
Vulnerabilities Patched in CrowdStrike, Tenable Products
CrowdStrike and Tenable disclosed critical vulnerabilities in their flagship products and released patches this week. CrowdStrike’s LogScale suffered CVE‑2026‑40050, an unauthenticated path‑traversal that lets attackers read arbitrary files, mitigated for SaaS users and patched for self‑hosted deployments. Tenable reported CVE‑2026‑33694 in its Nessus scanner on Windows, allowing file deletion and arbitrary code execution with system privileges. Both vendors say there is no evidence of exploitation in the wild, but urged customers to apply updates immediately.

Chinese Cybersecurity Firm’s AI Hacking Claims Draw Comparisons to Claude Mythos
Chinese cybersecurity firm 360 Digital Security announced an AI‑driven Multi‑Agent Collaborative Vulnerability Discovery System that reportedly uncovered roughly 1,000 bugs, including more than 50 high‑severity flaws, during the revived Tianfu Cup hacking contest. The firm claims its AI identified a...
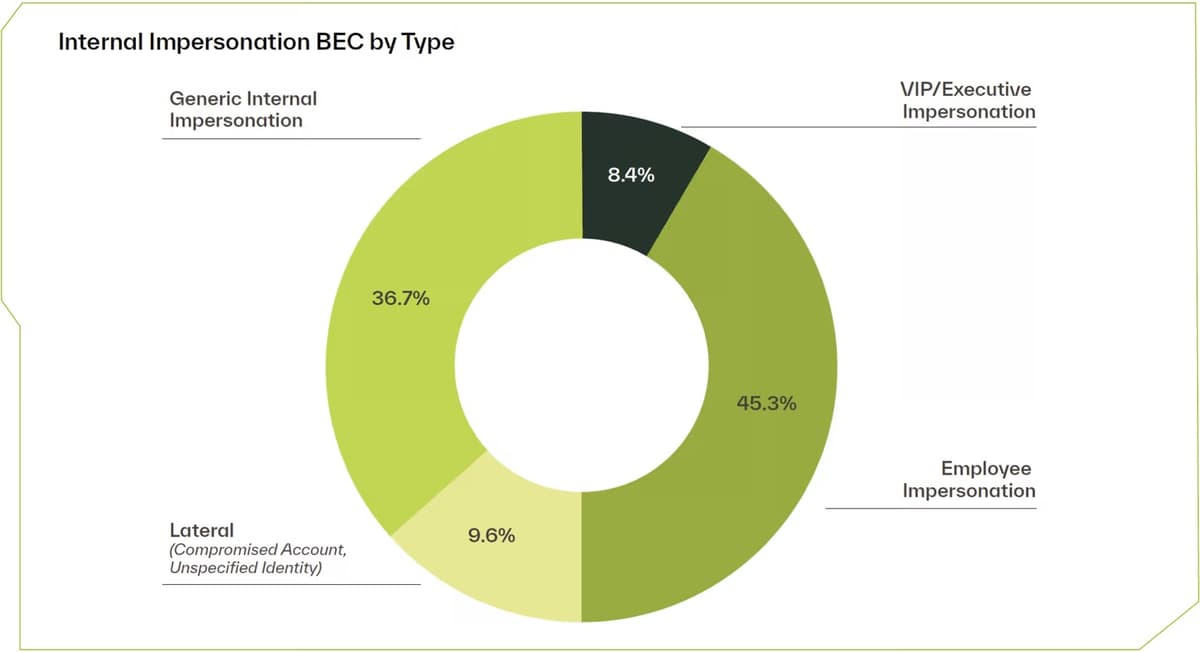
The Behavioral Shift: Why Trusted Relationships Are the Newest Attack Surface
Attackers are moving away from pure technical exploits toward manipulating trusted relationships and everyday workflows. An analysis of 800,000 email attacks across 4,600 firms shows phishing still dominates at 58%, while business email compromise (BEC) accounts for 11% and its...

