27,000-Download Codex UI Tool Secretly Stole OpenAI Refresh Tokens
Security researcher Charlie Eriksen uncovered that the popular npm package codexui-android, which has about 27,000 weekly downloads, contains hidden code that steals OpenAI authentication tokens, including long‑lived refresh tokens. The malicious payload is embedded only in the published package, bypasses source‑code audits, and activates immediately when the module loads, sending data to a disguised Sentry endpoint. The same infrastructure is used by Android apps published under the BrutalStrike developer, which install the package via a Termux‑derived Linux environment after passing Google’s security scans. The package and apps remain online, highlighting a new supply‑chain attack vector against AI developer tools.

Iran’s Nimbus Manticore Used Trojanized Zoom Installers Against US Firms
Check Point Research uncovered a campaign by Iran‑linked Nimbus Manticore that used trojanized Zoom installers and SEO‑poisoned sites to deliver AI‑assisted malware to U.S. aviation and software firms. Between February and April 2026 the group shifted from fake job offers...

How Can MSSPs Scale Threat Detection Without Burning Out Their Analysts?
Managed security service providers (MSSPs) face a talent bottleneck that limits analyst capacity as client demand surges. To avoid burnout, they are adopting AI‑driven threat intelligence, automated enrichment, and AI‑assisted triage from vendors like ANY.RUN. Integrated feeds, YARA‑based custom detection,...
Trojanized Gemini and Claude Installers Target Developers Via SEO Poisoning
Cybercriminals are leveraging SEO poisoning to promote typosquatted domains that mimic official AI tool installers such as Google Gemini CLI and Anthropic Claude Code. When developers follow the fake pages, a PowerShell script downloads a file‑less infostealer that silently installs...
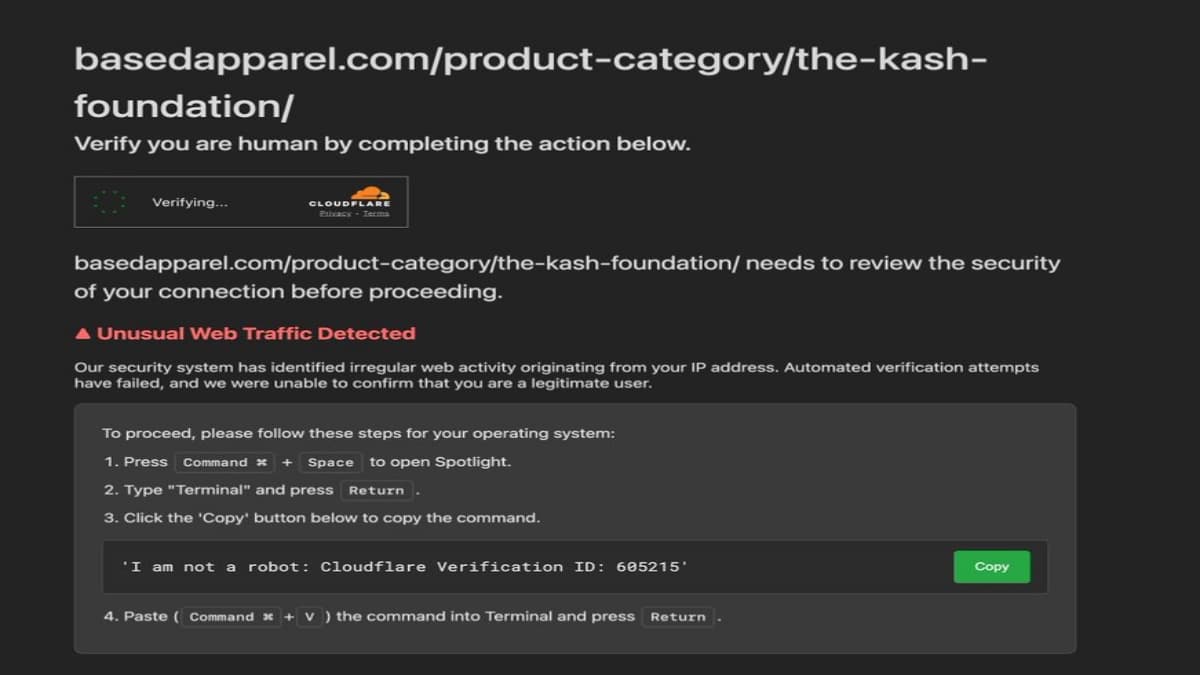
FBI Chief Kash Patel’s Clothing Store Hacked in ClickFix Infostealer Attack
An online clothing store tied to FBI Director Kash Patel, Based Apparel, was taken offline after a click‑fix attack distributed a macOS infostealer. The hack presented a counterfeit Cloudflare CAPTCHA that instructed visitors to paste malicious code into Terminal, enabling...

