •Internal communication ensures teams respond to deception alerts
Pulse Analysis
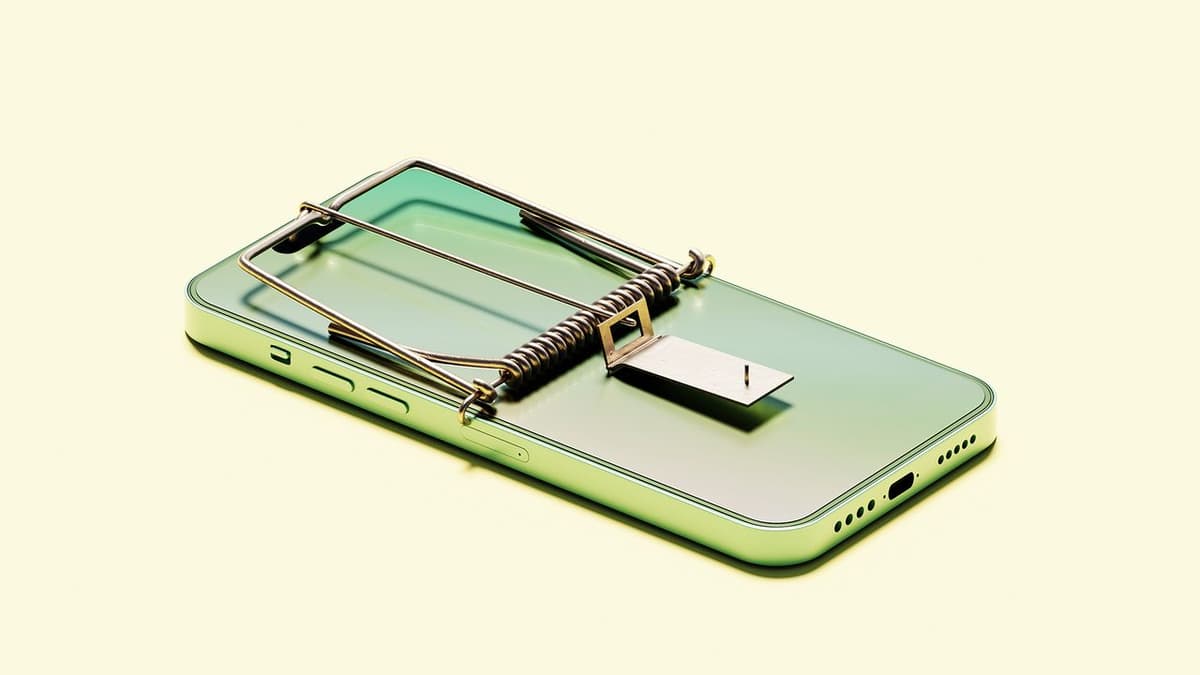
The accelerating pace of AI‑driven attacks has pushed cyber deception from a niche tactic to a core component of modern defense. In the United Kingdom, the National Cyber Security Centre (NCSC) has partnered with industry players to build a nation‑scale evidence base, citing a “compelling case” for broader adoption. This endorsement reflects a shift toward proactive threat hunting, where fake assets such as honeypots, honeytokens, and simulated credentials act as tripwires. By luring adversaries into controlled environments, organizations gain visibility into tactics that traditional controls often miss, especially lateral movement and credential abuse.
Deploying deception, however, demands careful design. High‑fidelity decoys must mimic real assets in behavior, configuration, and context to avoid easy fingerprinting. Open‑source and commercial platforms now offer plug‑and‑play honeypots, but success hinges on precise placement, continuous tuning, and integration with existing monitoring pipelines to keep alert noise low. Simple, low‑cost measures—such as canary tokens in shared drives or beaconed documents in crown‑jewel repositories—provide immediate value while limiting operational overhead. Organizations should define clear success metrics, whether faster detection, reduced dwell time, or higher‑confidence alerts, before scaling.
When layered on a mature security foundation, deception delivers measurable risk reduction. It complements vulnerability management, endpoint detection, and threat intelligence by forcing attackers onto false paths, wasting their time and exposing their methods. Internal communication about deployed decoys ensures response teams recognize and act on alerts, turning deception into an actionable intelligence source. As threat actors adopt automated fingerprinting tools, continuous rotation and contextual relevance of decoys become essential. Looking ahead, broader industry collaboration and shared threat data will likely refine best practices, making cyber deception an indispensable element of resilient enterprise security strategies.
How to use cyber-deception in your security strategy
0
Comments
Want to join the conversation?
Loading comments...