Companies Mentioned
Why It Matters
Risk concentrates in the long‑tail of open‑source images, so focusing only on popular components leaves most vulnerabilities unaddressed and drives demand for comprehensive security platforms.
Key Takeaways
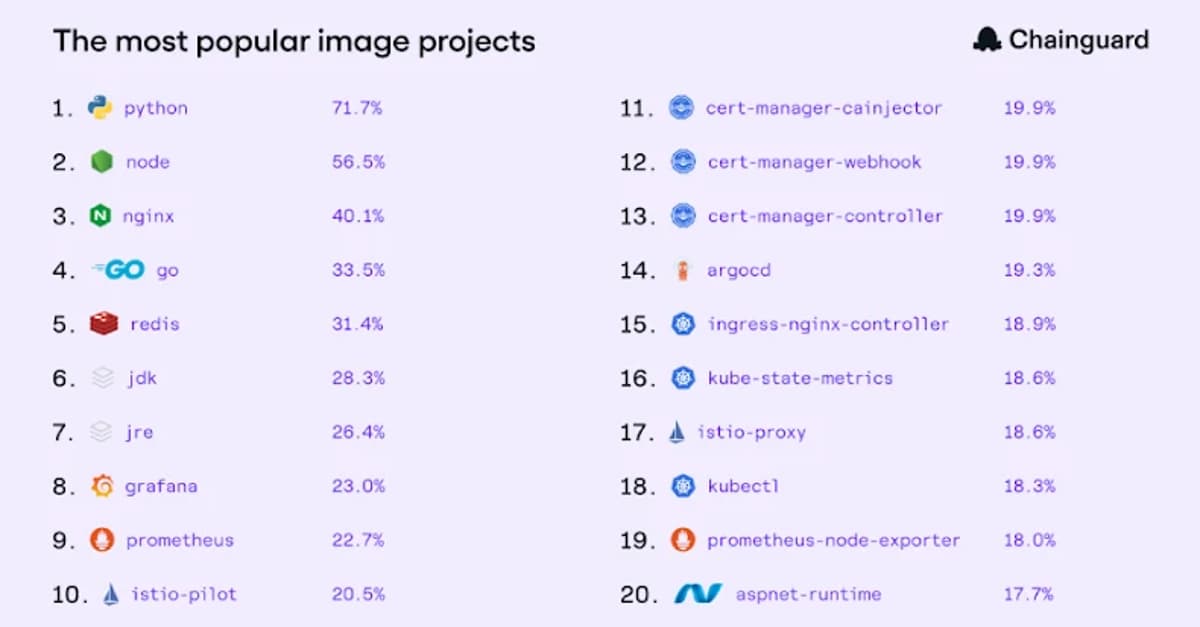
- •Python dominates AI container stack (71% customers)
- •98% CVEs found in long‑tail images
- •Long‑tail images represent 61% of portfolio
- •44% customers run FIPS‑validated images
- •Critical CVEs fixed in under 20 hours
Pulse Analysis
The Chainguard report highlights a fundamental shift in how modern enterprises build software. Python’s dominance—used by more than 70% of customers—reflects the rise of AI‑driven workloads, while traditional runtimes like Node, Go, and nginx remain core. Yet the data reveal that the so‑called “long‑tail” of over 1,400 less‑popular images supplies the other half of container pulls, proving that production environments are far more diverse than the top‑20 image list suggests.
Security implications are stark. Although the top‑20 images receive most of the visibility, they account for just 2% of CVE instances; the remaining 98% arise from long‑tail components, a 50‑fold disparity in exposure. Chainguard’s ability to remediate critical vulnerabilities in under 20 hours demonstrates that rapid response is feasible at scale, but only when tools can monitor the full breadth of the supply chain. Organizations that ignore the quiet majority risk blind spots that can lead to costly breaches.
Compliance also shapes adoption patterns. With 44% of customers running at least one FIPS‑validated image, regulatory requirements are a catalyst for broader security investment. Chainguard’s coverage of both popular and obscure images positions it as a strategic partner for enterprises seeking to meet federal standards while managing operational overhead. As open‑source dependencies continue to proliferate, the market will increasingly favor platforms that provide end‑to‑end visibility and remediation across the entire software bill of materials.
The State of Trusted Open Source
0
Comments
Want to join the conversation?
Loading comments...