SmarterMail Auth Bypass Exploited in the Wild Two Days After Patch Release
•January 22, 2026
0
Why It Matters
The exploit grants attackers full control over email servers, jeopardizing confidential communications and enabling lateral movement across networks. Its rapid post‑patch exploitation highlights weaknesses in disclosure practices and patch‑deployment speed.
Key Takeaways
- •Auth bypass lets password reset without credentials
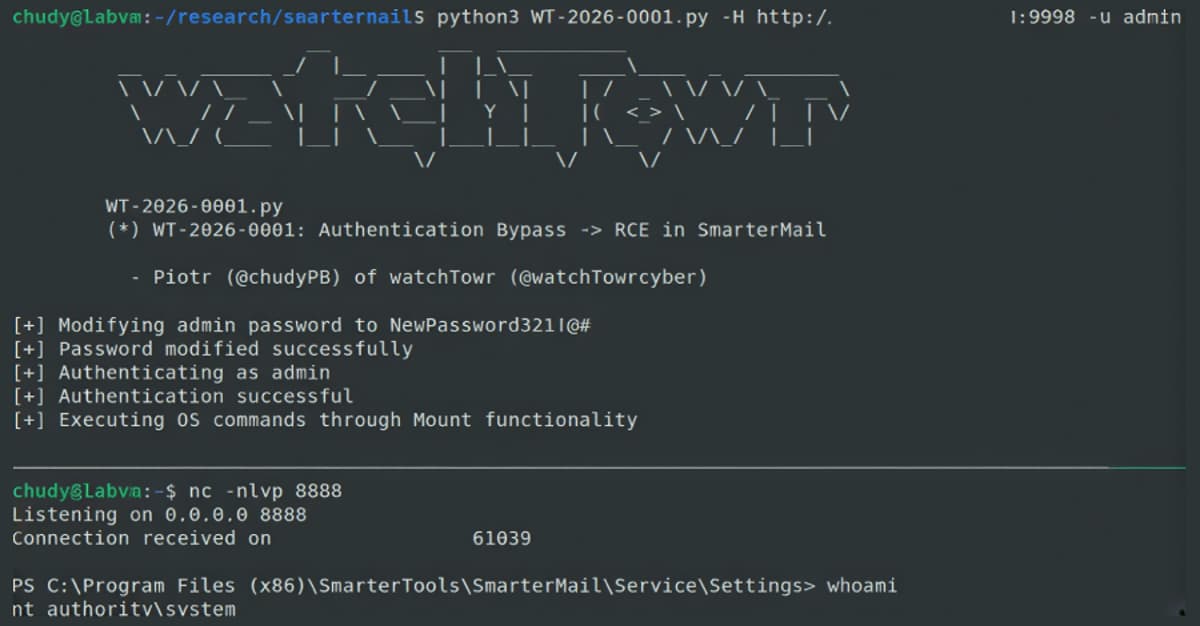
- •Exploit grants SYSTEM-level shell via volume mount
- •Patch released Jan 15, exploited by Jan 17
- •No CVE ID, tracked as WT‑2026‑0001
- •Vague release notes impede timely administrator alerts
Pulse Analysis
SmarterMail remains a staple for midsize enterprises seeking on‑premise email hosting, yet its recent authentication bypass underscores the hidden risks of legacy mail platforms. The flaw resides in the ForceResetPassword API, which erroneously accepts unauthenticated requests and a Boolean IsSysAdmin flag. By supplying a known admin username, an attacker can overwrite the admin password and, through the built‑in volume‑mount feature, inject arbitrary commands that run with SYSTEM privileges. This chain transforms a simple credential reset into remote code execution, effectively handing threat actors full control of the underlying server.
The timeline of this incident is striking: a responsible disclosure on Jan 8 prompted SmarterTools to issue Build 9511 on Jan 15, yet logs from Jan 17 show successful exploitation. The absence of a CVE identifier and the cryptic “critical security fixes” note in the release notes hampered rapid detection by security teams. Administrators relying on conventional patch‑notification channels may have missed the urgent nature of the update, leaving their environments exposed during the narrow window between patch release and exploit confirmation.
For the broader security community, the SmarterMail case reinforces the necessity of transparent vulnerability communication and swift, verifiable remediation. Vendors should assign CVE IDs promptly, detail affected components, and provide clear remediation steps to reduce ambiguity. Organizations must adopt layered defenses—such as network segmentation, strict API access controls, and continuous monitoring—to mitigate the impact of zero‑day exploits that surface shortly after patches. As email infrastructure continues to be a prime target, proactive threat‑intel sharing and disciplined patch management will be pivotal in preventing similar rapid‑fire attacks.
SmarterMail Auth Bypass Exploited in the Wild Two Days After Patch Release
0
Comments
Want to join the conversation?
Loading comments...