Apple Patches iOS Flaw Allowing Recovery of Deleted Chats
Apple rolled out iOS 26.4.2, iPadOS 26.4.2, iOS 18.7.8 and iPadOS 18.7.8 updates that fix CVE‑2026‑28950, a logging flaw that kept deleted notifications in device caches. The bug allowed recovered previews of messages, even after apps like Signal were uninstalled, and was reportedly used...

Most Serious Cyberattacks Against the UK Now From Russia, Iran and China, Cyber Chief Says
The UK’s National Cyber Security Centre (NCSC) warned that hostile states—Russia, Iran and China—now drive the most serious cyberattacks against Britain. NCSC chief Richard Horne said the agency dealt with around four nationally significant incidents each week, handling over 200...
Mirai Botnet Targets Flaw in Discontinued D-Link Routers
A Mirai botnet is exploiting CVE‑2025‑29635, a command‑injection flaw in discontinued D‑Link DIR‑823X routers. The vulnerability resides in firmware versions 240126 and 24082, which no longer receive patches because the products were retired last year. Akamai observed attackers using a...
Are SBOMs Failing? Supply Chain Attacks Rise as Security Teams Struggle With SBOM Data
Software Bills of Materials (SBOMs) and Vulnerability Exploitability eXchange (VEX) statements were mandated in 2021 to give organizations visibility into component inventories and exploitability. Five years later, supply‑chain attacks such as the March 2026 Trivy and Axios incidents have intensified,...

Claude Mythos Finds 271 Firefox Vulnerabilities
Anthropic's Claude Mythos AI model uncovered 271 vulnerabilities in Mozilla Firefox, prompting the release of Firefox version 150 which patched over 40 CVEs, including three directly credited to the AI. While most findings were low‑severity issues not assigned CVEs, the...

North Korean Hackers Use AppleScript, ClickFix in Fresh macOS Attacks
North Korean state‑linked groups have launched two macOS‑focused campaigns against financial firms. One uses the ClickFix technique, tricking executives into running a Terminal command that installs the Go‑based Mach‑O Man malware. A second, attributed to Sapphire Sleet, leverages compiled AppleScript files to...

Google Antigravity in Crosshairs of Security Researchers, Cybercriminals
Google’s Antigravity, an AI‑agent development platform powered by Gemini, has drawn attention from both security researchers and cybercriminals. Pillar Security uncovered a sandbox‑escape vulnerability that allowed remote code execution, which Google patched in late February 2026. Separately, Malwarebytes reported a...

Oracle Patches 450 Vulnerabilities With April 2026 CPU
Oracle issued its April 2026 Critical Patch Update, delivering 481 security patches that address roughly 450 CVEs across 28 product families. More than 300 of the fixes target vulnerabilities that can be exploited remotely without authentication, and about three dozen are...

Third US Security Expert Admits Helping Ransomware Gang
A third U.S. cybersecurity professional, 41‑year‑old Angelo Martino, pleaded guilty in March 2026 for aiding the BlackCat/Alphv ransomware gang while serving as a negotiator for an incident‑response firm. Martino supplied confidential negotiation details in exchange for a share of ransom...

Serial-to-IP Converter Flaws Expose OT and Healthcare Systems to Hacking
Researchers at Forescout Technologies uncovered 20 new vulnerabilities in serial-to-IP converters from Silex and Lantronix, devices that bridge legacy serial equipment to Ethernet networks. The flaws, dubbed BRIDGE:BREAK, allow unauthenticated command injection, firmware tampering, denial‑of‑service and full device takeover. Nearly...
British Scattered Spider Hacker Pleads Guilty in the US
A 24‑year‑old British hacker, Tyler Robert Buchanan, pleaded guilty in a U.S. federal court to conspiring with the Scattered Spider group to infiltrate dozens of corporate networks and steal cryptocurrency. He employed SMS‑phishing and SIM‑swapping attacks to harvest employee credentials,...

Hackers Abuse QEMU for Defense Evasion
Security firm Sophos has identified a rise in the misuse of the open‑source QEMU emulator by threat actors to facilitate ransomware and remote‑access operations. In campaign STAB4713 linked to the PayoutsKing ransomware, attackers leveraged QEMU to create reverse‑SSH tunnels after...

