Microsoft Takes Down Malware-Signing Service Behind Ransomware Attacks
Microsoft’s Digital Crimes Unit announced the takedown of the Fox Tempest malware‑signing‑as‑a‑service (MSaaS) operation, which abused the company’s Artifact Signing platform to issue short‑lived, fraudulent code‑signing certificates. The service, priced between $5,000 and $9,000, enabled ransomware families such as Rhysida, Oyster, and Lumma Stealer to appear as legitimate software like Microsoft Teams and AnyDesk. In the operation dubbed OpFauxSign, Microsoft seized the attacker’s website, offline hundreds of virtual machines, and revoked illicit certificates. The disruption cuts off a critical supply‑chain foothold used by ransomware groups targeting healthcare, finance, and government sectors worldwide.
Typosquatting Is No Longer a User Problem. It's a Supply Chain Problem
Typosquatting has evolved from mistyped URLs into a supply‑chain threat, with AI‑generated look‑alike domains embedded in trusted third‑party scripts. Malicious npm and PyPI uploads surged 156 % YoY, enabling campaigns to launch in under ten minutes. The December 2025 Trust Wallet Chrome‑extension breach,...

Trapdoor Android Ad Fraud Scheme Hit 659 Million Daily Bid Requests Using 455 Apps
Researchers at HUMAN’s Satori team uncovered a sophisticated Android ad‑fraud operation named Trapdoor, leveraging 455 malicious utility‑style apps and 183 C2 domains. At its peak the scheme generated 659 million ad‑bid requests per day and prompted more than 24 million app installs,...

How to Reduce Phishing Exposure Before It Turns Into Business Disruption
Phishing attacks now bypass traditional filters, exposing credentials, SaaS apps, and cloud platforms before security teams can react. Early detection using interactive sandboxes uncovers the full attack chain in seconds, providing concrete evidence for rapid response. Enriching sandbox findings with...
Four Malicious Npm Packages Deliver Infostealers and Phantom Bot DDoS Malware
Researchers identified four npm packages—chalk‑tempalte, @deadcode09284814/axios‑util, axois‑utils, and color‑style‑utils—containing malicious code that either steals credentials or deploys a Golang‑based Phantom Bot DDoS malware. One package clones the open‑source Shai‑Hulud worm, while another delivers a distributed denial‑of‑service bot capable of HTTP,...
NGINX CVE-2026-42945 Exploited in the Wild, Causing Worker Crashes and Possible RCE
A heap‑buffer overflow in NGINX’s rewrite module (CVE‑2026‑42945) has been actively exploited just days after disclosure, allowing unauthenticated attackers to crash worker processes and, on systems with ASLR disabled, execute remote code. The flaw spans NGINX versions 0.6.27 through 1.30.0...

Four OpenClaw Flaws Enable Data Theft, Privilege Escalation, and Persistence
Cybersecurity firm Cyera disclosed four linked vulnerabilities in the OpenClaw agent platform, dubbed the Claw Chain, that enable sandbox escape, credential theft, privilege escalation, and persistent backdoors. The flaws—CVE‑2026‑44112, ‑44113, ‑44115, and ‑44118—combine TOCTOU race conditions, heredoc injection, and a spoofable...

What 45 Days of Watching Your Own Tools Will Tell You About Your Real Attack Surface
Bitdefender reports that 84% of 700,000 high‑severity incidents involve abuse of trusted Windows utilities, underscoring the living‑off‑the‑land (LOLBin) threat. To counter this, the firm offers a complimentary 45‑day Internal Attack Surface Assessment for organizations with 250+ employees, leveraging GravityZone PHASR to...
TanStack Supply Chain Attack Hits Two OpenAI Employee Devices, Forces macOS Updates
OpenAI disclosed that two employee devices were compromised in a supply‑chain attack targeting the TanStack library, part of the Mini Shai‑Hulud campaign. The breach resulted in limited credential exfiltration from internal source‑code repositories, but no intellectual property or production systems...

