MongoDB Vulnerability CVE-2025-14847 Under Active Exploitation Worldwide
•December 29, 2025
0
Companies Mentioned
Why It Matters
The exploit compromises confidential data on widely used database servers, forcing enterprises to patch quickly or risk regulatory penalties and breach fallout.
Key Takeaways
- •87k+ MongoDB instances vulnerable worldwide.
- •CVE-2025-14847 scores 8.7 CVSS.
- •Exploits leak memory via zlib compression flaw.
- •42% cloud environments host vulnerable MongoDB.
- •Patch by upgrading to MongoDB 8.2.3 or later.
Pulse Analysis
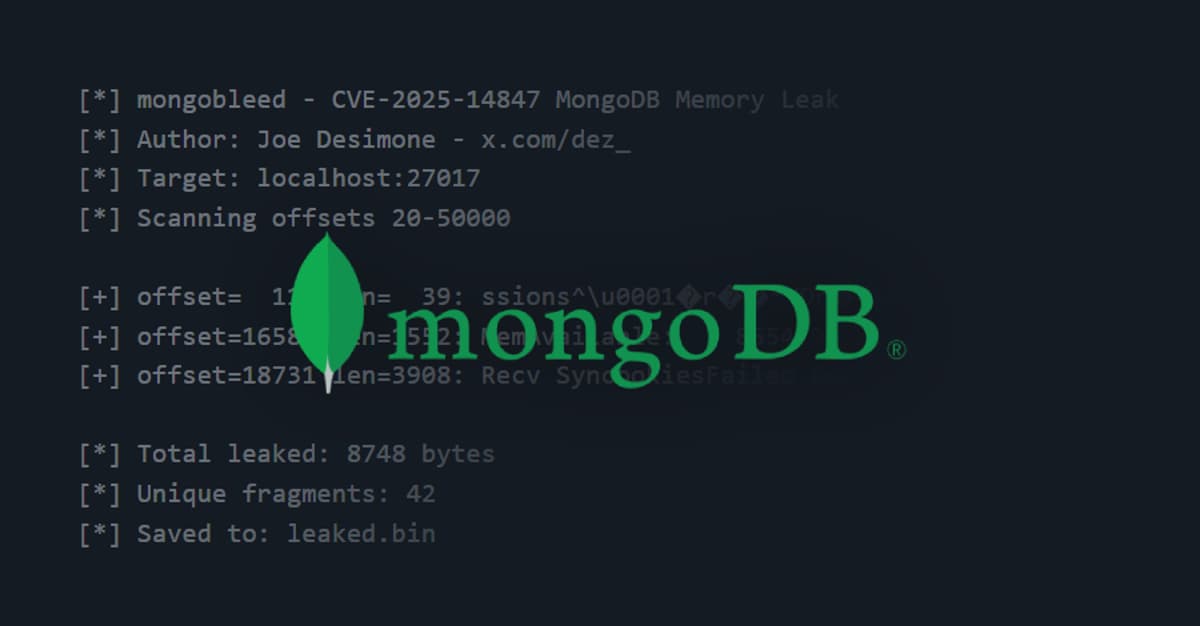
The MongoBleed flaw stems from an incorrect length‑parameter check in MongoDB's zlib message decompression routine. By sending malformed compressed packets, an attacker can coax the server into returning uninitialized heap memory, effectively leaking fragments of data without any credentials. Because zlib compression is enabled by default, the vulnerability surfaces on any deployment that exposes the MongoDB port, making it a prime target for opportunistic threat actors scanning the internet for weak configurations.
Enterprises that rely on MongoDB for mission‑critical applications face immediate risk. The exposure of passwords, API keys and proprietary data can trigger cascading security incidents, from credential stuffing to supply‑chain attacks. Cloud providers report that nearly half of their customers run at least one vulnerable instance, underscoring the need for rapid remediation. Recommended steps include applying the official patches for versions 4.4.30 through 8.2.3, disabling zlib compression via the networkMessageCompressors setting, and tightening network access controls with firewalls or VPNs. Continuous monitoring of pre‑authentication logs can also help detect probing activity.
Looking ahead, the rapid inclusion of CVE‑2025‑14847 in CISA's catalog signals heightened regulatory scrutiny. Organizations must integrate vulnerability scanning for database services into their DevSecOps pipelines to avoid future exposure. The incident highlights the broader challenge of default‑on features that, while improving performance, can introduce severe attack surfaces. Proactive patch management, coupled with a zero‑trust network posture, will be essential for maintaining the confidentiality and integrity of data stored in MongoDB environments.
MongoDB Vulnerability CVE-2025-14847 Under Active Exploitation Worldwide
0
Comments
Want to join the conversation?
Loading comments...