
Is Advanced AI Security Affordable for Small Businesses
Small businesses can adopt AI‑driven security without breaking the bank by choosing scalable, subscription‑based or open‑source solutions that integrate with existing infrastructure. Managing Non‑Human Identities (NHIs) with automated discovery and lifecycle tools further reduces breach risk and compliance costs. A strategic budget that prioritizes critical assets, preventive controls, and automation enables continuous protection while freeing resources for growth. Ongoing metrics, training, and a culture that blends technology with human vigilance ensure the security posture remains effective as threats evolve.

Can We Be Certain AI Keeps Cloud Data Secure
Non‑human identities (NHIs) are machine credentials—secrets, tokens, keys—essential for securing cloud environments. Organizations across finance, healthcare, and travel are shifting from point solutions like secret scanners to comprehensive NHI management platforms that cover discovery, classification, monitoring, and decommissioning. The article...

How AI Impacts the Cyber Market and The Future of SIEM
The rise of large‑language models is prompting a fundamental rethink of cyber‑security architectures, especially around Security Information and Event Management (SIEM). After decades of network‑centric prevention, data‑heavy SIEMs, and the EDR‑driven response era, AI has sparked a fifth phase where...

CCPA: Understanding How Synthetic Data Can Help Achieve Compliance
The California Consumer Privacy Act (CCPA) and its 2023 amendment, the CPRA, now affect any firm handling data from California residents, yet only 11 % of U.S. businesses are fully compliant. Compliance requires embedding consent management, sensitive‑data classification, audit trails, and...

NDSS 2025 – Vulnerability, Where Art Thou? Vulnerability Management In Android Smartphone Chipsets
The NDSS 2025 paper presents the first unified knowledge base of 3,676 Android smartphone chipset vulnerabilities spanning 437 chipset models and 6,866 phone models. It shows that many flaws are inherited across multiple chipset generations, contradicting the assumption that newer...

JWT Claims Explained: Complete Guide to Standard & Custom JWT Token Claims
The article outlines emerging quantum‑resistant frameworks for federated learning, highlighting how lattice‑based cryptography can slash communication overhead by roughly 20 percent while preserving privacy. It details new P2P tunnel architectures and Gopher Security’s post‑quantum encryption to thwart man‑in‑the‑middle attacks. Zero‑trust...

From Quantum Resilience to Identity Fatigue: Three Trends Shaping Print Security in 2026
Print devices are emerging as high‑risk edge nodes, with 2025 attacks exposing blind spots in firmware, default credentials, and network exposure. In 2026 organizations must adopt continuous, automated monitoring of printer fleets to curb IoT‑related breaches. Simultaneously, the rollout of...

Inside the Rise of the Always Watching, Always Learning Enterprise Defense System
Enterprises are abandoning perimeter‑based defenses in favor of zero‑trust architectures that continuously verify identity, intent, and behavior. AI‑driven detection platforms now ingest authentication logs, network flows, and telemetry to spot anomalies in real time. Automated remediation isolates suspicious devices or...

NDSS 2025 – “Who Is Trying To Access My Account?”
The NDSS 2025 paper investigates how users perceive risk‑based authentication (RBA) notifications triggered by correct passwords, incorrect passwords, and password resets. In a study of 273 participants, over 90% rated these alerts as important, yet they felt suspicious, nervous, and...

The Cost of EKS Auto + Capabilities vs Fairwinds Managed KaaS
Amazon’s EKS Auto Mode and EKS Capabilities automate the infrastructure layer of Kubernetes—node provisioning, scaling, networking and storage—while leaving architecture, add‑on lifecycle, and 24×7 incident response to the customer. Fairwinds Managed Kubernetes‑as‑a‑Service (KaaS) assumes those omitted responsibilities, delivering design, full...

The Next Security Battleground: Agentic Identity
Cyata is building a unified control plane to manage "agentic identity," the emerging security challenge of AI‑driven agents that act across SaaS, endpoints, and data stores. Unlike traditional employee accounts, these agents operate dynamically, creating "shadow agents" that evade existing...

