New Phishing Attack Exploits Vercel to Host and Deliver Remote Access Malware
A sophisticated phishing campaign has been leveraging Vercel's *.vercel.app subdomains since November 2025 to deliver remote‑access malware. The attackers disguise malicious pages as invoice portals or document viewers, then conditionally serve a signed GoTo Resolve installer after fingerprinting the victim’s browser. Information gathered is relayed to a Telegram channel, which decides whether to release the payload, allowing the threat to evade sandboxes and security researchers. Cloudflare reports tens of thousands of detections in the past month, highlighting the campaign’s scale and persistence.

TrustAsia Pulls 143 Certificates Following Critical LiteSSL ACME Vulnerability
TrustAsia revoked 143 SSL/TLS certificates after uncovering a critical vulnerability in its LiteSSL ACME service. The flaw allowed domain‑validation data to be reused across different ACME accounts, enabling unauthorized issuance of wildcard certificates. The issue stemmed from a logic error...
NVIDIA CUDA Toolkit Flaw Allows Command Injection, Arbitrary Code Execution
NVIDIA released a patch on January 20 2026 for four critical vulnerabilities in its CUDA Toolkit, affecting Nsight Systems and Nsight Visual Studio tools. The flaws enable local command injection and arbitrary code execution through inadequate input validation and insecure DLL loading,...

BIND 9 Flaw Lets Attackers Crash Servers With Malicious DNS Records
A critical vulnerability identified as CVE‑2025‑13878 affects BIND 9 DNS servers, allowing remote attackers to crash the named process using malformed BRID or HHIT records. The flaw impacts several stable branches—9.18.40‑9.18.43, 9.20.13‑9.20.17, and 9.21.12‑9.21.16—and carries a CVSS v3.1 score of 7.5,...

PNB MetLife Phishing Attack: Multi-Stage Scheme Steals Data, Triggers UPI Payments
A sophisticated multi‑stage phishing campaign is targeting PNB MetLife insurance customers through mobile‑optimized fake payment‑gateway pages hosted on free EdgeOne Pages. The first stage harvests personal details and forces fraudulent UPI payments using dynamically generated QR codes and clipboard manipulation. A...

JA3 Fingerprinting Tool Exposes Attackers’ Infrastructure
JA3 fingerprinting, once considered outdated, is re‑emerging as a potent tool for tracking malicious infrastructure. By hashing TLS ClientHello parameters, JA3 creates a stable identifier that persists across malware variants. Recent threat‑intel investigations linked specific JA3 hashes to Remcos RAT,...

New ClickFix Campaign Exploits Fake Verification Pages to Hijack Facebook Sessions
A new ClickFix campaign is hijacking Facebook accounts by luring users into fake verification and appeal pages that instruct them to extract live session tokens (c_user and xs) from their browsers. The operation spans 115 phishing pages hosted on abuse‑friendly...

Malicious PyPI Package Impersonates Sympy-Dev, Targeting Millions of Users
A malicious PyPI package named sympy-dev impersonates the popular SymPy library, using typosquatting to lure developers into installing it. Four versions (1.2.3‑1.2.6) were released on Jan 17 2026 and amassed over 1,000 downloads within the first day. The package embeds a memory‑only...

ClearFake Malware Exploits Proxy Execution to Run Malicious PowerShell Commands via Trusted Windows Feature
ClearFake, a JavaScript‑based malware distribution framework, has upgraded its evasion tactics by abusing the legitimate Windows script SyncAppvPublishingServer.vbs to execute hidden PowerShell commands via proxy execution. The campaign retrieves multi‑stage payloads from smart contracts on the BNB Smart Chain testnet,...

ErrTraffic Exploits Visual Page Breaks to Fuel ClickFix Attacks, Rebranding Exploits as “GlitchFix”
ErrTraffic is a traffic‑distribution system that powers ClickFix social‑engineering attacks by deliberately corrupting website visuals—a technique dubbed “GlitchFix.” When a victim visits a compromised page, the script distorts text, CSS and cursor movement before presenting a fake update prompt that...

