
Agentic AI Governance: How to Approach It
Agentic AI agents are now in production at roughly 70% of enterprises, creating a hidden layer of "identity dark matter" that traditional IAM tools cannot see or control. Existing identity providers struggle to enforce runtime policies for these autonomous, short‑lived agents, leaving them over‑privileged and unmanaged. Strata proposes an identity control plane—its AI Identity Gateway—that injects per‑task, five‑second tokens, provides vendor‑neutral enforcement, and logs full delegation chains without changing upstream services. With the EU AI Act enforcement slated for August 2026 and fines up to $38 million, treating agentic identity as a first‑class security concern is becoming a regulatory imperative.

Key Leaks, Vault Failures, and TEE Attacks: Highlights From RWC 2026
GitGuardian presented at the Real World Cryptography Symposium 2026, revealing that 945,560 private keys have leaked in the wild, compromising 139,767 certificates. The team also demonstrated 27 attacks that break the zero‑knowledge promises of four leading password managers and showcased...

5 AWS AI Controls Every Security Team Should Have
AWS now offers organization‑wide controls that let security teams govern AI workloads beyond the application layer. Five key mechanisms—MCP server access blocks, Bedrock policy guardrails, model‑specific SCP denies, service‑wide SCP disables, and long‑term Bedrock API‑key restrictions—can be applied uniformly across...

48 Hours: The Window Between Infostealer Infection and Dark Web Sale
Whiteintel researchers mapped the full infostealer lifecycle and found that stolen corporate credentials appear on dark‑web marketplaces within 48 hours of infection, often much sooner. The five‑stage process—infection, harvest, packaging, marketplace listing, and exploitation—compresses credential theft into a window far...

Inventors of Quantum Cryptography Win Turing Award
Charles Bennett and Gilles Brassard have been awarded the 2026 ACM A.M. Turing Award for inventing quantum cryptography, specifically the BB84 quantum key distribution protocol. Bruce Schneier, while applauding the scientific breakthrough, reiterates his long‑standing view that the technology offers...

Change Intelligence and Deployment Connectors for Liquibase Secure
Liquibase Secure announced two new capabilities—Change Intelligence and Deployment Connectors for ServiceNow, GitHub, Harness, and Terraform. Change Intelligence aggregates change data, applies AI‑driven risk analysis, and automatically captures audit evidence in a single view. Deployment Connectors embed governed database change...

Let’s Stop Sovereignty Washing
The article warns that cloud providers are marketing “sovereignty” while delivering only data residency, creating a gap between promises and technical reality. It explains that U.S. laws such as the CLOUD Act can compel access to data stored in Europe,...

California Gets Serious About Regulation (Again)
Effective Jan 1 2026, California expanded its CCPA/CPRA into a unified governance framework that blends privacy, cybersecurity, and AI regulations. The new rules mandate formal risk assessments for high‑risk processing, regulate automated decision‑making technologies, and require independent cybersecurity audits. Obligations roll out...

What Makes Browser Hijacking a Silent Threat?
Browser hijacking, where attackers covertly alter browser settings or install malicious extensions, is emerging as a silent threat to enterprises. Researchers have identified 33 rogue extensions affecting over 2.6 million users, and Microsoft reported a 111 % surge in token‑replay attacks in...

The EU CRA – Treating Cybersecurity as Product Liability
The EU’s Cyber Resilience Act (CRA) moves cybersecurity from post‑incident tort claims to product‑level liability, obligating manufacturers, importers and distributors to ensure devices are secure by design, supported and able to report vulnerabilities. The regulation, which entered force on Dec 10 2024,...

FIFA World Cup 2026: A Match Between Fans and Scammers
As the FIFA World Cup 2026 approaches, a NordVPN survey reveals that 11% of American internet users have already encountered soccer‑related scams. Betting fraud (46%) and counterfeit ticket offers (44%) are the most common schemes, proliferating on platforms such as...

