
ZeroDayRAT Targets Android and iOS Devices for Surveillance and Financial Data Theft
ZeroDayRAT, a Malware‑as‑a‑Service kit, now targets both Android and iOS devices, merging real‑time surveillance with direct financial theft through a browser‑based control panel. The service is marketed on Telegram, with subscriptions ranging from $250 per day to $3,500 per month, and is delivered via smishing messages and counterfeit app distributions. Once installed, the RAT provides live video, audio, GPS tracking, keylogging, and cryptocurrency‑wallet hijacking capabilities. Researchers note some promotional material may exaggerate features, but the core functionality poses a genuine cross‑platform threat.

Deserialization Flaw in Ruby Workers That Could Enable Full Compromise
A critical remote code execution vulnerability has been discovered in RubitMQ job workers due to unsafe JSON deserialization with the Ruby Oj library. The flaw allows attackers to craft malicious JSON that triggers object injection, instantiating a Node class whose...

LUKS Encryption Compromised on Linux ICS Devices via TPM Bus Sniffing Exploit
Security researchers have disclosed CVE‑2026‑0714, a high‑severity flaw in Moxa’s UC‑1222A Secure Edition industrial computer. The vulnerability allows an attacker with physical access to the SPI bus to sniff the TPM2_NV_Read command and capture the LUKS full‑disk encryption key in...

Cache Deception Flaw in SvelteKit And Vercel Stack Exposes User Data
A cache‑deception flaw was found in SvelteKit applications deployed on Vercel, where the `__pathname` query parameter can override request paths and cause private API responses to be cached as public assets. The vulnerability affects any route under `/_app/immutable/`, which Vercel...

Anthropic Debuts Claude Code Security – AI Now Scan Vulnerabilities in Your Entire Codebase
Anthropic launched Claude Code Security, an AI‑driven tool that scans entire codebases for vulnerabilities and suggests patches. Powered by Claude Opus 4.6, it uses frontier reasoning to map data flows and identify complex bugs that traditional SAST tools miss. Internal tests...

CharlieKirk Grabber Malware Targets Windows Systems to Steal Login Credentials
CharlieKirk Grabber is a new Python‑based Windows infostealer first seen in February 2026. It rapidly harvests credentials from Chromium and Firefox browsers, Wi‑Fi profiles, Discord tokens, and gaming sessions, then packages the data into a ZIP archive for exfiltration via...

ClickFix Exploits Homebrew Workflow to Deploy Cuckoo Stealer for macOS Credential Theft
ClickFix is weaponizing a fake Homebrew installation workflow to deliver Cuckoo Stealer, a macOS credential‑stealing RAT. The campaign uses typosquatted domains such as homabrews.org that mimic brew.sh and inject a malicious curl | bash command into the clipboard, prompting developers to run it....

New SysUpdate Variant Malware Discovered, Decryption Tool for Linux C2 Traffic Released
Researchers at LevelBlue identified a new SysUpdate variant targeting Linux systems, packaged as a packed ELF64 binary that mimics a system service. The malware employs a custom, multi‑layered symmetric cipher to encrypt its command‑and‑control traffic across several protocols. By emulating...

New Phishing Campaign Exploits Booking.com Partners, Targets Customers in Multi-Stage Fraud Scheme
A coordinated phishing campaign is exploiting Booking.com’s partner platform to steal hotel staff credentials and then target guests with payment‑stealing lures. The operation uses a three‑stage chain: email phishing to hotel inboxes, a bespoke partner login kit to harvest credentials,...

Malicious Fork of Legitimate Triton App Discovered on GitHub, Exposing New Malware Threat
A malicious fork of the legitimate Triton macOS client was posted on GitHub, masquerading as an official release while embedding a Windows‑only malware payload. The attacker, operating under the account “JaoAureliano,” used a deceptive README and raw asset links to...
.webp?ssl=1)
LockBit 5.0 Emerges: Cross-Platform Ransomware Now Targeting Windows, Linux, and ESXi Systems
LockBit has released version 5.0, a cross‑platform ransomware that encrypts Windows, Linux and VMware ESXi systems with a single code base. The new variant uses XChaCha20 and Curve25519 encryption, while the Windows build adds sophisticated anti‑forensic tricks such as ETW...