Magecart Hack Injects JavaScript to Steal Online Payment Data
Security researchers have uncovered a new Magecart‑style campaign that injects obfuscated JavaScript from cc-analytics.com/app.js into e‑commerce checkout pages. The script captures credit‑card numbers and billing details, then exfiltrates them to attacker‑controlled servers at pstatics.com via XMLHttpRequest POSTs. Infrastructure analysis reveals...
.webp?ssl=1)
Threat Actors Exploit LinkedIn for RAT Delivery in Enterprise Networks
A new phishing campaign is using LinkedIn private messages to deliver remote access trojans to enterprise networks. Attackers send self‑extracting WinRAR archives that contain a legitimate PDF reader, a malicious DLL, and a portable Python interpreter. The DLL is loaded...
.webp?ssl=1)
Apache Airflow Flaws Expose Sensitive Workflow Data to Potential Attackers
Apache Airflow released version 3.1.6 to fix two credential‑exposure flaws (CVE‑2025‑68675 and CVE‑2025‑68438). The first flaw logged proxy URLs with embedded usernames and passwords, while the second allowed unmasked API keys and tokens in the Rendered Templates UI. Both issues affect...
%20(1).webp?ssl=1)
OPNsense 25.7.11 Enhances Network Visibility With Host Discovery Feature
OPNsense 25.7.11 introduces a native host discovery service that automatically resolves and stores MAC addresses for IPv4 and IPv6 hosts. The feature feeds live data to MAC‑based firewall aliases and captive‑portal client tracking, improving policy accuracy and device visibility. IPv6...
.webp?ssl=1)
TP-Link Router Flaw Enables Authentication Bypass Through Password Recovery Mechanism
TP‑Link disclosed a high‑severity authentication bypass (CVE‑2026‑0629) affecting its VIGI security‑camera line. The flaw exploits the password‑recovery feature, allowing any LAN‑connected attacker to reset admin credentials without verification. With a CVSS v4.0 score of 8.7, the vulnerability grants full control over...

Discord Exploited to Spread Clipboard Hijacker Stealing Cryptocurrency Funds
Security firm CloudSEK’s STRIKE team uncovered a new cryptocurrency‑theft campaign that leverages Discord communities to distribute a clipboard‑hijacking trojan dubbed Pro.exe. The malware, attributed to the RedLineCyber group, monitors Windows clipboard for wallet addresses and silently replaces them with attacker‑controlled...
Cloudflare Zero-Day Flaw Allows Attackers to Bypass Security and Access Any Host
A critical zero‑day in Cloudflare’s Web Application Firewall allowed attackers to bypass all WAF rules by targeting the ACME certificate‑validation path. Researchers from FearsOff demonstrated that arbitrary requests to /.well-known/acme-challenge/ could reach origin servers, exposing sensitive endpoints in Spring Boot,...

Visual Studio Code Abused in Sophisticated Multistage Malware Attacks
A new campaign dubbed Evelyn Stealer leverages compromised Visual Studio Code extensions, such as the Bitcoin Black theme and Codo AI assistant, to deliver a multi‑stage malware chain. The first‑stage payload uses DLL hijacking of the Lightshot utility to execute PowerShell scripts that...

Cybercriminals Impersonate Malwarebytes to Steal User Credentials
A short‑lived campaign from January 11‑15 2026 masqueraded as Malwarebytes installers to deliver infostealers. Attackers distributed ZIP archives named like “malwarebytes‑windows‑github‑io‑X.X.X.zip” that contain a legitimate EXE loader, a malicious CoreMessaging.dll, and a benign‑looking TXT pivot file. The DLL is sideloaded, granting code...

Attackers Rerouted Employee Pay Without Breaching IT Systems
An attacker bypassed technical defenses by socially engineering help‑desk staff to reset passwords and re‑enroll MFA, gaining legitimate access to payroll accounts. Using the compromised credentials, the fraudster altered direct‑deposit details and diverted salaries from three employees without triggering alerts....

PDFSIDER Malware Actively Exploited to Evade Antivirus and EDR Defenses
Researchers have uncovered PDFSIDER, a backdoor malware that exploits DLL side‑loading in the legitimate PDF24 Creator application to evade endpoint detection and response tools. The malicious payload is delivered via spear‑phishing ZIP archives, signed with valid certificates, and replaces the...

