
Resecurity Supports Microsoft DCU in Disrupting Fox Tempest ’S Cybercriminal Code-Signing Ecosystem
Microsoft’s Digital Crimes Unit, with Resecurity’s assistance, dismantled Fox Tempest—a malware‑signing‑as‑a‑service that leveraged counterfeit Microsoft code‑signing certificates. On May 19, 2026, the agency seized the signspace.cloud site, shut down hundreds of virtual machines, and revoked more than 1,000 fraudulent certificates. The operation, coordinated with Europol’s EC3 and the FBI, targeted the infrastructure that enabled ransomware groups to present malicious files as trusted software. By cutting off this upstream capability, the disruption hampers the broader ransomware ecosystem.
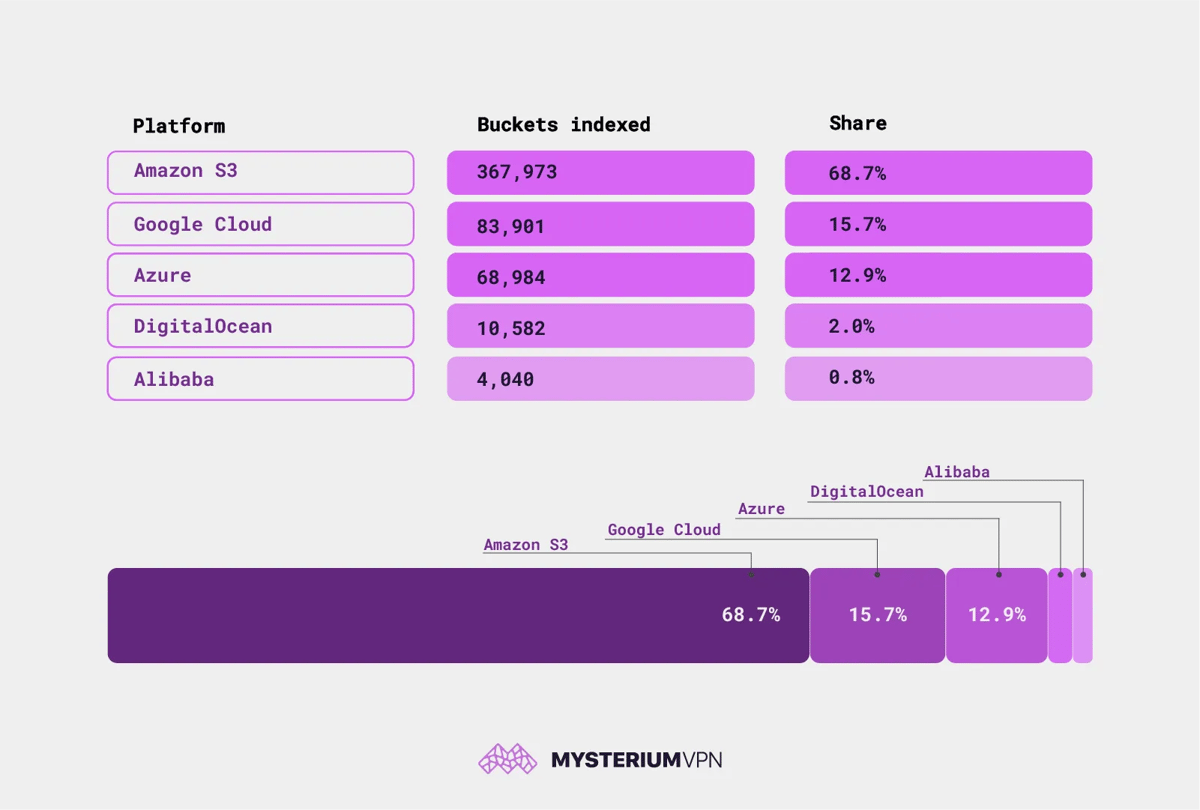
19.6 Billion Files Are Sitting Open on the Internet. No Password Required
Researchers at Mysterium VPN identified 19.6 billion publicly accessible files across 535,480 cloud storage buckets on AWS, Google Cloud, Azure, DigitalOcean and Alibaba. Among them are 685,000 credential files and nearly 1 million database dumps, exposing passwords, API keys and customer data....
