
Ghost Campaign Uses 7 Npm Packages to Steal Crypto Wallets and Credentials
Security researchers have identified a new "Ghost" campaign that distributes seven malicious npm packages under the author name mikilanjillo. The packages masquerade as popular React utilities and AI trading tools, prompting developers to enter their sudo password during a fabricated installation process. Once the password is captured, the malware contacts a Telegram channel to retrieve a downloader, which then deploys a remote‑access trojan capable of harvesting cryptocurrency wallets, browser credentials, SSH keys and cloud tokens. The operation extends to GitHub repositories and AI‑assisted workflows, broadening its attack surface.

⚡ Weekly Recap: CI/CD Backdoor, FBI Buys Location Data, WhatsApp Ditches Numbers & More
The open‑source Trivy vulnerability scanner was backdoored, injecting credential‑stealing malware that spread a self‑propagating worm through thousands of CI/CD pipelines. A coordinated DOJ operation dismantled four Mirai‑derived IoT botnets, removing control of more than three million compromised devices. Critical flaws...

We Found Eight Attack Vectors Inside AWS Bedrock. Here's What Attackers Can Do with Them
XM Cyber identified eight distinct attack vectors within Amazon Bedrock, the AI service that links foundation models to enterprise data. The vectors span log manipulation, knowledge‑base credential theft, agent hijacking, flow injection, guardrail degradation, and prompt poisoning, each triggered by over‑privileged...

Microsoft Warns IRS Phishing Hits 29,000 Users, Deploys RMM Malware
Microsoft’s threat intel team warned that a tax‑season phishing campaign compromised 29,000 users in 10,000 organizations, primarily in the United States. The attacks impersonated the IRS and used QR‑code, CPA, and cryptocurrency lures to deliver malicious links and attachments. Many...

CISA Flags Apple, Craft CMS, Laravel Bugs in KEV, Orders Patching by April 3, 2026
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added five high‑severity flaws affecting Apple WebKit, Apple kernel components, Craft CMS, and Laravel Livewire to its Known Exploited Vulnerabilities (KEV) catalog, mandating remediation by April 3 2026. The vulnerabilities carry CVSS scores from...

Trivy Security Scanner GitHub Actions Breached, 75 Tags Hijacked to Steal CI/CD Secrets
Trivy, a widely used open‑source vulnerability scanner, suffered a second supply‑chain breach when attackers force‑pushed 75 of 76 tags in the official aquasecurity/trivy‑action repository to deliver a malicious payload. The code runs inside GitHub Actions runners, harvesting environment variables, cloud...

The Importance of Behavioral Analytics in AI-Enabled Cyber Attacks
Artificial intelligence is empowering cybercriminals to craft hyper‑personalized phishing, automate credential abuse, and generate adaptive malware that mimics legitimate user behavior. Traditional rule‑based and signature‑based defenses struggle because AI‑driven attacks operate within normal activity thresholds and continuously evolve their code....

Critical Unpatched Telnetd Flaw (CVE-2026-32746) Enables Unauthenticated Root RCE
A critical vulnerability (CVE‑2026‑32746) in GNU InetUtils telnetd allows unauthenticated remote attackers to achieve root‑level code execution via a buffer overflow in the SLC sub‑option handler. The flaw affects all telnetd versions up to 2.7 and carries a CVSS score...

Why Security Validation Is Becoming Agentic
Traditional security validation relies on disconnected tools like BAS platforms, periodic penetration tests, and vulnerability scanners, creating blind spots as attackers chain identity, cloud, and vulnerability exploits. This fragmentation forces manual data stitching, delaying insight and remediation. Emerging agentic exposure...

DRILLAPP Backdoor Targets Ukraine, Abuses Microsoft Edge Debugging for Stealth Espionage
The DRILLAPP backdoor, discovered by security researchers, is actively targeting Ukrainian entities, including government agencies and critical infrastructure. It exploits Microsoft Edge's remote debugging interface to execute malicious JavaScript, achieving fileless persistence while evading traditional antivirus solutions. The malware establishes...

OpenClaw AI Agent Flaws Could Enable Prompt Injection and Data Exfiltration
China’s CNCERT has warned that OpenClaw, an open‑source autonomous AI agent, suffers from weak default security configurations that can be exploited for prompt‑injection attacks. Researchers demonstrated that indirect prompt injection via link previews can exfiltrate confidential data without user interaction....