Bluesky Disrupted by Sophisticated DDoS Attack
Bluesky, the decentralized microblogging platform, suffered a distributed denial‑of‑service attack that began late on April 15 and persisted for roughly 24 hours, causing intermittent outages across feeds, notifications, threads, and search. The company reported no evidence of data theft and said it...

Senate Extends Surveillance Powers Until April 30 After Chaotic Votes in House
The Senate approved a 10‑day stopgap extension of the Section 702 foreign intelligence surveillance authority, keeping the program alive until April 30. The measure passed by voice vote after a chaotic, after‑midnight scramble in the House that saw a 14‑page amendment fail...

Half of the 6 Million Internet-Facing FTP Servers Lack Encryption
A Censys study found roughly 6 million internet‑facing FTP servers, with 2.45 million (about 41%) offering no encryption. While the total number of FTP hosts fell 40% since 2024, the protocol still represents 2.72% of all visible internet services. Pure‑FTPd powers the...

Next.js Creator Vercel Hacked
Vercel, the creator of the Next.js framework and a leading frontend cloud platform, confirmed a breach on April 20, 2026 after a hacker group offered its stolen databases, source code, and access keys for $2 million. The intrusion stemmed from a...

Tycoon 2FA Loses Phishing Kit Crown Amid Surge in Attacks
Tycoon 2FA, once the dominant phishing‑as‑a‑service platform with an 89% market share, lost its crown after a coordinated law‑enforcement seizure of 330 domains in March. Barracuda Networks reports that attacks using the four major kits—Tycoon, Mamba, EvilProxy and Sneaky—have risen from...

CoChat Launches AI Collaboration Platform to Combat Shadow AI
CoChat debuted in early April 2026 as an AI collaboration platform aimed at curbing the rise of shadow AI within enterprises. By consolidating access to leading large language models (LLMs) and autonomous agents, it eliminates fragmented, unmanaged AI silos. The...

In Other News: Satellite Cybersecurity Act, $90K Chrome Flaw, Teen Hacker Arrested
The Senate advanced the bipartisan Satellite Cybersecurity Act of 2025, directing the Commerce Department to create a central hub for satellite security best practices as half of commercial satellite signals remain unencrypted. Law enforcement agencies dismantled the W3LL phishing‑as‑a‑service operation...

Cursor AI Vulnerability Exposed Developer Devices
Security firm Straiker uncovered a critical vulnerability, dubbed NomShub, in the Cursor AI coding assistant. The flaw combines indirect prompt injection with a sandbox‑escape that lets attackers write files and hijack the editor’s Azure‑based remote tunnel, granting persistent shell access...

Artemis Emerges From Stealth With $70 Million in Funding
New York‑based Artemis, a cybersecurity startup founded in 2025, announced it has emerged from stealth with a $70 million seed and Series A round. The company’s AI‑driven platform detects and contains threats across applications, users, machines and cloud workloads by building a...

Splunk Enterprise Update Patches Code Execution Vulnerability
Splunk released emergency patches for several critical flaws across its Enterprise, Cloud Platform, and MCP Server products. The most severe issue, CVE‑2026‑20204, allowed low‑privileged users to upload malicious files and achieve remote code execution due to improper handling of temporary...

Claude Code, Gemini CLI, GitHub Copilot Agents Vulnerable to Prompt Injection via Comments
Security researchers disclosed a new prompt‑injection technique called “Comment and Control” that exploits AI‑driven code tools on GitHub. The method tricks Claude Code Security Review, Google Gemini CLI Action, and GitHub Copilot Agent by embedding malicious prompts in pull‑request titles, issue...

Exploited Vulnerability Exposes Nginx Servers to Hacking
A critical vulnerability (CVE‑2026‑33032) in Nginx UI’s AI‑driven management console has been exploited in the wild, allowing unauthenticated attackers to take full control of servers. Pluto Security identified more than 2,600 internet‑exposed instances and demonstrated a proof‑of‑concept exploit. The flaw...

