RenEngine Loader Deploys Stealthy Multi-Stage Execution to Bypass Security Measures
•February 6, 2026
0
Why It Matters
The campaign shows how threat actors weaponize popular gaming engines to bypass defenses, raising risk for gamers and enterprises alike. It underscores the need for tighter controls on pirated software distribution and advanced behavioral detection.
Key Takeaways
- •Over 400,000 victims worldwide since April 2025
- •5,000 new infections daily via pirated game downloads
- •Malware hides in Ren'Py game launcher archives
- •Uses sandbox evasion and process doppelgänging techniques
- •Deploys ACR Stealer to exfiltrate credentials and crypto
Pulse Analysis
The gaming ecosystem has become a fertile ground for cyber‑crime, and the latest RenEngine Loader campaign illustrates this trend vividly. By piggybacking on the open‑source Ren’Py visual‑novel engine, attackers disguise their payload as a harmless game installer, luring users who download cracked titles from illicit sites. Since April 2025 the operation has compromised more than 400,000 systems, with an average of 5,000 fresh infections per day across India, the United States and Brazil. This scale signals a shift from opportunistic ad‑ware to highly organized credential‑stealing operations targeting a broad consumer base.
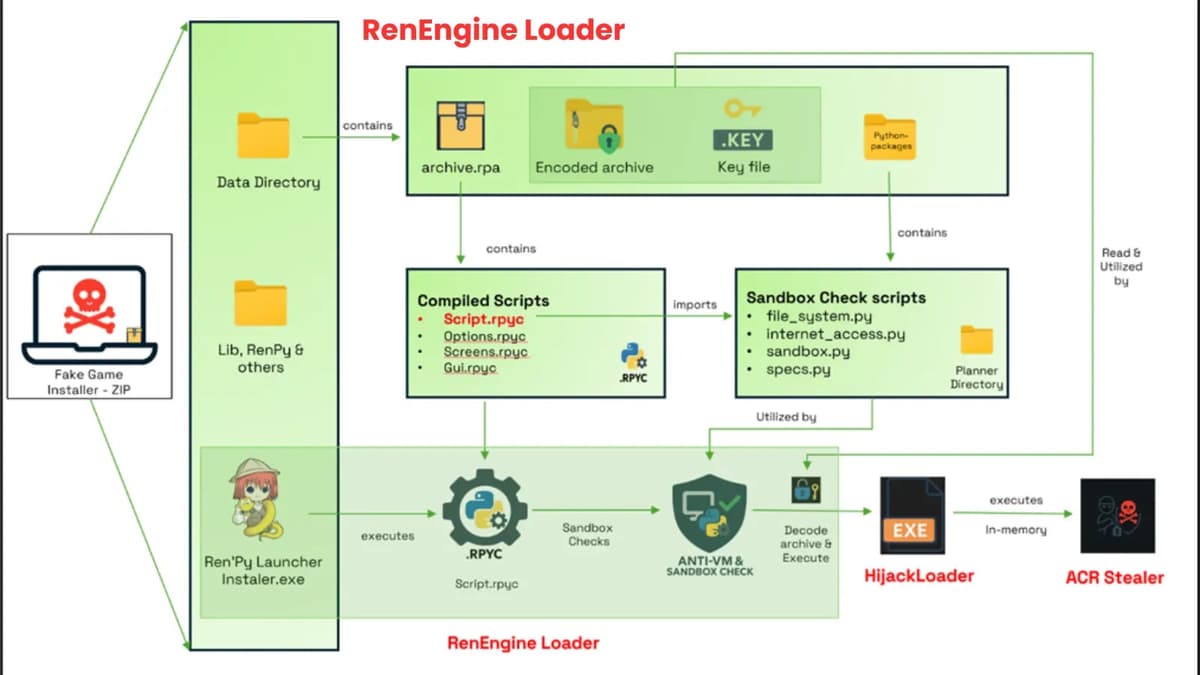
RenEngine Loader’s sophistication lies in its multi‑stage execution chain. The first stage performs rigorous sandbox evasion, checking RAM, disk size, mouse activity and virtualization artifacts before proceeding. Once the environment is deemed genuine, the loader decrypts a second stage—an evolved HijackLoader—equipped with 38 modules that employ DLL side‑loading, module stomping and GPU‑virtualization detection. The final delivery leverages Process Doppelgänging, a kernel‑level code‑injection method that injects the ACR Stealer into trusted processes, thereby slipping past signature‑based antivirus solutions and many behavioral monitors.
The implications for enterprises and security teams are immediate. Credential harvesters like ACR Stealer can feed large‑scale credential stuffing attacks, cryptocurrency theft and further ransomware campaigns. Defenders must augment traditional endpoint protection with heuristic and memory‑analysis tools capable of spotting abnormal process‑creation patterns and sandbox‑evasion logic. Moreover, organizations should enforce strict download policies, educate users about the dangers of pirated software, and monitor network traffic for unusual exfiltration to known attacker‑controlled domains. Proactive threat‑intel sharing on campaigns such as RenEngine Loader will be essential to stay ahead of this evolving threat vector.
RenEngine Loader Deploys Stealthy Multi-Stage Execution to Bypass Security Measures
0
Comments
Want to join the conversation?
Loading comments...