Recent Posts
News•Mar 1, 2026
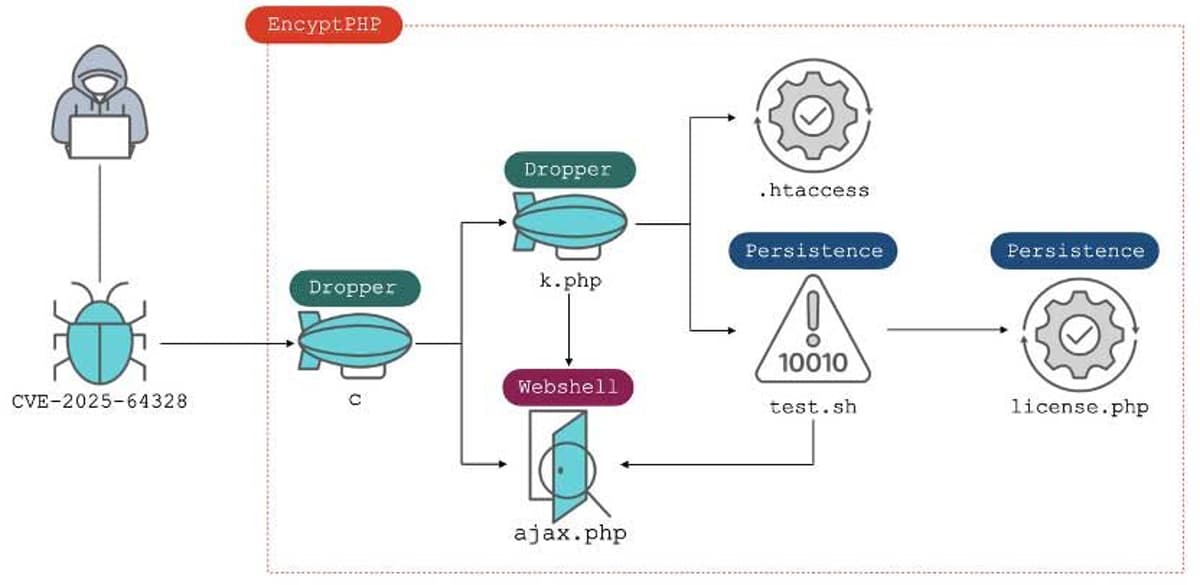
CVE-2025-64328 Exploitation Impacts 900 Sangoma FreePBX Instances
Around 900 Sangoma FreePBX installations were compromised after attackers leveraged CVE-2025-64328, a post‑authentication command‑injection flaw in the Endpoint Manager module. The vulnerability, rated 8.6 on the CVSS scale, allowed malicious code execution and led to the deployment of the EncystPHP PHP web shell. Threat group INJ3CTOR3 orchestrated the campaign, targeting systems worldwide and maintaining persistence through root‑level accounts and SSH key injection. CISA has added the flaw to its Known Exploited Vulnerabilities catalog, highlighting its severity.
By Security Affairs

News•Feb 28, 2026
Iran ’S Internet Near-Totally Blacked Out Amid US, Israeli Strikes
Iran experienced a near‑total internet blackout on Feb. 28, 2026, as U.S. and Israeli strikes hit the country. Network monitoring by NetBlocks showed national connectivity dropping to roughly 4% of normal levels, while Cloudflare reported traffic falling to effectively zero...
By Security Affairs
News•Feb 27, 2026
How AI Aids Incident Response: Why Humans Alone Cannot Do IR Efficiently
Incident response traditionally relies on manual log correlation, alert validation, and report drafting, consuming 10‑20 minutes per case and often days for complex attacks. AI‑enabled platforms now ingest telemetry from SIEM, EDR, identity, and cloud sources the moment an alert...
By Security Affairs
News•Feb 27, 2026
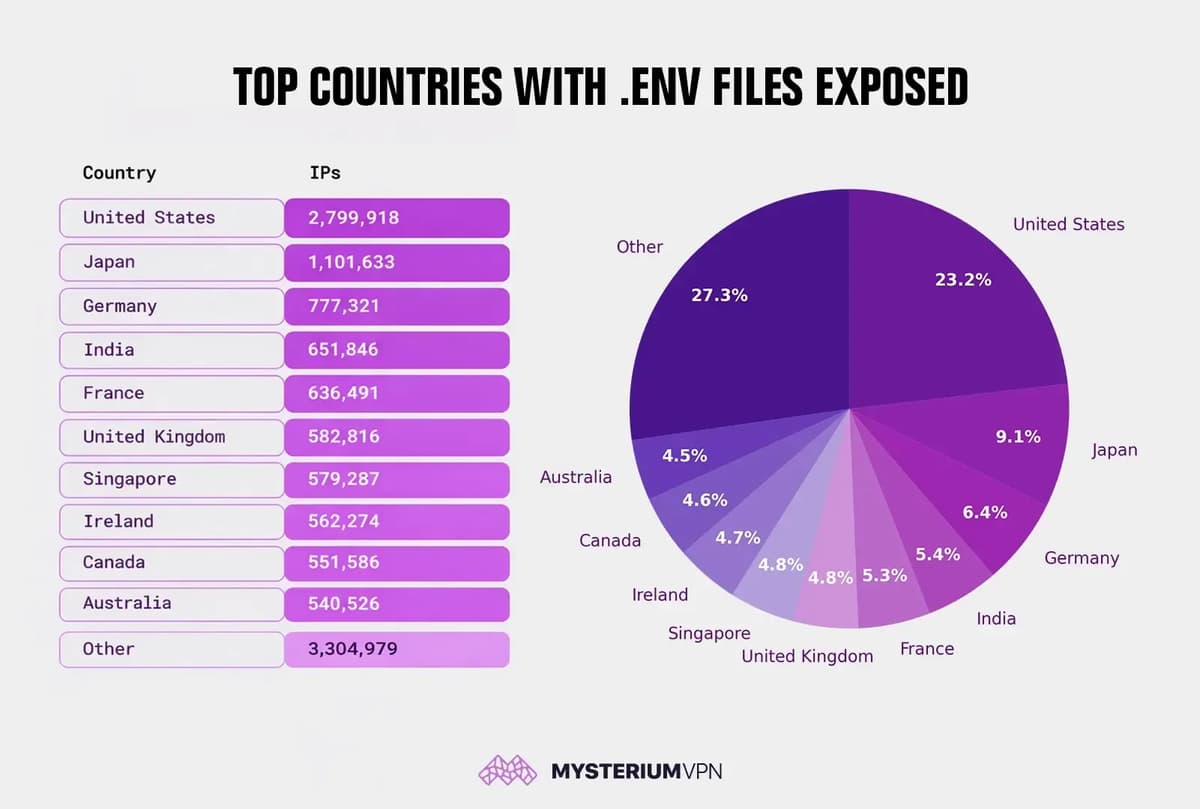
12 Million Exposed .env Files Reveal Widespread Security Failures
Mysterium VPN’s research uncovered more than 12 million IP addresses serving publicly accessible .env‑style files, leaking credentials such as database passwords, API keys, and JWT signing secrets. The United States leads the exposure count with roughly 2.8 million IPs, while Japan, Germany,...
By Security Affairs