On-Prem Microsoft Exchange Server CVE-2026-42897 Exploited via Crafted Email
Microsoft disclosed CVE‑2026‑42897, an 8.1‑rated cross‑site scripting flaw in on‑premise Exchange Server that is already being exploited via crafted emails. The vulnerability allows arbitrary JavaScript to run in Outlook Web Access when a malicious message is opened. Microsoft’s temporary countermeasure...
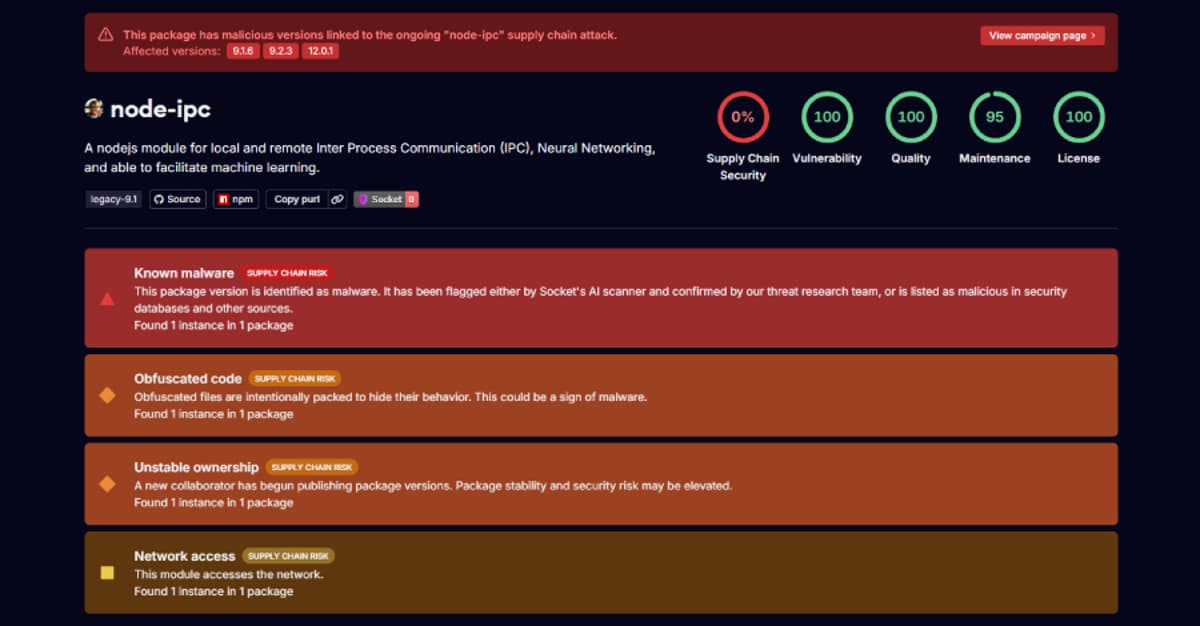
Stealer Backdoor Found in 3 Node-IPC Versions Targeting Developer Secrets
Security researchers have identified three compromised releases of the popular npm package node‑ipc (versions 9.1.6, 9.2.3 and 12.0.1) that embed a stealthy stealer/backdoor. The malicious code executes whenever the module is required, bypassing standard npm lifecycle hooks, and harvests roughly...

ThreatsDay Bulletin: PAN-OS RCE, Mythos cURL Bug, AI Tokenizer Attacks, and 10+ Stories
The ThreatsDay bulletin highlights a surge of active exploits, starting with Palo Alto Networks confirming limited attacks against its PAN‑OS CVE‑2026‑0300 buffer overflow, which grants root‑level code execution. Meta introduced Incognito Chat, a private AI interface that runs inference inside...
Ghostwriter Targets Ukrainian Government With Geofenced PDF Phishing, Cobalt Strike
The Belarus‑aligned threat group Ghostwriter has launched a new campaign against Ukrainian government entities, using geofenced PDF attachments that only deliver a malicious RAR archive when the victim’s IP originates from Ukraine. The archive drops a JavaScript version of PicassoLoader,...

