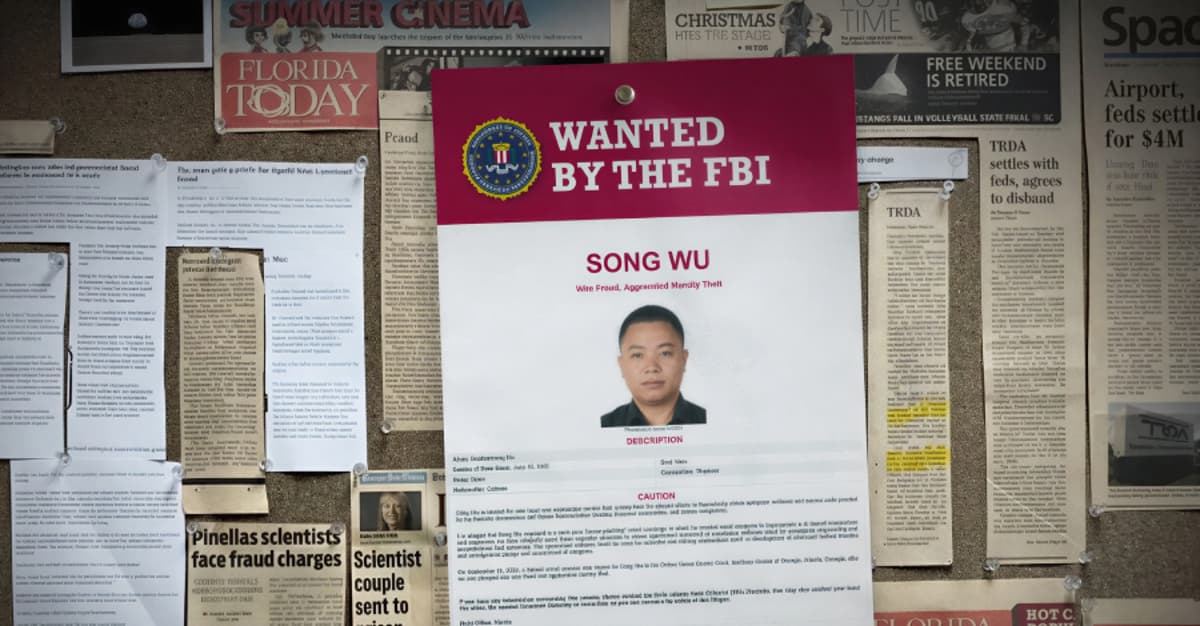
NASA Employees Duped in Chinese Phishing Scheme Targeting U.S. Defense Software
The U.S. Office of Inspector General disclosed that a Chinese national, Song Wu, impersonated American researchers to obtain NASA and defense‑related aerospace software through a multi‑year spear‑phishing campaign. The scheme targeted employees at NASA, the military services, universities and private firms, leading some to unknowingly share export‑controlled code. Wu faces wire‑fraud and aggravated identity‑theft charges, with potential sentences of up to 20 years per count, and has been placed on the FBI’s Most Wanted list. The case highlights vulnerabilities in data‑sharing practices across government and industry.

Bridging the AI Agent Authority Gap: Continuous Observability as the Decision Engine
Enterprises face an AI Agent Authority Gap because agents inherit authority from existing human, bot and service‑account identities. The core problem is not the agents themselves but the ungoverned delegation chain, often hidden as "identity dark matter" across applications and...
26 FakeWallet Apps Found on Apple App Store Targeting Crypto Seed Phrases
Cybersecurity firm Kaspersky uncovered 26 malicious iOS apps on Apple’s App Store that impersonate popular cryptocurrency wallets, primarily targeting users with Chinese‑region Apple accounts. The apps use typosquatted names and identical icons to trick users into installing them, then hijack...

Tropic Trooper Uses Trojanized SumatraPDF and GitHub to Deploy AdaptixC2
Zscaler ThreatLabz uncovered a new campaign attributed to the APT group Tropic Trooper that weaponizes a trojanized version of the SumatraPDF reader to drop the AdaptixC2 post‑exploitation beacon. The malware fetches encrypted shellcode, uses GitHub as a command‑and‑control hub, and later...

