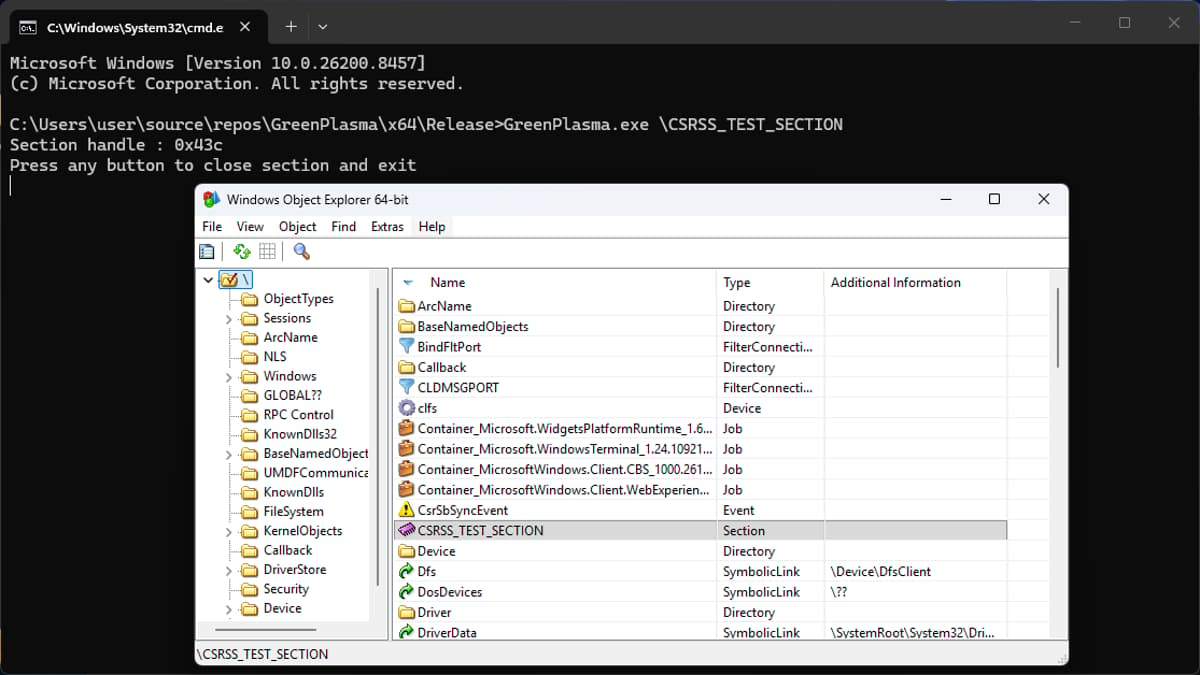
Researchers Uncover YellowKey and GreenPlasma Windows Zero-Days
Security researcher Chaotic Eclipse disclosed two fresh Windows zero‑days, YellowKey and GreenPlasma. YellowKey lets attackers with physical access bypass BitLocker on Windows 11 and Windows Server 2022/2025 by planting crafted files in the WinRE image. GreenPlasma targets the CTFMON framework, enabling privilege escalation to SYSTEM level on the same OS versions. Microsoft has only patched a prior Defender flaw; both new vulnerabilities remain unpatched.

U.S. CISA Adds a Flaw in Cisco Catalyst SD-WAN to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added Cisco Catalyst SD‑WAN vulnerability CVE‑2026‑20182 to its Known Exploited Vulnerabilities (KEV) catalog. The flaw, rated a perfect 10.0 on the CVSS scale, lets an unauthenticated remote attacker bypass peering authentication,...
Broadcom Releases VMware Fusion Security Update for Root Access Bug
Broadcom has issued a security update for VMware Fusion that fixes a high‑severity TOCTOU flaw (CVE‑2026‑41702). The vulnerability allowed a local, non‑administrative user to elevate privileges to root on macOS systems running Fusion. The patch arrives as Broadcom participates in...

