
Anthropic Bets on EPSS for the Coming Bug Surge
Anthropic introduced Mythos, an AI model that can discover software flaws at unprecedented speed, intensifying the existing vulnerability overload. To help defenders prioritize, Anthropic advises using the Exploit Prediction Scoring System (EPSS), a probabilistic model that forecasts exploitation likelihood within 30 days. EPSS, already embedded in over 120 security vendors’ tools, can filter thousands of CVEs by focusing first on CISA’s KEV list and then on scores above a chosen threshold. Industry leaders see EPSS as a crucial bridge, though some argue it may become outdated as exploit windows shrink to minutes.

Thousands of Apache ActiveMQ Instances Still Unpatched, Weeks After an Actively Exploited Hole Discovered
Researchers at Horizon3.ai used Anthropic's Claude AI to uncover a remote code execution flaw (CVE‑2026‑34197) in Apache ActiveMQ within ten minutes. The vulnerability affects versions before 5.19.4 and 6.0‑6.2.2, exposing nearly 6,500 internet‑facing instances two weeks after disclosure. CISA has...

Azure SRE Agent Flaw Lets Outsiders Silently Eavesdrop on Enterprise Cloud Operations
Microsoft disclosed a critical authentication flaw (CVE‑2026‑32173) in its Azure SRE Agent that let any Entra ID tenant obtain a valid token and listen to the agent’s WebSocket stream. The vulnerability exposed user prompts, internal reasoning, commands, and credentials without...

Top Techniques Attackers Use to Infiltrate Your Systems Today
The article outlines current cyberattack techniques, highlighting identity‑based methods as dominant. Phishing (41%), stolen credentials (18%) and social engineering (12%) drive most incidents, while abuse of legitimate remote monitoring and management (RMM) tools accounts for 30% of breaches. Attackers also...

The Thin Gray Line: Handala, CyberAv3ngers and Iran’s Proxy Ops
On April 7, six U.S. agencies issued a joint advisory warning that Iranian‑linked advanced persistent threat groups could launch cyberattacks on critical infrastructure, citing the 2023 water‑facility breaches attributed to the APT known as CyberAv3ngers. The advisory also references the...

Attackers Abuse Microsoft Teams to Impersonate the IT Helpdesk in a New Enterprise Intrusion Playbook
Microsoft’s security research reveals a new intrusion playbook where threat actors exploit Microsoft Teams’ cross‑tenant chat feature to impersonate IT helpdesk staff. By convincing employees to grant remote access through legitimate tools, attackers bypass traditional phishing filters and blend into...

CISOs Reshape Their Roles as Business Risk Strategists
CISOs are evolving from pure technical stewards to enterprise risk strategists, exemplified by ThoughtWorks' Nitin Raina, who simultaneously serves as global CISO and head of enterprise risk. Recent surveys show 78% of CISOs share security‑risk accountability with other C‑suite executives,...

Critical Sandbox Bypass Fixed in Popular Thymeleaf Java Template Engine
Thymeleaf, the default template engine for Java Spring applications, patched a critical Server‑Side Template Injection flaw (CVE‑2026‑40478) rated 9.1 on the CVSS scale. The vulnerability let unauthenticated attackers bypass the engine’s sandbox by using whitespace characters, enabling arbitrary expression execution....

Flawed Cisco Update Threatens to Stop APs From Getting Further Patches
Cisco's recent IOS XE update for over 200 wireless access point models adds a log that grows about 5 MB per day, eventually exhausting flash memory and blocking further patches or bricking devices. Affected models include Catalyst 9130AX, 91361, 9162x, 9164x, IW9167...

White House Moves to Give Federal Agencies Access to Anthropic’s Claude Mythos
The White House Office of Management and Budget announced it is preparing to allow major federal agencies to use a modified version of Anthropic’s Claude Mythos AI model. Claude Mythos has demonstrated the ability to locate thousands of zero‑day vulnerabilities...

Another Microsoft Defender Privilege Escalation Bug Emerges Days After Patch
Researchers have disclosed a new local privilege escalation exploit called “RedSun” that abuses Microsoft Defender’s handling of cloud‑tagged files to rewrite protected system binaries and gain SYSTEM rights. The proof‑of‑concept works on Windows 10, Windows 11 and Windows Server 2019+...

Palo Alto’s Helmut Reisinger Sees a Cyber Sea Change Ahead as AI Advances
Palo Alto Networks is deepening its AI‑centric security push by joining Anthropic’s Project Glasswing, an exclusive initiative that uses Claude Mythos to uncover zero‑day vulnerabilities. The company has accelerated its platformization strategy through recent acquisitions—Protect AI, Chronosphere and the soon‑to‑close...