Why Agentic AI Is Security's Next Blind Spot
Agentic AI is already deployed across enterprises, executing tasks and accessing data without security oversight. The article outlines three agent categories—general‑purpose coding assistants, MCP‑enabled vendor agents, and custom user‑built agents—each presenting distinct risk profiles. It argues that security teams must...
OpenAI Launches Daybreak for AI-Powered Vulnerability Detection and Patch Validation
OpenAI unveiled Daybreak, an AI‑powered platform that combines GPT‑5.5 models with Codex Security to automate vulnerability detection, threat modeling, and patch validation. The service offers three model variants—including a Trusted Access version for verified defensive work and a permissive Cyber...
Your Purple Team Isn't Purple — It's Just Red and Blue in the Same Room
The article argues that today’s purple‑team concept is ineffective because human handoffs slow response while attackers exploit vulnerabilities in seconds. In 2026 the average time from CVE disclosure to a working exploit is roughly ten hours, and AI‑assisted adversaries can...

Ollama Out-of-Bounds Read Vulnerability Allows Remote Process Memory Leak
A critical out‑of‑bounds read bug (CVE‑2026‑7482, CVSS 9.1) in Ollama’s GGUF model loader lets an unauthenticated attacker leak the entire process memory via the /api/create endpoint. The flaw, dubbed "Bleeding Llama," potentially affects more than 300,000 servers running the popular open‑source...
One Missed Threat Per Week: What 25M Alerts Reveal About Low-Severity Risk
The new Intezer AI SOC report analyzed more than 25 million security alerts across 10 million endpoints and identities. It found that roughly 1 % of alerts classified as low‑severity or informational correspond to real breaches—about one missed incident per week for a...

Linux Kernel Dirty Frag LPE Exploit Enables Root Access Across Major Distributions
A new Linux kernel local‑privilege‑escalation flaw, dubbed Dirty Frag, chains two page‑cache write bugs—one in the xfrm‑ESP subsystem and another in RxRPC—to obtain root on most major distributions. The vulnerability was reported on 30 April 2026 and, unlike prior race‑condition exploits, is deterministic...

PAN-OS RCE Exploit Under Active Use Enabling Root Access and Espionage
Palo Alto Networks disclosed a critical buffer‑overflow flaw (CVE‑2026‑0300) in the PAN‑OS User‑ID Authentication Portal that permits unauthenticated remote code execution with root privileges. Threat actors began probing the vulnerability on April 9, 2026 and achieved successful exploitation by mid‑April, injecting shellcode...

Day Zero Readiness: The Operational Gaps That Break Incident Response
The article argues that having an incident‑response retainer is insufficient without Day Zero operational readiness. It stresses that immediate visibility—especially into identity, cloud, endpoint, and logging systems—is the first priority when a breach is detected. The guide outlines common access bottlenecks,...

Vm2 Node.js Library Vulnerabilities Enable Sandbox Escape and Arbitrary Code Execution
An extensive set of twelve critical vulnerabilities has been disclosed in the popular vm2 Node.js library, which is used to sandbox untrusted JavaScript code. The flaws, each scoring 9.1‑10.0 on the CVSS scale, enable attackers to break out of the...

Mirai-Based Xlabs_v1 Botnet Exploits ADB to Hijack IoT Devices for DDoS Attacks
Researchers at Hunt.io have uncovered a new Mirai‑derived botnet, xlabs_v1, that hijacks IoT devices exposing Android Debug Bridge (ADB) on TCP 5555. The malware targets Android TV boxes, set‑top boxes, smart TVs and residential routers, then offers a DDoS‑for‑hire service with...

MuddyWater Uses Microsoft Teams to Steal Credentials in False Flag Ransomware Attack
Iranian‑backed MuddyWater disguised a ransomware campaign as a Chaos RaaS attack, using Microsoft Teams screen‑sharing to steal credentials and bypass MFA. The group focused on data exfiltration and persistence via DWAgent and AnyDesk rather than encrypting files. A code‑signing certificate...