Lotus Blossom Hackers Breach Official Notepad++ Hosting Infrastructure
Between June and December 2025, the state‑sponsored Lotus Blossom group compromised the shared hosting provider that delivered Notepad++ updates, turning the popular text editor into a covert espionage conduit. By exploiting weaknesses in the older WinGUp updater, attackers redirected update...

Hackers Abuse ClawHub Skills to Evade VirusTotal via Social Engineering
Hackers have revamped ClawHub skill attacks by removing embedded malware and instead using clean SKILL.md files that lure users to counterfeit OpenClawCLI download sites. The malicious payload is hosted on look‑alike domains and fetched via an obfuscated bash command, allowing...

APT Hackers Abuse Trusted Edge Services to Stealthily Deploy Malware
APT groups, largely China‑linked, are shifting attacks from protected endpoints to edge infrastructure such as firewalls, routers and IoT devices. Taiwan emerged as the most targeted APAC region, logging 173 incidents and serving as a testing ground for new tools....

Vortex Werewolf Targets Organizations With Tor-Enabled RDP, SMB, SFTP, and SSH Backdoors
Vortex Werewolf, also known as SkyCloak, is a threat cluster that has been delivering Tor‑enabled remote‑access backdoors to Russian government and defense organizations through sophisticated Telegram‑themed phishing campaigns. Victims are lured to counterfeit Telegram login pages that harvest phone numbers,...

Cybersquatting Attacks Exploit Trusted Brands to Steal Customer Data and Spread Malware
Cybercriminals are increasingly exploiting cybersquatting to clone trusted brands, harvest customer credentials, and deliver malware. Research from SecPod shows a 19‑fold surge in malicious domain registrations between late 2024 and mid‑2025, with more than 99 % used for phishing or malware...

New Telegram Phishing Scam Hijacks Login Flow to Steal Fully Authorized User Sessions
Cyber‑intelligence firm CYFIRMA uncovered a new Telegram phishing campaign that hijacks the platform’s QR‑code and manual login flows. Attackers register their own Telegram API credentials and relay victim‑supplied phone numbers, OTPs, or QR scans to create fully authorized sessions on...