Chinese Hackers Target Southeast Asian Militaries with AppleChris and MemFun Malware
Unit 42 has identified a China‑backed espionage campaign, designated CL‑STA‑1087, that has been infiltrating Southeast Asian military organizations since at least 2020. The operation deploys two custom backdoors, AppleChris and MemFun, alongside a credential‑harvesting tool called Getpass, using techniques such...

Authorities Disrupt SocksEscort Proxy Botnet Exploiting 369,000 IPs Across 163 Countries
International law‑enforcement agencies dismantled the SocksEscort proxy botnet, which compromised roughly 369,000 residential routers in 163 countries. The operation, dubbed Operation Lightning, seized 34 domains, 23 servers and froze $3.5 million in cryptocurrency. SocksEscort sold proxy access to criminals, enabling fraud...

Rust-Based VENON Malware Targets 33 Brazilian Banks with Credential-Stealing Overlays
Brazilian security firm ZenoX has uncovered VENON, a Rust‑based banking trojan that targets 33 banks and digital‑asset platforms. The malware uses DLL side‑loading, shortcut hijacking, and nine evasion techniques before delivering credential‑stealing overlays. Distribution relies on a PowerShell‑driven ZIP chain,...

Attackers Don't Just Send Phishing Emails. They Weaponize Your SOC's Workload
Attackers are weaponizing phishing campaigns to overload Security Operations Center (SOC) analysts, turning the investigation process into an informational denial‑of‑service (IDoS) attack. By flooding the SOC with thousands of low‑sophistication emails, they force analysts to triage quickly, allowing a few...

FortiGate Devices Exploited to Breach Networks and Steal Service Account Credentials
Threat actors are exploiting FortiGate next‑generation firewalls to gain initial access and harvest service‑account credentials. Researchers identified abuse of recent CVEs (2025‑59718, 2025‑59719, 2026‑24858) and misconfigurations to extract configuration files containing LDAP and AD service accounts, targeting healthcare, government and...

New "LeakyLooker" Flaws in Google Looker Studio Could Enable Cross-Tenant SQL Queries
Researchers at Tenable disclosed nine cross‑tenant vulnerabilities in Google Looker Studio, dubbed “LeakyLooker,” that could let attackers execute arbitrary SQL queries against BigQuery, Spanner, PostgreSQL, MySQL and other GCP data sources. The flaws, ranging from zero‑click SQL injection to data‑source...

Multi-Stage VOID#GEIST Malware Delivering XWorm, AsyncRAT, and Xeno RAT
Researchers have uncovered a multi‑stage malware campaign dubbed VOID#GEIST that uses obfuscated batch scripts, an embedded Python runtime, and Early Bird APC injection to deliver encrypted RAT payloads—XWorm, AsyncRAT and Xeno RAT. The chain is launched from a phishing email, displays...

The MSP Guide to Using AI-Powered Risk Management to Scale Cybersecurity
The guide explains how managed service providers (MSPs) can leverage AI‑powered risk management to transform fragmented cybersecurity services into a scalable, revenue‑generating model. It outlines the shift from isolated, compliance‑only offerings to a risk‑first approach that delivers continuous protection and...

Where Multi-Factor Authentication Stops and Credential Abuse Starts
Multi‑factor authentication (MFA) is effective for cloud and federated apps, but many Windows authentication paths—interactive logons, RDP, NTLM, Kerberos tickets, and service accounts—remain outside its protection. Attackers exploit these gaps using stolen passwords, pass‑the‑hash, or forged tickets, gaining lateral movement...

New RFP Template for AI Usage Control and AI Governance
Enterprises are finally allocating budgets for AI security, but many lack clear requirements. A new RFP template reframes AI protection as an interaction‑level problem rather than an app‑cataloging exercise, enabling tool‑agnostic control. It exposes the blind spots of legacy CASB/SSE...
Fake Laravel Packages on Packagist Deploy RAT on Windows, macOS, and Linux
Cybersecurity researchers discovered three malicious Laravel packages on Packagist—nhattuanbl/lara-helper, simple-queue, and lara-swagger—that install a cross‑platform remote access trojan (RAT) on Windows, macOS, and Linux. The RAT connects to a C2 server at helper.leuleu.net, gathers system data, and executes commands via...