The Hacker News Launches 'Cybersecurity Stars Awards 2026' — Submissions Now Open
The Hacker News has launched the Cybersecurity Stars Awards 2026, a global program that spotlights outstanding products, solutions, companies, and professionals in the security sector. Submissions open now and close on May 15, 2026, with winners to be announced on May 26, 2026. The awards...
Your AI Agents Are Already Inside the Perimeter. Do You Know What They're Doing?
Enterprises are rapidly deploying AI agents faster than identity‑security policies can keep up, creating a hidden layer of unmanaged activity that Gartner calls “identity dark matter.” Orchid Security’s new Ask Orchid AI engine surfaces these agents, evaluates NIST compliance, and...
Google's Android Apps Get Public Verification to Stop Supply Chain Attacks
Google announced that its Binary Transparency system will cover all production Android applications and Mainline modules starting May 1, 2026. The public, cryptographic ledger records metadata for each released binary, allowing anyone to confirm that the software matches Google’s intended build. By...

Critical Apache HTTP/2 Flaw (CVE-2026-23918) Enables DoS and Potential RCE
The Apache Software Foundation disclosed a critical vulnerability, CVE‑2026‑23918, in the HTTP/2 module of Apache HTTP Server 2.4.66, earning an 8.8 CVSS rating. The flaw is a double‑free in `mod_http2` that can be triggered by sending a HEADERS frame followed by...
DAEMON Tools Supply Chain Attack Compromises Official Installers with Malware
Kaspersky has uncovered a supply‑chain attack that trojanized DAEMON Tools Lite installers released between April 8 and early May 2026 (versions 12.5.0.2421‑12.5.0.2434). The compromised binaries launch a loader that contacts a command‑and‑control server, downloads a .NET info‑gatherer and a minimalist backdoor, and in...
Phishing Campaign Hits 80+ Orgs Using SimpleHelp and ScreenConnect RMM Tools
A phishing campaign dubbed VENOMOUS#HELPER has compromised over 80 U.S. organizations by masquerading as the Social Security Administration and delivering malicious Remote Monitoring and Management (RMM) tools. The attackers use legitimate SimpleHelp and ConnectWise ScreenConnect binaries to create a redundant...
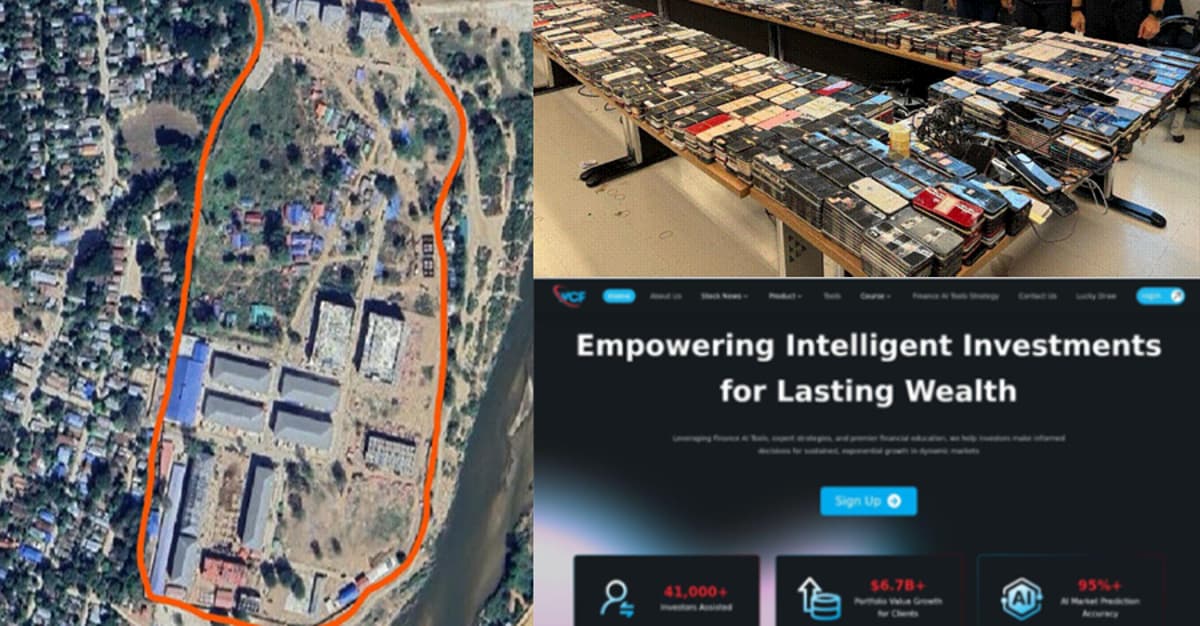
Global Crackdown Arrests 276, Shuts 9 Crypto Scam Centers, Seizes $701M
A coordinated international operation led by Dubai Police, the FBI and China’s Ministry of Public Security arrested at least 276 suspects, shut down nine cryptocurrency‑investment scam centers and seized roughly $701 million in illicit crypto assets. The crackdown, which also rescued...
Cybercrime Groups Using Vishing and SSO Abuse in Rapid SaaS Extortion Attacks
Researchers have identified two cyber‑crime groups, Cordial Spider and Snarky Spider, that specialize in rapid SaaS‑only extortion attacks. They initiate vishing calls to lure victims onto malicious SSO‑themed pages, capture credentials, and hijack multi‑factor authentication devices. Within an hour they...

