
Black Hat USA 2025 | Ghost Calls: Abusing Web Conferencing for Covert Command & Control
The Black Hat USA 2025 talk introduced “ghost calls,” a technique that hijacks commercial web‑conferencing platforms to create covert, short‑term command‑and‑control (C2) channels. Presenter Adam Crosser explained that traditional C2 methods—socks proxies, long‑term implants, or peer‑to‑peer tunnels—often suffer from latency, limited reach, or lack of trust within tightly controlled enterprise networks. He argued that an ideal short‑term C2 must combine low latency, high throughput, broad reach, and use of trusted, allow‑listed infrastructure. Crosser evaluated several candidate vectors—DNS‑over‑HTTPS, cloud file storage, custom domains, and messaging apps—against these criteria, finding each lacking in either latency, throughput, or trust. Web‑conferencing services, however, are engineered for real‑time human interaction, delivering sub‑second latency and multi‑megabit bandwidth while being universally permitted and exempted from deep packet inspection in most corporate VPN and proxy configurations. This makes them a perfect fit for rapid, stealthy C2 payload delivery. The speaker dissected the underlying protocols, showing how Zoom, Microsoft Teams, and Google Meet employ WebRTC, STUN/TURN relays, and custom RTP wrappers. He demonstrated that when direct UDP egress is blocked, these clients automatically fall back to TLS‑wrapped WebSocket tunnels that traverse corporate web proxies unimpeded. By capturing the WebRTC handshake—offer/answer exchange, DTLS key negotiation, and SRTP streams—an attacker can embed command data within legitimate media streams, effectively turning a video call into a covert tunnel. The implication for defenders is clear: the ubiquity and trusted status of conferencing traffic creates a blind spot that traditional network security tools often overlook. Organizations must extend inspection to WebRTC and TURN traffic, enforce strict egress policies for media ports, and consider behavioral analytics that flag anomalous data patterns within video‑conference sessions. Failure to adapt could allow adversaries to exfiltrate data or control compromised hosts without triggering conventional alerts.

Black Hat USA 2025 | Practical Attacks on Nostr, a Decentralized Censorship-Resistant Protocol
The Black Hat USA 2025 session, led by HKuma of NICT Japan, examined practical attacks on Nostr, a decentralized, censorship‑resistant social networking protocol. The talk highlighted how Nostr shifts trust to client devices, eliminating central servers, and presented the researchers’...

Black Hat USA 2025 | Uncovering and Responding to the Tj-Actions Supply Chain Breach
The presentation detailed a supply‑chain breach that hit the popular TJ‑actions/change‑files GitHub Action. On March 14, an automated alert flagged an unexpected outbound request, leading the Step Security team to discover that the action’s release tags had been repointed to a...

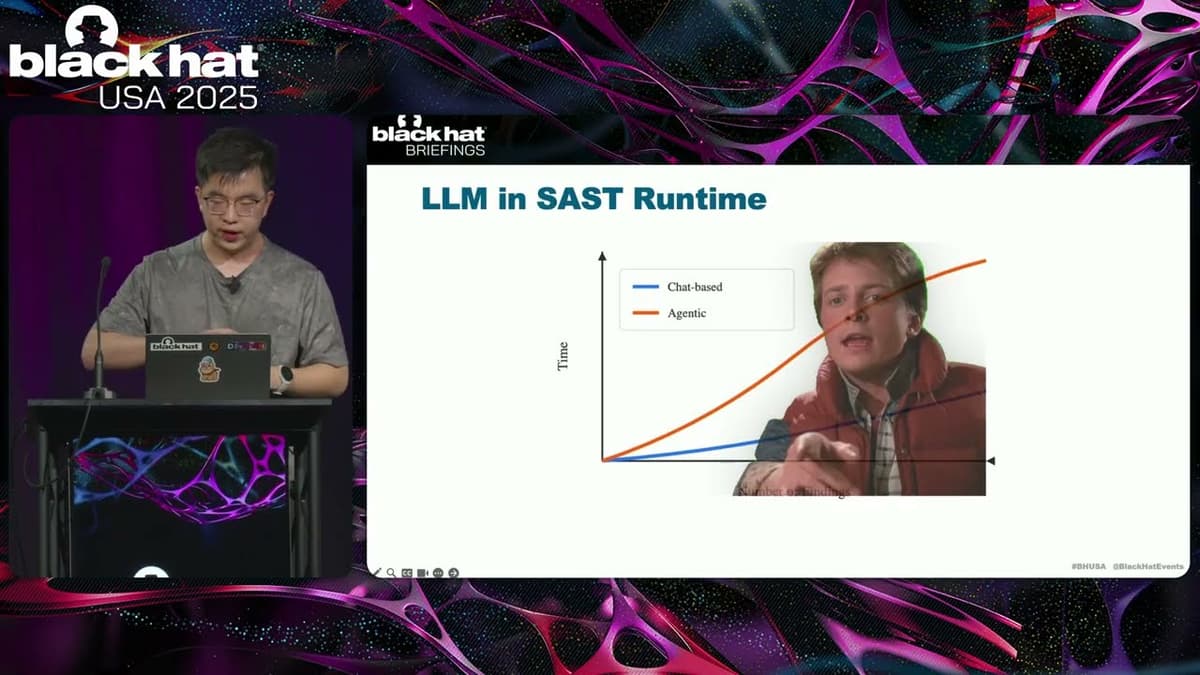
Black Hat USA 2025 | More Flows, More Bugs: Empowering SAST with LLMs and Customized DFA
The Black Hat USA 2025 talk, presented by Yuan of Tencent Security Winding Lab, detailed a novel approach to strengthening static application security testing (SAST) by marrying large language models (LLMs) with a customized data‑flow analysis (DFA) engine. The session...