Fake Tech Support Spam Deploys Customized Havoc C2 Across Organizations
Threat actors masquerading as IT support used a spam‑email and phone‑call campaign to deliver the Havoc command‑and‑control framework across five organizations. By tricking users into remote‑access sessions, they sideloaded malicious DLLs that deployed Havoc Demon payloads and legitimate RMM tools...
Microsoft Warns OAuth Redirect Abuse Delivers Malware to Government Targets
Microsoft warned that threat actors are exploiting OAuth redirect functionality to deliver malware to government and public‑sector targets. The attackers create malicious applications with rogue redirect URLs, send phishing emails containing crafted OAuth links, and use an invalid scope to...

⚡ Weekly Recap: SD-WAN 0-Day, Critical CVEs, Telegram Probe, Smart TV Proxy SDK and More
This week’s cyber‑threat landscape featured a critical Cisco SD‑WAN zero‑day (CVE‑2026‑20127) being actively exploited, highlighting the risk to network infrastructure. Anthropic accused three Chinese AI firms of large‑scale model‑distillation attacks, echoing similar concerns raised by OpenAI. Google disrupted the UNC2814...

How to Protect Your SaaS From Bot Attacks with SafeLine WAF
SaaS companies are increasingly targeted by sophisticated bots that inflate sign‑ups, scrape APIs, and overload infrastructure. SafeLine, a self‑hosted web application firewall, inspects every HTTP request using a semantic analysis engine that detects malicious intent with 99.45% accuracy. By deploying...

ScarCruft Uses Zoho WorkDrive and USB Malware to Breach Air-Gapped Networks
North Korean APT ScarCruft launched the Ruby Jumper campaign, employing a chain of malware that includes RESTLEAF, SNAKEDROPPER, THUMBSBD, VIRUSTASK, FOOTWINE and BLUELIGHT. The first‑stage payload uses a malicious LNK file to execute PowerShell, which carves and runs additional components....

Trojanized Gaming Tools Spread Java-Based RAT via Browser and Chat Platforms
Threat actors are distributing trojanized gaming utilities through browsers and chat platforms to install a Java‑based remote‑access trojan (RAT). The downloader stages a portable Java runtime, executes a malicious JAR via PowerShell and cmstp.exe, then deletes itself and configures Microsoft...

UAT-10027 Targets U.S. Education and Healthcare with Dohdoor Backdoor
Cisco Talos has identified a new threat cluster, UAT-10027, delivering a novel backdoor called Dohdoor that leverages DNS‑over‑HTTPS for command‑and‑control. The malware uses DLL side‑loading through legitimate Windows executables and drops a Cobalt Strike beacon that unhooks NTDLL calls to evade...

SLH Offers $500–$1,000 Per Call to Recruit Women for IT Help Desk Vishing Attacks
Scattered LAPSUS$ Hunters (SLH) is paying women $500 to $1,000 per call to conduct voice‑phishing attacks against IT help desks. The group supplies pre‑written scripts and leverages legitimate proxy services and tunneling tools to evade detection. These vishing campaigns aim...

Top 5 Ways Broken Triage Increases Business Risk Instead of Reducing It
The article outlines five common triage failures that inflate business risk, from decisions made without execution evidence to manual, error‑prone processes. It shows how interactive sandboxes—exemplified by ANY.RUN—provide rapid execution evidence, enabling analysts to reach evidence‑backed verdicts within seconds. Reported...
Manual Processes Are Putting National Security at Risk
More than half of national‑security agencies still move classified data by hand, a practice the CYBER360 report flags as a strategic liability. Manual transfers introduce human error, audit gaps, and exploitable seams that adversaries can weaponize. Legacy platforms, protracted procurement...

Identity Prioritization Isn't a Backlog Problem - It's a Risk Math Problem
Identity programs still rank remediation like IT tickets, ignoring context. The article argues that true prioritization must treat identity risk as a function of controls posture, hygiene, business impact, and user intent, not just checklist completion. When these factors align,...