FvncBot Targets Android Users, Exploiting Accessibility Services for Attacks
A new Android banking trojan named FvncBot was first seen in late 2025, masquerading as a security app from Poland’s mBank. The malware uses a two‑stage loader, both obfuscated with the APK0day cryptor, to install an unencrypted payload that hijacks...
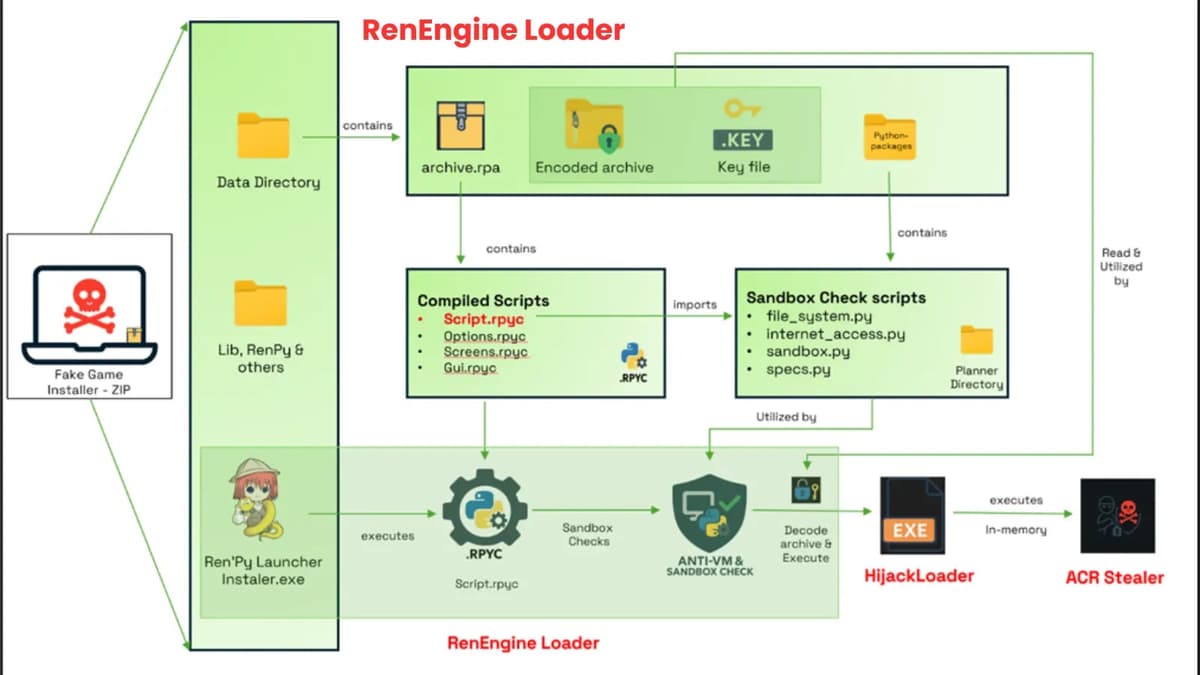
RenEngine Loader Deploys Stealthy Multi-Stage Execution to Bypass Security Measures
RenEngine Loader, a new malware family, embeds malicious code in legitimate Ren’Py game launchers used for cracked games. Since its emergence in April 2025, it has infected over 400,000 users, adding roughly 5,000 new victims each day, primarily in India,...
New Wave of Odyssey Stealer Targets macOS Users in Active Cyberattack Campaign
A new wave of Odyssey Stealer is actively targeting macOS users across more than twenty countries, expanding far beyond its initial foothold in the United States and Western Europe. The malware is delivered through fake CAPTCHA pages that mimic legitimate...

CentOS 9 Security Flaw Enables Privilege Escalation – PoC Released
A critical use‑after‑free vulnerability has been discovered in the `sch_cake` packet scheduler of the CentOS 9 Linux kernel. The flaw lets a local user trigger memory corruption and execute arbitrary code with root privileges, as demonstrated by a publicly released proof‑of‑concept....

Phishing and OAuth Token Vulnerabilities Lead to Full Microsoft 365 Breach
Researchers identified two medium‑severity flaws—a publicly accessible email API endpoint and verbose error handling that discloses OAuth tokens—that can be combined to launch authenticated phishing campaigns inside Microsoft 365 tenants. By exploiting the open relay, attackers send messages that appear to...

Spam Campaign Distributes Fake PDFs, Deploys Remote Monitoring Tools for Ongoing Access
A spam campaign is distributing PDFs that appear to be Adobe Acrobat updates, but the attachment redirects users to a spoofed download page that installs legitimate Remote Monitoring and Management (RMM) tools such as TrustConnect and Datto RMM. By leveraging signed...

TP-Link Vulnerabilities Let Hackers Take Full Control of Devices
TP‑Link disclosed nine critical authenticated command‑injection flaws in its Archer BE230 v1.2 router firmware, each assigned a separate CVE and scoring 8.5‑8.6 on the CVSS v4.0 scale. The vulnerabilities affect web, VPN, cloud, and configuration modules, allowing attackers with high‑privilege access to...

Interlock Ransomware Exploits Zero-Day in Gaming Anti-Cheat Driver to Disable EDR, AV
Interlock ransomware has added a zero‑day exploit in a gaming anti‑cheat driver (CVE‑2025‑61155) to its arsenal, deploying a signed kernel driver called UpdateCheckerX64.sys. The new BYOVD tool, dubbed Hotta Killer, creates a demand‑start service and uses DeviceIoControl to terminate security...