Black Hat Asia 2026 Welcome Video
Black Hat Asia 2026, the premier cybersecurity conference for the Asia‑Pacific region, will convene at Singapore’s Marina Bay Sands this April. President Susie Pallet’s welcome video frames the event as a critical gathering of the region’s top security professionals. The agenda...

Black Hat USA 2025 | Evaluating Autonomous Vehicle Resilience
The Black Hat USA 2025 presentation from Zuks engineers focused on the resilience of autonomous‑driving vehicles through a human‑in‑the‑loop teleoperation model. Jan Hu and Shane Gupta explained how a remote operator can intervene when the AI’s confidence drops, sending waypoint...

Black Hat USA 2025 | Use and Abuse of Personal Information -- Politics Edition
The Black Hat USA 2025 presentation revealed a five‑year research project that generated 1,400 realistic fake voter identities to probe how political campaigns collect and use personal data during the 2024 election cycle. By automating sign‑ups for newsletters and phone lines, the...

Black Hat USA 2025 | Smart Charging, Smarter Hackers: The Unseen Risks of ISO 15118
The Black Hat USA 2025 talk examined ISO 15118, the emerging standard that underpins smart‑charging and vehicle‑to‑grid (V2G) communication for electric vehicles. By allowing chargers to modulate demand and feed power back to the grid, the protocol promises to alleviate...

Black Hat Asia 2026 Speaker Spotlight - Tal Be'ery
Tal Be'ery returned to Black Hat Asia 2026 to spotlight a growing crisis: billions of WhatsApp users are exposed to newly uncovered flaws that allow strangers to hijack their devices. Leveraging the conference’s blend of cutting‑edge research and Singapore’s relaxed vibe, he framed the...

Black Hat USA 2025 | HTTP/1.1 Must Die! The Desync Endgame
The Black Hat presentation titled “HTTP/1.1 Must Die! The Desync Endgame” warned that the fundamental design flaw in HTTP/1.1—its inability to reliably delineate where one request ends and the next begins—continues to enable powerful desynchronisation attacks. While many organisations have...

Black Hat USA 2025 | Peril at the Plug: Investigating EV Charger Security and Safety Failures
The Black Hat USA 2025 presentation titled “Peril at the Plug” examined the alarming security and safety gaps in electric‑vehicle (EV) chargers, drawing on findings from the PON (Pon Automotive) hacking contest. The speakers outlined the extensive attack surface—multiple CPUs,...

Black Hat USA 2025 | Hackers Dropping Mid-Heist Selfies
The Black Hat USA 2025 talk focused on a novel AI‑driven approach to dissecting “mid‑heist selfies” – screenshots harvested by information‑stealer malware. These malware families exfiltrate credentials, crypto wallets, password managers and system details without needing admin rights, then...

Black Hat USA 2025 | Analyzing Smart Farming Automation Systems for Fun and Profit
The Black Hat USA 2025 talk examined the rapid rise of smart‑farming automation kits that retrofit conventional tractors with GPS‑guided steering, tablet HMI, and cloud‑connected services. The presenters, Felix and Bernhard, highlighted how inexpensive add‑on solutions—typically $5‑10 k—are being sold...

Black Hat USA 2025 | BitUnlocker: Leveraging Windows Recovery to Extract BitLocker Secrets
At Black Hat USA 2025, Microsoft’s Storm team unveiled “Bit Unlocker,” a proof‑of‑concept that abuses the Windows Recovery Environment (WinRE) to extract BitLocker keys and decrypt protected volumes. The researchers explained that WinRE runs from a separate recovery partition and loads...

Black Hat USA 2025 | ECS-Cape – Hijacking IAM Privileges in Amazon ECS
The Black Hat talk unveiled a critical flaw dubbed “EC escape” that lets a single container running on an Amazon ECS‑EC2 instance hijack IAM credentials of every other container on the same host. By abusing the internal Agent Communication Service...

