Techie Buys Fake Ledger Nano S+ Hardware Crypto Wallet and Almost Falls for Phishing — a Convincing Clone Would Have Caught Newbies Unaware
Companies Mentioned
Why It Matters
The incident highlights how counterfeit hardware can bypass user vigilance and exfiltrate crypto assets, underscoring the need for strict supply‑chain verification in the rapidly growing digital‑asset market.
Key Takeaways
- •Counterfeit Ledger Nano S+ uses ESP32‑S3 chip.
- •Ledger software flagged device as non‑genuine upon connection.
- •Embedded firmware harvests seed phrases and sends to C2 servers.
- •Fake Ledger app mimics website, distributes malicious desktop/mobile binaries.
- •Buy hardware wallets only from official channels to avoid scams.
Pulse Analysis
The hardware wallet market has exploded as investors seek tangible protection for crypto assets, yet the surge in demand has attracted counterfeiters. Devices that appear identical to reputable brands can slip through informal sales channels, especially on overseas marketplaces where price parity tempts buyers. Ledger’s built‑in device authentication provides a critical line of defense, but many users still rely on visual cues alone, leaving them vulnerable to sophisticated clones that mimic official firmware and branding.
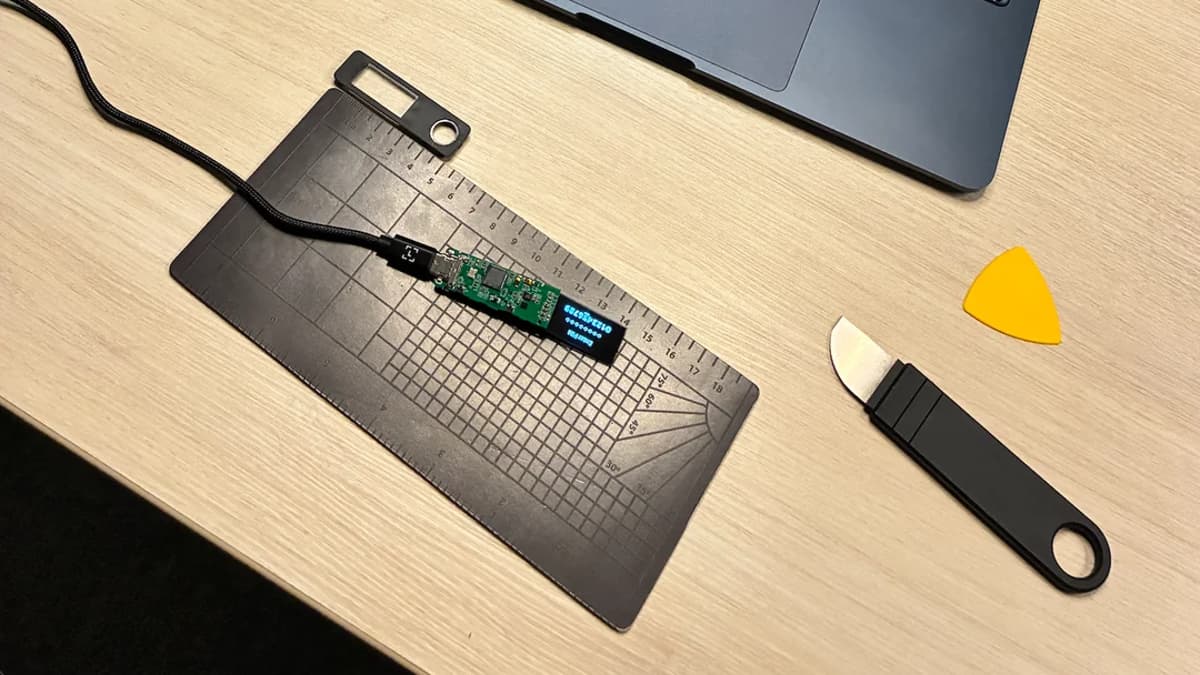
Mendes’s teardown revealed a full‑scale phishing operation hidden inside a fake Ledger Nano S+. The device’s core is an ESP32‑S3 system‑on‑chip, a versatile microcontroller commonly used in IoT projects, repurposed here to run malicious code. The firmware scrapes chip markings, fabricates a serial number, and stores a test PIN, seed phrases, and hard‑coded credentials for command‑and‑control servers. A counterfeit Ledger app, signed with an Android debug certificate, redirects users to a cloned ledger.com site where they can download trojanized Android, Windows, or macOS binaries. Even after the app is closed, it tracks location and monitors public‑key balances, alerting attackers to incoming funds.
For the broader crypto ecosystem, this episode is a cautionary tale about supply‑chain integrity. Users must purchase hardware wallets directly from manufacturers or authorized resellers, verify device authenticity through official software, and avoid scanning QR codes or downloading apps from packaging. Companies like Ledger are likely to tighten firmware verification and expand public awareness campaigns. As the industry matures, robust provenance checks and user education will become essential safeguards against increasingly sophisticated counterfeit attacks.
Techie buys fake Ledger Nano S+ hardware crypto wallet and almost falls for phishing — a convincing clone would have caught newbies unaware
Comments
Want to join the conversation?
Loading comments...