Argus: Python-Based Recon Toolkit Aims to Boost Security Intelligence
Argus v2.0, a Python‑based reconnaissance toolkit, launches with 135 specialized modules unified under a professional command‑line interface. The overhaul adds multi‑threaded execution, over 25 CLI commands, and four deployment options—including pip, Docker, script, and direct Python. It integrates major threat‑intelligence...

Researchers Hijack Hacker Domain Using Name Server Delegation
Infoblox researchers exploited a DNS misconfiguration called lame nameserver delegation to seize control of abandoned hacker domains. Within hours they intercepted over 57 million push‑notification logs from roughly 120 misconfigured domains, capturing traffic at 30 MB per second. The data exposed a...

Threat Actors Abuse Browser Extensions to Deliver Fake Warning Messages
Huntress researchers uncovered a malicious Chrome extension, NexShield, that masquerades as the legitimate uBlock Origin Lite ad blocker. The extension installs a delayed denial‑of‑service loop, then displays a fake crash warning that tricks users into running a PowerShell command which...
.webp?ssl=1)
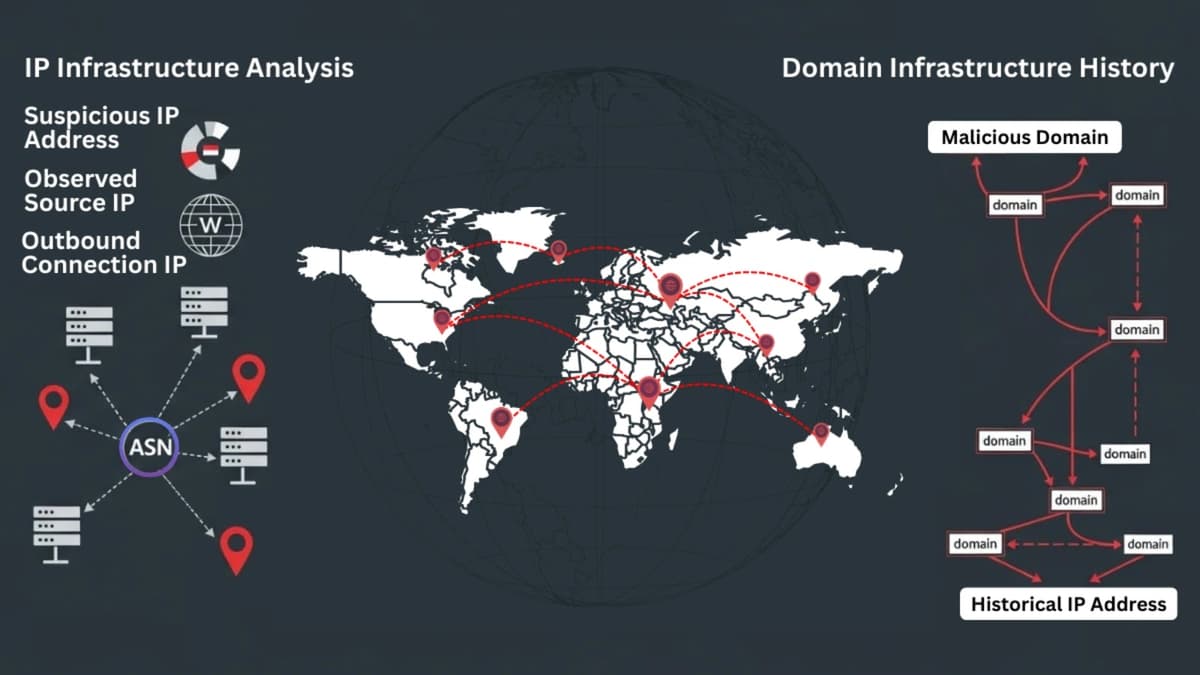
How Security Teams Use IP Location and DNS History In Cybercrime Investigation
Security teams start cybercrime investigations with a single alert—often a suspicious IP or login—and quickly need context beyond raw logs. By enriching that alert with IP location data and DNS history, analysts can identify geographic anomalies, hosting providers, and past...

Critical XSS Vulnerabilities in Meta Conversion API Enable Zero-Click Account Takeover
Security researchers identified two critical cross‑site scripting flaws in Meta’s Conversions API Gateway that enable zero‑click Facebook account takeover. The client‑side XSS stems from improper postMessage origin validation, while a stored XSS arises from unsafe string concatenation in the backend...