China-Linked Hackers Target Asian Governments, NATO State, Journalists, and Activists
Trend Micro has uncovered a China‑aligned espionage group, SHADOW‑EARTH‑053, targeting government and defense networks across South, East and Southeast Asia and Poland, a NATO member, by exploiting unpatched Microsoft Exchange and IIS servers. The actors install Godzilla web shells and...

Top Five Sales Challenges Costing MSPs Cybersecurity Revenue
The managed security services market is set to jump from $38.3 billion in 2025 to $69.2 billion by 2030, yet many MSPs miss revenue because their go‑to‑market (GTM) approach fails to link technical security work with business outcomes. Cynomi’s GTM Academy Sales...
Poisoned Ruby Gems and Go Modules Exploit CI Pipelines for Credential Theft
A coordinated supply‑chain campaign dubbed BufferZoneCorp has published malicious Ruby gems and Go modules that act as sleeper packages. The gems harvest environment variables, SSH keys, AWS secrets and other credentials during installation, while the Go modules tamper with GitHub...

PyTorch Lightning and Intercom-Client Hit in Supply Chain Attacks to Steal Credentials
Threat actors compromised the PyTorch Lightning PyPI package, publishing malicious versions 2.6.2 and 2.6.3 on April 30, 2026. The payload drops the Bun JavaScript runtime and executes an obfuscated script that harvests GitHub tokens, cloud keys, and other developer credentials....

ThreatsDay Bulletin: SMS Blaster Busts, OpenEMR Flaws, 600K Roblox Hacks and 25 More Stories
The latest ThreatsDay bulletin highlights a wave of cyber threats, from Canadian police arresting three men operating an SMS‑blaster tower that sent phishing texts, to a malicious npm package that stole developers' .env files. Browser extensions openly selling user data,...

New Python Backdoor Uses Tunneling Service to Steal Browser and Cloud Credentials
Security firm Securonix disclosed a new Python‑based backdoor called DEEP#DOOR that embeds its payload inside a batch dropper, enabling fileless execution and multiple persistence mechanisms. The malware uses the public Rust tunneling service bore.pub for command‑and‑control, allowing operators to issue...

EtherRAT Distribution Spoofing Administrative Tools via GitHub Facades
Atos Threat Research Center uncovered a sophisticated EtherRAT campaign that spoofs administrative utilities and delivers malware via a dual‑stage GitHub distribution chain optimized for SEO. The malicious MSI installers impersonate tools such as PsExec and Sysmon, then install a Node.js‑based...