NGINX Rift: An 18-Year-Old Flaw in the World’s Most Deployed Web Server Just Came to Light
Security researchers at depthfirst disclosed NGINX Rift (CVE‑2026‑42945), a critical heap buffer overflow that has existed in the NGINX codebase for 18 years. The flaw lives in the ngx_http_rewrite_module and can be triggered by a common rewrite pattern that mixes...
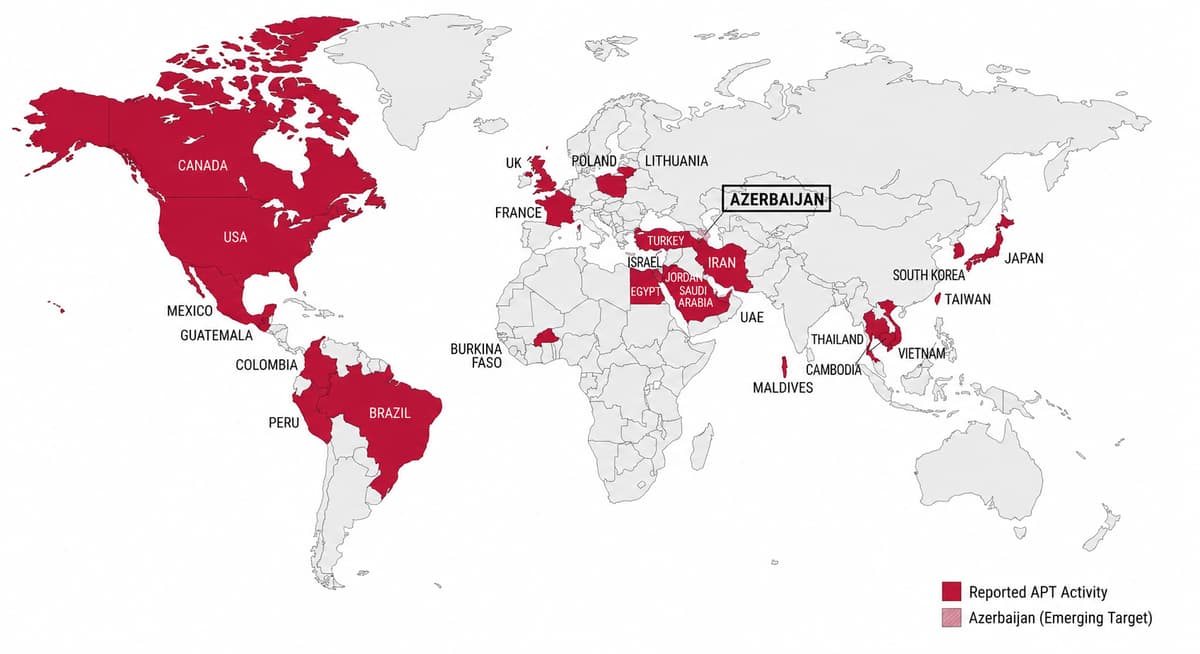
FamousSparrow Targets Azerbaijani Energy Sector in Multi-Wave Espionage Campaign
Chinese‑linked APT group FamousSparrow launched three intrusion waves against an Azerbaijani oil and gas firm from Dec 2025 to Feb 2026, repeatedly exploiting a vulnerable Microsoft Exchange server via the ProxyNotShell chain. The campaign deployed evolving payloads—Deed RAT, an attempted Terndoor backdoor,...

OpenLoop Health Confirms January 2026 Data Breach Affecting 716,000
OpenLoop Health, a telehealth infrastructure provider, confirmed a cyberattack in early January 2026 that exposed personal information of 716,000 individuals. The intrusion lasted from January 7 to 8, during which threat actors exfiltrated data but did not access electronic health...