The Hidden Tracking Risk Inside Your Tires
In this episode of the Shared Security Podcast, hosts Tom and co‑host Scott Wright explore the privacy risks posed by tire pressure monitoring systems (TPMS). They discuss a recent study by Spain’s IMDEA institute that captured 6 million wireless signals from...

Microsoft’s March Security Update of High-Risk Vulnerability Notice for Multiple Products
Microsoft issued its March 2026 security update, fixing 83 vulnerabilities across Windows, Office, SQL Server, Azure and other core products. The bulletin includes eight critical and 75 important flaws, notably remote‑code‑execution bugs in Office (CVE‑2026‑26110, CVE‑2026‑26113) and the Print Spooler service...

Attribute-Based Access Control for AI Capability Negotiation
The article provides a practical guide for users and developers to disconnect from Apple Single Sign‑On (SSO) and replace it with enterprise‑grade identity solutions. It details the UI steps for consumers, explains why SaaS firms view Apple SSO as a...

Are Your NHIs Fully Supported for Optimal Performance?
Non‑Human Identities (NHIs), or machine identities, are becoming a cornerstone of modern cybersecurity, especially in cloud‑first environments. Organizations must manage the full NHI lifecycle—from discovery and classification to threat detection, remediation, and continuous monitoring—to prevent breaches. Traditional point solutions like...

What Role Does Innovation Play in Agentic AI Development?
Non‑human identities (NHIs), also known as machine identities, are becoming a critical focus for cybersecurity, especially in cloud environments. Managing the full lifecycle of these encrypted secrets and permissions reduces breach risk, improves compliance, and drives operational efficiency. The article...

Cybersecurity AI Awareness Training for Texas Government Agencies: How Kratikal’s Threatcop Meets the DIR Mandate
Texas’ Department of Information Resources (DIR) has mandated AI‑aware cybersecurity awareness training for all state and local government employees, with a certification deadline of August 31. Kratikal’s Threatcop platform is one of only five vendors approved under the DIR certification, offering...

From Data to Intelligence: Why More Signals Don’t Equal Better Security
The article argues that simply accumulating more security signals does not improve protection; instead, organizations need to convert raw data into actionable intelligence through verification, attribution, and context, especially around identity. It highlights problems like alert fatigue, false positives, and...

Secure Authentication Starts With Secure Software Development
The MojoAuth blog stresses that secure authentication begins with secure software development, not just choosing the right protocol. It highlights how modern methods like passkeys, WebAuthn, OAuth, and JWT introduce implementation challenges that can become breach vectors. The article outlines...

What Is Shift Left Security?
Shift‑Left Security embeds protection into the earliest phases of the software development lifecycle, moving security checks leftward on the SDLC diagram. Gartner forecasts cloud spending will exceed $1 trillion by 2028, intensifying the need for proactive AppSec. By integrating automated SAST,...

Breach of Confidence – 27 March 2026
The security community faced a wave of incidents in late March, starting with the compromise of Trivy, a popular open‑source scanner, which turned a defensive tool into an attack vector. A separate breach of McKinsey’s AI platform exposed 22 unauthenticated...

Anthropic’s Mythos Leak Is a Wake-Up Call: Phishing 3.0 Is Already Here
Anthropic’s accidental disclosure of its upcoming Claude Mythos model has ignited concerns about AI‑driven cyber threats, but the real alarm is that today’s publicly available generative AI already powers sophisticated phishing attacks. These models can scrape public data, mimic corporate tone,...

BSidesSLC 2025 – LLM-Assisted Risk Management For Small Teams & Budgets
At BSidesSLC 2025, cloud architect Connor Turpin presented a framework for leveraging large‑language models (LLMs) to streamline risk management in security‑constrained environments. He demonstrated how open‑source LLMs can automate vulnerability triage, threat‑intel summarization, and ticket generation for teams with limited...

GPT Can’t Trace an Attack Chain. A Purpose-Built Cybersecurity LLM Can.
Cybersecurity teams face a chronic talent gap, with 4.8 million positions unfilled and 71% of SOC analysts reporting burnout. General‑purpose LLMs like GPT‑4 can summarize alerts but fail to trace attack chains or correlate data across dozens of tools. Purpose‑built cybersecurity...

