
Grafana Says It Rejected Ransom Demand After Source Code Theft
Grafana Labs reported that a threat actor accessed its GitHub repository using a compromised token, downloading parts of the company’s open‑source codebase. The investigation found no evidence of customer data exposure or impact on client systems. Grafana publicly refused the attacker’s ransom demand, citing FBI guidance that payments rarely protect stolen assets. The firm has revoked the compromised credentials and added new security safeguards while planning a post‑incident review.

CalPhishing Scam Uses EvilTokens Kit, Outlook Invites to Steal M365 Sessions
Cybercriminals are leveraging a new CalPhishing technique that embeds malicious iCalendar (.ics) files into Outlook invites, automatically adding tentative meetings to victims' calendars. The campaign, identified by Fortra Intelligence and Research Experts, uses the EvilTokens phishing kit sold on Telegram...

China-Linked Twill Typhoon Uses Fake Apple and Yahoo Sites for Espionage
Security firm Darktrace has identified a new wave of espionage attacks across Japan and the broader Asia‑Pacific region, attributed to the China‑linked group Twill Typhoon. The actors disguise malicious payloads as legitimate software and host them on counterfeit Apple and...
Pwn2Own Berlin 2026 Hits Capacity as Rejected Hackers Release 0-Days
Pwn2Own Berlin 2026 hit its registration limit on May 7, forcing organizers to close entries early. The surge in submissions is driven by AI‑enhanced tools such as Claude Code, GitHub Copilot, and others that accelerate zero‑day exploit creation. Researchers who were denied a...

Two US Men Jailed for Helping North Korean Hackers Infiltrate US Firms
Two American residents, Matthew Isaac Knoot and Erick Ntekereze Prince, were sentenced to 18 months in federal prison for operating laptop farms that let North Korean hackers masquerade as U.S. remote workers. The scheme, which ran from 2020 to 2024,...

Fake macOS Troubleshooting Sites Used to Steal iCloud Data in ClickFix Scam
Microsoft Defender researchers uncovered a new ClickFix campaign that lures Mac users with fake troubleshooting articles on platforms like Medium, Craft, and Squarespace. The pages urge victims to copy‑paste a terminal command, which silently downloads macOS stealer families such as...

Scammers Use Hidden Text to Bypass AI Email Filters in Phishing Scams
Security firm Sublime has uncovered a new phishing technique called indirect prompt injection, where attackers hide benign text in emails to manipulate AI‑based filters. By using zero‑font or color‑matched HTML, scammers embed content from reputable sources like Adidas newsletters or...

ShinyHunters’ Instructure Canvas LMS and Vimeo Breaches Impact Millions of Users
ShinyHunters disclosed a massive data breach affecting Instructure’s Canvas learning platform and video‑hosting service Vimeo. The group claims to have exfiltrated 3.65 TB of data, including 275 million Canvas records and private messages from roughly 15,000 institutions worldwide. Vimeo’s breach stemmed from...
Building Strategic Advantage With Integrated Planning
Integrated Business Planning (IBP) unites demand, supply, and financial forecasting into a single, disciplined cycle, replacing siloed decision‑making. By sharing assumptions across sales, operations, and finance, companies achieve earlier risk visibility, cleaner trade‑offs, and tighter control of margins, service levels,...
The “Juice” Factor: Designing Game Feel
Game feel, often dubbed “juice,” transforms basic mechanics into satisfying, immersive experiences. By layering visual cues like screen shake and hit‑stop, audio layers, and responsive camera work, developers give actions weight and immediacy. Input forgiveness techniques such as coyote time...

Application Security Strategies Are Changing as AI-Generated Code Floods the SDLC
AI coding assistants have shifted from experimental tools to daily development aids, accelerating function drafting, test generation, and repetitive changes. However, security teams now grapple with how much AI‑generated code reaches pull requests without proper validation, as 46% of developers...
Massive “Low and Slow” DDoS Attack Hits Platform With 2.45 Billion in 5 Hours
Cybercriminals launched a fragmented "low and slow" DDoS campaign that flooded a major user‑generated content platform with 2.45 billion requests over five hours. The attack leveraged more than 1.2 million unique IP addresses across 16,402 autonomous systems, peaking at 205,344 requests per...

