Marquis Breach Toll Rises to 80 Banks, 824,000 Consumers
•January 5, 2026
0
Companies Mentioned
Why It Matters
The incident underscores persistent supply‑chain risks for community banks and the limits of patching when credential hygiene lags, prompting tighter regulatory scrutiny. It also highlights the financial and reputational costs of ransomware extortion in the fintech ecosystem.
Key Takeaways
- •823k customers impacted at 80 banks
- •Akira ransomware exploited SonicWall CVE‑2024‑40766
- •MFA bypass used stolen credentials despite patches
- •Marquis allegedly paid ransom to suppress data
- •Institutions offer up to 24 months credit monitoring
Pulse Analysis
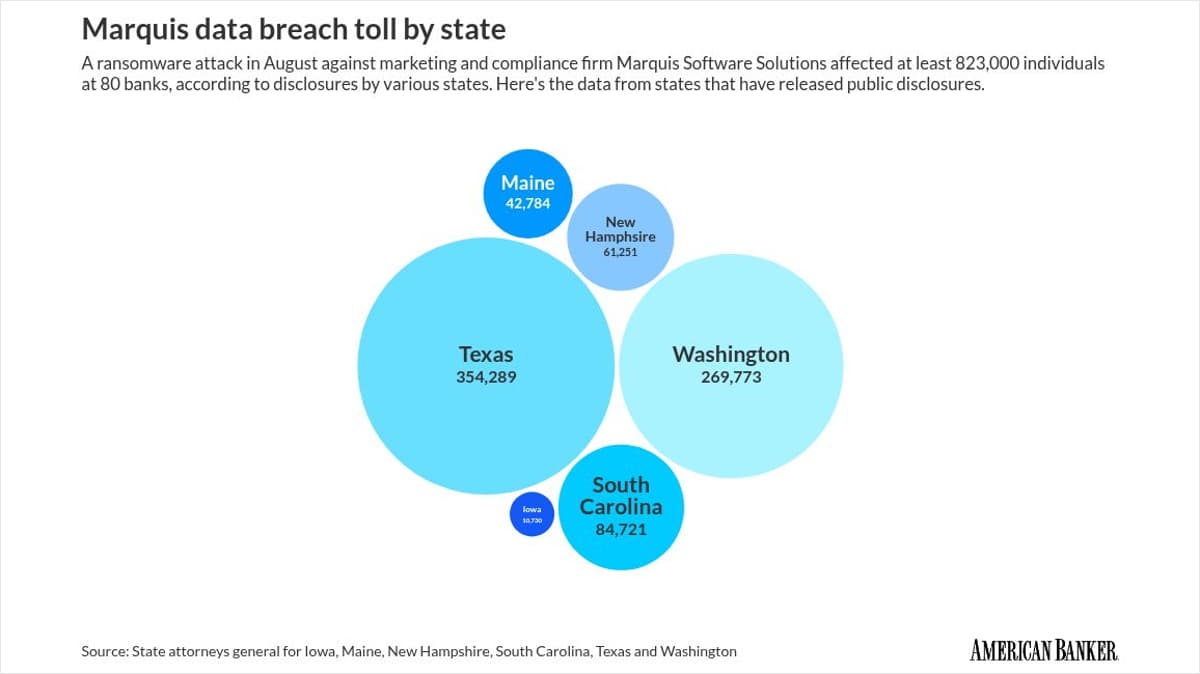
The Marquis Software Solutions breach has become a textbook case of supply‑chain risk for community‑banking institutions. Over 823,000 consumers at 80 banks and credit unions now face exposure of names, Social Security numbers, birth dates and account details—more than double the early estimate of 400,000. The scale of the incident forces regulators and boardrooms to reassess third‑party vendor oversight, especially as smaller banks lack the resources of larger lenders. As disclosures roll out across Texas, Washington, South Carolina and other states, the sector grapples with a sudden wave of notification obligations and potential litigation.
Security researchers traced the intrusion to the Akira ransomware group, which leveraged a known SonicWall VPN flaw (CVE‑2024‑40766) to breach Marquis’s network on August 14. Even after the vulnerability was patched, attackers sidestepped multifactor authentication by reusing credentials harvested before the update, a technique confirmed by Arctic Wolf Labs. Internal emails later revealed that Marquis paid a ransom to the criminals in exchange for data suppression, contradicting public statements that no misuse was evident. This dual failure—technical and governance—highlights how ransomware actors profit when organizations neglect credential rotation and incident‑response transparency.
In response, Marquis has deployed endpoint detection and response tools, rebuilt its servers on hardened operating systems, rotated local passwords and instituted geographic IP filtering. Affected banks are offering 12 to 24 months of complimentary credit‑monitoring and identity‑theft protection through Epiq, while state attorneys general issue advisories urging swift credential updates after firmware patches. The breach serves as a cautionary signal for the broader financial services ecosystem: robust third‑party risk programs, continuous MFA enforcement, and rapid post‑patch credential hygiene are now non‑negotiable components of cyber resilience.
Marquis breach toll rises to 80 banks, 824,000 consumers
0
Comments
Want to join the conversation?
Loading comments...