
Use of XMRig Cryptominer by Threat Actors Expanding: Expel
XMRig, an open‑source Monero miner, is increasingly weaponized by threat actors across Windows, Linux, Kubernetes and AWS environments. Recent campaigns have leveraged the high‑severity React2Shell exploit and UPX‑packed binaries to spread the miner via game torrents and commodity malware. Expel’s Ben Nahorney likens unauthorized cryptominers to weeds, warning they reveal deeper security gaps. The global crypto‑mining market is projected to reach $3.12 billion in 2026, fueling continued abuse.
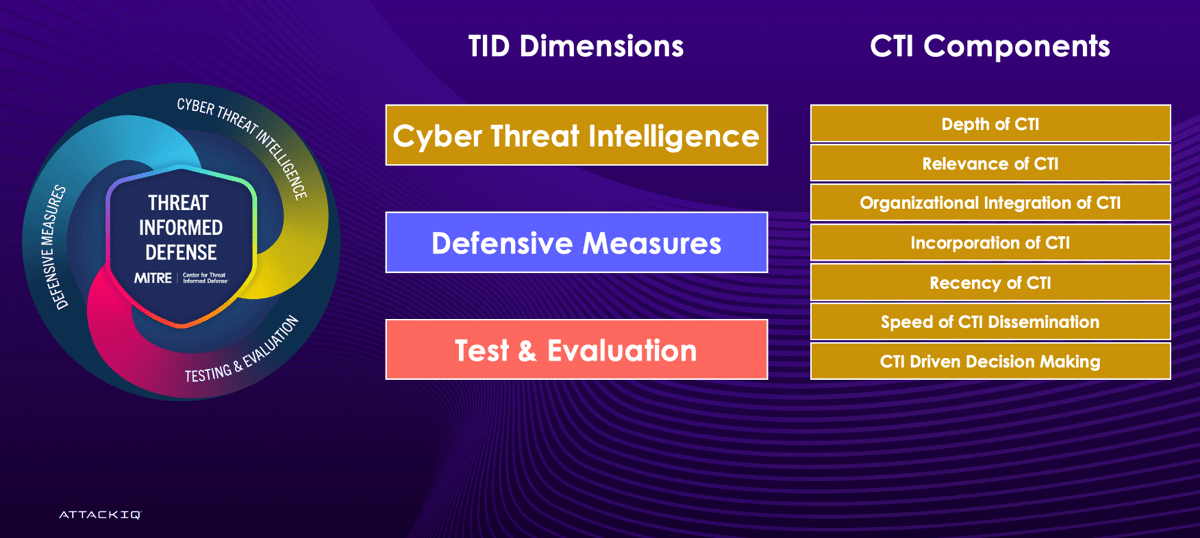
INFORM 2026: MITRE’s Updated Threat-Informed Defense Maturity Model Explained
MITRE’s Center for Threat‑Informed Defense released a major update to its INFORM maturity model, incorporating two years of field feedback and new partner input. The revision introduces revamped assessment questions, a timeliness factor, and an impact‑vs‑complexity recommendation matrix. INFORM now...
![Sectigo New Public Roots and Issuing CAs Hierarchy [2025 Migration Guide]](/cdn-cgi/image/width=1200,quality=75,format=auto,fit=cover/https://certera.com/blog/wp-content/plugins/wp-postratings/images/stars/rating_on.gif)
Sectigo New Public Roots and Issuing CAs Hierarchy [2025 Migration Guide]
Sectigo is retiring its legacy multi‑purpose root and intermediate CAs in favor of single‑purpose public roots, with a hard migration deadline of January 1 2026. Browsers will cease to trust certificates issued under the old chains, causing security warnings, broken HTTPS, and...

CCPA Compliance Checklist for 2026: What You Need to Know
The California Consumer Privacy Act (CCPA) is entering a pivotal phase in 2025‑26 as inflation‑adjusted thresholds raise applicability and new rules target automated decision‑making and cybersecurity governance. Organizations must continuously reassess scope, maintain precise data inventories, and embed repeatable rights‑fulfillment...

How Does Agentic AI Adapt to Changing Security Needs?
Organizations increasingly rely on machine identities, or non‑human identities (NHIs), to authenticate services in cloud environments. Effective NHI management—covering discovery, classification, threat detection, and remediation—delivers risk reduction, compliance, and operational efficiency. Agentic AI platforms enable dynamic policy adaptation, cross‑department collaboration,...

NDSS 2025 – ReThink: Reveal The Threat Of Electromagnetic Interference On Power Inverters
Researchers from Zhejiang University presented at NDSS 2025 a study exposing electromagnetic interference (EMI) threats to photovoltaic (PV) power inverters. They found that current and voltage sensors inside inverters are vulnerable to EMI at frequencies of 1 GHz or higher despite...

135% Surge: Inside the Holiday Bot Attacks of December 2025
In December 2025, malicious bot traffic surged 135% year‑over‑year, turning the holiday season into a cyber‑fraud hotspot. AI‑enhanced bots mimicked human browsing, generated high‑fidelity synthetic identities, and performed adaptive reconnaissance, making detection harder. The spike spanned vulnerability scanning, credential stuffing,...