APT28 Targeted European Entities Using Webhook-Based Macro Malware
Russia‑linked APT28 launched Operation MacroMaze, a campaign against Western and Central European entities from September 2025 through January 2026. The attackers delivered spear‑phishing documents containing a macro that calls a webhook.site URL, acting as a tracking‑pixel to verify document opening. The macro drops...

How Exposed Endpoints Increase Risk Across LLM Infrastructure
Enterprises deploying private Large Language Models are rapidly adding inference APIs, model‑management dashboards, and tool‑calling endpoints. Each new endpoint widens the attack surface, especially when permissions are excessive and credentials remain static. Exposed endpoints let attackers hijack non‑human identities, enabling...

MuddyWater Targets MENA Organizations with GhostFetch, CHAR, and HTTP_VIP
Iranian APT group MuddyWater has launched Operation Olalampo, targeting organizations across the Middle East and North Africa. The campaign, first seen on Jan 26, 2026, deploys new malware families—GhostFetch, HTTP_VIP, the Rust backdoor CHAR, and the GhostBackDoor implant—delivered via macro‑laden Office...

EC-Council Expands AI Certification Portfolio to Strengthen U.S. AI Workforce Readiness and Security
EC‑Council announced its Enterprise AI Credential Suite, adding four role‑based AI certifications and an updated Certified CISO v4 program. The launch targets the estimated $5.5 trillion global AI risk exposure and a U.S. reskilling gap of 700,000 workers. It aligns with recent...

Identity Cyber Scores: The New Metric Shaping Cyber Insurance in 2026
Identity cyber scores are emerging as the primary metric insurers use to underwrite cyber‑insurance policies in 2026. Insurers now scrutinize password hygiene, privileged‑access management and MFA coverage, linking weak identity controls to higher breach likelihood and premium costs. The global...

Former Google Engineers Indicted Over Trade Secret Transfers to Iran
Two former Google engineers and a spouse were indicted for allegedly stealing trade secrets related to Google’s Tensor processor and other hardware designs, then transferring the data to Iran. The defendants used personal devices, messaging channels, and manual photographs to...

INTERPOL Operation Red Card 2.0 Arrests 651 in African Cybercrime Crackdown
INTERPOL’s Operation Red Card 2.0, conducted from Dec 8 2025 to Jan 30 2026, resulted in 651 arrests across 16 African nations and the seizure of more than $4.3 million. The eight‑week crackdown exposed scams responsible for roughly $45 million in losses and identified 1,247 victims worldwide....

3 Ways to Start Your Intelligent Workflow Program
Security, IT and engineering teams face pressure to accelerate outcomes while extracting AI value, yet 88% of AI proofs‑of‑concept never reach production despite 70% of workers seeking time‑saving automation. The Hacker News article outlines three pre‑built intelligent‑workflow use cases—automated phishing response,...