Microsoft Patches Exploited SharePoint Zero-Day and 160 Other Vulnerabilities
Microsoft’s April 2026 Patch Tuesday delivered fixes for 165 vulnerabilities, highlighted by an exploited SharePoint Server zero‑day (CVE‑2026‑32201) rated “important” with a CVSS score of 6.5. The flaw enables network‑level spoofing and has been added to CISA’s Known Exploited Vulnerabilities list, prompting...

SAP Patches Critical ABAP Vulnerability
SAP released 20 new and updated security notes on April 14, 2026, including two critical CVEs. The most severe, CVE‑2026‑27681 (CVSS 9.9), is a SQL‑injection flaw in Business Planning and Consolidation and Business Warehouse that enables arbitrary code execution. SAP mitigated the issue...

Triad Nexus Evades Sanctions to Fuel Cybercrime
Triad Nexus, an illicit cyber‑crime network active since 2020, has generated over $200 million in losses through sophisticated cryptocurrency investment‑fraud known as pig‑butchering. After the U.S. sanctioned its primary CDN partner Funnull in 2025, the group adopted infrastructure‑laundering tactics, using front‑company...

Nightclub Giant RCI Hospitality Reports Data Breach
RCI Hospitality Holdings, a leading adult nightclub operator, disclosed a data breach affecting its independent contractors. The breach stemmed from an insecure direct object reference (IDOR) vulnerability on an IIS web server discovered on March 23, with unauthorized access beginning March 19....

OpenAI Impacted by North Korea-Linked Axios Supply Chain Hack
OpenAI disclosed that a GitHub Actions workflow used for macOS app signing inadvertently downloaded a malicious version of the popular Axios JavaScript library, version 1.14.1, as part of a supply‑chain attack linked to North Korean group UNC1069. The compromised workflow...

Fake Claude Website Distributes PlugX RAT
Security researchers discovered a counterfeit Anthropic Claude website that offered a fake "pro" version of the LLM, but the download actually installed a trojanized MSI. The installer runs a VBScript dropper that places a signed G DATA updater in the startup...

In Other News: Cyberattack Stings Stryker, Windows Zero-Day, China Supercomputer Hack
The weekly SecurityWeek roundup highlighted several high‑profile cyber incidents, including a March 2026 attack on medical‑device maker Stryker that will shave earnings from its first‑quarter results, and a newly disclosed Windows zero‑day dubbed BlueHammer that gives attackers full SYSTEM privileges....

Juniper Networks Patches Dozens of Junos OS Vulnerabilities
Juniper Networks released patches for nearly three dozen vulnerabilities affecting its Junos OS and Junos OS Evolved platforms. The most critical flaw, CVE-2026-33784 (CVSS 9.8), involves a default password in the Support Insights Virtual Lightweight Collector that could be exploited...

Orthanc DICOM Vulnerabilities Lead to Crashes, RCE
A CERT/CC advisory disclosed nine critical vulnerabilities (CVE‑2026‑5437 to CVE‑2026‑5445) in the open‑source Orthanc DICOM server, affecting versions up to 1.12.10. The flaws include out‑of‑bounds reads, decompression‑bombs, memory‑exhaustion bugs, and heap buffer overflows that can crash servers, leak image data,...

MITRE Releases Fight Fraud Framework
MITRE Corporation unveiled the Fight Fraud Framework (MITRE F3), a free, open‑source knowledge base that maps fraudsters’ tactics, techniques and procedures using a behavior‑based model. The framework extends the ATT&CK taxonomy with two fraud‑specific tactics—positioning and monetization—covering the full lifecycle from...

Critical Marimo Flaw Exploited Hours After Public Disclosure
Security firm Sysdig reported that a critical‑severity RCE flaw in the open‑source Python notebook Marimo (CVE‑2026‑39987, CVSS 9.3) was exploited less than ten hours after its public disclosure. The vulnerability stems from an unauthenticated WebSocket terminal endpoint that grants a full...