Best Security Awareness Training Platforms For 2026
The 2026 roundup identifies the ten leading security awareness training platforms, highlighting AI‑driven phishing simulations, micro‑learning, gamification, and comprehensive compliance reporting. Solutions such as KnowBe4, Proofpoint, and Cofense demonstrate measurable risk reductions, with industry benchmarks showing up to an 80%...

Promptware Kill Chain – Five-Step Kill Chain Model For Analyzing Cyberthreats
The Promptware Kill Chain introduces a five‑step framework that treats malicious prompts and poisoned content as a distinct class of AI malware. It maps the lifecycle of attacks on large language model applications from initial access through privilege escalation, persistence,...

GoLogin vs MultiLogin vs VMLogin – What’s the Anti-Detect Browsers Difference?
Anti-detect browsers let users conceal fingerprints and manage multiple online identities. The article compares three leading solutions—GoLogin, MultiLogin, and VMLogin—detailing their core features, user bases, and pricing models. GoLogin distinguishes itself with cloud‑based profile storage, multilingual support, and a seven‑day...
%20(1).webp?ssl=1)
Spring CLI Vulnerability Allows Attackers to Execute Commands on User Systems
A command‑injection flaw (CVE‑2026‑22718) has been discovered in the Spring CLI VS Code extension, affecting all versions up to 0.9.0. The vulnerability allows an attacker with local access to execute arbitrary commands, earning a medium severity rating and a CVSS score...
.webp?ssl=1)
Multiple Elastic Vulnerabilities Could Lead to File Theft and DoS
Elastic has issued urgent patches for four critical Kibana vulnerabilities spanning versions 7.x through 9.2.3. The most severe, CVE‑2026‑0532, combines SSRF and file disclosure, allowing authenticated attackers to exfiltrate credentials. Three medium‑severity flaws can cause denial‑of‑service through resource exhaustion in...

PowerShell-Driven Multi-Stage Windows Malware Using Text Payloads
Researchers have uncovered the SHADOW#REACTOR campaign, a multi‑stage Windows malware chain that starts with an obfuscated VBS script and escalates through a PowerShell stager, text‑only payloads, and a .NET Reactor‑protected loader. The loader reflectively injects a Remcos RAT payload entirely...

HoneyTrap: Outsmarting Jailbreak Attacks on Large Language Models
Researchers from Shanghai Jiao Tong University, UIUC and Zhejiang University introduced HoneyTrap, a deceptive‑defense framework that counters multi‑turn jailbreak attacks on large language models. The system employs four specialized defensive agents to mislead attackers, prolong interactions, and drain computational resources...
Android Banking Malware deVixor Actively Targeting Users with Ransomware Capabilities.
Android banking trojan deVixor, active since October 2025, is distributing through counterfeit automotive‑sale websites targeting Iranian users. The malware harvests SMS OTPs, banking credentials, and cryptocurrency exchange data, and can remotely lock devices with a ransomware command demanding 50 TRX. Its...

Threat Actors Exploit RMM Tools Through Weaponized PDF Files
Threat actors are leveraging weaponized PDF attachments to install legitimate Remote Monitoring and Management (RMM) tools such as Syncro, SuperOps, NinjaOne, and ScreenConnect. The campaign, uncovered by ASEC, began with deceptive PDFs that display error messages or images, prompting users...
%20(1)%20(1).webp?ssl=1)
SAP January 2026 Security Patch Day Fixes Critical Injection and RCE Flaws
On January 13, 2026 SAP issued its monthly Security Patch Day, releasing 17 security notes that address 15 vulnerabilities across its product portfolio. Four critical‑severity flaws—CVE‑2026‑0501 (SQL injection in S/4HANA General Ledger), CVE‑2026‑0500 (remote code execution in Wily Introscope), and...

DPRK Hackers Earn $600M Posing as Remote Workers
North Korean state‑sponsored hackers are masquerading as remote IT workers, generating up to $600 million annually for the regime. They infiltrate Western firms by securing legitimate remote positions or creating fake front‑company job postings, then use living‑off‑the‑land techniques to embed persistent...

Top 5 Best Free VPN for 2026 to Protect Your Anonymity on the Internet
The article lists the top five free VPN services projected for 2026, emphasizing their ability to safeguard anonymity during activities like torrenting. It highlights common pitfalls of free VPNs, such as data leaks, bandwidth limits, and ad injection. Each recommended...