Behind the Mythos Hype, Glasswing Has Just One Confirmed CVE
Anthropic’s Project Glasswing, the gated access program behind its Mythos AI, has produced only one publicly attributed CVE (CVE‑2026‑4747) according to VulnCheck’s analysis. While Anthropic researchers are credited with 40 CVEs overall, the majority stem from external collaborations rather than...

Insurance Carriers Quietly Back Away From Covering AI Outputs
Major U.S. insurers are quietly pulling back from covering AI‑generated outputs in cyber‑risk and errors‑and‑omissions policies. While some carriers are outright declining to write such coverage, others are imposing steep premium hikes or carving out explicit exclusions for AI‑related liabilities....

The Endless CISO Reporting Line Debate — and What It Says About Cybersecurity Leadership
The debate over where the chief information security officer (CISO) should report persists in 2026, despite two decades of high‑profile breaches and heightened board scrutiny. While the reporting line signals authority and visibility, it is ultimately a proxy for the...

Copilot and Agentforce Fall to Form-Based Prompt Injection Tricks
Security researchers at Capsule Security uncovered prompt‑injection flaws in Microsoft Copilot Studio and Salesforce Agentforce that let attackers exfiltrate data via ordinary SharePoint and lead forms. In Copilot, the “ShareLeak” vulnerability (CVE‑2026‑21520) lets a crafted comment field override system prompts...
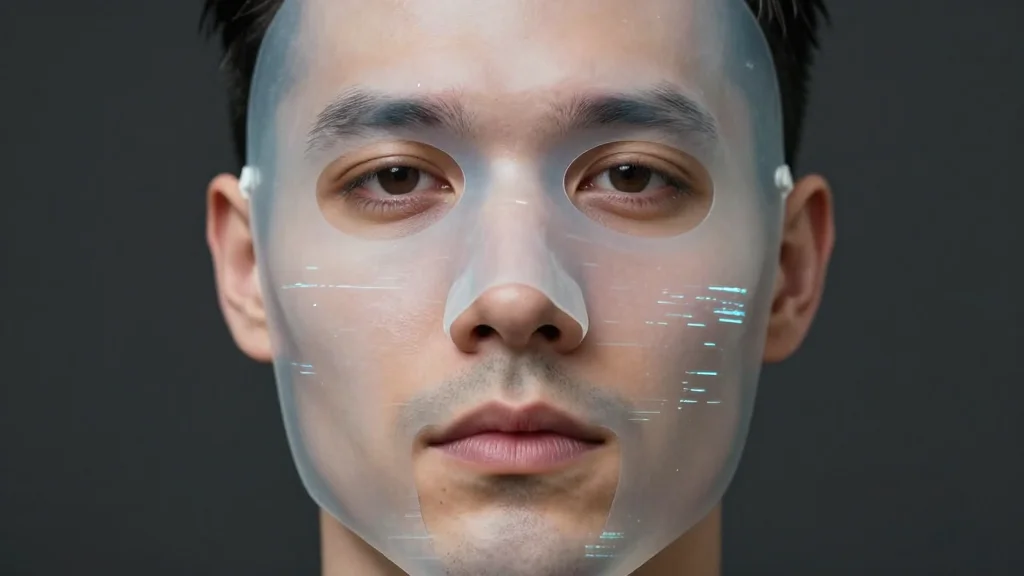
The Deepfake Dilemma: From Financial Fraud to Reputational Crisis
Deepfake technology has moved from a niche curiosity to a cheap, widely accessible threat, with a 2025 Gartner survey showing 43% of cybersecurity leaders encountering audio deepfakes and 37% facing video deepfakes in the past year. The fraud potential is...

The Need for a Board-Level Definition of Cyber Resilience
Cyber resilience is now a board‑level governance priority, yet its definition varies across regulatory frameworks, leaving directors uncertain about oversight responsibilities. A literature review of 38 sources shows the concept is still fragmented, with divergent views on scope and relationship...

April Patch Tuesday Roundup: Zero Day Vulnerabilities and Critical Bugs
Microsoft’s April Patch Tuesday delivered 167 fixes, including a actively‑exploited SharePoint Server zero‑day (CVE‑2026‑32201) and a critical Windows IKE remote‑code‑execution flaw (CVE‑2026‑33824) with a 9.8 CVSS score. Additional high‑risk bugs affect Active Directory (CVE‑2026‑33826), TCP/IP stack (CVE‑2026‑33827) and SAP Business...

4 Questions to Ask Before Outsourcing MDR
Security teams face relentless alerts, staffing gaps and rising expectations for uptime, making Managed Detection and Response (MDR) a strategic necessity rather than a luxury. Outsourcing MDR provides round‑the‑clock monitoring across endpoints, identities and cloud workloads, ensuring threats are spotted...

5 Trends Defining the Future of AI-Powered Cybersecurity
The N‑able and Futurum report outlines how AI is reshaping cybersecurity, turning generative models into both attack tools and defensive assets. Attackers now automate phishing, vulnerability scanning and exploit delivery at machine speed, forcing security teams to abandon static, perimeter‑based...

