CYBERSECURITY PULSE
Monday, March 2, 2026
Market Intelligence for Cybersecurity Professionals
🎯 Today's Cybersecurity PulseUpdated 58m ago
What's happening: DHS shutdown stalls critical‑infrastructure breach‑reporting rule
A partial shutdown of the Department of Homeland Security is delaying the finalization of the Cyber Incident Reporting for Critical Infrastructure Act rule, which would impose stricter breach‑notification requirements on critical‑infrastructure firms. The agency announced in February that it is reopening the comment period after companies raised concerns about the rule’s scope in June.
Also developing:
By the numbers: Zafran Security raises $60M Series C
🚀 Top Cybersecurity Headlines

CISA Releases New Guidance on Assembling Multi-Disciplinary Insider Threat Management Teams
Ashley Nyquist, Ashden Fein, Caleb Skeath, John Webster Leslie, Matthew Harden, Catherine McGrath, and Samar Amidi of Covington and Burling write: On January 28, 2026, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) published a new resource on Assembling a Multi-Disciplinary Insider Threat Management Team.The guidance is intended to assist critical infrastructure stakeholders, which includes private... Source
DataBreaches.net

Escalating Cyber Attacks From Iran: Is Your Organization Prepared for State Sponsored Threat Groups?
Military action in Iran has increased the potential of cyberattacks from Iranian sponsored actors and hacktivists, and criminal groups aligned with Iran.
Homeland Security Today (HSToday)
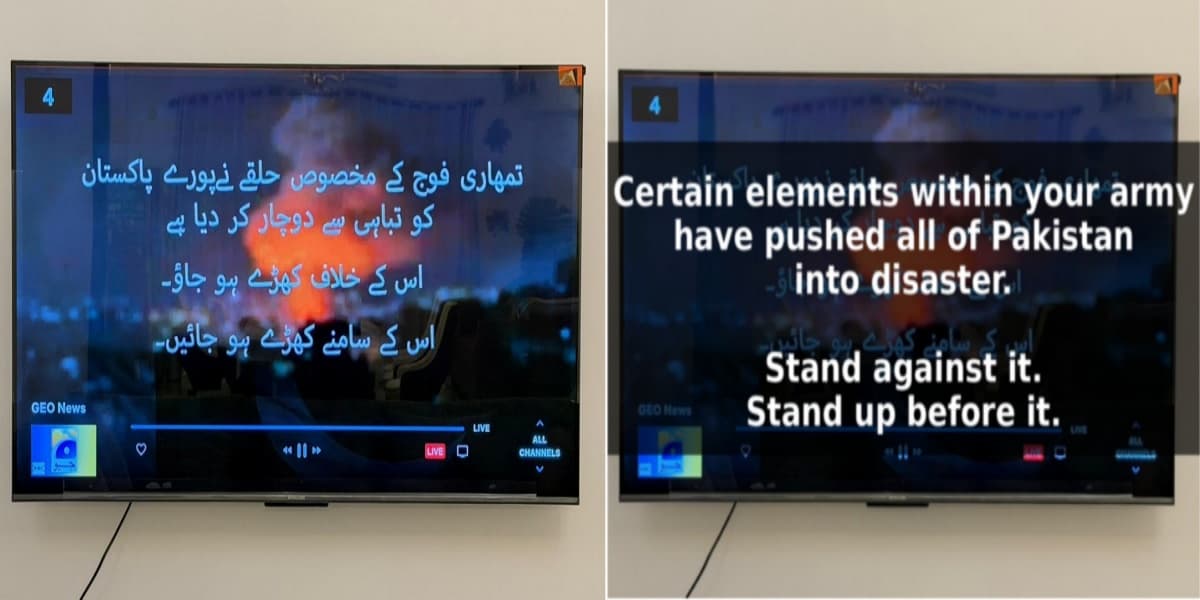
Pakistan’s Top News Channels Hacked and Hijacked With Anti-Military Messages
Major Pakistani TV channels, including Geo News and ARY News, were hit by a coordinated cyberattack on 1 March 2026. Hackers took control of live satellite feeds to display unauthorised messages. Read more about the breach, the regional impact, and the reported counter-cyber response.
HackRead

Link11 Releases European Cyber Report 2026: DDoS Attacks Become a Constant Threat
Frankfurt am Main, Germany, 2nd March 2026, CyberNewswire
HackRead

Quantum-Secure Cloud Computing: The Next Frontier in Enterprise Data Protection
All content provided by Ian Khan Ian Khan, FutureSHIFT™ Experience Keynote & Workshop A breakthrough in quantum-resistant encryption protocols is reshaping cloud security, offering enterprises unprecedented protection against future quantum computing threats. The post Quantum-Secure Cloud Computing: The Next Frontier in Enterprise Data Protection first appeared on Ian Khan, FutureSHIFT™ Experience Keynote & Workshop.
Ian Khan’s Technology Blog
💬 Top Cybersecurity Social Posts

Tweet by @Eastdakota
Whatever may come next from Iran, @Cloudflare is well aware of their techniques, not worried, and fully prepared to defend our customers.
by Matthew Prince•

Thread by @Seandmacknyc
Cybercrime growth is outpacing cybersecurity spend. We are not going to tool our way out of this. Architecture, identity discipline, and operational resilience matter more than another dashboard.
by Sean D. Mack•