Securing MCP Servers at Scale: How to Govern AI Agents with an Enterprise Identity Fabric
Enterprises are witnessing a rapid, uncontrolled rollout of Model Context Protocol (MCP) servers, with research showing 15.28% of a 10,000‑person workforce running an average of two servers each. Most deployments use full‑privilege personal access tokens, store credentials in plaintext, and...

When the Vendor Becomes the Customer: Building Internal Tools on an Agentic IAM Platform
Aembit’s test automation team built an internal dashboard to aggregate nightly test results from Qase.io and Slack, using the Aembit Workload IAM platform for runtime credential injection. By centralizing access policies, the Flask‑Vue service never handled static API keys, eliminating...

The Myth of Linux Invincibility: Why Automated Patch Management Is Key to Securing the Open Source Enterprise
The article debunks the myth that Linux’s inherent security makes it invulnerable, emphasizing that unpatched vulnerabilities are a growing risk for enterprises. Recent SANS and NVD data show rising ransomware, kernel exploits, and misconfigurations targeting Linux workloads. Automated, autonomous patch...

Attackers Don’t Guess and Defenders Shouldn’t Either
Enterprises now juggle an average of 45 cybersecurity products, yet breach reductions remain modest. Organizations that adopt continuous threat exposure management see far better outcomes than those relying on larger toolsets. The article argues that security teams often base defenses...

Zero-Knowledge Compliance: How Privacy-Preserving Verification Is Transforming Regulatory Technology
Zero-knowledge proofs are emerging as a privacy-preserving alternative to traditional compliance reporting, allowing firms to demonstrate regulatory adherence without revealing sensitive data. The article highlights adoption in finance, healthcare, and cybersecurity, noting that ZK‑SNARKs and ZK‑STARKs each offer distinct trade‑offs...

Stop Leaking API Keys: The Backend for Frontend (BFF) Pattern Explained
The article warns that any API key embedded in a frontend—web, mobile, or desktop—can be extracted, citing studies where over half of Android apps and 71 % of iOS apps leaked credentials. It recommends the Backend for Frontend (BFF) pattern, which...

The Boardroom Case for Penetration Testing
Cybersecurity has shifted from an IT concern to a material business risk, with 43% of UK firms reporting breaches in the past year and average losses of £3.29 million per incident. Boards now face pressure to demonstrate proactive risk management, and...

Embracing Uncertainty with AI Agents: Vulnerability Assessment Using Pydantic AI
The article demonstrates how AI agents built with Pydantic AI can use union‑type structured output to manage uncertainty in software vulnerability triage. By allowing the model to return either a detailed CriticalVulnerability record or an UnableToAssess response, agents avoid hallucinating fields...

How to Automate Safe Removal of Unused Code
Azul Intelligence Cloud now integrates with the open‑source OpenRewrite engine to automatically identify, flag, and safely remove unused or dead Java code. The solution combines runtime visibility from Azul Code Inventory with rule‑based refactoring, applying incremental annotations before code deletion....

Creating a Safe Learning Environment in K-12 Schools Without Adding Complexity
Today's K‑12 schools must protect students across physical spaces, emotional climate, psychological trust, and digital platforms. Research shows that safety directly boosts engagement, participation, and academic achievement. Districts ignoring any safety dimension risk lower attendance, disrupted instruction, and eroding community...

Bridging the Gap Between SRE and Security: A Unified Framework for Modern Reliability
Site reliability engineering (SRE) and security teams traditionally operate in separate silos, creating friction that stalls reliability initiatives and slows security controls. The article proposes a unified framework that merges reliability goals, risk budgets, joint observability, and integrated incident response...

Turning Data Security Into the Defining MSP Opportunity of 2026
Managed service providers (MSPs) are facing a market shift where cybersecurity is now a core expectation rather than an optional add‑on. Data Security Posture Management (DSPM) offers a continuous, automated view of sensitive data across tenants, turning security into a...

PayPal Email Scam: How It Worked Before the Fix
In December 2025 scammers hijacked PayPal’s subscription feature to generate authentic‑looking notification emails from service@paypal.com, inserting fake purchase details and a phone number to lure victims into callback scams. The abuse relied on a paused subscription triggering a legitimate “payment no...

Cybersecurity Predictions Are a Window Into a Vendor’s Roadmap and Business Priorities
Every November the cybersecurity sector launches a predictable wave of vendor‑authored prediction reports. While marketed as forward‑looking guidance, these pieces are timed to influence budgeting cycles and often reinforce the vendor’s existing value proposition or pre‑justify upcoming roadmap items. The...

NDSS 2025 – A Multifaceted Study On The Use of TLS And Auto-Detect In Email Ecosystems
Researchers from The Chinese University of Hong Kong presented a comprehensive analysis of TLS usage and auto‑detect features across email ecosystems at NDSS 2025. Testing 49 popular email clients revealed multiple vulnerabilities that enable covert security downgrades and credential leakage....