Supply Chain Attack Exploits Notepad++ Update Mechanism to Push Targeted Malware
A sophisticated supply‑chain attack hijacked Notepad++'s update mechanism after a hosting‑provider breach, remaining active from June 2025 to December 2025. Attackers rotated command‑and‑control servers and deployed three distinct infection chains that delivered Cobalt Strike beacons and a custom Chrysalis backdoor. The...
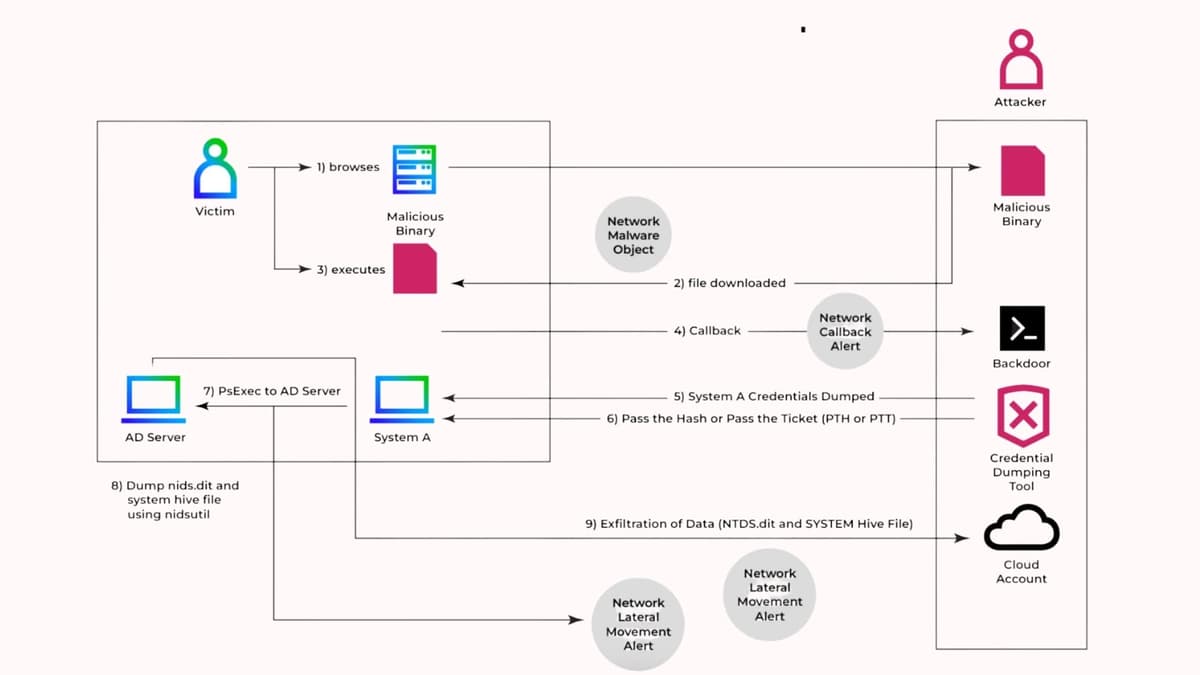
Hackers Exfiltrate NTDS.dit File, Gain Full Control of Active Directory Environments
Threat actors are increasingly targeting the NTDS.dit database, the core repository of Active Directory credentials and configuration, to gain unrestricted domain access. By creating Volume Shadow Copies and leveraging native tools such as ntdsutil, SecretsDump, and Mimikatz, attackers can extract...

Chollima APT Hackers Weaponize LNK Files to Deploy Sophisticated Malware
In March 2025, North Korean‑linked APT37 (Ricochet Chollima) launched “Operation: ToyBox Story,” a spear‑phishing campaign targeting activists focused on North Korean affairs. The emails delivered Dropbox links to ZIP archives containing malicious LNK shortcut files that execute hidden PowerShell commands, creating...