NDSS 2025 – SKILLPoV: Towards Accessible And Effective Privacv Notice For Amazon Alexa Skills
Researchers at NDSS 2025 introduced SKILLPoV, a tool that automatically generates voice‑based privacy notices for Amazon Alexa skills. By analyzing skill code and leveraging ChatGPT, SKILLPoV creates concise notices delivered at skill launch, achieving 91.3% detection accuracy and 96.4% completeness....

Saying Goodbye to Windows Hello for Business: Five User Experience Pitfalls that Make Business Leaders Go for Best-in-Breed Solutions
The article highlights five user‑experience pitfalls of Windows Hello for Business that cause employees to abandon biometric authentication. Environmental variables—lighting, glasses, hats, facial hair, and device positioning—lead to frequent failures, prompting users to fall back on PINs or passwords. This...

Report: Massive Amounts of Sensitive Data Being Shared with GenAI Tools
A Harmonic Security report analyzing 22.4 million prompts across six generative AI tools reveals an exponential rise in sensitive data exposure, with 71% of incidents tied to ChatGPT. Approximately 579,000 prompts (2.6%) contained company‑sensitive information, especially code, legal discourse, and M&A...

Delinea Acquries StrongDM to Secure Access to IT Infrastructure
Delinea announced it will acquire StrongDM, a platform that provides just‑in‑time (JIT) access to IT infrastructure for both human operators and non‑human identities. The deal expands Delinea’s privileged access management suite to cover dynamic, AI‑driven workloads and supports a zero...

7 Reasons to Get Certified in API Security
Wallarm University now offers a free, hands‑on API security certification that lets participants run real attacks and practice defenses. The program is built by seasoned API security experts and covers emerging threats such as AI‑driven and agentic APIs. Recent Wallarm...

Classroom Device Management: 8 Strategies for K-12 Success
Classroom device management is essential for K‑12 schools integrating laptops, tablets, and BYOD. The article outlines eight practical strategies, including clear rules, mobile device management tools, app whitelisting, screen monitoring, scheduled access, BYOD integration, activity tracking, and continuous teacher development....

Arcjet Python SDK Sinks Teeth Into Application-Layer Security
Arcjet has released a Python SDK that brings its application‑layer security platform directly into Python services and APIs. The SDK provides built‑in bot protection, rate limiting, email validation and signup spam prevention, and works with both FastAPI and Flask with...

Modern Executive Protection: Digital Exposure & Physical Risk
Executive protection is expanding beyond physical guards to include digital exposure analysis. Executives and their households generate extensive online footprints that adversaries exploit to shape targeting before any physical action. The article argues that most security teams have abundant data...

How the OWASP Application Security Verification Standard Helps Improve Software Security
Centraleyes recently integrated the OWASP Application Security Verification Standard (ASVS) into its cyber‑risk platform, enabling structured, repeatable assessments for web and cloud services. ASVS defines three verification levels—opportunistic, standard, and advanced—allowing organizations to match security controls to application risk. The...

Microsoft, Law Enforcement Disrupt RedVDS Global Cybercrime Service
Microsoft and international law‑enforcement agencies, including Europol, dismantled RedVDS, a cybercrime‑as‑a‑service platform that has stolen roughly $40 million since March 2025. The operation seized the service’s marketplace, customer portal, and associated domains, cutting off access to cheap virtual dedicated servers rented for...

NDSS 2025 – PolicyPulse:Precision Semantic Role Extraction For Enhanced Privacy Policy Comprehension
Researchers from the University of Denver introduced PolicyPulse, an information‑extraction pipeline that converts natural‑language privacy policies into structured, machine‑readable formats. The system combines a specialized XLNet classifier with a BERT‑based semantic role labeler, processing sentences to preserve predicate‑argument relationships. Trained...

From Bot Noise to Real Insights: How Jobrapido Achieved True Marketing ROI
Jobrapido, a global recruitment‑marketing platform, partnered with DataDome to combat bot‑driven traffic that was inflating costs and skewing performance metrics. The AI‑powered solution filtered out roughly 15% of invalid visits, giving the company a clean, real‑time view of genuine user...