How to Use a Risk Prioritization Matrix: Step By Step
A risk prioritization matrix transforms vague risk lists into a structured grid that plots likelihood against business impact, enabling teams to spot the most threatening issues at a glance. The guide outlines a seven‑step process—from building a clean risk inventory...

Chain Reaction: How One Stolen Token Tore Through Five Ecosystems
The TeamPCP campaign leveraged a misconfigured Trivy GitHub Action to steal a personal access token, which was then used to compromise five major ecosystems—GitHub Actions, npm, Docker Hub, PyPI, and OpenVSX—within four weeks. Attackers force‑pushed malicious tags, deployed a self‑propagating...

What Is PUE? A Guide to Data Center Efficiency
Power Usage Effectiveness (PUE) is the standard metric that gauges how much of a data center’s total power consumption actually serves IT equipment versus supporting infrastructure. It is calculated by dividing total facility power by IT equipment power, with a...

How Redaction Software Can Help Government Agencies Comply with FOIA
Government agencies are grappling with a record 1.5 million FOIA requests in fiscal 2024, inflating backlogs by 267,000 cases. Manual redaction cannot keep pace, exposing agencies to legal penalties and eroding public trust. Automated redaction platforms, such as Tonic Textual, use...

BSidesSLC 2025 – LLM-Powered Network Intrusion Detection
At BSidesSLC 2025, Pattern Inc. Machine Learning Engineer Taeyang Kim unveiled an LLM‑powered network intrusion detection system (NIDS). The solution leverages large language models to parse raw packet data and identify malicious patterns in real time. Kim demonstrated a prototype...

The Dark Side of DDoS: Why DDoS Downtime Is Harder to Prevent
Cloudflare’s 2026 report reveals DDoS attacks are growing larger, more frequent, and increasingly AI‑driven, shifting from blunt traffic floods to precise, low‑volume Layer 7 assaults timed around high‑impact events. Traditional point‑in‑time testing can’t keep pace with rapid network changes, leading to...

Seceon Wins Four Global InfoSec Awards at RSA 2026 and Launches ADMP and SeraAI 2.0 Autonomous SOC
Seceon Inc. swept four Global InfoSec Awards at RSA 2026, confirming its Open Threat Management platform as the most recognized unified XDR solution. At the same event the company launched ADMP, a module that discovers and protects shadow AI agents, LLM...

Helping MSPs Take Control of Certificate Management: Introducing Sectigo Partner Platform
Only 13% of organizations feel confident tracking every digital certificate, creating a sizable visibility gap. Managed service providers (MSPs) see this as a high‑margin opportunity to offer Certificate Lifecycle Management (CLM) services. Sectigo launched the Partner Platform, the first true...

Vicarius Launches vIntelligence, a Second Flagship Product for Continuous Agentic Validation
Vicarius unveiled vIntelligence, its second flagship product, adding continuous agentic validation to its security suite. The solution tackles the “assurance gap” by independently validating findings and re‑checking exposures as environments evolve. vIntelligence can operate alone or integrate with the existing...

Entro Security Launches AGA to Govern AI Agents and Non-Human Identities Across the Enterprise
Entro Security unveiled Agentic Governance & Administration (AGA), a new platform pillar designed to govern AI agents and non‑human identities across enterprise systems. AGA tackles the shortcomings of traditional Identity Governance and Administration tools, which were built for people and...

News: AI-Native Security Assurance Leads the GRC Transformation
TrustCloud unveiled an AI‑native Security Assurance Platform that replaces legacy GRC tools with continuous, automated risk monitoring. The solution delivers live control signals, connected data and AI‑driven automation, giving CISOs real‑time visibility and credible reporting. Early adopters report up to...