Anti-ICE Site GTFO ICE Accused of Exposing Data of 17,000+ Activists
Former DHS chief Miles Taylor launched GTFO ICE, an anti‑ICE advocacy platform, in April 2026. Researchers discovered the site’s public REST API was unprotected and lacked rate‑limiting, allowing anyone to download the personal data of 17,662 users in seconds. The breach...
Wiz ZeroDay.Cloud Event Reveals 20-Year-Old PostgreSQL Vulnerabilities
Cybersecurity researchers at Wiz’s ZeroDay.Cloud event uncovered two critical, decade‑old vulnerabilities in PostgreSQL’s pgcrypto extension, CVE‑2026‑2005 and CVE‑2026‑2006. The flaws, dating back to 2005, enable buffer overflows and out‑of‑bounds memory writes that can lead to full database compromise. Wiz’s scans...

Cyber-Secure Philanthropy: Tech Infrastructure for Global Donations
Nonprofit donation platforms are increasingly targeted by ransomware, formjacking, and SQL‑injection attacks because many charities run outdated web forms and third‑party scripts without dedicated security staff. The article outlines how payment flows, API exposure, and weak compliance practices create exploitable...

7 Key Features That Make Secure Browsers Safer
New research shows browsers are involved in 48% of cyberattacks, making them the most exploited vector in modern workplaces. Gartner predicts enterprise adoption of secure browsers will rise from 10% today to 28% by 2028, reflecting growing awareness of the...
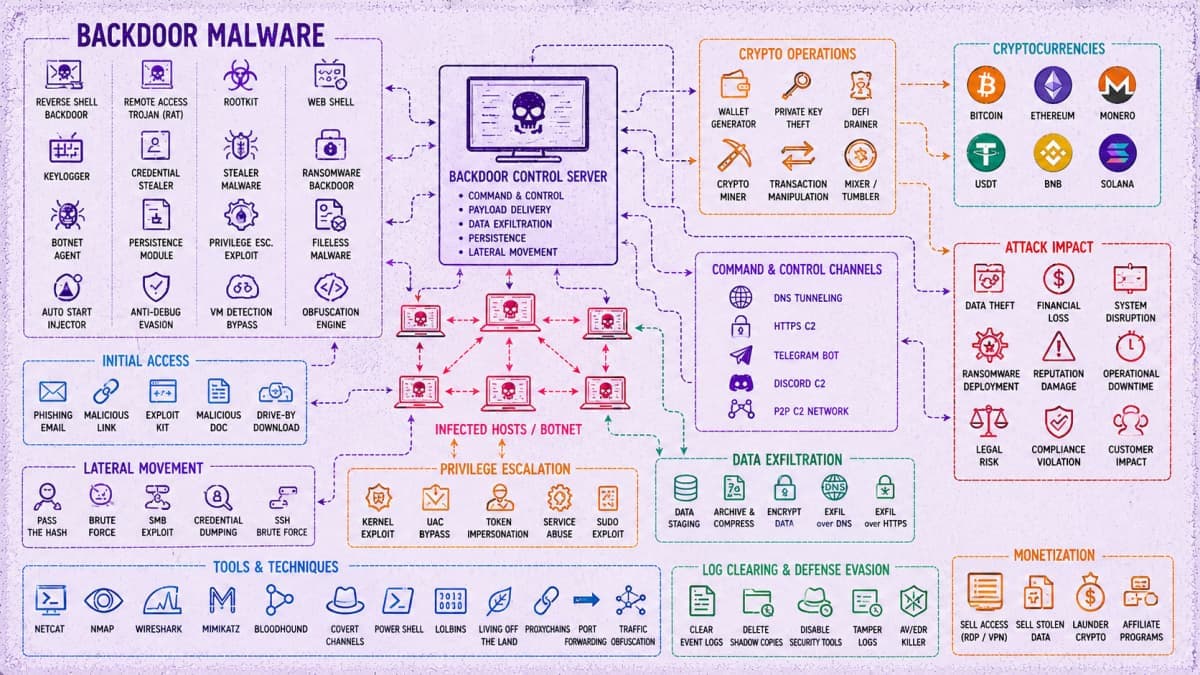
45,000 Attacks, 5,300+ Backdoors Tied to China-Linked Cybercrime Operation
The SOCRadar team uncovered a China‑linked cyber‑crime operation that runs a centralized backend called Paperclip and an agent workflow named OpenClaw. The automated infrastructure launched roughly 45,000 attack attempts, deploying over 5,300 backdoors across nearly 5,400 compromised hosts. Hackers focus...

Hackers Use Jenkins Access to Deploy DDoS Botnet Against Gaming Servers
Hackers exploited mis‑configured Jenkins servers via the scriptText endpoint to gain remote code execution and deploy a DDoS botnet aimed at Valve’s Source Engine game servers. The attackers delivered Windows and Linux binaries from a single Vietnamese IP address, using...
Private Chats, Photos of Celebs Exposed in Suspected Stalkerware Leak
Cybersecurity researcher Jeremiah Fowler discovered a massive leak of nearly 87,000 private images and chat logs belonging to a high‑profile European celebrity and several influencers. The data, stored in an unprotected online database, included screenshots from WhatsApp, Facebook, TikTok and...