Quest KACE SMA Flaw CVE-2025-32975: When One Unpatched Tool Opens the Door to 60 Organizations
Quest KACE Systems Management Appliance (SMA) suffers a critical authentication‑bypass flaw (CVE‑2025‑32975) rated CVSS 10.0. The vulnerability lets an unauthenticated attacker impersonate any user, including administrators, via the SSO module. Although a patch was issued in May 2025, more than 12,000...
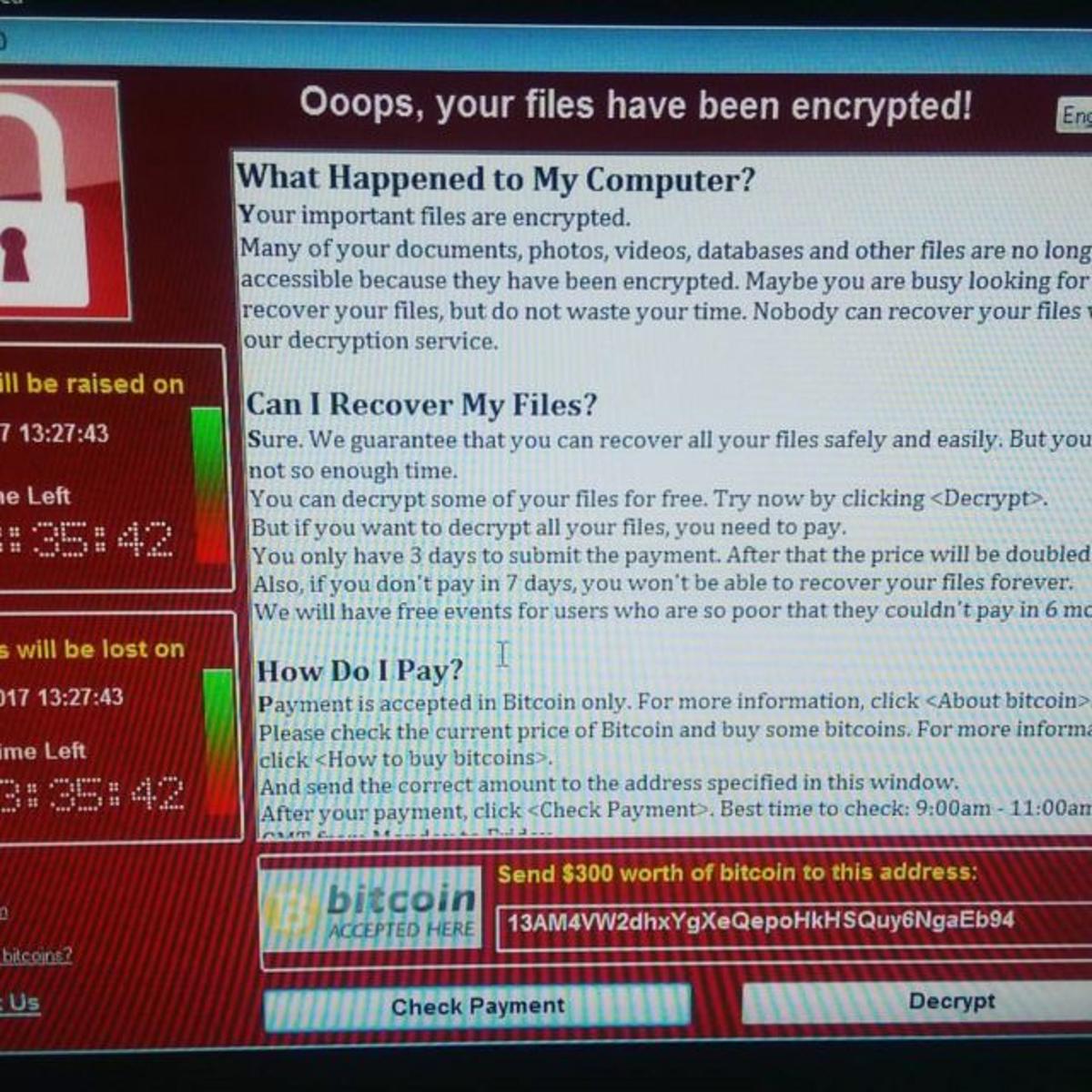
WannaCry, the Ransomware Attack that Changed the History of Cybersecurity
On May 12, 2017, the WannaCry ransomware leveraged the NSA‑derived EternalBlue exploit (CVE‑2017‑0144) to spread as a worm across Windows networks. Within hours it infected more than 200,000 computers in over 150 countries, crippling hospitals, telecoms and other critical infrastructure....

Google Warns Artificial Intelligence Is Accelerating Cyberattacks and Zero-Day Exploits
Google Cloud Threat Intelligence released a report warning that attackers are now leveraging artificial intelligence to accelerate cyber‑attacks, including the creation of AI‑generated zero‑day exploits. The research shows a clear shift from credential‑theft tactics to targeting software flaws, cloud APIs,...

Crimenetwork Returns After Takedown, Dismantled Again by German Authorities
German police dismantled a revived version of the German‑language cybercrime marketplace Crimenetwork, which had amassed more than 22,000 users and over 100 sellers. The site generated over €3.6 million (≈$3.9 million) in revenue before being shut down, and authorities seized €194,000 (≈$210,000)...

U.S. CISA Adds a Flaw in BerriAI LiteLLM to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the critical LiteLLM flaw (CVE‑2026‑42208, CVSS 9.3) to its Known Exploited Vulnerabilities catalog. Attackers began exploiting the SQL‑injection bug within 36 hours of disclosure, targeting the proxy’s database tables that store API...

AI, Cyberwarfare, and Autonomous Weapons: Inside America’s New Military Strategy
The Pentagon has formalized partnerships with OpenAI, Google, Microsoft, Amazon and SpaceX to embed advanced generative‑AI models into classified networks, launching an "AI‑first" military doctrine. More than 1.3 million Department of Defense personnel now operate on the GenAI.mil platform, accelerating intelligence,...