5,561 GitHub Repositories Hit by Megalodon Supply Chain Attack in Six Hours
Cybersecurity firm SafeDep uncovered a rapid supply‑chain attack dubbed Megalodon that compromised 5,561 GitHub repositories within six hours on 18 May 2026, injecting 5,718 malicious code updates. The attackers created fake accounts and inserted hidden workflow files (.github/workflows/ci.yml) that act as dormant...
Deleted Google API Keys Remain Active up to 23 Minutes, Study Finds
Aikido Security discovered that Google API keys remain functional for up to 23 minutes after deletion, with an average lag of 16 minutes. The delay stems from eventual consistency across Google’s global authentication servers, allowing attackers to continue accessing enabled...
Fake Word Phishing Reveals Enterprise Blind Spot in Trusted Remote Access Tools
A fake Word Online phishing page is being leveraged to deliver a silent MSI installer that launches ScreenConnect remote‑access software, then hides its activity with HideUL. The attack chain—email, fake preview, installer, remote tool—uses trusted enterprise utilities, allowing it to...
AI Agent Security: Automating Workflow Without Creating Prompt Injection or Data Leak Risks
Enterprises are rapidly deploying AI agents to automate tasks such as ticket triage, data summarization, and CRM updates. While these agents boost efficiency, their elevated authority creates new attack surfaces, notably prompt injection and data‑leak risks. The article outlines how...

New Reaper Malware Uses Fake Microsoft Domain to Steal macOS Passwords
