Researchers Null-Route Over 550 Kimwolf and Aisuru Botnet Command Servers
•January 14, 2026
0
Companies Mentioned
Why It Matters
Disrupting the C2 network curtails the botnet’s ability to launch DDoS attacks and monetize proxy services, forcing attackers to rebuild and buying time for defenders. The incident also illustrates the growing threat posed by compromised consumer devices that evade traditional security controls.
Key Takeaways
- •Null‑routed 550+ Aisuru/Kimwolf C2 servers.
- •Botnet controls over 2 million Android devices.
- •300% bot surge tied to residential proxy sales.
- •Exploits ADB and router firmware for propagation.
- •Resi Rack hosting used for C2 infrastructure.
Pulse Analysis
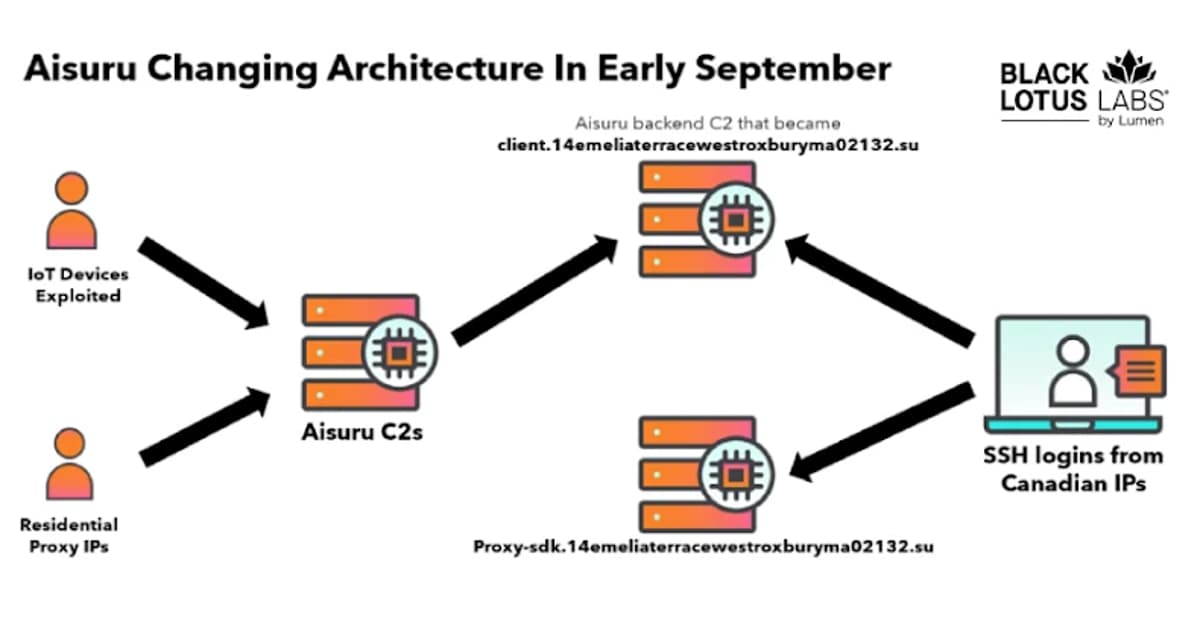
The AISURU/Kimwolf family has evolved from a simple Android‑TV malware into a sprawling residential‑proxy network that now compromises more than two million devices. By hijacking the Android Debug Bridge (ADB) on unsecured TV boxes and exploiting firmware flaws in home routers, the operators turn ordinary consumer hardware into low‑latency exit nodes for DDoS attacks and illicit traffic. Recent intelligence shows the botnet’s architecture pivoting toward SSH‑based command‑and‑control servers hosted on cloud‑friendly providers such as Resi Rack, blurring the line between legitimate hosting and malicious infrastructure.
In early October 2025 Black Lotus Labs, operating under Lumen Technologies, began null‑routing traffic to over 550 identified C2 domains, effectively cutting off command channels for a large slice of the botnet. The rapid 300 % increase in newly recruited bots—most listed for sale on a single residential‑proxy marketplace—demonstrated how quickly the threat actors can replenish their fleet when a single node is taken down. Null‑routing, while not a permanent cure, forces attackers to rebuild their infrastructure, buying defenders valuable time to update signatures and block compromised IP ranges.
The episode underscores a broader shift toward abusing consumer‑grade devices as stealthy proxies, a trend mirrored by the 832 compromised KeeneticOS routers reported by Chawkr. Because residential IPs carry clean reputations, malicious traffic can evade many traditional security filters, raising the stakes for network defenders and ISPs. Mitigation now requires coordinated takedown efforts, stricter default security on IoT and router firmware, and proactive monitoring of unusual SSH or ADB activity. As botnets continue to monetize proxy services, industry‑wide visibility and rapid response will be essential to curb their growth.
Researchers Null-Route Over 550 Kimwolf and Aisuru Botnet Command Servers
0
Comments
Want to join the conversation?
Loading comments...