U.S. CISA Adds a Flaw in Palo Alto Networks PAN-OS to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has placed Palo Alto Networks' PAN-OS vulnerability CVE‑2026‑0300 into its Known Exploited Vulnerabilities (KEV) catalog. The flaw is a high‑severity (CVSS 9.3) buffer overflow in the User‑ID Authentication Portal that permits unauthenticated...
Iranian Cyber Espionage Disguised as a Chaos Ransomware Attack
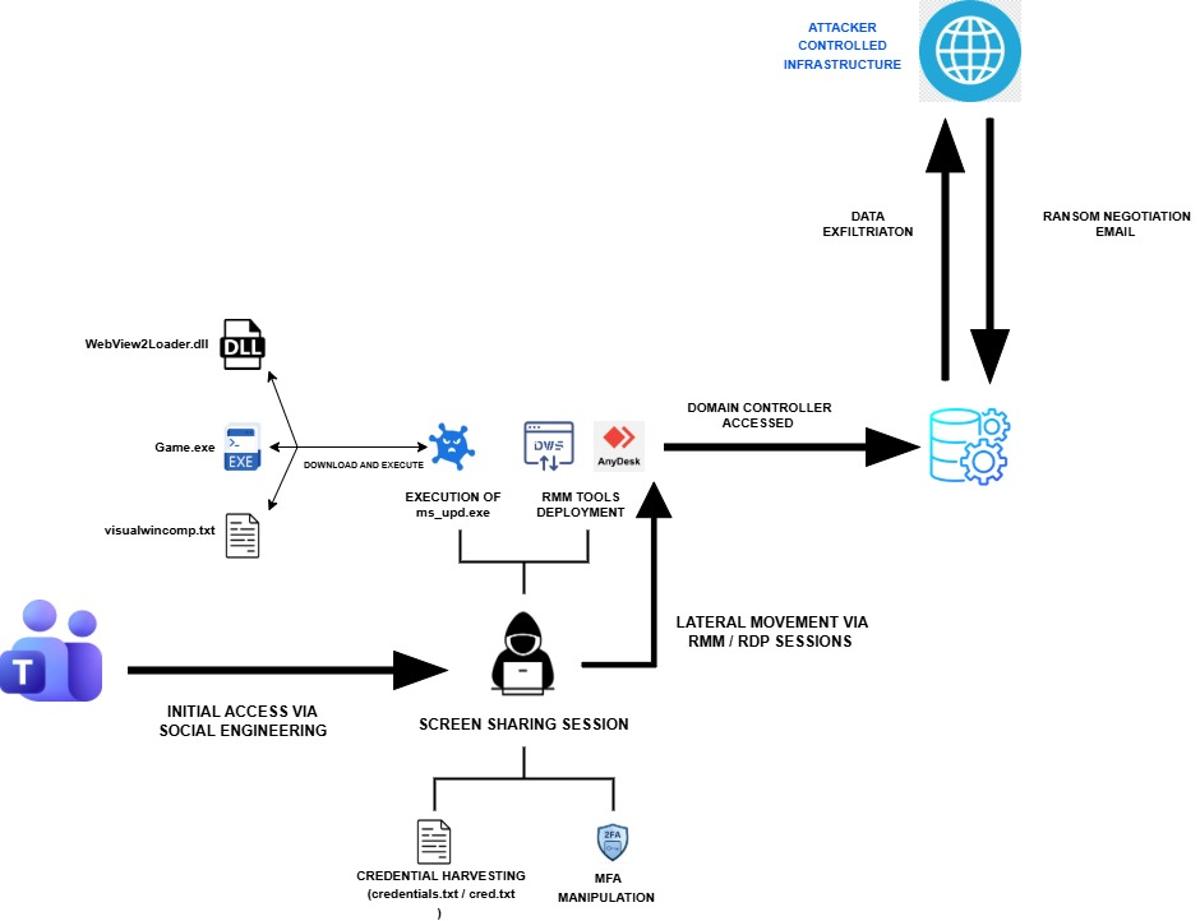
Rapid7 uncovered an Iran‑linked MuddyWater intrusion that masqueraded as a Chaos ransomware attack, but no encryption occurred. The group used Microsoft Teams phishing, remote tools such as AnyDesk and DWAgent, and extortion emails to disguise a pure espionage operation. Credential...
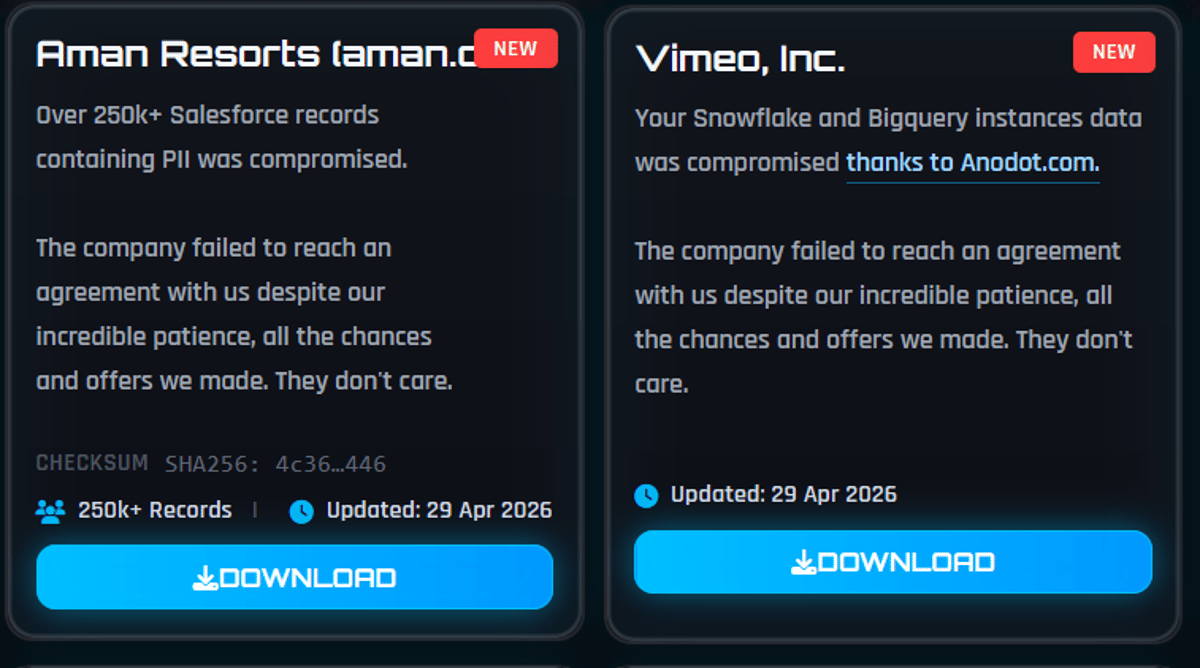
Vimeo Confirms Breach via Third-Party Vendor Impacts 119K Users
Vimeo disclosed that the ShinyHunters cybercrime group accessed data belonging to about 119,000 users in April 2026. The breach stemmed from a compromise of Anodot, a third‑party analytics provider integrated with Vimeo’s platform. Exfiltrated information included email addresses, video titles,...
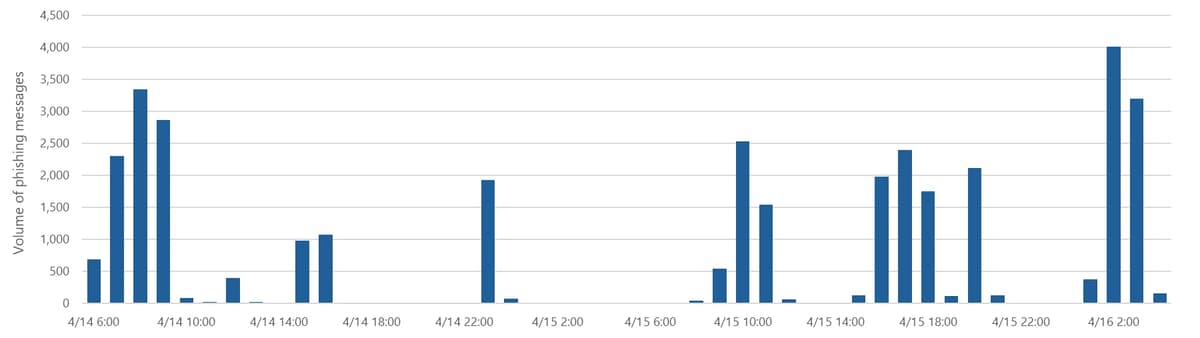
Microsoft Warns of Global Campaign Stealing Auth Tokens From 35K Users
Microsoft disclosed a multi‑stage phishing campaign that compromised authentication tokens for more than 35,000 users in 26 countries, with 92% of victims located in the United States, especially in healthcare and finance. The attackers sent polished “code‑of‑conduct” emails through a...