LMDeploy CVE-2026-33626 Flaw Exploited Within 13 Hours of Disclosure
A critical SSRF flaw (CVE‑2026‑33626) in LMDeploy’s vision‑language module was exploited within 13 hours of its public disclosure. The vulnerability, affecting all versions up to 0.12.0, let attackers reach cloud metadata services, internal databases and perform internal port scans. Sysdig’s...
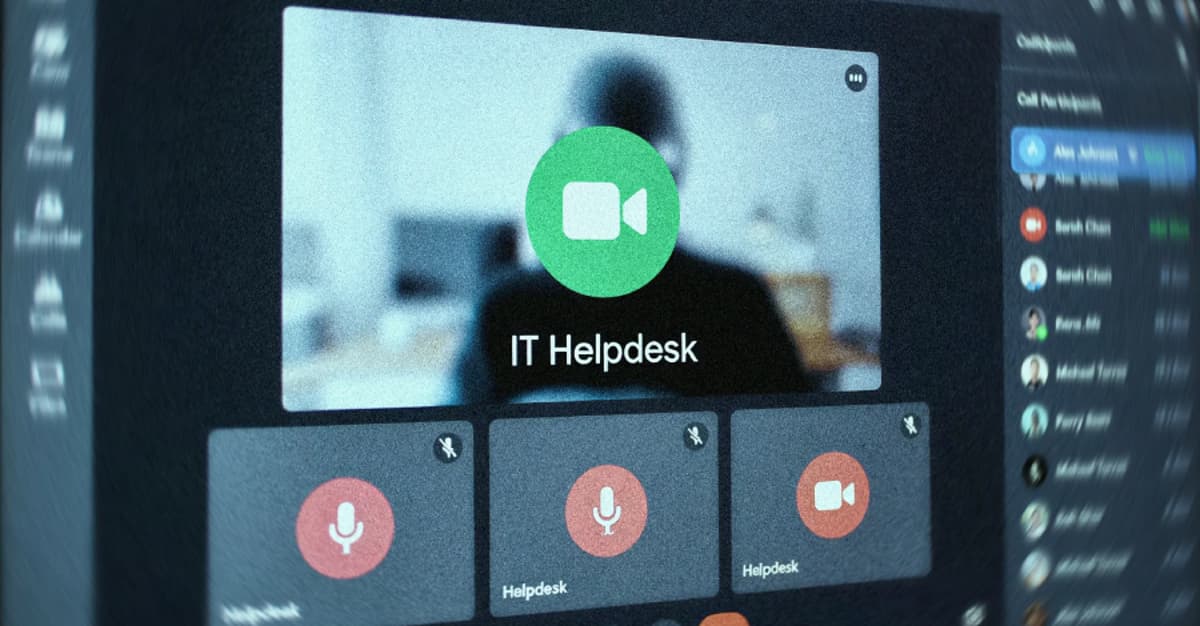
UNC6692 Impersonates IT Helpdesk via Microsoft Teams to Deploy SNOW Malware
UNC6692 is a newly identified threat group that hijacks Microsoft Teams to impersonate IT help‑desk staff and convince victims to install remote‑support tools. The actors deliver a custom SNOW malware suite—including the SNOWBELT browser extension, SNOWGLAZE tunnel, and SNOWBASIN backdoor—after...

Project Glasswing Proved AI Can Find the Bugs. Who's Going to Fix Them?
Anthropic’s Project Glasswing, built on the Mythos model, can autonomously discover and chain software vulnerabilities, achieving a 72.4% success rate in Firefox’s JavaScript shell and uncovering bugs that survived decades of human review. The AI identified exploits across all major...