Misconfigured Server Run by Hackers Leaks 345,000 Stolen Credit Cards
Researchers discovered a mis‑configured server operated by the Jerry’s Store card‑ing market, exposing 345,000 stolen credit cards after an AI‑assisted coding tool, Cursor, generated an unauthenticated web directory. The leak, uncovered on April 16, revealed over 145,000 active cards that...

Polymarket Rejects Data Breach Claims as Hacker Alleges 300K Records Stolen
A hacker identified as Xorcat alleges that they extracted roughly 300,000 records from Polymarket by exploiting undocumented API endpoints, a pagination bypass, and CORS misconfigurations. The purported data dump, said to total 2.24 GB, includes user profiles, market information, and an...

Top AI-Powered Vendor Risk Management Platforms for SaaS Companies in 2026
Vendor risk breaches now account for roughly 30% of incidents, prompting regulators like Europe’s DORA and the SEC to tighten third‑party oversight. AI‑powered TPRM platforms promise continuous, machine‑speed visibility, turning multi‑page SOC 2 reports into concise insights and auto‑generating tickets in...

Decoding Q1 2026’s $152.9 Billion Crypto Custody Concentration
Q1 2026 saw crypto trading volume plunge 48% to $4.3 trillion, prompting institutions to reallocate risk toward perpetual futures. Binance dominates the derivatives space, handling $1.4 trillion in monthly perpetual volume and holding $152.9 billion in custodial assets—73.5% of centralized‑exchange reserves. Perpetual‑futures volume...
Stablecoins: Always-On Money Needs Always-On Controls
Stablecoins now move money 24/7, turning payments into continuous financial infrastructure. Their adoption has expanded beyond trading to cross‑border settlements, treasury flows, and platform payouts, supporting roughly $4.2 trillion of economic activity in 2025. This round‑the‑clock operation exposes risks beyond private‑key...

Why Unofficial Download Sources Are Still a Security Risk in 2026
Downloading security and privacy software from unofficial sites remains a major risk in 2026. Users habitually click the first search result, often landing on third‑party mirrors that look legitimate but lack verification. Even when the installer is genuine, a confusing...

The Role of Aggregated Liquidity in Modern Crypto Markets
Liquidity fragmentation once made crypto trading chaotic, with thin order books and wide spreads across isolated venues. Aggregated liquidity solutions now combine order books, market makers, and pools from multiple sources, delivering deeper depth and tighter rates, especially for mid‑cap...

ShinyHunters Leaks Data of Udemy, Zara, 7-Eleven in Salesforce Linked Breach
The ShinyHunters hacker group posted dark‑web listings that claim to expose data from Udemy, Zara and 7‑Eleven, all allegedly harvested from Salesforce‑linked environments. Udemy’s dump is said to total 2.3 GB and over 1.4 million records, 7‑Eleven’s 12.8 GB contains more than 600,000...
Vidar Infostealer Spreads via Fake CAPTCHAs, Hides in JPEG and TXT Files
Point Wild’s Lat61 team uncovered a revamped Vidar infostealer that hides its payload in ordinary JPEG and TXT files. The campaign uses fake CAPTCHA prompts, compromised GitHub repositories, and steganography to deliver a multi‑stage, file‑less infection chain leveraging Windows LotL...
Microsoft Entra Agent ID Flaw Enabled Tenant Takeover via Privilege Escalation
Security researchers at Silverfort uncovered a critical flaw in Microsoft Entra's Agent ID framework that let the Agent ID Administrator role modify any Application Service Principal. By adding themselves as owners, attackers could inject credentials and impersonate high‑privilege accounts, including Global...
Fake CAPTCHA Scam Abuses Verification Clicks to Send Costly International Texts
Infoblox has uncovered a long‑running International Revenue Share Fraud scheme that disguises itself as a CAPTCHA verification. The fraud begins with typosquatted telecom domains that redirect users through a traffic distribution system to a fake CAPTCHA page. Each click on...

New ClickFix Attack Hides in Native Windows Tools to Reduce Detection Risk
CyberProof uncovered a new ClickFix campaign that tricks users into running malicious code via a fake CAPTCHA prompt. The attack leverages native Windows utilities cmdkey and regsvr32—known as LOLBins—to download a DLL from a remote server and register a scheduled...