Microsoft Finds Vulnerability Exposing Millions of Android Crypto Wallet Users
Microsoft’s security researchers uncovered a critical intent‑redirection flaw in EngageLab’s EngageSDK, a messaging library embedded in over 30 million Android cryptocurrency‑wallet installations. The vulnerability lets a malicious app craft intents that bypass Android’s sandbox, exposing personal data and financial credentials. Microsoft...

Apple Intelligence AI Guardrails Bypassed in New Attack
Researchers from RSAC demonstrated a method to bypass Apple Intelligence's on‑device AI guardrails, achieving a 76% success rate across 100 test prompts. The technique merges the Neural Execs prompt‑injection attack with Unicode right‑to‑left override manipulation, allowing malicious output to slip...

Palo Alto Networks, SonicWall Patch High-Severity Vulnerabilities
Palo Alto Networks and SonicWall each released emergency patches addressing multiple vulnerabilities, including two high‑severity flaws. Palo Alto fixed three bugs—most notably CVE‑2026‑0234 affecting Cortex XSOAR/XSIAM’s Microsoft Teams integration—and added dozens of Chromium security updates. SonicWall patched four issues in...

Google Warns of New Campaign Targeting BPOs to Steal Corporate Data
Google’s Threat Intelligence Group has identified a financially motivated actor, tracked as UNC6783, launching a focused campaign against business process outsourcing firms to pilfer data from their high‑value corporate clients. The group uses live‑chat lures, spoofed Okta login pages and...

Adobe Reader Zero-Day Exploited for Months: Researcher
A researcher has identified an actively exploited zero‑day vulnerability in Adobe Reader, discovered through a malicious PDF that can harvest system data and may enable remote code execution or sandbox escape. The exploit has been observed in the wild since...

$3.6 Million Stolen in Bitcoin Depot Hack
Bitcoin Depot, the largest U.S. Bitcoin ATM operator, disclosed that hackers stole roughly 50.903 BTC, valued at about $3.6 million, after breaching its corporate IT systems on March 23. The company says the intrusion was limited to internal wallets and did not affect...

Shaky Ceasefire Unlikely to Stop Cyberattacks From Iran-Linked Hackers for Long
A tentative cease‑fire between Iran, the United States and Israel is unlikely to halt cyber attacks from Iran‑linked groups. Pro‑Iranian hacktivist collective Handala announced it will pause attacks on U.S. targets but continue striking Israel, warning it will resume U.S....

The New Rules of Engagement: Matching Agentic Attack Speed
AI‑enabled cyberwarfare has moved from theory to reality, highlighted by Anthropic's September 2025 disclosure of an autonomous attack that operated with minimal human input. A 2026 Armis report shows 64% of U.S. IT decision‑makers already suffered AI‑generated attacks, while 92%...

Severe StrongBox Vulnerability Patched in Android
Google released the April 2026 Android security patch, fixing two high‑profile flaws: a local denial‑of‑service bug (CVE‑2026‑0049) in the Framework and a high‑severity vulnerability (CVE‑2025‑48651) affecting StrongBox, the hardware‑backed keystore. StrongBox implementations from Google, NXP, STMicroelectronics and Thales are impacted. While...

GrafanaGhost: Attackers Can Abuse Grafana to Leak Enterprise Data
Security researcher Noma Security disclosed a critical Grafana vulnerability dubbed GrafanaGhost, which lets attackers exploit the platform’s AI features to exfiltrate enterprise data via crafted image prompts. By injecting a hidden “intent” keyword, the flaw bypasses Grafana’s image URL validation...

In Other News: ChatGPT Data Leak, Android Rootkit, Water Facility Hit by Ransomware
This week’s cybersecurity roundup revealed a wave of high‑profile threats, from a new Android banking trojan called Mirax that can be rented for $3,000 a month to an Android rootkit dubbed NoVoice that has infected roughly 2.3 million devices via Google...

Mobile Attack Surface Expands as Enterprises Lose Control
Jamf’s 2025 mobile security report, based on 1.7 million devices, reveals a sprawling, poorly‑controlled attack surface. Over half of enterprises host at least one device with a critically outdated OS, while 86% of the 135 most common apps contain known vulnerabilities....