Malicious KICS Docker Images and VS Code Extensions Hit Checkmarx Supply Chain
Cybersecurity firm Socket disclosed that threat actors compromised the official Checkmarx KICS Docker Hub repository, overwriting tags such as v2.1.20 and alpine and adding a rogue v2.1.21 image. The malicious KICS binary harvests infrastructure‑as‑code scans, encrypts the data and exfiltrates it...
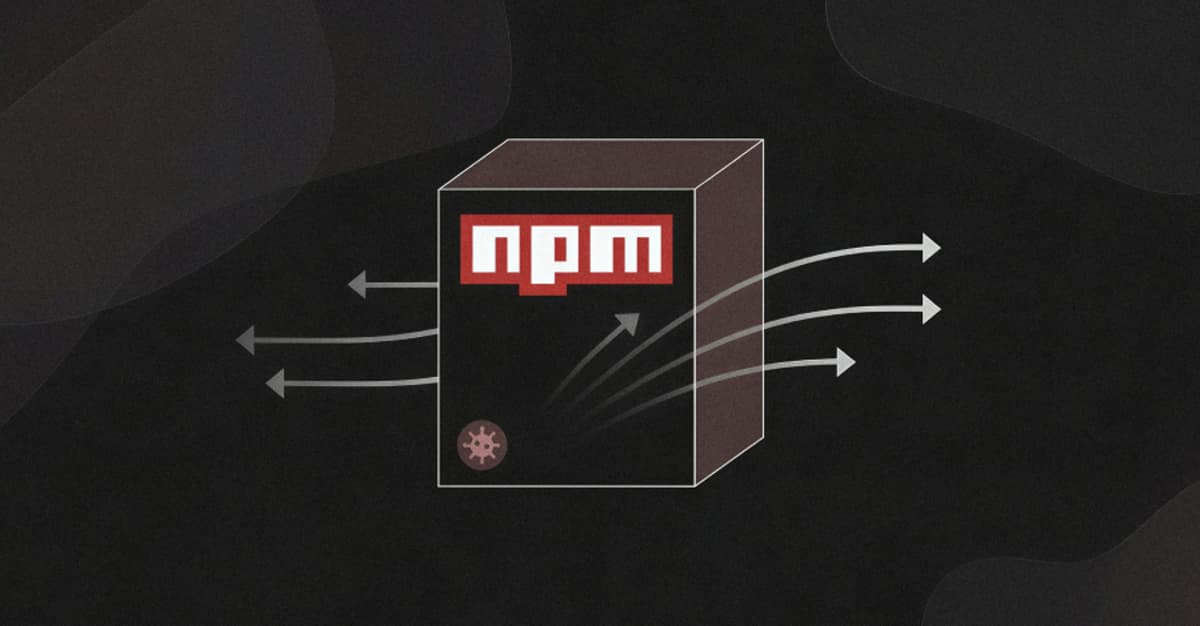
Self-Propagating Supply Chain Worm Hijacks Npm Packages to Steal Developer Tokens
Security researchers have uncovered a self‑propagating supply‑chain worm, dubbed CanisterSprawl, that compromises npm packages and injects malicious post‑install scripts to harvest developer credentials. The worm steals a wide range of secrets—including .npmrc files, SSH keys, cloud provider tokens, Docker and...
Toxic Combinations: When Cross-App Permissions Stack Into Risk
On Jan. 31 2026 researchers revealed that Moltbook, an AI‑agent social network, left its database exposed, leaking 35,000 email addresses and 1.5 million agent API tokens. Private messages also contained plaintext third‑party credentials, including OpenAI API keys stored alongside the tokens. The breach...

SGLang CVE-2026-5760 (CVSS 9.8) Enables RCE via Malicious GGUF Model Files
SGLang, a popular open‑source framework for serving large language models, has been found vulnerable to CVE‑2026‑5760, a critical 9.8‑score remote code execution flaw. The issue resides in the `/v1/rerank` endpoint, where unsandboxed Jinja2 rendering of a malicious GGUF model’s `tokenizer.chat_template`...
Why Most AI Deployments Stall After the Demo
Most AI projects dazzle during demos but stall when moved into production because real‑world data is messy, latency surfaces, and integration challenges emerge. Clean demo environments hide issues like noisy inputs, fragmented systems, and edge‑case failures that undermine performance at...

Google Blocks 8.3B Policy-Violating Ads in 2025, Launches Android 17 Privacy Overhaul
Google announced that in 2025 it blocked or removed 8.3 billion policy‑violating ads and suspended 24.9 million accounts worldwide. At the same time it rolled out Android 17, which replaces the broad READ_CONTACTS permission with a granular Contact Picker and adds a one‑time...

Newly Discovered PowMix Botnet Hits Czech Workers Using Randomized C2 Traffic
Researchers at Cisco Talos have uncovered a new botnet, PowMix, actively targeting Czech workers since at least December 2025. The malware is delivered through phishing emails that contain a malicious ZIP file, which drops a Windows shortcut that launches a...

ThreatsDay Bulletin: Defender 0-Day, SonicWall Brute-Force, 17-Year-Old Excel RCE and 15 More Stories
The ThreatsDay bulletin highlights a wave of cyber incidents, from a North Korean‑linked breach at Zerion that stole $100 K from internal hot wallets to a newly disclosed Microsoft Defender privilege‑escalation zero‑day called RedSun. Legacy flaws remain dangerous, with CISA adding...

Hidden Passenger? How Taboola Routes Logged-In Banking Sessions to Temu
Reflectiz discovered that a Taboola tracking pixel approved in a bank’s CSP silently redirected logged‑in users to a Temu endpoint via a 302 response. The redirect included an Access‑Control‑Allow‑Credentials header, causing browsers to send authentication cookies to Temu and link...