KnowBe4 Expands AIDA to Eight AI Agents at RSAC 2026, Targeting Fully Autonomous Human Risk Management
KnowBe4 unveiled an expanded AIDA suite with eight AI agents at RSAC 2026, including the fully autonomous AIDA Orchestration Agent that creates and manages personalized training and phishing simulations. The Orchestration Agent reportedly cuts users’ risk scores by nearly threefold versus...

Utimaco Survey: 78% of US Companies Say Data Breaches Are the Top GenAI Risk, But Most Haven’t Acted
Utimaco’s 2026 Digital Trust Report, based on a 250‑company survey, finds that 78% of U.S. enterprises view data breaches as the greatest generative AI risk, while 57% have yet to deploy any safeguards. Intellectual‑property theft ranks a close second, and...

EU AI Act Compliance Guide for CISOs & GRC Leaders | Kovrr
The European Union’s AI Act, set to become enforceable on August 2, 2026, imposes a risk‑based regulatory framework on any organization that develops, deploys, or offers AI within the EU market. It distinguishes unacceptable, high‑risk, limited‑risk and minimal‑risk systems, with high‑risk AI...

How to Master Multi-Source Intelligence with AI Agents
Swimlane’s Hero AI Threat Intelligence Agent tackles the long‑standing threat‑intelligence correlation problem by automatically aggregating data from multiple feeds—VirusTotal, Recorded Future, Cisco Umbrella, and others—and synthesizing a single, explainable assessment. The agent applies a reasoning engine that weighs source reliability,...

Building a Layered Security Stack: Identity, Network and Device Protection
Modern enterprises increasingly rely on cloud services and remote work, exposing them to broader cyber threats. To counter this, organizations are adopting a layered security stack that spans identity, network, and device protections. Each layer adds distinct controls—passwordless authentication, MFA,...

A Week in Security (March 16 – March 22)
Malwarebytes’ weekly roundup highlights a surge in privacy‑focused regulations and a wave of novel cyber threats. New legislation in New York aims to curb biometric tracking, while researchers uncovered a font‑rendering trick that masks malicious commands. High‑profile vulnerabilities were disclosed,...

This Is All It Takes to Stop a Train (Lock and Code S07E06)
Bay Area Rapid Transit (BART) experienced three major network failures between May 2025 and February 2026, each shutting down service for thousands of commuters. The outages stemmed from aging networking equipment that lost train‑location visibility, forcing a system‑wide halt. Repeated crashes exposed...

RSAC 2026 Innovation Sandbox | ZeroPath: From Alarm Accumulation to Executable Fixes
ZeroPath, an AI‑native application security startup founded in 2024, was named a finalist in the RSAC 2026 Innovation Sandbox. Its platform unifies SAST, SCA, secrets and IaC scanning into a single AI‑driven engine that verifies exploitability and produces automated repair pull...

Does Your NHI System Deliver Essential Value
Non‑Human Identities (NHIs) now outnumber human users, making machine‑credential security a top priority for enterprises. A robust NHI system manages secrets throughout their lifecycle, providing visibility, automated rotation, and context‑aware controls. Organizations that rely solely on point tools miss hidden...

Is Your Agentic AI Optimized for Latest Threats
Non‑Human Identities (NHIs) are emerging as digital passports that secure machine credentials across cloud environments. A comprehensive lifecycle—discovery, classification, threat detection, and remediation—enables organizations to manage the exploding volume of machine identities in sectors such as finance and healthcare. Integrating...

BSidesSLC 2025 – • Al Red Teaming For Artificial Dummies
At BSidesSLC 2025, Bryson Loughmiller, Principal Platform Security Architect at Entrata, delivered the session "AI Red Teaming For Artificial Dummies." The talk broke down AI red‑team concepts for non‑specialists, showcasing real‑world attack scenarios and mitigation tactics. Loughmiller emphasized the growing...

How Controlled Should Your Cloud-Native AI Security Be
Enterprises adopting cloud‑native architectures must secure machine identities, known as Non‑Human Identities (NHIs), and the secrets they carry. A full lifecycle—discovery, classification, continuous monitoring, and remediation—shifts protection from point solutions to proactive governance. Automation and real‑time oversight cut breach risk,...