K2view vs Broadcom For Test Data Management
The article pits Broadcom’s traditional, schema‑centric test data management (TDM) platform against K2view’s newer, entity‑centric solution. Broadcom offers solid integration with legacy databases but struggles with modern SaaS, cloud‑native, and NoSQL environments, and its self‑service portal is often seen as...

Mustang Panda Hits India and S. Korea with Updated LOTUSLITE Backdoor
China‑linked threat group Mustang Panda has broadened its espionage campaign to hit India’s banking sector and South Korean political circles. In March 2026 the actors delivered a malicious CHM file that installed the updated LOTUSLITE v1.1 backdoor on HDFC Bank workstations, while a...

Bluesky Back Online After DDoS Attack, as Iran-Linked 313 Team Takes Credit
Bluesky, the decentralized alternative to Twitter/X with about 43.7 million users, experienced a multi‑day outage after its API was flooded by a DDoS attack on April 15‑20, 2026. The attack was claimed by the Iran‑linked hacker group known as the 313 Team,...
Microsoft Vulnerabilities Drop, But Critical Flaws Double, Report Warns
BeyondTrust’s 13th Microsoft Vulnerabilities Report shows a 6% drop in total flaws to 1,273 this year, but critical vulnerabilities have doubled. Office suite bugs tripled, with a ten‑fold rise in critical issues, while Azure and Dynamics 365 saw nine times more...
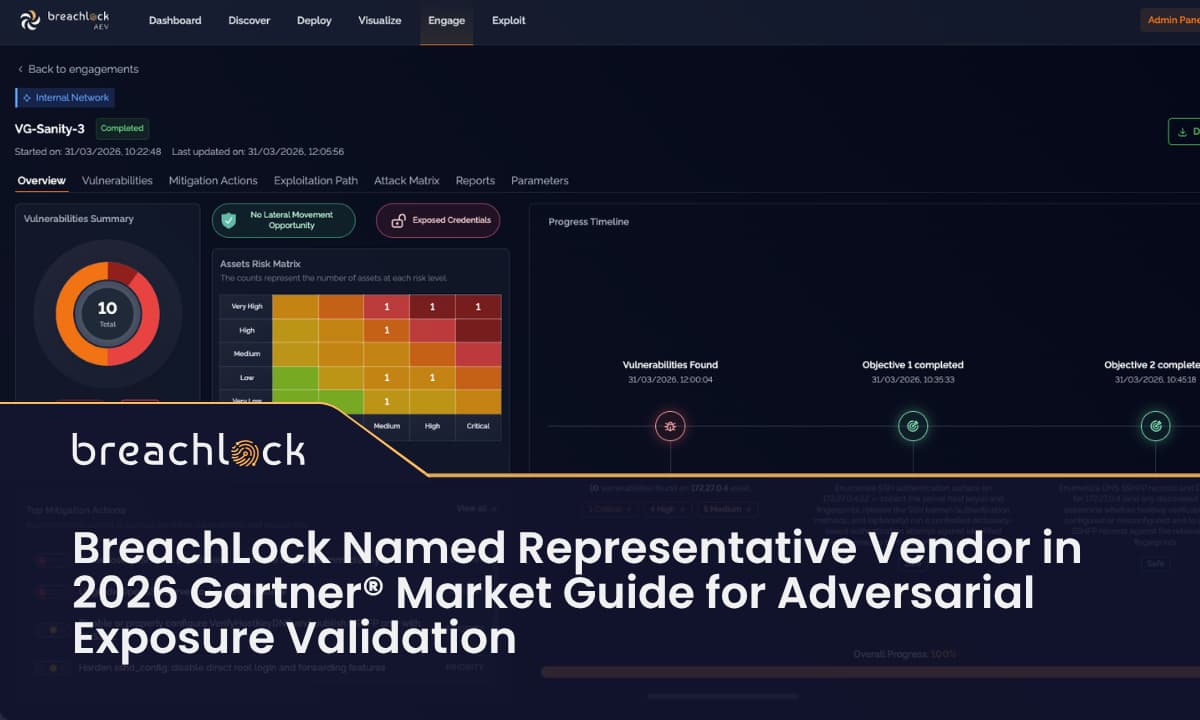
BreachLock Named Representative Vendor in the 2026 Gartner Market Guide for Adversarial Exposure Validation
BreachLock has been named a representative vendor in Gartner’s 2026 Market Guide for Adversarial Exposure Validation (AEV). The recognition follows the launch of its AI‑powered AEV platform in 2025 and highlights its unique combination of AEV, Penetration Testing as a...

The Ungoverned Workforce: Cybersecurity Insiders Finds 92% Lack Visibility Into AI Identities
Cybersecurity Insiders and Saviynt released a study revealing that 92% of enterprises lack full visibility into AI‑driven identities that now access core systems such as Salesforce and SAP. While 71% of CISOs confirm AI tools have such access, only 16%...