AppOmni Surfaces BodySnatcher AI Agent Security Flaw Affecting ServiceNow Apps
AppOmni, a SaaS security platform vendor, has disclosed a critical vulnerability in ServiceNow identified as CVE‑2025‑12420, nicknamed BodySnatcher. The flaw enables an unauthenticated attacker to impersonate any ServiceNow user and spawn a malicious AI agent within the platform. Because ServiceNow...

EasyDMARC Expands Executive Team with Armen Najarian as Chief Commercial Officer
EasyDMARC announced the appointment of Armen Najarian as its new Chief Commercial Officer. Najarian brings over 25 years of experience in email security, fraud prevention, and AI‑driven analytics, previously leading go‑to‑market roles at ThreatMetrix, Agari, Outseer and Sift. He will...

AI in Manufacturing: The Growing Risk and Reward Dilemma Escalating Data Security
AI adoption in U.S. manufacturing is accelerating, with 55% of firms already using generative AI and many planning further expansion. Meanwhile, ransomware attacks on the sector surged 87% in 2024, making manufacturing the most targeted industry. Without enterprise‑grade security—especially through...

AI Scraping in Mobile Apps: How It Works and How to Stop It
Scraping has migrated from web sites to mobile apps as AI‑driven bots target richer, structured API data. Attackers decompile Android APKs, extract endpoints and credentials, then replay authenticated requests without using the UI. Traditional defenses—rate limits, CAPTCHAs, and token‑based authentication—fail...

NDSS 2025 – A Comprehensive Memory Safety Analysis Of Bootloaders
Researchers at NDSS 2025 presented the first systematic memory‑safety study of bootloaders, revealing a growing attack surface as these low‑level programs add features. By surveying prior vulnerabilities and building a dedicated fuzzing framework, the team examined nine popular bootloaders and...

Identity Under Siege: What the Salt Typhoon Campaign Reveals About Trusted Access Risks
The Salt Typhoon espionage campaign compromised email accounts of U.S. congressional staff by exploiting stolen credentials rather than deploying malware. Attackers blended into normal email and cloud traffic, maintaining persistent, low‑noise access to sensitive communications. The breach underscores that identity systems...

GitGuardian Closes 2025 with Strong Enterprise Momentum, Protecting Millions of Developers Worldwide
GitGuardian reported record ARR growth in 2025, fueled by rapid enterprise adoption across North America and Europe. The platform now safeguards over 115,000 developers, monitors more than 610,000 repositories and 210,000 collaboration‑tool sources, a seven‑fold increase from the prior year....

