Erdal Ozkaya’s Cybersecurity Blog - Latest News and Information
Technology Pulse
EMAIL DIGESTS
Daily
Every morning
Weekly
Tuesday recap

Digital Forensics and Incident Response (DFIR) combines evidence collection with threat containment, forming a critical capability for CISOs. The guide outlines core functions—evidence preservation, malware and network analysis, and emerging cloud forensics—while stressing the need for pre‑enabled logging. It recommends a hybrid model that retains internal triage and leverages external specialists for complex cases. Legal considerations, including chain‑of‑custody and regulator‑mandated disclosure timelines, are highlighted as essential to protect evidence admissibility.

Network segmentation is the most effective control for safeguarding operational technology (OT) environments, limiting attackers to isolated zones rather than allowing lateral movement. Implementing segmentation in OT differs from IT because industrial protocols and legacy equipment resist typical firewall solutions...

Organizations lacking a tested incident response plan face escalating costs, reputational damage, and evidence loss during cyber attacks. The article outlines the NIST incident response lifecycle—preparation, detection, containment, and post‑incident review—and stresses integrating business continuity to meet recovery time objectives....

The 2021 Oldsmar water‑treatment hack exposed how connected operational technology (OT) can be weaponised, highlighting the stark contrast between OT and traditional IT security. In OT, availability outweighs confidentiality, because a brief outage can trigger safety incidents or regional blackouts....

The article argues that the modern CISO must become a business leader, not just a technical specialist. It stresses translating technical risk into revenue‑impact language for the board. Key skills include aligning security initiatives with business outcomes, building executive relationships,...

Quantum computing threatens to break today’s asymmetric encryption, making current data protection obsolete. The most immediate risk is a “harvest now, decrypt later” attack, where adversaries steal data today and decrypt it once quantum capabilities mature. Experts estimate viable quantum...
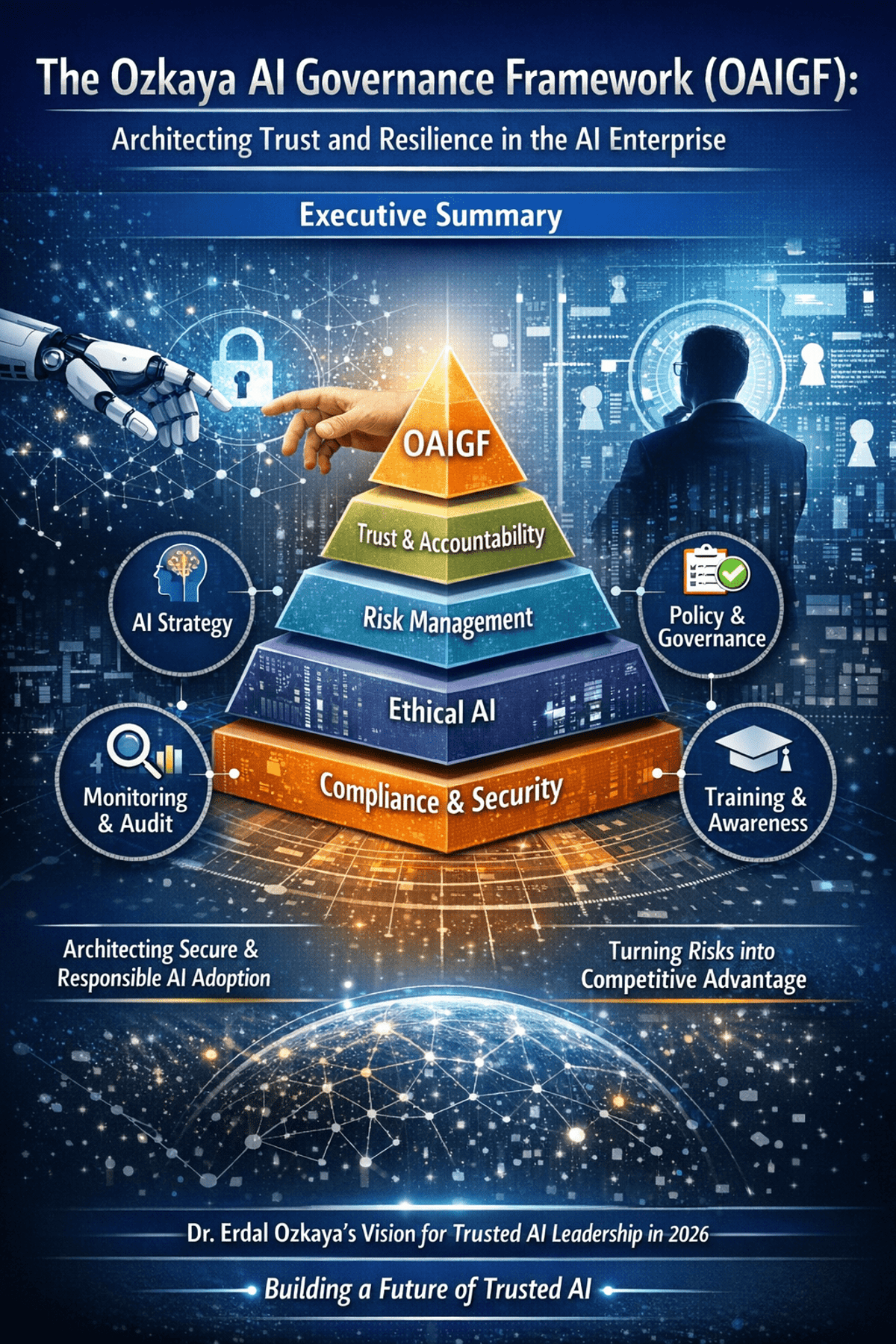
The Ozkaya AI Governance Framework (OAIGF) is a practitioner‑driven methodology that equips CISOs with a comprehensive blueprint for secure, ethical, and compliant AI deployment at enterprise scale. Building on standards such as NIST AI RMF and ISO/IEC 42001, the framework defines...

Anthropic’s Claude Code introduces a CLI‑based AI agent that can navigate repositories, draft patches, and run tests, turning code remediation into a near‑instant process. While the speed gains are compelling, the tool also grants autonomous execution rights that blur traditional...

Veteran CISOs are urged to abandon technical dashboards and become business risk leaders who speak the board’s language. By translating security concepts into revenue‑impact terms, aligning initiatives with corporate growth plans, and quantifying cyber risk in monetary values, they secure...
The author argues that AI did not break cybersecurity; longstanding governance failures did. AI merely amplified existing shadow‑IT practices and unclear risk ownership, exposing gaps that boards and CISOs have ignored. The piece calls for a shift from treating security...

The SEC is drafting rules that will require public companies to disclose their cybersecurity controls as part of regular financial reporting. This links cyber risk directly to compliance, forcing firms to treat security as a core reporting element. The article...

PwC‑affiliated firm A.F. Ferguson & Co. hosted a one‑day masterclass titled “Governing Cybersecurity in the AI Era – Digital Trust, Risk & Resilience” on 22 January 2026 in Karachi. More than 100 senior technology and business leaders, including CISOs, CIOs and CFOs,...

At SECON’s 2025 and 2026 conferences, the author highlighted a seismic shift in cyber risk, moving from classic phishing to automated, credential‑based attacks and AI‑driven threats. Data shows MFA bypass rates soaring to 45%, ransomware focusing on data theft, and...

The blog highlights the growing convergence of cybersecurity and intelligent transportation, emphasizing that autonomous vehicles and connected infrastructure are becoming "data centers on wheels." It outlines three core risk areas—V2X communication vulnerabilities, AI‑driven sensor attacks, and infrastructure resilience—and presents strategic...