Microsoft: Critical Security Issue Found in Windows Notepad
•February 20, 2026
0
Why It Matters
The bug shows how adding modern features to trusted built‑in tools expands attack surfaces, making timely patches and cautious user behavior critical for enterprise security.
Key Takeaways
- •CVE‑2026‑20841 enables RCE via crafted Markdown links.
- •Exploit requires opening file and clicking malicious link.
- •Only modern Notepad with Markdown support is vulnerable.
- •Patch released in February 2026 Patch Tuesday.
- •Apply updates and avoid untrusted Markdown attachments.
Pulse Analysis
Notepad’s evolution from a simple text viewer to a feature‑rich editor reflects Microsoft’s push to modernize legacy utilities. By integrating Markdown rendering and clickable links, the app now meets developer expectations for lightweight documentation. However, this added complexity introduces new parsing logic that, if not rigorously vetted, can become a vector for attackers. The Notepad case underscores a broader industry pattern: even long‑standing, low‑profile components must undergo the same security scrutiny as flagship products.
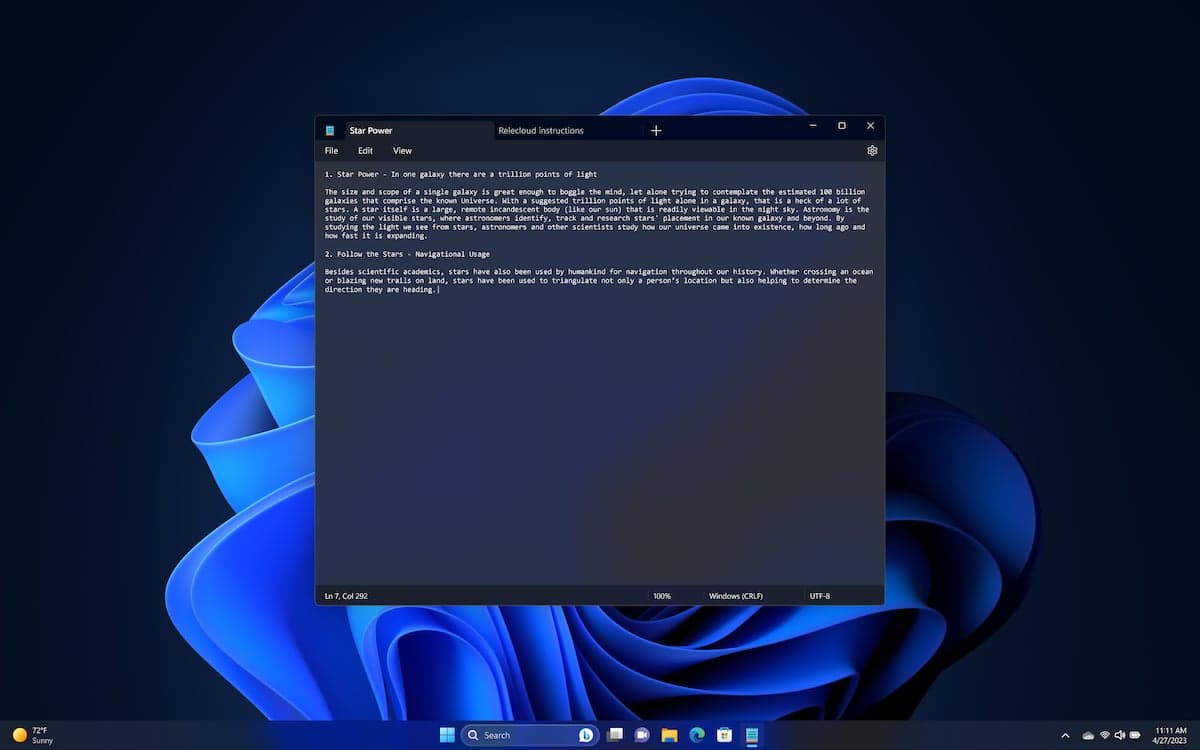
The CVE‑2026‑20841 flaw resides in the Markdown parser’s handling of protocol links. When a specially crafted .md file is opened, the parser misinterprets a link’s scheme, allowing arbitrary code to be executed under the current user’s context after the victim clicks the link. While the vulnerability does not trigger on plain‑text files, the required user interaction aligns with classic social‑engineering tactics, making phishing campaigns a likely exploitation path. If the compromised account holds administrative rights, the attacker could elevate privileges and move laterally across the network.
Mitigation steps are straightforward: deploy the February 2026 security update, enforce least‑privilege accounts, and educate users to treat Markdown attachments with the same caution as executables. Enterprises should also monitor for anomalous Notepad processes launching child applications, a tell‑tale sign of exploitation. This incident serves as a reminder that feature creep in trusted utilities can inadvertently broaden the threat landscape, reinforcing the need for continuous code review and rapid patch cycles.
Microsoft: Critical Security Issue Found in Windows Notepad
0
Comments
Want to join the conversation?
Loading comments...