SmartLoader Attack Uses Trojanized Oura MCP Server to Deploy StealC Infostealer
Researchers have uncovered a new SmartLoader campaign that distributes a trojanized Oura Health Model Context Protocol (MCP) server to install the StealC infostealer. The malicious server is hosted in fabricated GitHub repositories and submitted to the MCP Market registry, exploiting...
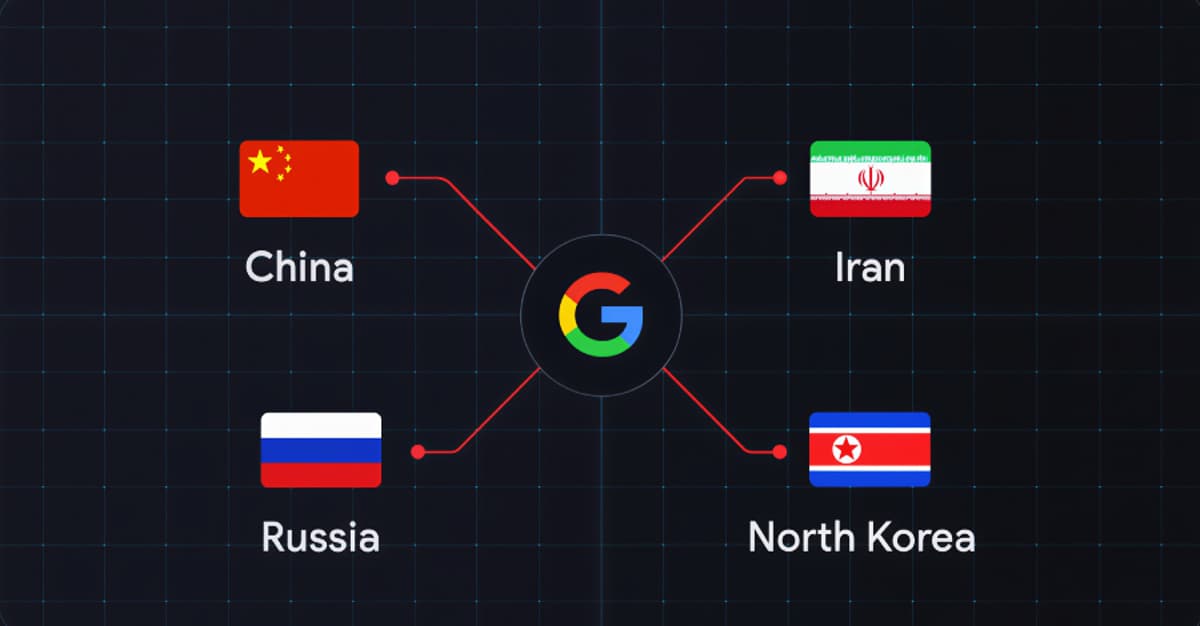
Google Links China, Iran, Russia, North Korea to Coordinated Defense Sector Cyber Operations
Google Threat Intelligence Group disclosed a coordinated campaign by state‑sponsored actors from China, Iran, Russia and North Korea targeting the defense industrial base. The operations concentrate on battlefield technologies used in the Russia‑Ukraine war, recruitment‑process infiltration, edge‑device entry points, and...

Malicious Chrome Extensions Caught Stealing Business Data, Emails, and Browsing History
Researchers uncovered a wave of malicious Chrome extensions that siphon data from corporate tools, social platforms, AI assistants, and general browsing activity. The CL Suite add‑on steals Meta Business Suite credentials and analytics, while VK‑styled extensions hijacked roughly 500,000 VKontakte...

Npm’s Update to Harden Their Supply Chain, and Points to Consider
npm completed a major authentication overhaul in December 2025, revoking classic long‑lived tokens and moving to short‑lived session tokens with MFA default for publishing. The changes also promote OIDC Trusted Publishing, giving CI systems per‑run credentials. However, MFA phishing attacks...

Exposed Training Open the Door for Crypto-Mining in Fortune 500 Cloud Environments
Pentera Labs identified nearly 2,000 publicly exposed training applications across cloud platforms, with about 60% hosted on AWS, Azure or GCP. Roughly one‑fifth of these instances contained crypto‑mining scripts, web‑shells or persistence tools, indicating active exploitation. The vulnerable apps were...
ZAST.AI Raises $6M Pre-A to Scale "Zero False Positive" AI-Powered Code Security
ZAST.AI announced a $6 million Pre‑Series A round led by Hillhouse Capital, bringing total funding near $10 million. The Seattle‑based startup claims its AI‑driven platform delivers “zero false‑positive” code security by automatically generating and validating proof‑of‑concept exploits. In 2025 the company uncovered...

How Samsung Knox Helps Stop Your Network Security Breach
Samsung Knox introduces a per‑app firewall and Zero‑Trust Network Access (ZTNA) that extend traditional enterprise security to mobile devices. The firewall provides granular, app‑specific rules and detailed logging, shrinking investigation times from days to hours. Knox ZTNA works alongside existing...

Compromised dYdX Npm and PyPI Packages Deliver Wallet Stealers and RAT Malware
Security researchers uncovered a supply‑chain attack on dYdX's official npm package @dydxprotocol/v4-client-js and its PyPI counterpart dydx‑v4‑client. The compromised versions, published with legitimate maintainer credentials, embed wallet‑stealing code and, in the Python case, a remote‑access trojan. dYdX acknowledged the breach,...

AISURU/Kimwolf Botnet Launches Record-Setting 31.4 Tbps DDoS Attack
The AISURU/Kimwolf botnet launched a record‑setting DDoS attack in November 2025, peaking at 31.4 Tbps and lasting just 35 seconds. Cloudflare, which automatically mitigated the traffic, said the attack is part of a surge in hyper‑volumetric HTTP assaults, with average sizes...