Malicious Google Play App With 50K+ Downloads Spreads Anatsa Banking Trojan
A malicious Android app posing as a document reader amassed over 50,000 downloads on Google Play before being removed. The app functioned as a dropper for the Anatsa banking trojan, which can harvest credentials and execute unauthorized transactions. ThreatLabz identified...

Notepad++ Attack Breakdown Reveals Sophisticated Malware and Actionable IoCs
The Chinese APT group Lotus Blossom has been linked to a sophisticated supply‑chain attack on the Notepad++ distribution platform. Attackers delivered a custom backdoor dubbed Chrysalis via a malicious NSIS‑based update.exe that sideloaded a forged Bitdefender Submission Wizard DLL into...

TAMECAT PowerShell Backdoor Targets Edge and Chrome: Login Credentials At Risk
Iranian state‑sponsored group APT42 deployed a new PowerShell‑based backdoor named TAMECAT, targeting Microsoft Edge and Google Chrome to harvest saved login credentials. The malware is delivered via a VBScript downloader that checks for antivirus products before fetching an AES‑encrypted loader...

Threat Actors Hide Behind School-Themed Domains In Newly Uncovered Bulletproof Infrastructure
Researchers uncovered a sophisticated traffic‑distribution system (TDS) that leverages education‑themed domains to deliver phishing pages, scams, and malware. The infrastructure is hosted on bullet‑proof providers in AS202015 (HZ Hosting) and shares WHOIS details such as oreshnik@mailum.com and Regway nameservers. A...

Sophisticated Malware Lurks In Open VSX Extension With 5,066 Downloads
Annex Security uncovered a malicious VS Code extension in the Open VSX registry that pretended to be the Angular Language Service, amassing 5,066 downloads before activating sophisticated malware. The extension decrypts a payload with AES‑256‑CBC, contacts a Solana blockchain address for command‑and‑control,...
Attackers Weaponize Microsoft 365 Outlook Add-Ins to Quietly Exfiltrate Email Data
Researchers have uncovered a stealthy data‑theft method called “Exfil Out&Look” that abuses Microsoft 365 Outlook Web add‑ins to siphon email content. The technique leverages minimal‑permission manifests that execute on the OnMessageSend event, silently fetching email bodies and forwarding them via a fetch()...

Open Directory Exposure Leaks BYOB Framework Across Windows, Linux, and macOS
The Hunt.io team uncovered an openly accessible directory on IP 38.255.43.60 that hosts the complete BYOB (Build Your Own Botnet) framework, a sophisticated post‑exploitation tool targeting Windows, Linux and macOS. The infrastructure includes five C2 nodes across the United States, Singapore...

BlackIce Introduced as Container-Based Red Teaming Toolkit for AI Security Testing
Databricks unveiled BlackIce, an open‑source Docker‑based toolkit that bundles 14 leading AI security utilities into a single, reproducible environment. By containerizing both static command‑line tools and dynamic Python‑driven frameworks, BlackIce removes the setup friction and dependency clashes that have long...

Fake “Mac Cleaner” Campaign Uses Google Ads to Redirect Users to Malware
Cybercriminals are leveraging Google Search Ads to distribute macOS malware by directing users searching for “mac cleaner” to counterfeit Apple‑styled landing pages. The ads, hosted on compromised Google Ads accounts, redirect to Google Apps Script pages that decode Base64 payloads...

Python-Based PyRAT Emerges as Cross-Platform Threat With Advanced Remote Access Capabilities
A new Python‑based Remote Access Trojan, dubbed PyRAT, has been identified as a cross‑platform threat capable of compromising both Windows and Linux systems. The malware leverages Python’s portability, compiling into ELF and PE binaries, and employs lightweight persistence mechanisms—XDG autostart...

Matanbuchus Malware Evolves to Bypass AV Defenses by Swapping Core Components
Matanbuchus, a C++‑based downloader sold as Malware‑as‑a‑Service since 2020, has evolved into a modular backdoor platform with its latest 3.0 release featuring heavy obfuscation, ChaCha20‑encrypted strings, and Protobuf‑encoded C2 traffic. The malware leverages DLL sideloading through a malicious HRUpdate.exe MSI...

