Microsoft Entra ID Will Auto-Enable Passkey Profiles, Synced Passkeys
•January 26, 2026
0
Companies Mentioned
Why It Matters
The change streamlines password‑less authentication across enterprises, giving security teams granular control while reducing manual migration effort. It accelerates adoption of modern, phishing‑resistant credentials in the Azure ecosystem.
Key Takeaways
- •Passkey profiles become GA March 2026.
- •New passkeyType property controls device‑bound vs synced.
- •Automatic migration for tenants that do not opt‑in.
- •Group‑based policies replace tenant‑wide passkey settings.
- •Microsoft campaigns now include passkey registration flow.
Pulse Analysis
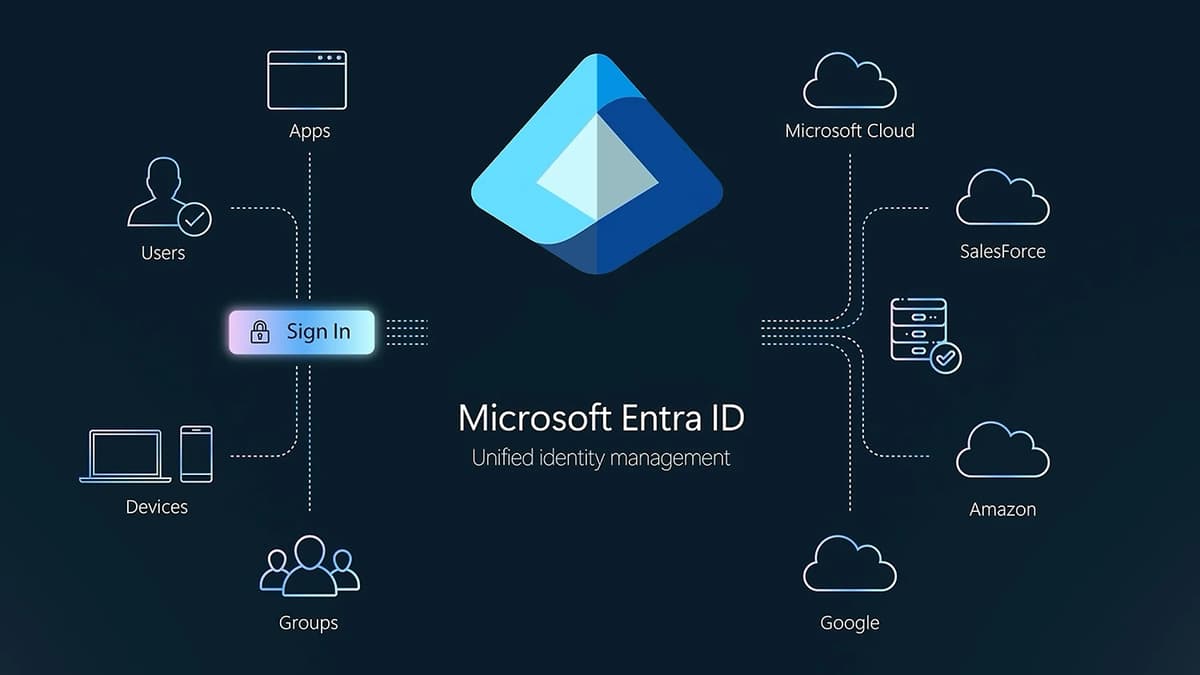
The shift toward password‑less authentication has gathered momentum as organizations seek to curb credential‑based breaches. Microsoft’s Entra ID, a core identity platform for Azure and Microsoft 365, is now positioning passkeys—cryptographic credentials stored on devices or synced to the cloud—as the default authentication method. By announcing automatic enablement for passkey profiles in March 2026, Microsoft signals confidence that the ecosystem of browsers, devices, and security keys is mature enough for broad enterprise rollout. This move aligns with industry standards such as WebAuthn and FIDO2, reinforcing the platform’s compatibility with emerging digital identity frameworks.
At the heart of the update is the passkeyType property, which grants administrators the ability to dictate whether users can register device‑bound passkeys, cloud‑synced passkeys, or a hybrid of both. Coupled with group‑based configuration, security teams can now tailor policies to specific departments, high‑risk users, or geographic regions without imposing a one‑size‑fits‑all setting across the tenant. This granularity reduces friction for end‑users while preserving strict security postures, as organizations can pilot synced passkeys in low‑risk groups before broader adoption. The new experience also integrates with Microsoft‑managed registration campaigns, automatically prompting eligible users to enroll passkeys during routine sign‑in flows.
Microsoft’s staged rollout includes an automatic migration path for tenants that choose not to opt in early. Existing FIDO2 settings will be migrated into a default passkey profile, preserving current attestation configurations and minimizing administrative overhead. For IT leaders, the key action is a review of current authentication policies to ensure alignment with the upcoming schema. By embracing passkey profiles, enterprises can reduce reliance on passwords, lower phishing risk, and future‑proof their identity infrastructure as the industry moves toward seamless, credential‑less access.
Microsoft Entra ID will auto-enable passkey profiles, synced passkeys
0
Comments
Want to join the conversation?
Loading comments...