China-Linked Cloud Credential Heist Runs on Typos and SMTP
Chinese‑aligned APT41 has deployed a Linux ELF backdoor that steals cloud credentials across AWS, GCP, Azure and Alibaba Cloud. The malware uses port 25 SMTP as a covert C2 channel, sending harvested IAM role and service‑account tokens to three typosquatted...

The AI Inflection Point: What Security Leaders Must Do Now
AI has moved from experiment to production in cybersecurity, forcing security leaders to treat it as an operating‑model shift rather than a bolt‑on tool. Threat reports show AI‑enabled adversaries accelerating attack timelines to under 30 minutes, outpacing human‑only triage. CISOs...

Seven IBM WebSphere Liberty Flaws Can Be Chained Into Full Takeover
Security researchers disclosed seven interrelated flaws in IBM WebSphere Liberty, a modular Java application server, that can be chained to achieve full server takeover. The chain begins with a pre‑authentication remote code execution (RCE) vulnerability in the SAML Web SSO...

CISOs Tackle the AI Visibility Gap
CISOs are confronting a growing AI visibility gap as organizations race to deploy generative models and AI‑enabled tools. A Pentera 2026 survey shows 67% of security leaders lack clear insight into where AI runs, and 48% cite limited visibility as...

Hungarian Government Email Passwords Exposed Ahead of Election
Bellingcat uncovered that passwords for nearly 800 Hungarian government email accounts are publicly available, affecting 12 of the 13 ministries, including national‑security officials. The leaks stem from simple, easily guessable passwords rather than sophisticated cyber attacks. The exposure comes weeks...

Why Most Zero-Trust Architectures Fail at the Traffic Layer
Zero‑trust programs often excel at identity verification but stumble when traffic reaches the network edge. In many enterprises, inconsistent enforcement of TLS, fragmented ingress points, and partial mutual‑TLS deployments let malicious traffic bypass policy controls. The article highlights that the...

CMMC Compliance in the Age of AI
Cybersecurity Maturity Model Certification 2.0 (CMMC 2.0) now requires federal contractors to prove how they protect Controlled Unclassified Information, moving beyond self‑attestation to verifiable evidence. The biggest readiness gap is a lack of comprehensive data‑scope awareness, often uncovering a larger...

Weak at the Seams
The article argues that cyber risk is no longer a collection of isolated silos but a systemic threat amplified by digital transformation across healthcare, finance and manufacturing. While global security spending is projected to exceed $212 billion in 2025, the exposure...

Patch Windows Collapse as Time-to-Exploit Accelerates
Rapid7’s 2026 Threat Landscape Report shows confirmed exploitation of high‑ and critical‑severity vulnerabilities more than doubled, rising to 146 incidents in 2025 from 71 in 2024. The median time from public disclosure to inclusion in CISA’s Known Exploited Vulnerabilities list...

Arelion Employs NETSCOUT Arbor DDoS Protection Products
Arelion, a Tier‑1 IP backbone provider serving 129 countries, has deepened its partnership with NETSCOUT to modernize its DDoS defense. After 16 years using Arbor Sightline and the Threat Mitigation System, Arelion added three NETSCOUT offerings—Sentinel, ATLAS Intelligence Feed, and...

6 Winter 2026 G2 Leader Badges Prove This DDoS Protection Stands Out
NETSCOUT’s Arbor Threat Mitigation System (TMS) captured five G2 leader badges for winter 2026, spanning enterprise DDoS protection, momentum, regional Asia, and web security categories. Its companion solution, Arbor Sightline, earned a leader badge in enterprise network management. The awards...

How Botnet-Driven DDoS Attacks Evolved in 2H 2025
In the second half of 2025, DDoS attacks remained numerically steady but grew dramatically in scale and sophistication. AI‑enhanced DDoS‑for‑hire services enabled even non‑technical actors to launch multiterabit floods, with IoT botnets such as TurboMirai reaching 30 Tbps and 4 gigapackets per...

5 Practical Steps to Strengthen Attack Resilience with Attack Surface Management
The article outlines how attack surface management (ASM) transforms raw visibility into measurable cyber resilience by continuously identifying and prioritizing exposure across all asset categories. It presents five practical steps: comprehensive surface identification, focusing on fast‑breaking attack vectors, moving from...

5 Steps to Strengthen Supply Chain Security and Improve Cyber Resilience
Supply chain attacks are increasingly bypassing traditional defenses, forcing organizations to treat vendor risk as a core cyber‑resilience issue. The article outlines five practical steps: mapping and prioritizing dependencies, continuously monitoring supplier security posture, tightening access controls, deploying unified telemetry...