Obsidian Plugin Abuse Delivers PHANTOMPULSE RAT in Targeted Finance, Crypto Attacks
Researchers at Elastic Security Labs identified a novel social‑engineering campaign that abuses Obsidian’s community plugins to deliver the previously unknown PHANTOMPULSE remote‑access trojan. Threat actors pose as venture‑capital contacts on LinkedIn and Telegram, coaxing finance and cryptocurrency professionals to enable...

Actively Exploited Nginx-Ui Flaw (CVE-2026-33032) Enables Full Nginx Server Takeover
A critical authentication‑bypass flaw (CVE‑2026‑33032, CVSS 9.8) in the open‑source nginx‑ui management console is being actively exploited, allowing attackers to seize full control of Nginx services. The vulnerability stems from two MCP endpoints that default to an empty IP whitelist, effectively...

April Patch Tuesday Fixes Critical Flaws Across SAP, Adobe, Microsoft, Fortinet, and More
April’s Patch Tuesday delivered a wave of critical fixes across major vendors, highlighted by a CVSS 9.9 SQL‑injection flaw in SAP Business Planning and Consolidation that lets low‑privileged users execute arbitrary database commands. Adobe Acrobat Reader faced a remote‑code‑execution vulnerability (CVSS 8.6)...

AI-Driven Pushpaganda Scam Exploits Google Discover to Spread Scareware and Ad Fraud
Cybersecurity firm HUMAN uncovered a new ad‑fraud operation dubbed Pushpaganda that weaponizes AI‑generated news articles to infiltrate Google Discover. The scheme tricks Android and Chrome users into enabling push notifications that deliver scareware and financial scams, driving traffic to malicious...

108 Malicious Chrome Extensions Steal Google and Telegram Data, Affecting 20,000 Users
Security researchers have uncovered a coordinated campaign involving 108 malicious Chrome extensions that share a common command‑and‑control server. The extensions, published under five publisher names, have collectively been installed about 20,000 times and harvest Google OAuth credentials, Telegram Web session...

Your MTTD Looks Great. Your Post-Alert Gap Doesn't
The security industry has narrowed mean‑time‑to‑detect (MTTD) but still suffers a lengthy post‑alert gap, where analysts spend 20‑40 minutes investigating alerts. Recent AI‑driven exploits, such as Anthropic’s Mythos model, demonstrate that attackers can move in seconds, making human‑speed investigations untenable....

Citizen Lab: Law Enforcement Used Webloc to Track 500 Million Devices via Ad Data
Citizen Lab uncovered that law‑enforcement agencies worldwide are deploying Webloc, an advertising‑based geolocation platform originally built by Israeli firm Cobwebs Technologies and now sold by its successor Penlink. The system harvests identifiers, location coordinates and profile data from up to...

GlassWorm Campaign Uses Zig Dropper to Infect Multiple Developer IDEs
Researchers have uncovered a new GlassWorm variant that hides a Zig‑compiled native binary inside a counterfeit WakaTime VS Code extension. The binary acts as a dropper, locating every IDE that supports VS Code extensions and silently installing a malicious VSIX package. The...

Browser Extensions Are the New AI Consumption Channel That No One Is Talking About
LayerX’s new report reveals that AI-powered browser extensions are an overlooked yet high‑risk attack vector for enterprises. While 99% of corporate users run at least one extension, AI extensions are 60% more likely to contain vulnerabilities, have three times more...

ThreatsDay Bulletin: Hybrid P2P Botnet, 13-Year-Old Apache RCE and 18 More Stories
ThreatsDay bulletin highlights a surge in the hybrid P2P botnet Phorpiex, a 13‑year‑old Apache ActiveMQ RCE chain, record cyber‑fraud losses, AI‑driven DDoS evolution, and multiple supply‑chain and malware incidents. Phorpiex now infects roughly 125,000 devices daily, using peer‑to‑peer communication to...

The Hidden Security Risks of Shadow AI in Enterprises
The article warns that shadow AI—unauthorized artificial‑intelligence tools adopted by employees—creates hidden security gaps in enterprises. A 2024 Salesforce survey shows 55% of workers use AI solutions outside IT approval, exposing data to external platforms. These tools can leak credentials,...

