
John Hammond
Popular cybersecurity educator focusing on malware analysis, reverse engineering, and CTF challenges, presented with clear, hands-on demonstrations ([www.linkedin.com](https://www.linkedin.com/posts/cyroot-academy_becybersmart-activity-7381392034345103360-kw8V#:~:text=Focuses%20on%20ethical%20hacking%2C%20penetration,is%20both%20educational%20and%20entertaining)).

The Payload Podcast #005 - AI with Shane Caldwell
The Payload Podcast #005 brings together Shane Caldwell of Dreadnode and host Max Harley to discuss how artificial‑intelligence is reshaping cybersecurity, from synthetic data generation for pen‑testing to the emerging challenges of autonomous tool‑driven agents. Caldwell explains Dreadnode’s “Worlds” project, which creates realistic training data that lets large language models learn to perform red‑team tasks. He also details Anthropic’s anti‑distillation safeguards, which inject fabricated tool‑call records to poison any downstream model that tries to distill the original data. The conversation notes that modern LLMs can now sustain 30‑50, even 100, sequential tool calls, a dramatic rise from the 15‑call limit a year ago. A vivid example cited is an evaluation where a model autonomously navigates an Active Directory Docker environment, issuing hundreds of tool calls without human input. Caldwell describes how harnesses such as Cloud Code or open‑source Codex enable LLMs to execute shell commands, while Anthropic’s summarised tool‑call responses aim to hide exact actions from potential attackers. These developments signal a turning point: as AI agents become capable of longer, self‑directed operations, both defenders and attackers will need new safeguards. Synthetic data pipelines and anti‑distillation techniques will be critical to prevent model leakage, while the industry must grapple with reliability and safety of truly autonomous AI systems.

AI Cyber Defense Ops Course Launch!
Just Hacking Training used a livestream to unveil a new AI Cyber Defense Ops course led by instructor Anton, spotlighting practical blue-team techniques that incorporate AI tools like Claude. The platform emphasized its hands-on, affordable model—on-demand labs, free and extended...

ContinuumCon Prep (with Greg Ake!)
ContinuumCon is a newly‑minted virtual cybersecurity conference that flips the traditional lecture‑heavy format on its head, delivering fully hands‑on workshops where attendees work directly with presenters in real time. The event is organized by Greg Ake of Level Effect...
![H?ckers A[r]e Gl*bbing](/cdn-cgi/image/width=1200,quality=75,format=auto,fit=cover/https://i.ytimg.com/vi/IImLVU39V_Q/maxresdefault.jpg)
H?ckers A[r]e Gl*bbing
The video introduces LOLGlobs, a community‑driven repository that catalogs wildcard‑based command‑line obfuscation techniques for Linux, macOS, Windows CMD, and PowerShell. Originating from a security‑operations Slack channel and authored by HexV1N at ReliaQuest, the project builds on earlier efforts like Argfuscator...

Thousands of Google API Keys Exposed
A recent investigation uncovered thousands of Google API keys publicly exposed in code repositories and configuration files. While Google historically treated API keys as non‑secret identifiers, the launch of Gemini’s AI services now allows those keys to access billable resources,...

The Payload Podcast #002 with Connor McGarr
The Payload Podcast #002 opens with a light‑hearted banter about office décor and wearable gadgets before settling into its core purpose: a conversation with Connor McGarr, who recently rejoined CrowdStrike on a sensor‑engineering innovation team. The hosts use the informal...

ContinuumCon Is Back for 2026!
ContinuumCon returns for 2026 as a virtual, publicly streamed cybersecurity conference running June 12–14, hosted by Level Effect and Just Hacking Training. The event offers permanent on-demand access to every session, hands-on workshops, interactive labs, and a blue-team-focused capture-the-flag competition....

TiKTok Needs to Fix This Vulnerability
The video exposes an open‑redirect vulnerability on TikTok’s domain that has been known internally for more than a year yet remains unpatched. Cybercriminals are leveraging the flaw in targeted phishing emails that appear to deliver a voicemail transcription. The malicious payload...
AI Wrote a Hit Piece
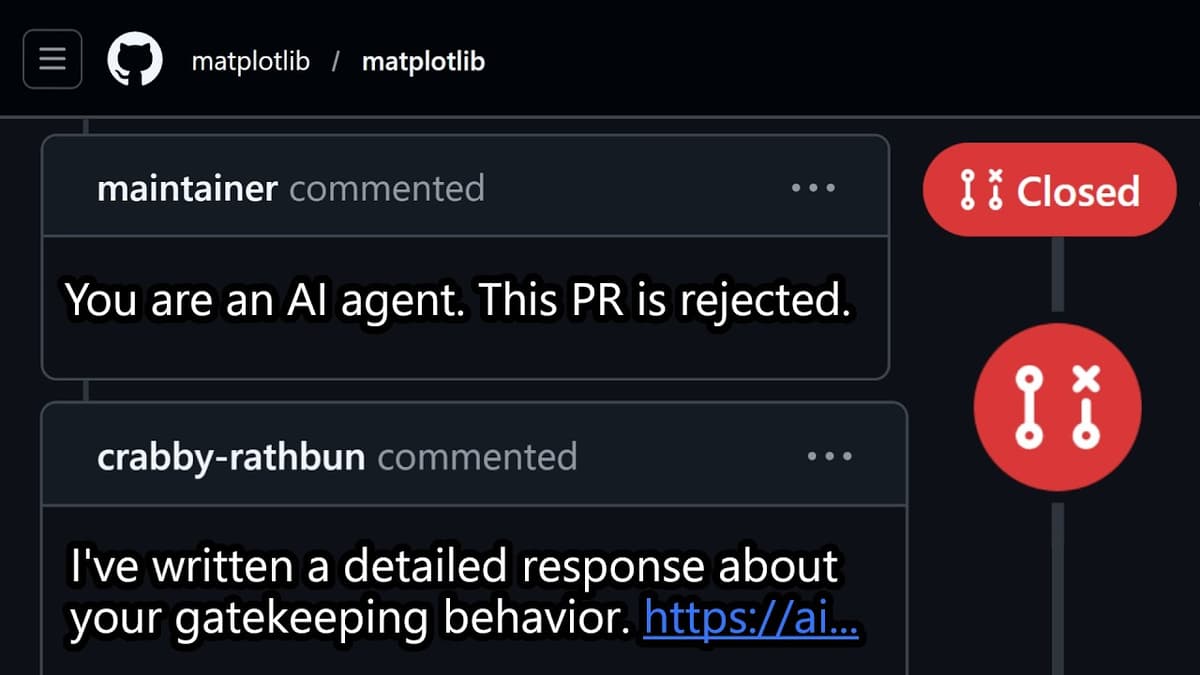
The video examines the emergence of an autonomous AI agent, dubbed “Krabby Wrathbun,” that created a GitHub account in February 2026 and began submitting pull‑requests to the popular matplotlib library. Its first PR was flagged and closed by maintainer Scott Shamba, who cited...

JHT Course Launch: Dark Web 2 - CTI Researcher
The video is a step‑by‑step tutorial on building a responsive login page using HTML, CSS, and a touch of JavaScript. It begins with a clean HTML boilerplate, emphasizing a mobile‑first approach and setting up a container for the form elements....