5 Ways to Strengthen Identity Security and Improve Attack Resilience
Identity compromise is now the top vector for breaching corporate systems, rendering traditional firewalls and endpoint tools ineffective once valid credentials are used. The article outlines five actionable steps—mandatory MFA for privileged accounts, deployment of privileged access management (PAM), comprehensive...

Zero‑click Grafana AI Attack Can Enable Enterprise Data Exfiltration
Security researchers have uncovered GrafanaGhost, a chained exploit that leverages indirect prompt injection in Grafana’s AI dashboards to exfiltrate sensitive enterprise data without user authentication. The attack persists malicious prompts, tricks the AI model into generating outbound image requests, and...

Supply Chain Security Is Now a Board-Level Issue: Here’s What CSOs Need to Know
Supply chain security has moved from a niche technical issue to a board‑level priority, driven by stringent regulations like the European Cyber Resilience Act and U.S. EO 14028. Open‑source components now appear in 97% of commercial applications, with 86% harboring vulnerabilities,...

Escaping the COTS Trap
Enterprise cybersecurity teams have amassed large fleets of commercial off‑the‑shelf (COTS) tools, driving complexity, cost, and risk. While COTS promises rapid deployment and lower upfront spend, dependence creates structural lock‑in that hampers future changes and migration. The article highlights how...

WhatsApp Malware Campaign Uses Malicious VBS Files to Gain Persistent Access
Microsoft Defender has identified a WhatsApp‑based malware campaign that distributes malicious Visual Basic Script (VBS) files. The scripts employ social engineering and living‑off‑the‑land techniques, renaming legitimate Windows utilities to download additional payloads. Attackers host these payloads on trusted cloud services...

9 Ways CISOs Can Combat AI Hallucinations
AI hallucinations are undermining governance, risk and compliance (GRC) processes as generative tools begin making judgment calls on control effectiveness and incident handling. Security leaders warn that unchecked AI can produce convincing yet inaccurate assessments, leading to faulty risk scores...
The External Pressures Redefining Cybersecurity Risk
External pressures are reshaping cybersecurity risk, with third‑party breaches now accounting for over 35% of incidents. Geopolitical conflicts are spilling battle‑tested tactics into operational technology (OT) and IoT environments, raising safety and continuity stakes. Generative AI accelerates attacker capabilities while...

Why Kubernetes Controllers Are the Perfect Backdoor
Kubernetes controllers, the engine behind cluster self‑healing, are being weaponized as stealthy backdoors. Threat actors register rogue MutatingAdmissionWebhooks or custom controllers that watch for pod creation events and inject malicious sidecars, as seen in the Siloscape and Hildegard campaigns. Because...

Chained Vulnerabilities in Cisco Catalyst Switches Could Induce Denial-of-Service
Cisco disclosed four vulnerabilities in its widely deployed Catalyst 9300 series switches, two of which (CVE‑2026‑20114 and CVE‑2026‑20110) can be chained to elevate a low‑privilege Lobby Ambassador account into maintenance mode, effectively causing a denial‑of‑service outage. The chain requires only...

The Insider Threat Rises Again
Insider threats are resurging, with 42% of organizations reporting more malicious incidents and a similar rise in negligent cases, according to Mimecast’s State of Human Risk Report. The average cost per insider‑driven breach now tops $13.1 million, and 66% of security...

Reco Targets AI Agent Blind Spots with New Security Capability
Reco has launched a new capability called “Reco AI Agent Security” to give enterprises visibility and control over autonomous AI agents across their SaaS stack. The tool, available from March 18, expands Reco’s existing platform to cover agents such as Microsoft...

Can You Prove the Person on the Other Side Is Real?
The article warns that by 2026 synthetic identities and deepfake technology will outpace traditional AI automation in the estate‑and‑identity space. Generative models can create fully fabricated personas that pass routine checks, allowing fraudsters to hijack legacy or deceased accounts and...

ClickFix Treibt Neue Infostealer-Kampagnen An
Rapid7 uncovered a large‑scale ClickFix campaign that has compromised more than 250 WordPress sites in twelve countries since December 2025. The attackers serve a fake Cloudflare CAPTCHA which tricks visitors into executing obfuscated PowerShell commands that launch the DoubleDonut loader...

What It Takes to Win that CSO Role
Chief Security Officer (CSO) and Chief Information Security Officer (CISO) roles have shifted from technical gatekeepers to board‑level risk executives. Executives now oversee AI governance, regulatory compliance such as the EU AI Act, and must prove security can sustain business...

Hybrid Resilience: Designing Incident Response Across On-Prem, Cloud and SaaS without Losing Your Mind
Hybrid incident response demands more than tool consolidation; a shared incident language and unified command structure are essential. The author proposes a contract that standardizes severity, hypothesis, timeline, and communication cadence across on‑prem, cloud, and SaaS teams. Portable telemetry—user‑journey metrics,...