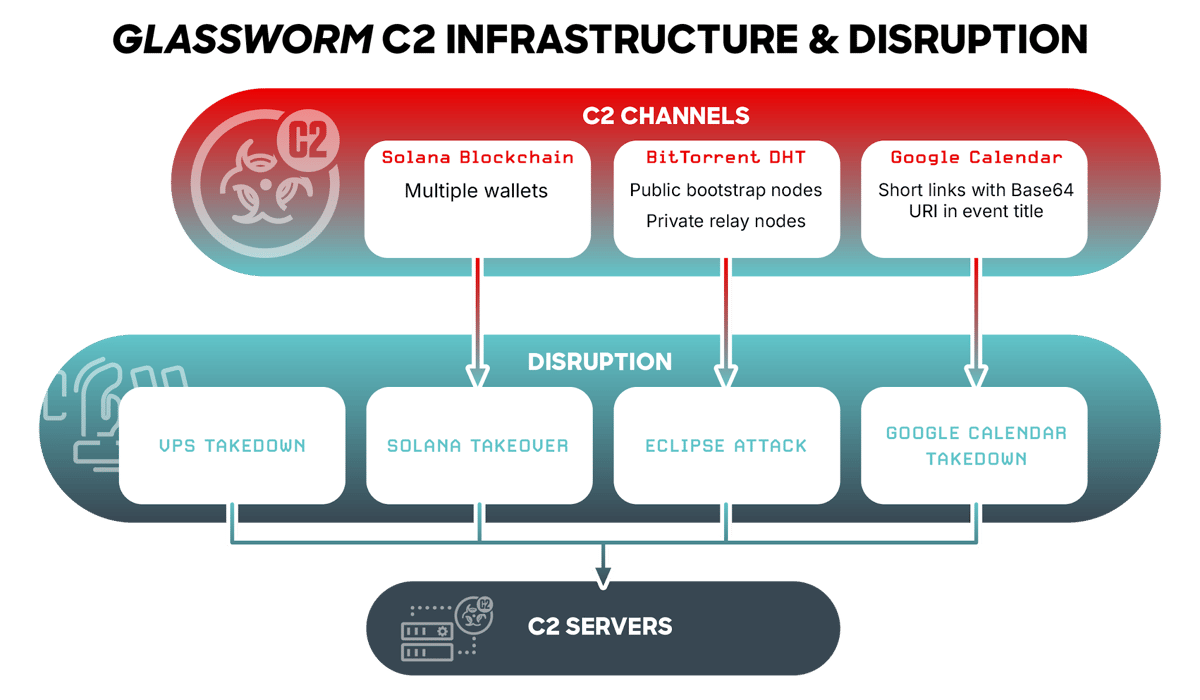
How Cybersecurity Firms Took Down Glassworm Botnet in One Shot
On May 26, 2026, CrowdStrike’s Counter Adversary Operations team, together with Google and the Shadowserver Foundation, simultaneously shut down all four command‑and‑control (C2) channels of the Glassworm botnet. The malware, which has been targeting software developers through poisoned npm packages,...

Third-Party Cyberattack Impacts Patient Information at The Oncology Institute
The Oncology Institute announced that a third‑party software vendor, likely Cognizant‑owned TriZetto, suffered a cyberattack that exposed patient information. The breach, first disclosed in November 2025, was confirmed on May 20, 2026 when Kroll, the vendor’s third‑party administrator, reported unauthorized...

Zero-Click WhatsApp Account Takeover Hits iPhone Users Running iOS 16. No Linked Devices, No Warning
Italian forensic firm Forenser uncovered a zero‑click attack that hijacked WhatsApp accounts on iPhones running iOS 16. The exploit leverages CVE‑2025‑43300 in Apple’s ImageIO framework and CVE‑2025‑55177 in WhatsApp’s sync code to steal session keys without any user interaction. Compromised devices...