U.S. CISA Adds a Flaw in Linux Kernel to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added Linux kernel flaw CVE-2026-31431, dubbed “Copy Fail,” to its Known Exploited Vulnerabilities (KEV) catalog. The vulnerability scores 7.8 on the CVSS scale and enables an unprivileged local user to write...
Salt Typhoon Breach IBM Subsidiary in Italy: A Warning for Europe’s Digital Defenses
In late April 2026, IBM Italy’s wholly‑owned subsidiary Sistemi Informativi suffered a cyber breach that authorities suspect was carried out by the China‑linked APT group Salt Typhoon. The firm provides IT infrastructure services to numerous Italian public agencies, making the outage...

U.S. CISA Adds a Flaw in WebPros cPanel to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added the critical cPanel authentication‑bypass flaw (CVE‑2026‑41940, CVSS 9.3) to its Known Exploited Vulnerabilities (KEV) catalog. The vulnerability affects cPanel/WHM versions after 11.40 and allows attackers to bypass login checks, potentially...

SonicWall Patches Three SonicOS Flaws in Gen 6, 7 and 8 Firewalls. Patch Them Now
SonicWall has issued urgent firmware updates to remediate three SonicOS vulnerabilities affecting its Gen 6, 7 and 8 firewalls. The flaws – CVE‑2026‑0204 (high severity, CVSS 8.0) and two medium‑severity issues CVE‑2026‑0205 and CVE‑2026‑0206 (both CVSS 6.8) – could let attackers bypass controls,...

