Payouts King Ransomware Exploits QEMU VMs to Slip Past Endpoint Security
Companies Mentioned
Why It Matters
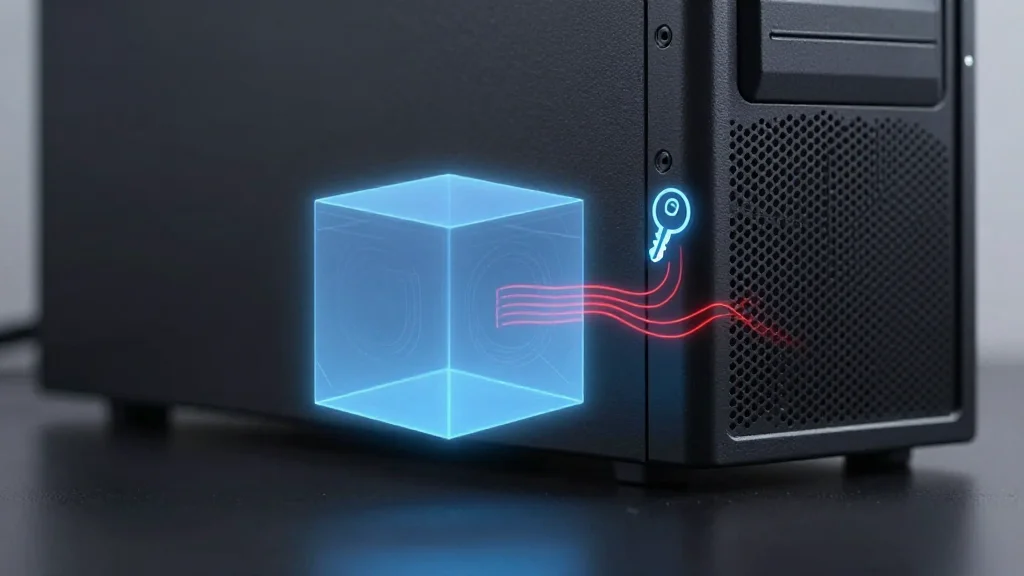
The emergence of QEMU‑based evasion raises the bar for ransomware operators, turning endpoint security into a cat‑and‑mouse game where attackers can hide entire operating systems from scanners. This development forces the cybersecurity industry to rethink detection models, emphasizing hypervisor visibility and network‑behavior analytics. If unaddressed, the technique could enable larger, more stealthy ransomware campaigns that exfiltrate data before encryption, amplifying the financial and reputational damage to victims. Moreover, the reuse of known initial‑access methods—exposed VPNs, Teams phishing, QuickAssist abuse—shows that threat actors continue to blend old and new tactics. Organizations that have patched high‑profile vulnerabilities but neglect basic access hygiene remain prime targets for sophisticated QEMU‑enabled attacks.
Key Takeaways
- •Payouts King creates hidden QEMU VMs via a scheduled task named “TPMProfiler”
- •VM runs Alpine Linux 3.22.0 with tools like AdaptixC2, Chisel, BusyBox, Rclone
- •Attackers use reverse SSH tunnels to bypass endpoint scans
- •Sophos identified two campaigns (STAC4713, STAC3725) linking QEMU use to ransomware
- •Zscaler ties Payouts King to former BlackBasta affiliates and similar initial‑access vectors
Pulse Analysis
The QEMU tactic signals a maturation of ransomware evasion that blurs the line between traditional malware and advanced persistent threats. By nesting malicious code inside a virtualized environment, attackers gain a sandbox that is invisible to most endpoint agents, effectively creating a ‘ghost’ operating system on the victim host. This mirrors tactics used by nation‑state actors who have long leveraged hypervisor abuse to hide command‑and‑control traffic.
From a market perspective, endpoint security vendors will need to accelerate development of VM‑aware modules. Products that can introspect guest OS activity or flag unexpected hypervisor calls will gain a competitive edge. Meanwhile, managed detection and response (MDR) services may see increased demand for deep‑packet inspection and anomaly‑based alerts that can surface the reverse SSH tunnels used by Payouts King.
Looking ahead, the convergence of ransomware and virtualization abuse could spawn a new class of “virtual‑machine ransomware” that not only encrypts files but also retains a persistent foothold inside the hidden VM. Defenders must therefore broaden their threat‑model assumptions, incorporate hypervisor hygiene into patching cycles, and enforce strict network segmentation to limit the blast radius of any covert tunnel. The race is now on to bring visibility into the invisible layers that attackers are exploiting.
Payouts King ransomware exploits QEMU VMs to slip past endpoint security
Comments
Want to join the conversation?
Loading comments...