When the Marketing Graph Becomes the Target Map
A Wired investigation uncovered that Google’s ad service hosted audience segments tied to highly sensitive groups, allowing marketers and potential adversaries to target mobile devices linked to government employees and executives. The article warns that modern ad‑tech pipelines collect granular...
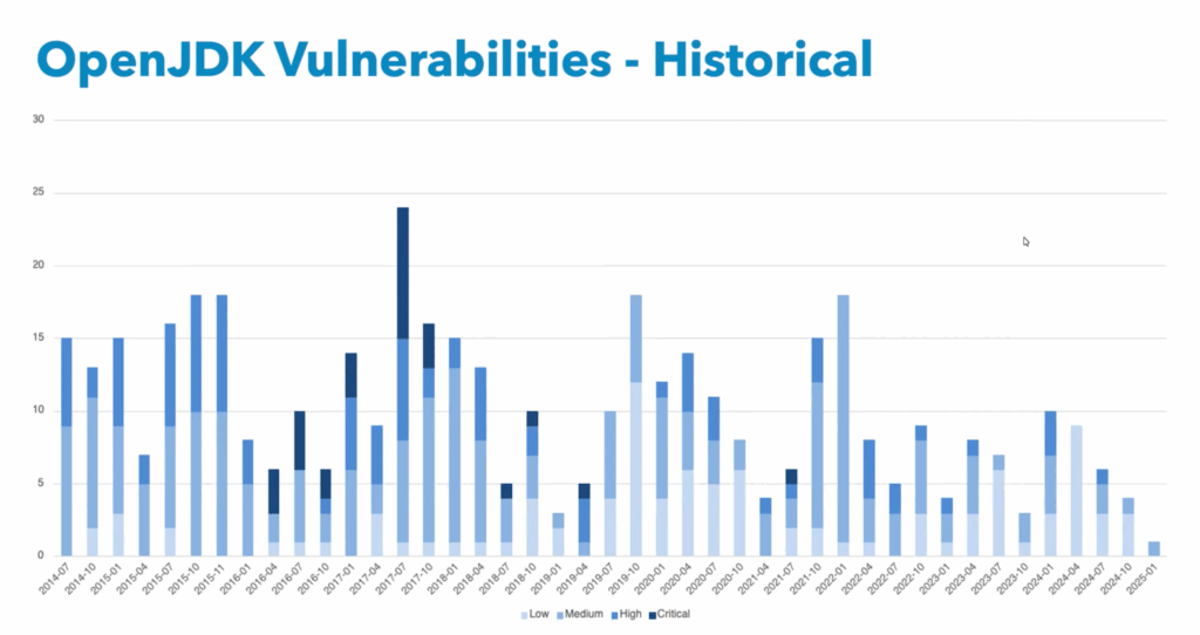
Can You Afford the Total Cost of Free Java?
Running Java on a free, unsupported JVM carries hidden risks as exploit timelines have accelerated dramatically. In 2023, attackers began leveraging newly disclosed Java flaws within five days, and some incidents occurred in under an hour. Without commercial support, organizations...

BodySnatcher (CVE-2025-12420): A Broken Authentication and Agentic Hijacking Vulnerability in ServiceNow
ServiceNow’s Virtual Agent API and Now Assist AI Agents contain a critical broken‑authentication flaw (CVE‑2025‑12420) that lets unauthenticated attackers impersonate any user using only an email address. The vulnerability exploits a static provider secret and email‑only auto‑linking to bypass MFA...

ColorTokens Achieves FedRAMP® Moderate ATO for Xshield™
ColorTokens announced that its Xshield Enterprise Microsegmentation Platform has received a FedRAMP® Moderate Authority to Operate, confirming compliance with hundreds of NIST SP 800‑53 controls. The authorization, validated by an accredited third‑party assessment organization, allows the solution to handle Controlled Unclassified Information...

CyRC Advisory: Vulnerability in Broadcom Chipset Causes Network Disruption and Client Disconnection on Wireless Routers
The Black Duck Cybersecurity Research Center identified a high‑severity vulnerability in Broadcom’s wireless chipset used in ASUS RT‑BE86U routers. A single over‑the‑air frame can render the 5 GHz Wi‑Fi network unresponsive, forcing a manual router reset and potentially corrupting ongoing data...

Key Learnings From the Latest CyRC Wi-Fi Vulnerabilities
Black Duck Cybersecurity Research Center (CyRC) disclosed high‑risk Wi‑Fi vulnerabilities in ASUS and TP‑Link routers that allow network disruption with a single malformed frame. The flaws were identified through Defensics fuzz testing and bypass WPA2/WPA3 encryption, highlighting protocol‑level weaknesses. Vendors...

Email Is Not Legacy. It’s Infrastructure.
Email remains the backbone of modern business, not a relic, because it operates as an open protocol that connects vendors, customers, and internal teams. A recent survey shows 82 % of IT leaders consider it the most important channel for external...

Russia’s Crackdown on Probiv Data Leaks May Have Fed the Beast Instead
Russia’s crackdown on the illegal probiv data‑leak market, spurred by a personal fraud incident involving President Putin’s associate, led to the arrest of Solaris platform founders but may have unintentionally strengthened the underground ecosystem. The probiv market, originally a convenient...