News•Feb 24, 2026
SolarWinds Patches Four Critical Serv-U Flaws Enabling Root Access
SolarWinds has issued patches for four critical Serv‑U vulnerabilities (CVE‑2025‑40538, 40539, 40540, 40541), each scoring 9.1 on the CVSS scale. The flaws—broken access control, two type‑confusion bugs, and an IDOR issue—enable remote code execution that can grant attackers full root...
By Security Affairs

News•Feb 24, 2026
VMware Aria Operations Flaws Could Enable Remote Attacks
Broadcom released security updates fixing three critical flaws in VMware Aria Operations, including a remote command injection (CVE-2026-22719) with a CVSS score of 8.1, a stored cross‑site scripting issue (CVE-2026-22720) rated 8.0, and a privilege‑escalation bug (CVE-2026-22721) scored 6.2. The...
By Security Affairs

News•Feb 24, 2026
Operation MacroMaze: APT28 Exploits Webhooks for Covert Data Exfiltration
Operation MacroMaze, a Russia‑linked APT28 campaign, targeted Western and Central European organizations from September 2025 to January 2026. The attackers embedded an INCLUDEPICTURE field in Word documents that fetched a JPG from webhook.site, creating a covert tracking pixel and confirming document opening....
By Security Affairs

News•Feb 22, 2026
SECURITY AFFAIRS MALWARE NEWSLETTER ROUND 85
The Security Affairs Malware Newsletter Round 85 aggregates the latest research and incident reports on global malware threats. Highlights include new Android threats like Ninja Browser, Lumma Infostealer, PromptSpy and Phantom Trojans, a surge in ATM jackpotting across the U.S., and...
By Security Affairs

News•Feb 21, 2026
U.S. CISA Adds RoundCube Webmail Flaws to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added two critical RoundCube Webmail vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog. The flaws—CVE-2025-49113, a deserialization bug with a 9.9 CVSS score, and CVE-2025-68461, an SVG‑based XSS issue scoring 7.2—target...
By Security Affairs

News•Feb 19, 2026
CISA Alerts to Critical Auth Bypass CVE-2026-1670 in Honeywell CCTVs
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued an alert for a critical authentication‑bypass vulnerability (CVE‑2026‑1670) in several Honeywell CCTV models, receiving a CVSS score of 9.8. The flaw lets unauthenticated attackers change the recovery email address, enabling...
By Security Affairs

News•Feb 18, 2026
French Ministry Confirms Data Access to 1.2 Million Bank Accounts
The French Economy Ministry disclosed that a hacker used stolen government credentials to view data from 1.2 million bank accounts across the country. The breach, detected in late January, exposed personal details such as names, addresses, account numbers and, in some...
By Security Affairs

News•Feb 17, 2026
Poorly Crafted Phishing Campaign Leverages Bogus Security Incident Report
A phishing campaign leveraged a fake PDF security incident report hosted on Amazon S3 to intimidate MetaMask users into enabling two‑factor authentication. The PDF, created with ReportLab, contains no malicious code but mimics an official security alert. Researchers noted the...
By Security Affairs

News•Feb 17, 2026
Encrypted RCS Messaging Support Lands in Apple’s iOS 26.4 Developer Build
Apple introduced end‑to‑end encrypted Rich Communication Services (RCS) messaging in the iOS 26.4 developer beta, extending the feature to iPadOS, macOS and watchOS in future updates. The encryption is currently limited to iPhone‑to‑iPhone conversations and depends on carrier support, with a...
By Security Affairs

News•Feb 9, 2026
Critical Fortinet FortiClientEMS Flaw Allows Remote Code Execution
Fortinet disclosed a critical vulnerability (CVE‑2026‑21643) in its FortiClientEMS product, earning a CVSS 9.1 rating. The flaw is an unauthenticated SQL‑injection that allows remote code execution via crafted HTTP requests. Only FortiClientEMS 7.4.4 is affected, and Fortinet recommends upgrading to...
By Security Affairs