SentinelOne’s research team has uncovered a new macOS infostealer, dubbed Reaper, that masquerades as legitimate updates for apps like WeChat and Miro. The malware leverages a typo‑squatted domain (mlcrosoft.co.com) to deliver a malicious Script Editor link that runs hidden AppleScript...

Government Backed Hackers Abuse Cloudflare in Malaysian Espionage Campaign
Oasis Security uncovered a multi‑year espionage campaign tied to the Malaysian government that uses hidden command‑and‑control servers cloaked behind Cloudflare’s CDN and storage services. The operators rotate and repurpose infrastructure to stay invisible, while malicious payloads and phishing pages are...
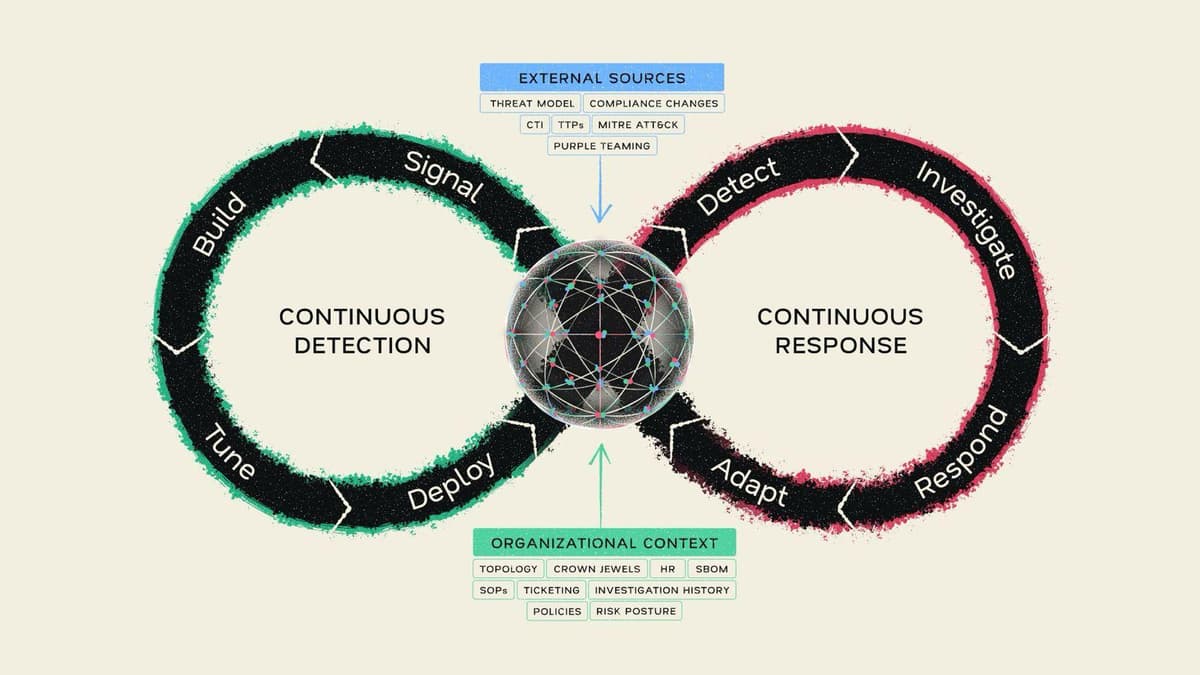
Continuous Detection, Continuous Response: Mate Security Redefines the Modern SOC
Mate Security unveiled its Continuous Detection, Continuous Response (CD/CR) model, which fuses detection and investigation into a single, self‑reinforcing loop. At the core is a Security Context Graph that aggregates real‑time organizational data from distributed sources, eliminating the need for...
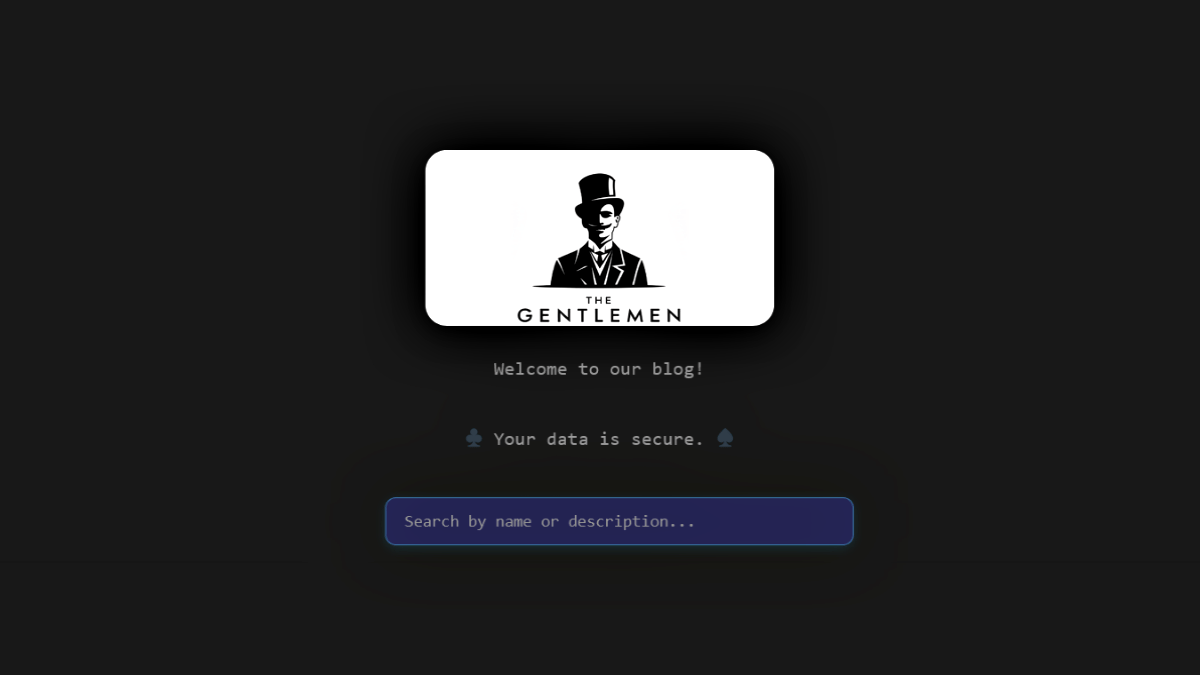
The Gentlemen Ransomware Gang Hit by Internal Breach, Operations Exposed
The Gentlemen ransomware gang suffered an internal breach in May 2026, exposing its backend infrastructure, affiliate communications, and victim‑management tools. Check Point Research uncovered leaked chats, databases, and evidence of over 1,570 probable victims, far exceeding the gang’s public leak counts....