New Chaos Variant Targets Misconfigured Cloud Deployments, Adds SOCKS Proxy
Researchers have identified a new Chaos malware variant that now targets misconfigured cloud deployments, such as a deliberately vulnerable Hadoop instance. The updated 64‑bit ELF binary drops a SOCKS proxy feature while removing its previous SSH‑based spreading mechanisms. The attack...

APT28 Deploys PRISMEX Malware in Campaign Targeting Ukraine and NATO Allies
Russian state‑linked group APT28 has launched a spear‑phishing campaign that deploys a new malware suite called PRISMEX. The operation, active since September 2025, exploits freshly disclosed zero‑days CVE‑2026‑21509 and CVE‑2026‑21513 to infiltrate Ukrainian government agencies, logistics firms and NATO‑affiliated entities. PRISMEX...

N. Korean Hackers Spread 1,700 Malicious Packages Across Npm, PyPI, Go, Rust
North Korean‑linked threat group UNC1069, operating under the Contagious Interview campaign, has published more than 1,700 malicious packages across major open‑source ecosystems including npm, PyPI, Go, Rust and Packagist. The packages act as stealthy loaders that fetch second‑stage payloads with...

Iran-Linked Hackers Disrupt U.S. Critical Infrastructure by Targeting Internet-Exposed PLCs
Iran‑affiliated cyber actors are targeting internet‑exposed programmable logic controllers (PLCs) across U.S. critical‑infrastructure sectors, including water, energy, and government facilities. The attackers use Dropbear SSH to gain remote access, manipulate HMI/SCADA displays, and disrupt device functionality, focusing on Rockwell Automation...

Over 1,000 Exposed ComfyUI Instances Targeted in Cryptomining Botnet Campaign
Security researchers have identified a campaign that scans cloud IP ranges for exposed ComfyUI instances—a popular Stable Diffusion UI—and hijacks them for cryptocurrency mining and proxy botnet operations. The Python‑based scanner exploits a misconfiguration in custom nodes to achieve unauthenticated...

The Hidden Cost of Recurring Credential Incidents
Recurring credential incidents impose hidden operational costs beyond headline breach expenses. IBM reports the average breach cost $4.4 million, yet everyday password resets represent up to 30 % of help‑desk tickets, each costing roughly $70. Weak policies and forced periodic changes drive...

Iran-Linked Password-Spraying Campaign Targets 300+ Israeli Microsoft 365 Organizations
Iranian‑linked threat actors launched a password‑spraying campaign against more than 300 Israeli Microsoft 365 organizations, exploiting common weak credentials. The operation, attributed to an APT group with ties to Tehran, was uncovered by security researchers who observed repeated login attempts...

Qilin and Warlock Ransomware Use Vulnerable Drivers to Disable 300+ EDR Tools
Cisco Talos and Trend Micro report that Qilin and Warlock ransomware groups are employing a bring‑your‑own‑vulnerable‑driver (BYOVD) strategy to neutralize endpoint detection and response (EDR) solutions. Qilin’s malware drops a malicious msimg32.dll that side‑loads two drivers—rwdrv.sys and hlpdrv.sys—to terminate more than...

Microsoft Details Cookie-Controlled PHP Web Shells Persisting via Cron on Linux Servers
Microsoft’s Defender Security Research team has uncovered a new web‑shell tradecraft that leverages HTTP cookies as a covert control channel for PHP loaders on Linux servers. The shells remain dormant until a specific cookie value is presented, then execute malicious...

Why Third-Party Risk Is the Biggest Gap in Your Clients' Security Posture
Third‑party risk has become the largest security gap for many organizations, accounting for 30% of data‑breach incidents and an average remediation cost of $4.91 million. The modern perimeter now extends across SaaS applications, vendor APIs, and subcontractors, prompting regulators such as...

Hackers Exploit CVE-2025-55182 to Breach 766 Next.js Hosts, Steal Credentials
Hackers are exploiting the critical CVE‑2025‑55182 flaw in Next.js to gain remote code execution and compromise at least 766 hosts across several cloud providers. The UAT‑10608 threat cluster deploys a multi‑phase dropper that harvests SSH keys, cloud IAM tokens, API...

Block the Prompt, Not the Work: The End of "Doctor No"
Enterprise security teams are abandoning blunt URL blocks in favor of session‑level governance. Legacy endpoint agents and SSL inspection create performance penalties that push users toward shadow AI tools and unmanaged extensions. The resulting "workaround economy" leaves critical data flowing...