Apache Struts External Entity (XXE) Injection Vulnerability S2-069 (CVE-2025-68493)
Apache Struts has been disclosed with a critical external entity injection flaw, S2‑069 (CVE‑2025‑68493), scoring 9.8 on the CVSS scale. The vulnerability resides in the XWork XML parser, enabling attackers to read files, perform SSRF, or launch DoS attacks. Affected...

NDSS 2025 – LLMPirate: LLMs For Black-Box Hardware IP Piracy
Researchers from Texas A&M unveiled LLMPirate, a novel technique that leverages large language models to generate pirated variations of hardware circuit designs. The system successfully evaded detection by four state‑of‑the‑art IP piracy tools across all tested circuits, achieving 100% evasion....

NDSS 2025 – Mens Sana In Corpore Sano: Sound Firmware Corpora For Vulnerability Research
The NDSS 2025 paper "Mens Sana In Corpore Sano" examines the difficulty of building scientifically sound firmware corpora for vulnerability research. It identifies practical obstacles such as proprietary, encrypted samples and inadequate documentation that hinder replicability. The authors derive a...

Predict 2026: AI, Trust and the Security Reckoning Ahead
Predict 2026 declares AI the defining technology of the year, emphasizing that security leaders must now focus on protecting, governing, and trusting autonomous AI systems. The event highlights how agentic AI reshapes risk, from evolving models to data pipelines that become...
Unlock Remote Work’s GRC Impact: Challenges to Opportunities
Remote work has become a permanent fixture, forcing organizations to overhaul traditional governance, risk, and compliance (GRC) frameworks. Distributed workforces increase cyber‑risk exposure, fragment data environments, and create overlapping regulatory obligations across jurisdictions. Companies are turning to centralized GRC platforms,...

Turkish Security Researcher Gets Nod From NASA Over Vulnerability Discoveries
Turkish researcher Hasan İsmail Gülkaya identified four security flaws in NASA’s systems and reported them through the agency’s Vulnerability Disclosure Program. NASA promptly patched the issues and sent the researcher a formal thank‑you letter, highlighting the success of its responsible‑disclosure framework. Industry...

Operation Cronos Leader Gets Nod From King Charles
British law enforcement officer Gavin Webb received an OBE from King Charles for his leadership of Operation Cronos. The National Crime Agency‑led operation seized LockBit ransomware’s infrastructure, source code and decryption keys, crippling a gang that accounted for roughly 25%...

NDSS 2025 – EMIRIS: Eavesdropping On Iris Information Via Electromagnetic Side Channel
Researchers at Shandong University presented EMIRIS at NDSS 2025, demonstrating that electromagnetic emissions from near‑infrared iris sensors can be captured and used to reconstruct iris patterns. By reverse‑engineering the sensor’s data transmission format and applying a diffusion‑based inverse‑problem solver, the...

Most Popular Cybersecurity Blogs From 2025
Dan Lohrmann’s January 2026 roundup lists the ten most‑viewed cybersecurity blogs of 2025, featuring stories on state bans of human microchip implants, humanoid robots, AI‑driven human verification, federal employee resilience, government cloud security, AI career impacts, and nation‑state threat assessments. The data...

What Is Application Security Testing? Detail Explanation
Application security testing (AST) is a set of processes and tools that identify vulnerabilities throughout the software development lifecycle, enabling organizations to shift security left and remediate issues before deployment. The global AST market now exceeds $33 billion, reflecting the critical...

Top 10 Privileged Access Management Solutions for 2026
Privileged Access Management has shifted from a compliance checkbox to a critical security control as organizations adopt hybrid cloud, SaaS, DevOps pipelines, and AI agents. The 2026 guide evaluates ten leading PAM vendors, highlighting capabilities such as Zero Standing Privileges,...
Tonic.ai Product Updates: January 2026
Tonic.ai’s January 2026 release adds Guided Redaction in Textual, a beta human‑in‑the‑loop workflow that couples AI detection with manual review for high‑risk data. The platform also expands model‑based custom entity types, letting users train detectors for niche business vocabularies. A...