VS Code Forks Recommend Missing Extensions, Creating Supply Chain Risk in Open VSX
•January 6, 2026
0
Companies Mentioned
Why It Matters
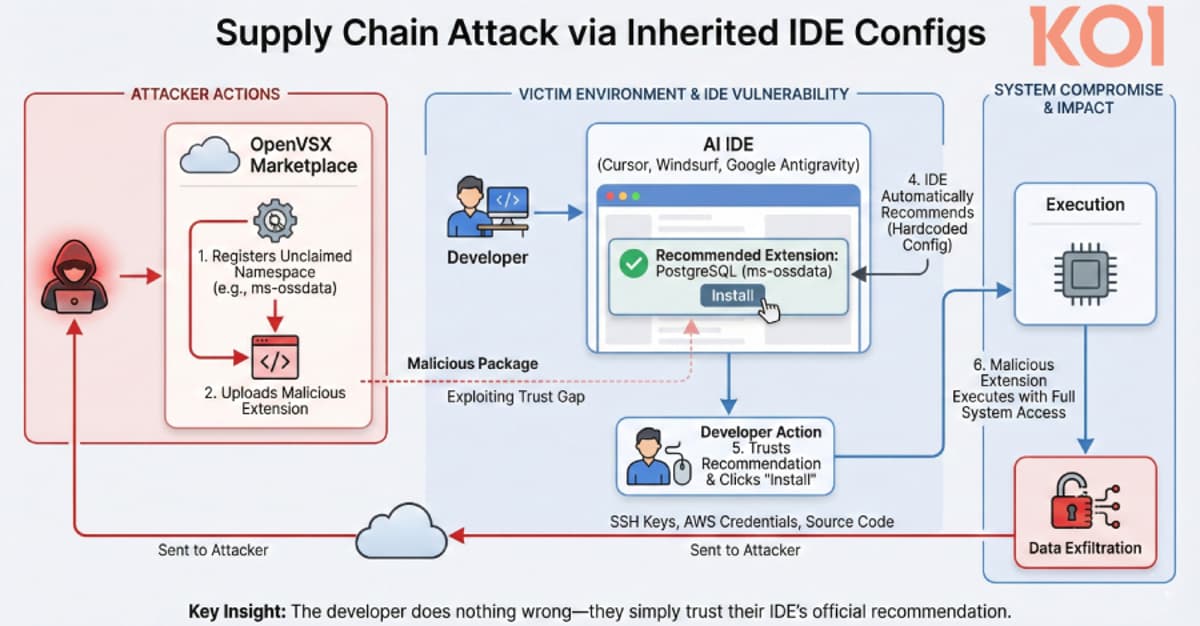
The flaw exposes developers to credential and source‑code theft through trusted IDE recommendations, highlighting a new attack vector in open‑source extension ecosystems.
Key Takeaways
- •AI‑powered VS Code forks recommend non‑existent extensions.
- •Missing extensions allow attackers to publish malicious packages.
- •Placeholder PostgreSQL extension recorded 500 installs.
- •Fixes deployed by Cursor, Windsurf, Google; Open VSX tightened controls.
- •Developers should verify publisher authenticity before installing.
Pulse Analysis
The discovery of phantom extension recommendations in popular VS Code forks underscores a growing blind spot in modern development tooling. While AI‑driven IDEs aim to boost productivity by surfacing relevant plugins, they inherit Microsoft’s curated list without verifying the presence of those packages in open registries like Open VSX. This mismatch creates a window for malicious actors to claim unregistered namespaces and publish rogue code, effectively weaponizing the IDE’s trust model. The incident mirrors recent supply‑chain attacks in software ecosystems, where a single compromised component can cascade into widespread compromise.
Open VSX, overseen by the Eclipse Foundation, has traditionally been a community‑driven alternative to Microsoft’s marketplace, offering open‑source extensions for a range of editors. The Koi researcher’s responsible disclosure prompted immediate remediation: the implicated forks rolled out updates that filter out missing recommendations, and the foundation removed non‑official contributors while introducing stricter namespace validation. These steps mitigate the immediate threat but also signal the need for continuous governance of open registries, including automated verification of publisher identities and provenance tracking for each extension.
For enterprises and individual developers, the episode serves as a cautionary tale about blind reliance on IDE suggestions. Security‑focused teams should incorporate extension vetting into their software‑bill‑of‑materials (SBOM) processes, enforce signed packages, and educate developers to cross‑check extension sources before installation. As AI‑enhanced development environments become more prevalent, maintaining a robust extension supply chain will be essential to protect intellectual property and operational integrity.
VS Code Forks Recommend Missing Extensions, Creating Supply Chain Risk in Open VSX
0
Comments
Want to join the conversation?
Loading comments...