Cal.com Broken Access Controls Lead to Account Takeover and Data Exposure
Cal.com, an open‑source scheduling platform, patched critical broken‑access‑control vulnerabilities that allowed attackers to hijack accounts and expose booking data. The flaws included an authentication bypass in the organization signup flow that let attackers take over any user by using an...

ESkimming Attacks Surge with Evolving Tactics and Ongoing Recovery Challenges
Source Defense’s year‑long study of 550 e‑commerce sites shows e‑skimming remains a chronic problem, with 18 % of sites still infected after twelve months. Over half of the persistent infections (57 %) have evolved into new script variants, indicating attackers adapt once...

Critical IDIS IP Camera Vulnerability Allows Full Computer Compromise with One-Click Exploit
IDIS Cloud Manager’s Windows viewer contains a critical flaw (CVE‑2025‑12556) that lets attackers trigger remote code execution with a single click. The vulnerability stems from CWGService.exe accepting unsanitized command‑line arguments via a local WebSocket, which are passed to the Chromium...

Cybercriminals Exploit Canadians’ Dependence on Digital Services in Widespread Attacks
Canadian cybercriminals are running a large‑scale phishing campaign that impersonates government agencies, Air Canada and Canada Post, using the PayTool phishing‑as‑a‑service platform. The operation distributes SMS alerts and malicious ads that direct victims to spoofed portals hosted on shared IP...

Chinese National Sentenced to 46 Months for Laundering Millions Stolen From U.S. Investors
A Chinese national, Jingliang Su, received a 46‑month federal prison sentence for laundering roughly $36.9 million stolen from U.S. investors in a cryptocurrency fraud scheme run from Cambodia. The court ordered him to pay nearly $27 million in restitution and highlighted a...

Attackers Hijack GitHub Desktop Repo to Spread Malware via Official Installer
Threat actors exploited a design flaw in GitHub’s fork architecture to distribute malware masquerading as the official GitHub Desktop installer. By forking the repository and altering the README download link, they created malicious commits that appear under the official namespace,...

G_Wagon NPM Package Exploits Users to Steal Browser Credentials with Obfuscated Payload
Security researchers identified a malicious npm package, ansi-universal-ui, that houses the G_Wagon infostealer. The package pretends to be a UI component library but delivers a Python‑based payload that extracts browser passwords, cryptocurrency wallets, cloud credentials, and messaging tokens. Over ten...

ShinyHunters Group Targets Over 100 Enterprises, Including Canva, Atlassian, and Epic Games
A newly identified threat supergroup called SLSH, formed by Scattered Spider, LAPSUS$ and ShinyHunters, is targeting more than 100 high‑profile enterprises through sophisticated human‑led vishing attacks on Single Sign‑On platforms, especially Okta. The attackers use a live phishing panel to...

Hackers Exploit SEO Poisoning to Target Users Seeking Legitimate Tools
Hackers are leveraging SEO poisoning to push malicious ZIP archives that contain BAT scripts masquerading as legitimate tools. The fraudulent pages rank highly in search results, directing users to fake repositories where the scripts contact command‑and‑control servers and download remote...

Lazarus Hackers Target European Drone Manufacturers in Active Campaign
North Korean state‑sponsored Lazarus group launched a new Operation DreamJob campaign targeting European defense firms that build uncrewed aerial vehicles. The attackers used fake job offers to distribute trojanized PDFs that install the ScoringMathTea RAT and BinMergeLoader loader. Malware leverages...
NetSupport Manager 0-Day Vulnerabilities Enable Remote Code Execution
Security researchers uncovered two critical 0‑day flaws—CVE‑2025‑34164 and CVE‑2025‑34165—in NetSupport Manager versions up to 14.10.4.0. The bugs reside in an undocumented broadcast feature and can be chained to achieve unauthenticated remote code execution by corrupting heap memory and reading stack...