Google Fixes CVSS 10 Gemini CLI CI RCE and Cursor Flaws Enable Code Execution
Google patched a critical CVSS 10.0 remote‑code‑execution flaw in the Gemini CLI npm package and its GitHub Actions runner, which previously auto‑trusted workspace folders in headless CI mode. The update forces explicit folder trust and tightens tool allow‑listing in --yolo mode, closing a...
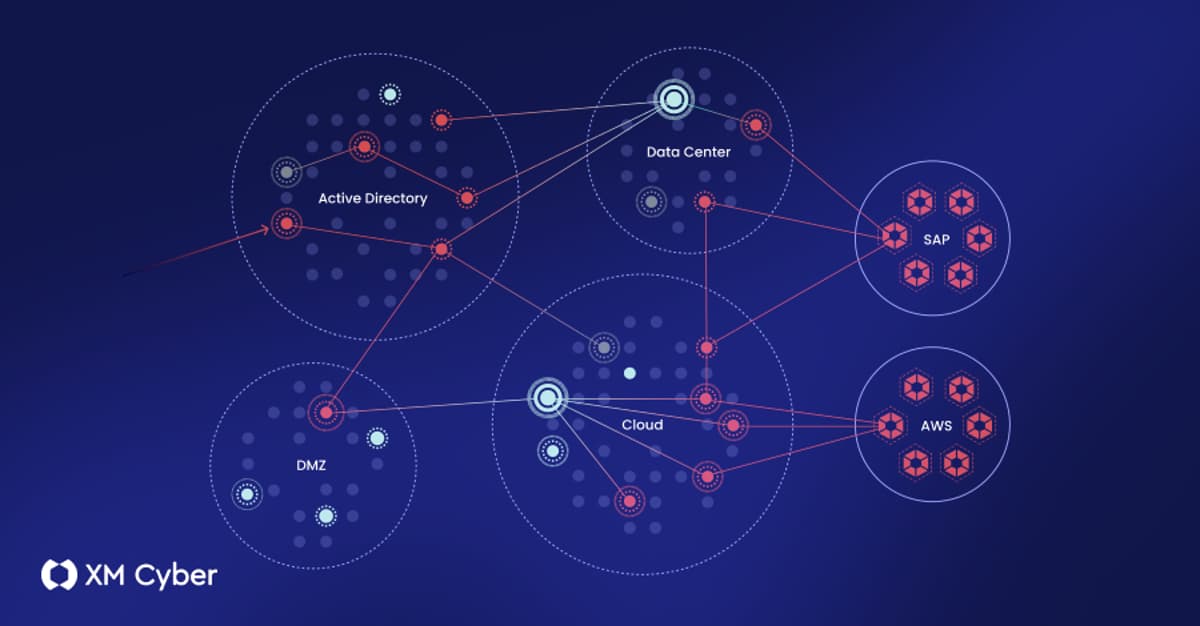
What to Look for in an Exposure Management Platform (And What Most of Them Get Wrong)
The article dissects exposure‑management platforms, outlining four architectural approaches—stitched portfolios, data aggregators, single‑domain specialists, and fully integrated solutions. It argues that only integrated platforms can correlate diverse exposure types, validate exploitability, and map realistic attack paths across on‑prem, cloud, and...

Critical cPanel Authentication Vulnerability Identified — Update Your Server Immediately
cPanel has issued emergency security updates to fix a critical authentication bypass vulnerability (CVE‑2026‑41940) that scores 9.8 on the CVSS scale. The flaw affects all supported cPanel and WHM versions and can allow unauthenticated attackers to gain full administrative control...

Brazilian LofyGang Resurfaces After Three Years With Minecraft LofyStealer Campaign
Brazilian cybercrime group LofyGang has resurfaced after a three‑year hiatus, launching a new Minecraft‑targeted campaign that distributes the LofyStealer (aka GrabBot) malware. The stealer is disguised as a popular Minecraft hack called "Slinky" and uses the game’s official icon to...
Why Secure Data Movement Is the Zero Trust Bottleneck Nobody Talks About
Everfox’s new Cyber360 report reveals that data movement, not identity or endpoints, is the hidden bottleneck in Zero Trust implementations. Eighty‑four percent of government security leaders view cross‑network data sharing as a top cyber risk, yet 53% still use manual...

Critical Unpatched Flaw Leaves Hugging Face LeRobot Open to Unauthenticated RCE
Researchers disclosed CVE‑2026‑25874, a critical deserialization flaw in Hugging Face’s LeRobot robotics platform. The bug stems from unsafe use of Python’s pickle in the async PolicyServer, allowing unauthenticated attackers to execute arbitrary code over gRPC. The vulnerability affects version 0.4.3 and...

After Mythos: New Playbooks For a Zero-Window Era
Anthropic’s Claude Mythos demonstrated that AI can locate operating‑system and browser flaws in minutes, collapsing the traditional patch window to near‑zero. The speed of AI‑driven discovery prompted an emergency meeting of Treasury Secretary Scott Bessent, Fed Chair Jerome Powell, and top banking...