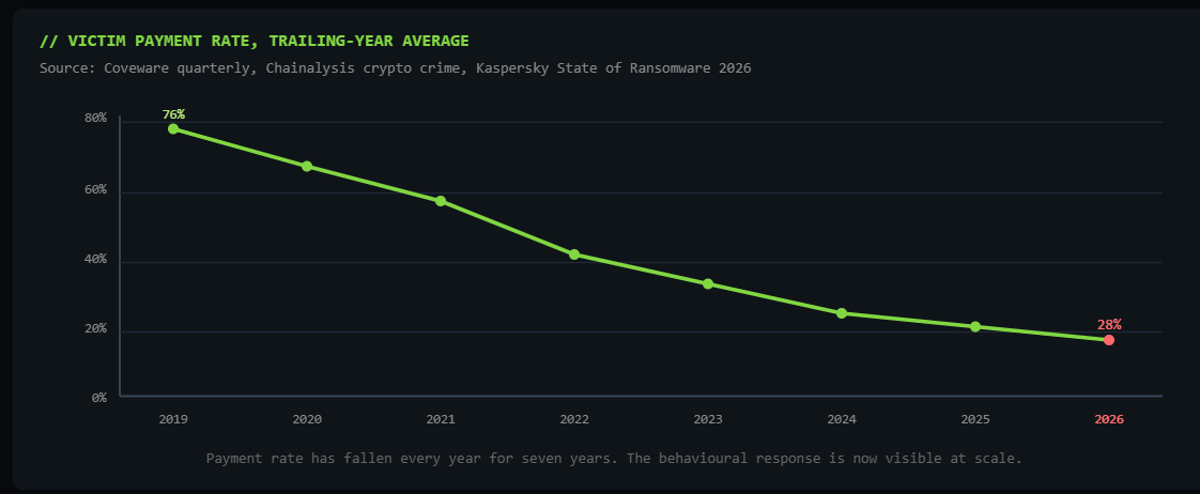
Why Pure Extortion Is Replacing Traditional Ransomware
Ransomware gangs are abandoning encryption in favor of pure data extortion, stealing sensitive information and threatening public leaks. The shift is driven by lower detection risk, faster execution and higher profitability, with payment rates dropping from 76% in 2019 to...
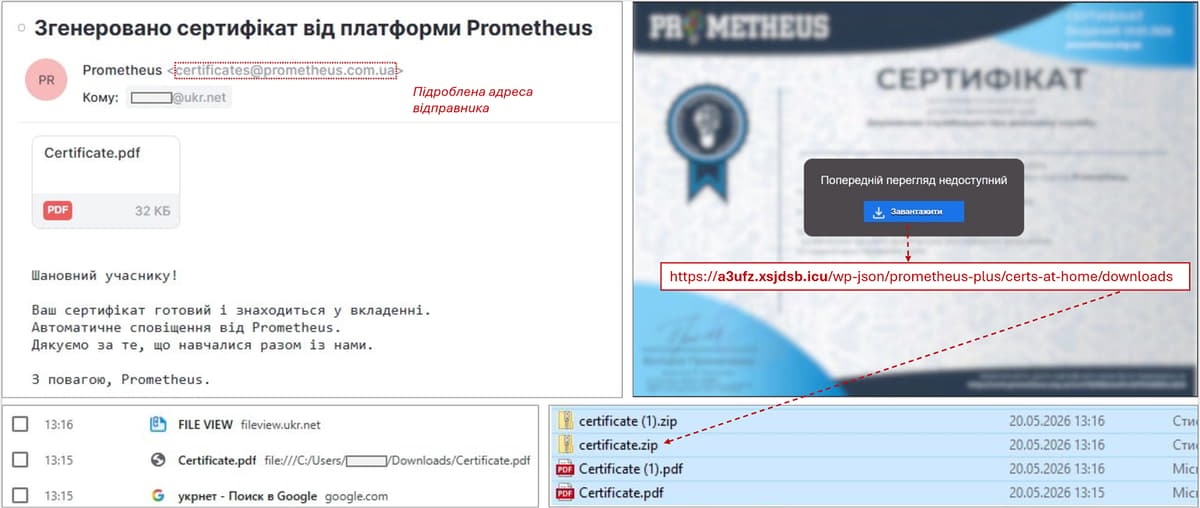
Ghostwriter Is Back, Using a Ukrainian Learning Platform as Bait to Hit Government Targets
Ghostwriter, the Belarus‑linked APT group, has revived a phishing campaign against Ukrainian government agencies by masquerading as the domestic e‑learning platform Prometheus. The emails, sent from compromised accounts, contain PDF attachments that lead to a ZIP file with a JavaScript...