Threat Intel Scraping Without Burning Your Cover or Your Stack
Threat‑intel scraping lets security teams harvest breach dumps, malware samples, and exploit chains, but adversary‑run sites actively hunt bots, deploying honeypots, malicious payloads, and aggressive rate limits. A misconfigured scraper can trigger WAF blocks, expose the organization’s IP range, or...

Fake TikTok Downloaders on Chrome and Edge Spying on 130,000 Users
LayerX Security uncovered a coordinated campaign dubbed “StealTok” that distributes fake TikTok video‑downloader extensions on Chrome and Edge. The extensions, marketed as watermark‑free download tools, have silently harvested data from more than 130,000 users worldwide, with roughly 12,500 still active....
ShowDoc Vulnerability Patched in 2020 Now Used in Active Server Takeovers
Researchers have confirmed that the five‑year‑old ShowDoc vulnerability CVE‑2025‑0520 is being actively exploited to upload malicious PHP web shells, granting remote code execution and full server takeover. The flaw, an unrestricted file‑upload issue with a CVSS score of 9.4, was...

Founder Liquidity Without Compromising on Growth
Founder liquidity—selling a portion of personal equity—can free up cash without forcing an exit or diluting the company. The article explains that secondary transactions let founders sell shares directly to investors, sidestepping new funding rounds. Structured deals can even preserve...

New RecruitRat, SaferRat, Astrinox, Massiv Android Malware Found Targeting 800 Apps
Zimperium’s zLabs identified four new Android malware families—RecruitRat, SaferRat, Astrinox and Massiv—targeting over 800 banking and crypto apps. The campaigns use phishing and smishing to deliver malicious APKs, then launch overlay attacks that mimic legitimate login screens. By abusing Accessibility...

The Race to Quantum-Proof the Internet Has Already Begun
The tech industry is moving from viewing quantum computing as a distant risk to treating it as an imminent threat. Researchers at a Fhenix livestream warned that encrypted data can be harvested now and decrypted later once quantum computers become...

New Mirai Variant Nexcorium Hijacks DVR Devices for DDoS Attacks
Fortinet’s FortiGuard Labs uncovered Nexcorium, a new Mirai‑derived malware that hijacks TBK DVR‑4104 and DVR‑4216 video recorders via the CVE‑2024‑3721 command‑injection flaw. The variant spreads across IoT devices, installs persistence mechanisms, and uses hard‑coded default passwords to recruit additional cameras...
New CGrabber and Direct-Sys Malware Spread Through GitHub ZIP Files
Cyderes uncovered a sophisticated multi‑stage campaign that distributes new malware families—Direct‑Sys Loader and CGrabber Stealer—through ZIP files hosted on GitHub. The loader leverages DLL sideloading and direct syscalls to bypass antivirus and sandbox checks, while the stealer harvests passwords, crypto‑wallet...

OpenAI Launches GPT-5.4-Cyber to Boost Defensive Cybersecurity
OpenAI unveiled GPT-5.4-Cyber, a defensive‑focused variant of its flagship GPT‑5.4 model, featuring binary reverse‑engineering to analyze compiled code without source access. The launch coincides with the expansion of its Trusted Access for Cyber (TAC) program, now available to thousands of...
Cybersecurity Risks of Hiring a Virtual Assistant and How to Protect Your Business
The surge in remote work has led many firms to hire virtual assistants (VAs) without robust security checks, exposing critical systems to credential theft, device compromise, and insider threats. Excessive access and shared passwords create a large attack surface, while...

Anonymizing Network Traffic: A Dive Into SOCKS5 and Data Encryption
SOCKS5 proxies have become a core tool for businesses that need to hide IP addresses while handling any traffic type, from HTTP to UDP. Unlike HTTP proxies, SOCKS5 does not inspect data, allowing seamless use for streaming, automated data collection,...

Securing Remote Server Access: Why VPNs Matter for Administrators
Remote server administrators face brute‑force, phishing and malware attacks when SSH or RDP are exposed to the internet. Deploying a corporate VPN tunnels remote connections through encrypted channels, limiting access to authenticated users and removing direct exposure of critical ports....

13.5M Device Botnet Drives 2 Tbps DDoS Attacks on FinTech, Qrator Finds
Qrator Labs reported that the world’s biggest DDoS botnet has swelled to about 13.5 million compromised devices, a ten‑fold increase since March 2025. The network can launch attacks up to 2.065 Tbps, with a recent assault sustaining that peak for forty minutes....