Trusted Java Containers: Azul Zulu OpenJDK Joins Docker’s Official Images
Azul Systems announced that its Zulu OpenJDK builds are now part of Docker’s Official Images, making them directly pullable from Docker Hub. The images meet Docker’s rigorous security, signing and maintenance standards and cover all current LTS Java versions—8, 11,...

CISA Recommends Privileged Access Controls for Endpoint Management After Stryker Incident
CISA issued an urgent advisory after a March 11 cyberattack on Stryker that leveraged a compromised Microsoft Intune administrator account to create a global admin and wipe managed devices. The breach highlights a growing trend where attackers target the control planes...
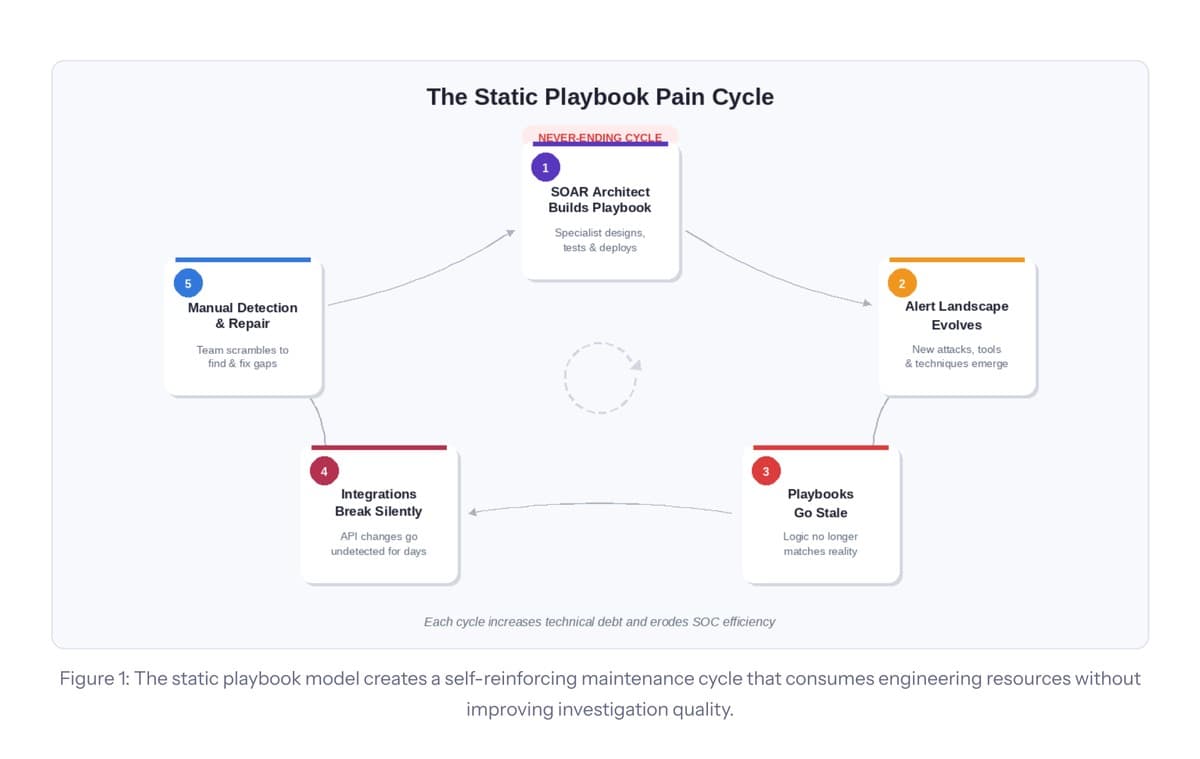
The SOAR Ceiling: Why Playbook Automation Has Hit Its Structural Limits
The article argues that the traditional SOAR playbook model has reached a structural ceiling, burdening security teams with escalating maintenance, scarce architect talent, and static logic that can’t keep pace with evolving threats. It outlines five fractures—architect dependency, playbook sprawl,...