Top 5 Best Cyber Attack Prevention Methods for Small Businesses With Breach & Attack Simulation
Hackers now target small businesses, accounting for 43% of attacks, making cyber‑attack prevention a critical priority. Affordable cloud‑based antimalware and firewall services, along with Breach and Attack Simulation (BAS) platforms like Cymulate, give SMBs enterprise‑level protection. The article outlines five...

Malicious Chrome Extension Steals Wallet Credentials, Enables Automated Trading Abuse
Socket’s Threat Research Team uncovered a malicious Chrome extension, MEXC API Automator, that silently creates MEXC exchange API keys with withdrawal permissions. The extension exfiltrates the keys to a hard‑coded Telegram bot, enabling attackers to programmatically trade and drain wallets....

Web3 Dev Environments Hit by Fake Interview Software Scam
Web3 developers are being targeted by a new inbound scam where attackers pose as legitimate hiring firms on sites like youbuidl.dev. They lure candidates with senior‑level job postings and then require the download of a fake interview or coding‑test application....

India Remains Top Target for Mobile Attacks as Threats Surge 38%
India has become the world’s leading target for mobile cyber‑attacks, recording a 38% year‑over‑year surge and now representing 26% of global mobile malware traffic. Zscaler’s ThreatLabz report identified 239 malicious Android apps downloaded 42 million times, with retail and hospitality sectors...

PoC Released for Atarim Plugin Auth Bypass Vulnerability
A proof‑of‑concept for CVE‑2025‑60188 reveals a critical authentication bypass in the Atarim WordPress plugin. The flaw stems from using the publicly exposed site_id as the HMAC‑SHA256 secret, allowing attackers to forge valid admin requests. Exploit code published by researcher m4sh‑wacker...

Massive Instagram Data Breach Exposes Personal Details of 17.5 Million Users
A dark‑web marketplace is selling personal data from 17.5 million Instagram accounts, marking one of the largest social‑media breaches to date. Malwarebytes first reported the leak on X, confirming that usernames, email addresses, phone numbers and partial location data are being...

Cybercriminals Exploit Maduro Arrest News to Spread Backdoor Malware
Cybercriminals are exploiting news of Venezuelan President Nicolás Maduro’s alleged arrest to distribute a backdoor malware via spear‑phishing ZIP attachments. The ZIP contains a weaponized KuGou executable that loads a malicious DLL through DLL search‑order hijacking, creates a hidden Technology360NB...

Fog Ransomware Targets U.S. Organizations via Compromised VPN Credentials
Arctic Wolf Labs identified a new ransomware variant called Fog targeting U.S. organizations, primarily in education (80%) and recreation (20%) sectors. The attackers gained entry through compromised VPN credentials from two vendors and quickly escalated privileges using pass‑the‑hash, PsExec, and credential‑stuffing...

XRAT Malware Targets Windows Users via Fake Adult Game
AhnLab Security Intelligence Center uncovered a campaign that disguises the open‑source xRAT (QuasarRAT) remote‑access trojan as a fake adult game on Korean web‑hard services. The ZIP archive contains a Game.exe launcher that first runs a legitimate game stub, then copies...

50 Best Free Cyber Threat Intelligence Tools – 2026
The article curates a list of the 50 best free cyber‑threat‑intelligence (CTI) tools available in 2026, spanning data‑feeds, analysis platforms, automation frameworks, and IOC‑parsers. It highlights open‑source projects such as MISP, OpenCTI, and IntelMQ, as well as real‑time feeds like...

The Role of Initial Access Markets in Ransomware Campaigns Targeting Australia and New Zealand
The 2025 Threat Landscape Report shows a sharp rise in initial‑access sales targeting Australia and New Zealand, with 92 documented compromised‑access listings. Retail accounts for roughly one‑third of incidents, while BFSI and professional services together make up over half. The market...
New DocuSign-Themed Phishing Scam Delivers Stealth Malware to Windows Devices
Researchers have uncovered a sophisticated phishing campaign that impersonates DocuSign to deliver the Vidar information‑stealing malware to Windows computers. The attack uses a look‑alike domain and a fake installer signed with a legitimate Chinese code‑signing certificate to bypass reputation filters....