U.S. CISA Adds Microsoft Windows Shell and ConnectWise ScreenConnect Flaws to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added two new flaws to its Known Exploited Vulnerabilities (KEV) catalog: a high‑severity path‑traversal issue in ConnectWise ScreenConnect (CVE‑2024‑1708) and a lower‑severity Windows Shell spoofing flaw (CVE‑2026‑32202). The ConnectWise bug scores...
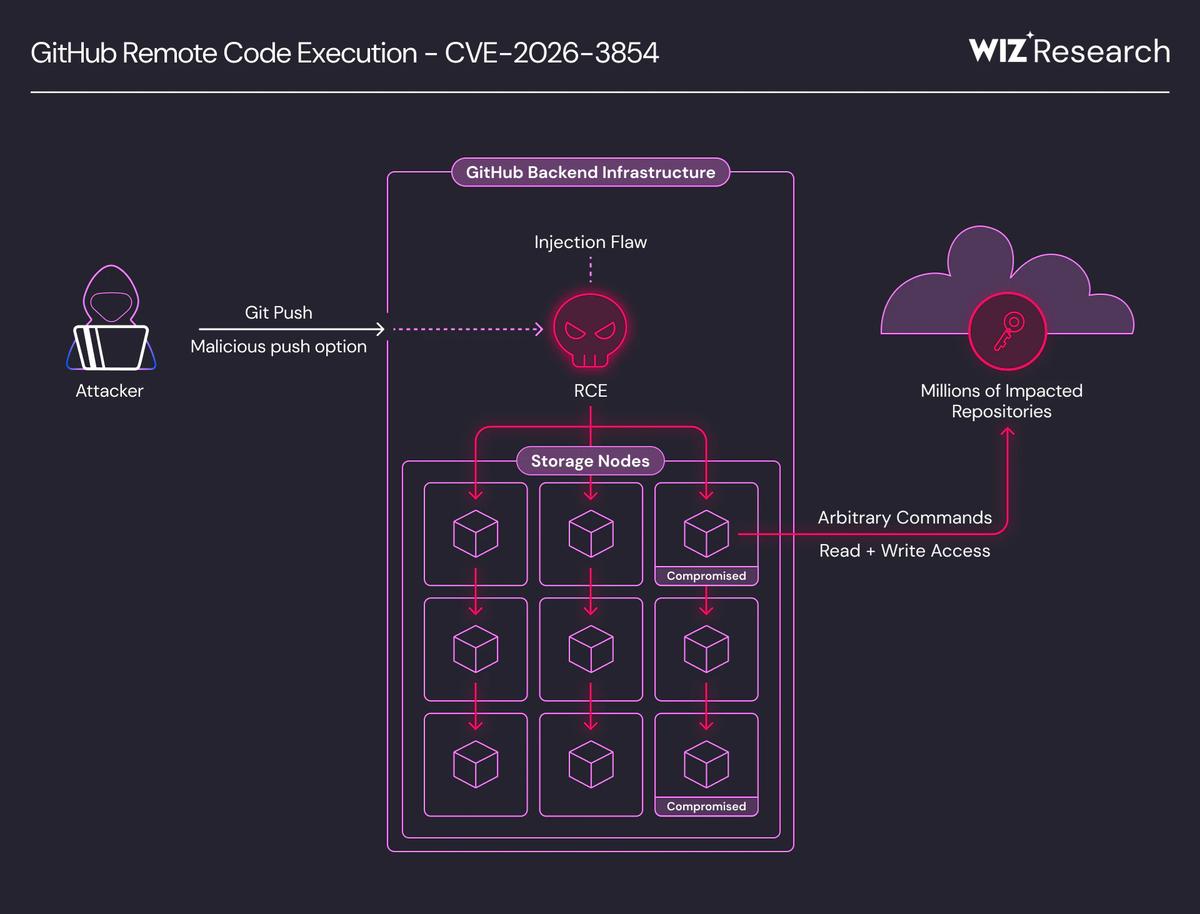
CVE-2026-3854 GitHub Flaw Enables Remote Code Execution
Researchers disclosed a critical GitHub vulnerability, CVE‑2026‑3854, that enables remote code execution through a single git push. The bug stems from unsanitized push‑option values that are embedded in internal service headers, allowing command injection across GitHub Enterprise Cloud, Enterprise Server,...

Medtronic Discloses Security Incident After ShinyHunters Claimed Theft of 9M+ Records
Medtronic confirmed a cyberattack on its corporate IT systems after hacker group ShinyHunters claimed to have stolen more than 9 million records. The breach was limited to internal corporate networks and did not affect product safety, manufacturing, or patient care. Medtronic...