Casbaneiro Phishing Targets Latin America and Europe Using Dynamic PDF Lures
Brazilian cyber‑crime group Augmented Marauder, also known as Water Saci, is running a multi‑vector phishing campaign against Spanish‑speaking organizations in Latin America and Europe. The campaign delivers the Casbaneiro banking trojan and the Horabot spreader via password‑protected PDF attachments that are...

TrueConf Zero-Day Exploited in Attacks on Southeast Asian Government Networks
A high‑severity zero‑day (CVE‑2026‑3502) in TrueConf’s video‑conferencing client was exploited in the wild, allowing attackers to replace legitimate updates with malicious code. The flaw, rated 7.8 CVSS, enables arbitrary code execution via DLL side‑loading and was used in the TrueChaos...

DeepLoad Malware Uses ClickFix and WMI Persistence to Steal Browser Credentials
Researchers at ReliaQuest uncovered DeepLoad, a new malware loader delivered through a ClickFix social‑engineering lure that tricks users into running obfuscated PowerShell commands. The loader employs AI‑generated code obfuscation, APC injection, and dynamic C# compilation to avoid static and behavioral...

⚡ Weekly Recap: Telecom Sleeper Cells, LLM Jailbreaks, Apple Forces U.K. Age Checks and More
The week’s cyber‑threat landscape was dominated by a critical Citrix NetScaler flaw (CVE‑2026‑3055) that is now being actively exploited, a confirmed breach of FBI Director Kash Patel’s personal email with a $10 million bounty offered, and the emergence of Red Menshen’s BPFDoor...

3 SOC Process Fixes That Unlock Tier 1 Productivity
The article outlines three SOC process fixes that boost Tier 1 productivity: a unified cross‑platform investigation workflow, a behavior‑first triage model powered by automation and interactivity, and standardized escalation with response‑ready evidence. Leveraging ANY.RUN’s sandbox, analysts can analyze Windows, macOS, Linux...

Iran-Linked Hackers Breach FBI Director’s Personal Email, Hit Stryker With Wiper Attack
Iran‑linked threat actors operating under the Handala Hack persona breached the personal email of FBI Director Kash Patel, leaking historical messages from 2010 and 2019. The same group claimed a destructive wiper attack on medical‑device giant Stryker, wiping thousands of...

We Are At War
The article warns that rising geopolitical tensions are now mirrored in a surge of state‑sponsored cyber operations targeting Europe’s critical infrastructure, from energy and telecom to defense networks. Hacktivist groups, once fringe protestors, have evolved into actors capable of cyber‑physical...
![[Webinar] Stop Guessing. Learn to Validate Your Defenses Against Real Attacks](/cdn-cgi/image/width=1200,quality=75,format=auto,fit=cover/https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEgCypzkb6uvHuNx6LKknUqtvQFoqsr6aalztDeBKT1aaUASzfjZMZAZqExx1k0w5iKWl08lx3MxbM_FwWxAvBdZODEerioaMp8OHVvhSjC8VL3uAW9_NMniMl_niggBVhVMdDFu2324YyhW5TrK4fua1PXlrb0DweOULvNgi5mlQUZUct_dIX3OePrfqks/s1700-e365/validate.jpg)
[Webinar] Stop Guessing. Learn to Validate Your Defenses Against Real Attacks
The upcoming cybersecurity webinar teaches organizations how to move beyond guesswork by validating defenses against real‑world attack paths, including those targeting autonomous AI agents. It emphasizes CTI‑driven, automated testing that integrates with existing pipelines, delivering continuous, accurate posture assessments. Attendees...

Claude Extension Flaw Enabled Zero-Click XSS Prompt Injection via Any Website
Security researchers uncovered a zero‑click XSS flaw in Anthropic’s Claude Chrome extension that let any website inject prompts into the AI assistant without user interaction. The vulnerability, dubbed ShadowPrompt, combined an overly permissive *.claude.ai origin allow‑list with an XSS bug...

Masters of Imitation: How Hackers and Art Forgers Perfect the Art of Deception
The article draws a parallel between 1960s art forger Elmyr de Hory and today’s cyber‑attackers, showing how both rely on convincing imitation to slip past experts. It highlights that 81% of modern attacks are malware‑free, using legitimate tools and AI‑generated identities...

The Hidden Cost of Cybersecurity Specialization: Losing Foundational Skills
Cybersecurity teams are increasingly specialized, but this focus erodes the foundational understanding needed to see the full risk picture. The loss of context leads to misaligned tool choices, fragmented risk communication, and slower incident response. Bryan Simon argues that without...