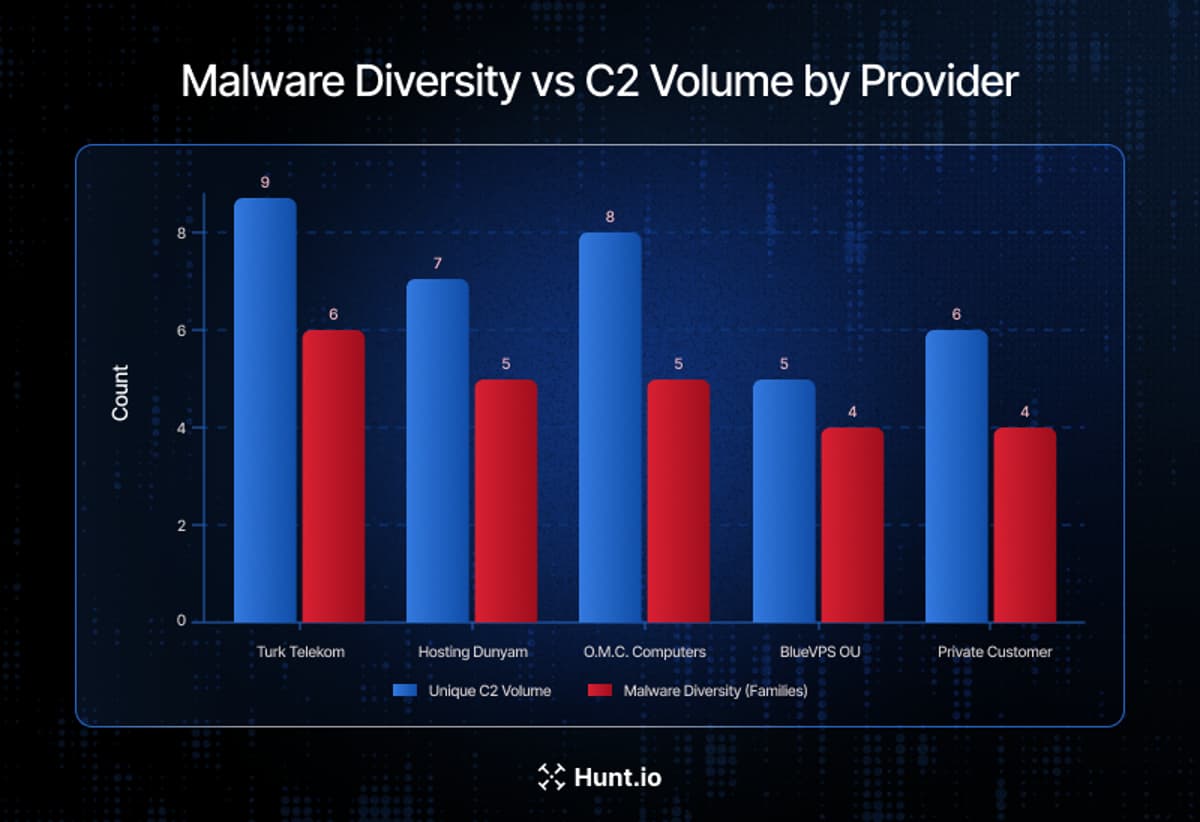
One Telecom Provider Hosted Most of the Middle East ’S Active C2 Infrastructure
Hunt.io’s three‑month survey of Middle East malicious infrastructure uncovered more than 1,350 command‑and‑control (C2) servers across 98 hosting providers in 14 countries. Saudi Telecom Company (STC) alone accounted for 981 servers, representing 72.4% of the region’s observed C2 activity. The...

U.S. CISA Adds Microsoft and Adobe Flaws to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added seven known‑exploited vulnerabilities to its KEV catalog, covering legacy Microsoft Windows, DirectX, Internet Explorer, Defender, and an Adobe Acrobat flaw. The list includes critical CVSS scores up to 9.8, such...
PinTheft: Another Linux Privilege Escalation, Another Working Exploit, This Time Targeting Arch
PinTheft is a newly disclosed Linux local privilege escalation flaw in the kernel’s RDS (Reliable Datagram Sockets) subsystem that leverages a zerocopy double‑free to overwrite the page cache and obtain root privileges. The vulnerability requires the RDS module, io_uring, a...