LINKEDIN BROWSERGATE
Fairlinked’s BrowserGate investigation reveals that LinkedIn embeds a 2.7 MB JavaScript bundle that silently fingerprints every visitor and scans installed Chrome extensions. The system, named APFC/DNA, collects 48 browser characteristics and probes a hard‑coded list that grew from 5,459 to 6,167...

Fast16: Pre-Stuxnet Malware that Targeted Precision Engineering Software
SentinelOne uncovered Fast16, a sabotage‑oriented malware first seen in 2005 that predates Stuxnet by at least five years. The code embeds a Lua virtual machine, uses an encrypted carrier (svcmgmt.exe) and a kernel driver (fast16.sys) to stealthily modify floating‑point calculations...
Italy Moves to Extradite Chinese National to the U.S. over Hacking Charges
Italy’s courts have approved the extradition of Chinese national Xu Zewei, arrested at Milan’s Malpensa Airport in July 2025, to the United States on cyber‑espionage charges. U.S. prosecutors allege Xu participated in the state‑backed Hafnium (aka Silk Typhoon) campaign that stole...

Critical Bug in CrowdStrike LogScale Let Attackers Access Files
CrowdStrike disclosed a critical vulnerability (CVE‑2026‑40050) in its self‑hosted LogScale product that enables unauthenticated path‑traversal file reads. The flaw affects specific LogScale cluster API endpoints and requires customers to upgrade to a patched version immediately. SaaS LogScale users were protected...

SECURITY AFFAIRS MALWARE NEWSLETTER ROUND 94
The Security Affairs Malware Newsletter Round 94 aggregates the most consequential malware developments from the past month. Highlights include the Morpheus spyware linked to IPS Intelligence, the DarkSword and Coruna iOS exploits that erode iPhone defenses, and the Lotus Wiper targeting...

Signal Phishing Campaign Targets Germany’s Bundestag President Julia Klöckner
Germany’s Bundestag President Julia Klöckner was compromised in a Signal phishing attack that used a fake CDU group chat. Attackers tricked her into revealing her PIN and verification code, bypassing Signal’s encryption without breaking the protocol. The incident follows earlier warnings...

RAMP Uncovered: Anatomy of Russia’s Ransomware Marketplace
A leaked MySQL dump from Russia’s RAMP forum reveals a sophisticated ransomware marketplace that operated from November 2021 to January 2024. The data shows 7,707 registered users, 1,732 threads, over 340,000 IP logs, and thousands of private messages coordinating sales of network...

U.S. CISA Adds a Flaw in Microsoft Defender to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added Microsoft Defender vulnerability CVE‑2026‑33825 to its Known Exploited Vulnerabilities (KEV) catalog. The flaw, rated 7.8 on the CVSS scale, enables privilege escalation and was patched in Microsoft’s April 2026 Patch Tuesday. Huntress reported...

Microsoft Out-of-Band Updates Fixed Critical ASP.NET Core Privilege Escalation Flaw
Microsoft released out‑of‑band updates to fix a critical ASP.NET Core vulnerability (CVE‑2026‑40372) with a CVSS score of 9.1. The flaw, present in versions 10.0.0‑10.0.6, allowed attackers to forge data‑protection tokens and elevate privileges to SYSTEM level on non‑Windows hosts. The...

AI Model Claude Opus Turns Bugs Into Exploits for Just $2,283
Anthropic's Claude Opus 4.6 model produced a functional Chrome V8 exploit after processing 2.3 billion tokens across 1,765 API calls, costing roughly $2,283. The experiment demonstrated that publicly accessible AI can turn software patches into weaponized code with modest investment. Researchers...

U.S. CISA Adds a Flaw in Apache ActiveMQ to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added Apache ActiveMQ’s critical CVE‑2026‑34197 to its Known Exploited Vulnerabilities (KEV) catalog. The flaw, scoring 8.8 on the CVSS scale, lets an authenticated attacker exploit the Jolokia JMX‑HTTP bridge to load a...

Sweden Reports Cyberattack Attempt on Heating Plant Amid Rising Energy Threats
Sweden’s civil defense ministry confirmed that a pro‑Russian group attempted a cyberattack on a western heating plant in 2025, but the intrusion was stopped. The operation is tied to Russian intelligence and mirrors a wave of sabotage that has hit...

U.S. CISA Adds Microsoft SharePoint Server, and Microsoft Office Excel Flaws to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added two Microsoft flaws to its Known Exploited Vulnerabilities (KEV) catalog: CVE‑2009‑0238, a remote‑code‑execution bug in Excel, and CVE‑2026‑32201, a spoofing/XSS issue in SharePoint Server. The Excel vulnerability carries a CVSS...