Microsoft Confirms Active Exploitation of Windows Shell CVE-2026-32202
Microsoft revised its advisory to confirm active exploitation of CVE‑2026‑32202, a Windows Shell spoofing flaw with a CVSS score of 4.3. The vulnerability enables zero‑click credential theft via malicious LNK files that trigger automatic SMB authentication. It is part of...

⚡ Weekly Recap: Fast16 Malware, XChat Launch, Federal Backdoor, AI Employee Tracking & More
A newly uncovered Lua‑based malware called fast16, dating back to 2005, predates the infamous Stuxnet worm and appears designed to subtly corrupt high‑precision calculation software. Threat groups are active: UNC6692 is impersonating Microsoft Teams help desks to deliver a Snow...
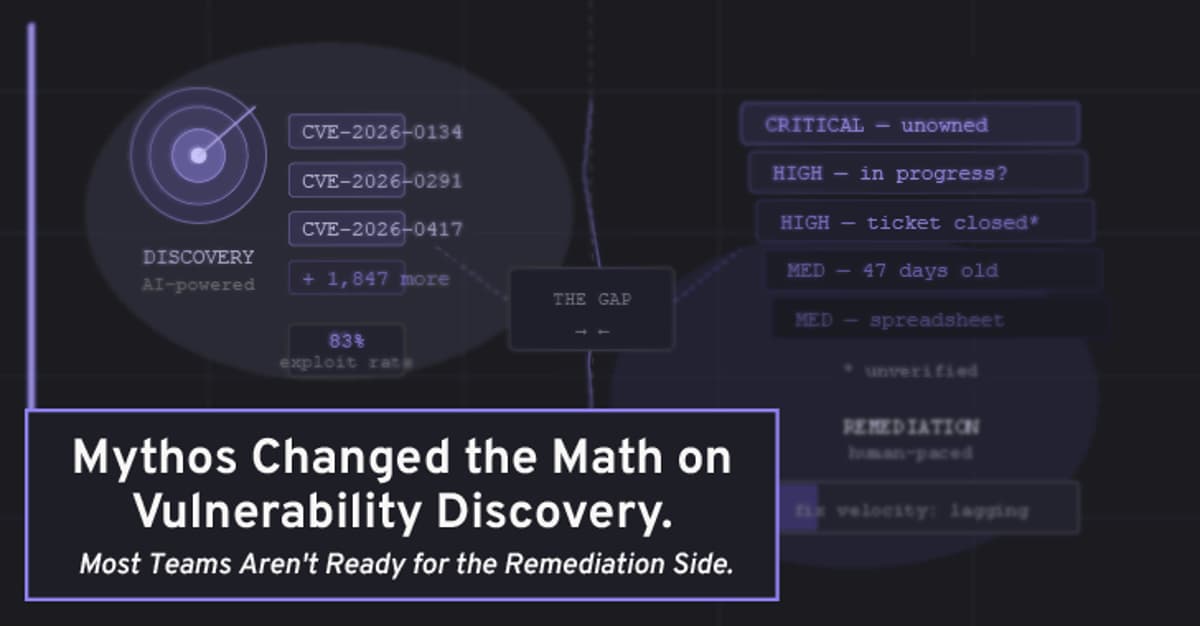
Mythos Changed the Math on Vulnerability Discovery. Most Teams Aren't Ready for the Remediation Side
Anthropic’s Claude Mythos AI dramatically accelerates vulnerability discovery, promising ten‑fold higher finding rates than traditional pentests. However, the article warns that most organizations lack the remediation infrastructure to handle the surge, creating a widening gap between detection and fix. It...

FIRESTARTER Backdoor Hit Federal Cisco Firepower Device, Survives Security Patches
U.S. CISA disclosed that a federal agency’s Cisco Firepower appliance was compromised in September 2025 by a new backdoor malware dubbed FIRESTARTER. The implant leverages two recently patched CVEs (2025‑20333, 2025‑20362) to gain root access and persists through firmware updates...