Microsoft Issues YellowKey Mitigation, No Patch Yet
Microsoft has acknowledged the YellowKey vulnerability (CVE‑2026‑45585), a BitLocker bypass affecting Windows 11 24H2, 25H2, 26H1 and Windows Server 2025 on x64 platforms. The flaw exploits the autofstx.exe component in the Windows Recovery Environment to launch an unrestricted shell after...

Alleged Huawei Zero-Day Blamed for the 2025 Luxembourg Telecom Crash
A previously unknown vulnerability in Huawei enterprise routers caused Luxembourg's nationwide telecom outage on July 23, 2025. Attackers sent specially crafted traffic that forced the devices into continuous reboot loops, taking down landline, 4G, 5G and emergency services for over...

Drupal Is Rolling Out an Emergency Security Update on May 20. You Cannot Miss It
The Drupal Security Team will issue an emergency core update on May 20 between 17:00‑21:00 UTC for all supported branches. The advisory warns that exploits could appear within hours, urging administrators to reserve time for immediate patching. Patches cover branches 11.3.x, 11.2.x,...
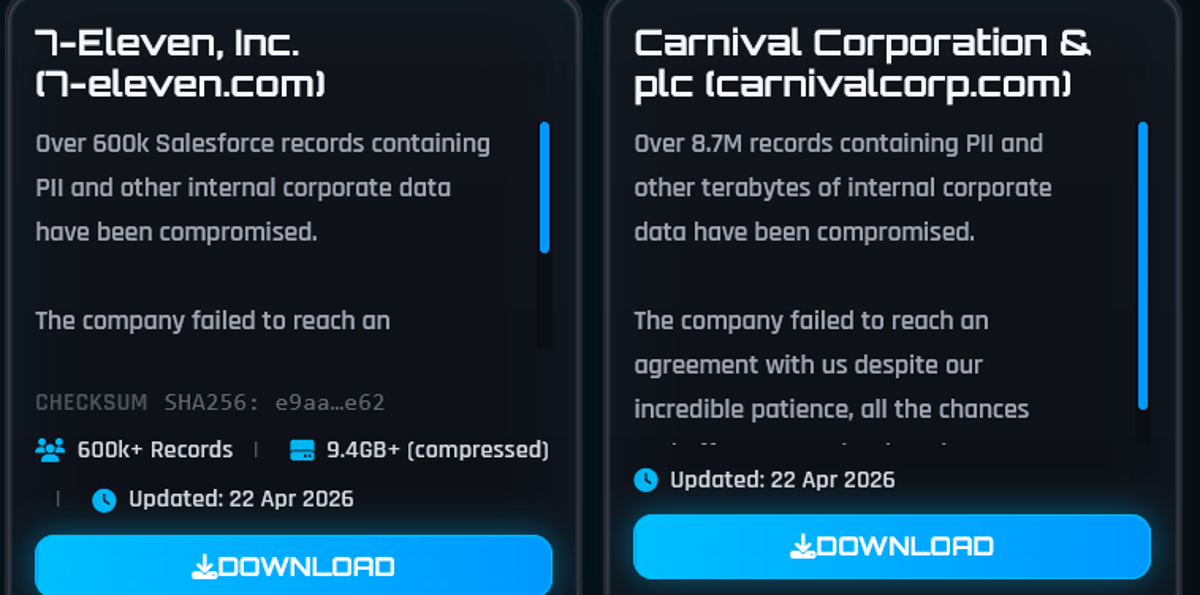
ShinyHunters Hack 7-Eleven: Franchisee Data and Salesforce Records Exposed
7‑Eleven disclosed a data breach after the ShinyHunters group claimed theft of over 600,000 Salesforce records and franchisee application files. The unauthorized access occurred on April 8, 2026, and the hackers threatened to publish the data unless a ransom was paid by...

CVE-2026-42897: Microsoft Confirms Active Exploitation of Exchange Server Zero-Day
Microsoft confirmed that attackers are actively exploiting a new Exchange Server zero‑day, CVE‑2026‑42897, with a CVSS rating of 8.1. The flaw is a cross‑site scripting issue affecting Outlook Web Access, allowing spoofing via malicious JavaScript embedded in crafted emails. Microsoft...