Closing the Gap: The Regulatory and Structural Maturation of Digital Assets
Digital assets have moved from a niche experiment to a $2.66 trillion market, driven by structural reforms that separate custody, execution, and clearing. The U.S. GENIUS Act, enacted in July 2025, imposes a 100 % reserve requirement on stablecoins, turning them into transparent,...
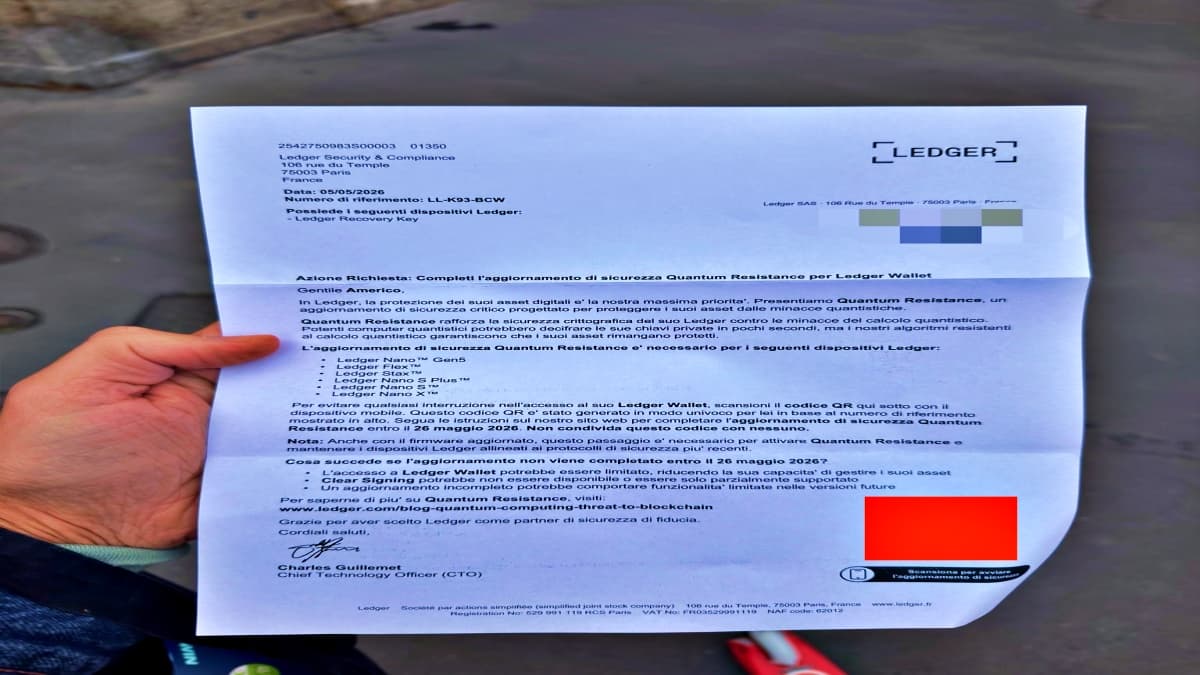
Scammers Send Physical Phishing Letters to Steal Ledger Wallet Seed Phrases
Scammers are sending forged Ledger‑branded letters that include QR codes to trick hardware‑wallet owners into revealing their 24‑word seed phrases. The campaign is localized, with versions in Italian and other languages, indicating attackers may have accessed customer shipping data from...