The Future of Cybersecurity Includes Non-Human Employees
•January 7, 2026
0
Companies Mentioned
Why It Matters
Securing NHIs closes a rapidly expanding attack vector, safeguarding automated workflows and cloud environments that underpin modern business operations. Failure to govern machine identities can lead to privileged credential compromise and regulatory non‑compliance.
Key Takeaways
- •NHIs now equal security priority to human accounts
- •Over‑permissioned bots create hidden attack vectors
- •Zero‑trust, least‑privilege, JIT reduce NHI risk
- •Automated secret rotation prevents credential sprawl
- •PAM solutions centralize machine credential governance
Pulse Analysis
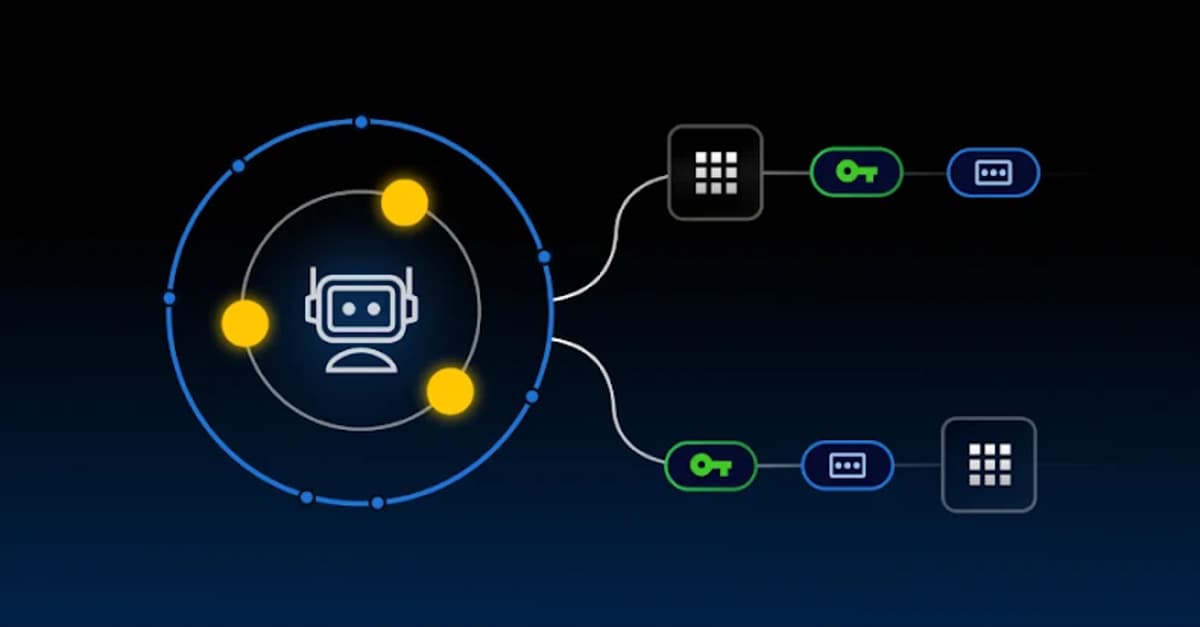
The rise of non‑human employees—bots, AI agents, service accounts—has transformed the identity landscape. As organizations accelerate AI and cloud automation, the number of machine identities dwarfs human users, expanding the attack surface. These entities often retain static credentials and broad, standing permissions, making them lucrative targets for threat actors. Traditional Identity and Access Management (IAM) solutions, built around human users, frequently miss these hidden actors, leaving gaps in visibility, logging, and auditability.
Zero‑trust principles offer a pragmatic path to securing NHIs. By treating every machine identity as an untrusted entity, firms can enforce strict authentication, role‑based access controls, and time‑bound credentials. Just‑in‑Time (JIT) access and ephemeral secrets replace permanent API keys, while automated rotation curtails credential sprawl. Coupled with comprehensive logging and continuous monitoring, these measures ensure that any anomalous activity is detected early, aligning with regulatory mandates and reducing the dwell time of compromised accounts.
Privileged Access Management (PAM) platforms, such as KeeperPAM, provide the orchestration layer needed to govern both human and non‑human credentials at scale. Centralized secret vaults, zero‑knowledge encryption, and session monitoring enable enterprises to audit machine activity, enforce least‑privilege policies, and rotate secrets without manual intervention. As automation becomes the backbone of digital transformation, integrating PAM with zero‑trust frameworks is essential for maintaining resilience against sophisticated cyber threats and preserving operational continuity.
The Future of Cybersecurity Includes Non-Human Employees
0
Comments
Want to join the conversation?
Loading comments...