PHP Composer Flaws Enable Remote Command Execution via Perforce VCS
Two high‑severity command‑injection flaws were discovered in PHP Composer’s Perforce VCS driver (CVE‑2026‑40176 and CVE‑2026‑40261). The vulnerabilities allow attackers to inject shell commands via malicious composer.json files or crafted source references, potentially executing code with the user’s privileges. Composer versions...

Iran-Linked Group Handala Claims to Have Breached Three Major UAE Organizations
Handala, an Iran‑linked hacktivist group believed to be a front for Void Manticore, claimed a massive cyberattack on three UAE agencies—Dubai Courts, Dubai Land Department, and Dubai Roads & Transport Authority. The group alleges it destroyed six petabytes of data...

CPUID Watering Hole Attack Spreads STX RAT Malware
Threat actors compromised the CPUID website between April 9‑10, 2026, swapping legitimate CPU‑Z and HWMonitor download links with malicious installers for roughly six hours. The trojanized files contained a malicious DLL that used DLL sideloading to deliver the STX remote‑access trojan,...

Hackers Claim Control over Venice San Marco Anti-Flood Pumps
Hackers claiming to be the "Infrastructure Destruction Squad" breached the operational technology controlling Venice’s San Marco flood‑gate system in late March, asserting they could disable defenses and flood the historic piazza. The group posted screenshots of control panels on Telegram...

Ransomware Attack on ChipSoft Knocks EHR Services Offline Across Hospitals in the Netherlands and Belgium
Dutch health‑IT firm ChipSoft confirmed a ransomware breach on April 7 that forced its flagship HiX electronic health‑record platform offline in the Netherlands and Belgium. The attack prompted the Dutch CERT (Z‑CERT) to shut down patient portals, HiX Mobile and the...

The Alleged Breach of China’s National Supercomputing Center Can Have Serious Geopolitical Consequences
A hacker group called FlamingChina claims to have exfiltrated more than 10 petabytes of classified military, aerospace and scientific data from China’s National Supercomputing Center in Tianjin. The breach allegedly lasted six months, using a compromised VPN and a botnet to...

Internet-Exposed ICS Devices Raise Alarm for Critical Sectors
A recent comparative study scanned the internet for Modbus‑exposed industrial control system (ICS) devices and identified 179 likely live units, with the United States accounting for 57 of them. The research highlights that many of these devices run legacy protocols...

Major Outage Cripples Russian Banking Apps and Metro Payments Nationwide
A widespread technical failure on April 3 crippled the mobile and ATM services of Russia’s largest banks, including Sberbank, VTB, Alfa‑Bank, T‑Bank and Gazprombank. Customers across major regions were unable to make card payments, withdraw cash or access mobile banking for...

GPUBreach Exploit Uses GPU Memory Bit-Flips to Achieve Full System Takeover
Researchers unveiled GPUBreach, a novel GPU Rowhammer attack that flips bits in GDDR6 memory to corrupt GPU page tables and achieve full system compromise. By chaining arbitrary GPU memory reads/writes with driver‑level bugs, an unprivileged CUDA kernel can elevate privileges...

U.S. CISA Adds a Flaw in Fortinet FortiClient EMS to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added Fortinet FortiClient EMS vulnerability CVE-2026-35616 to its Known Exploited Vulnerabilities (KEV) catalog. The flaw, rated 9.1 on the CVSS scale, enables unauthenticated attackers to bypass authentication via an API and...

Attackers Exploit RCE Flaw as 14,000 F5 BIG-IP APM Instances Remain Exposed
Shadowserver reports that more than 14,000 F5 BIG‑IP Access Policy Manager (APM) instances remain publicly reachable, and attackers are actively exploiting the newly‑re‑classified critical remote code execution flaw CVE‑2025‑53521. The vulnerability, now scored 9.8 on the CVSS v3.1 scale, allows...

SECURITY AFFAIRS MALWARE NEWSLETTER ROUND 91
The Security Affairs Malware Newsletter Round 91 aggregates the latest high‑impact malware research, spotlighting a new macOS infostealer called Infiniti that leverages ClickFix and Python/Nuitka, and a WebSocket‑based pivoting implant named RoadK1ll. It also details a series of supply‑chain compromises of...

SentinelOne Autonomous Detection Blocks Trojaned LiteLLM Triggered by Claude Code
SentinelOne’s AI‑driven endpoint platform automatically detected and halted a supply‑chain attack that leveraged a compromised LiteLLM package. The malicious chain was triggered after an AI coding assistant installed the tainted library, leading to hidden Python code execution, data theft and...

Free VPNs Leak Your Data While Claiming Privacy
Recent research by MysteriumVPN examined 18 of the most downloaded free Android VPN apps and found pervasive privacy violations. Nearly all apps embed multiple third‑party trackers and request dangerous permissions unrelated to VPN functionality, while many connect to hard‑coded servers...