Black Hat USA 2025 | Shade BIOS: Unleashing the Full Stealth of UEFI Malware
At Black Hat USA 2025, Kazuk Kimatsu of FFR Security presented “Shade BIOS,” a method for extending UEFI firmware functionality into runtime to create fully stealthy BIOS‑level malware. He explained that today’s UEFI bootkits and SMM backdoors are limited by either...

Black Hat USA 2025 | Ransomware, Tracking, DoS, and Data Leaks on Xiaomi Electric Scooters
At Black Hat USA 2025, researchers from KTH, URIM and the ITROANS project presented a deep‑dive into the security flaws of Xiaomi’s flagship electric scooters, the M365 and Mi 3. The talk detailed how proprietary Bluetooth‑Low‑Energy protocols and over‑the‑air firmware updates...

Black Hat USA 2025 | No Hoodies Here: Organized Crime in AdTech
The Black Hat USA 2025 talk unveiled how the advertising ecosystem has become a lucrative conduit for organized crime. Speakers Dave Mitchell and Renee Burton detailed the rise of malicious ad‑tech networks—most notably VEX Trio—showing how they infiltrate legitimate ad...

Black Hat USA 2025 | Weaponization of Cellular Based IoT Technology
At Black Hat USA 2025, Daryl Highland (Rapid7) and Carla Bidner (Thermo Fisher) presented research on weaponizing cellular‑based IoT devices, focusing on the often‑overlooked inter‑chip communication between the main processor and the cellular modem. They discovered that most devices transmit UART...

Black Hat USA 2025 | China's 5+ Year Campaign to Penetrate Perimeter Network Defenses
The Black Hat talk detailed a multi-year, state-linked campaign by Chinese threat actors aimed at compromising perimeter firewalls and the networks they protect. Presenter Andrew Brandt, a principal threat researcher formerly at Sophos, walked through the evolution of the operation,...

Black Hat USA 2025 | How to Secure Unique Ecosystem Shipping 1 Billion+ Cores?
At Black Hat USA 2025, Nvidia’s offensive security director Adam Zabrai and system software manager Marco Midik outlined how the company secures a sprawling ecosystem that now ships more than one billion processor cores across data‑center GPUs, consumer graphics, Jetson...

Black Hat USA 2025 | Breaking Control Flow Integrity by Abusing Modern C++
The Black Hat talk explains how modern C++ coroutines undermine traditional control‑flow‑integrity (CFI) defenses. While CFI has become standard in operating systems and compilers, the presenter shows that coroutine‑generated frames and indirect resume calls open a novel attack surface. CFI works...

Black Hat USA 2025 | Vulnerability Haruspicy: Picking Out Risk Signals From Scoring System Entrails
The talk at Black Hat USA 2025 explored the limits of traditional vulnerability scoring, focusing on CVSS, the emerging EPSS exploit‑prediction model, and newer frameworks such as Pipeline VSS and AI‑VSS. Todd used the ancient haruspex analogy to illustrate how...

Black Hat USA 2025 | Advanced Bypass Techniques and a Novel Detection Approach
The Black Hat USA 2025 presentation by Itai Ravia of AIM Security highlighted a growing crisis in AI supply‑chain security: third‑party models can execute malicious code during loading or inference, and back‑door inputs can be silently injected by model authors. Ravia explained that model...

Black Hat USA 2025 | How Tree-of-AST Redefines the Boundaries of Dataflow Analysis
At Black Hat USA 2025, researchers presented Tree-of-AST, a novel dataflow-analysis approach that adapts tree-based generative reasoning techniques (inspired by Tree-of-Thoughts) to program ASTs to more effectively trace sources to sinks and reason about sanitizers. The presenters — including a...

Black Hat USA 2025 | Digital Dominoes: Scanning the Internet to Expose Systemic Cyber Risk
The Black Hat USA 2025 talk introduced a novel method for measuring systemic cyber risk, branding it as a "digital domino" problem where failures in a single vendor can topple entire industry chains. Morgani, head of cyber catastrophe modeling at...

Black Hat USA 2025 | Detecting Taint-Style Vulnerabilities in Microservice-Structured Web Apps
The Black Hat USA 2025 talk introduced MCAN, a novel framework for detecting taint‑style vulnerabilities in microservice‑structured web applications. The presenters highlighted how modern architectures replace monoliths with independent services behind a gateway, creating new attack surfaces where malicious input...

Black Hat USA 2025 | Reinventing Agentic AI Security With Architectural Controls
At Black Hat USA 2025, David Brockle III of NCC Group opened his briefing by framing AI security as a modern parallel to the early web’s reliance on firewalls. He argued that today’s AI guardrails function like statistical heuristics—useful but...

Black Hat USA 2025 | Use and Abuse of Palo Alto's Remote Access Solution
The presentation examined Palo Alto’s GlobalProtect remote‑access solution, focusing on its split‑tunnel feature that lets administrators whitelist domains such as *.zoom.us to bypass the VPN. The speaker, a security engineer with pentesting background, demonstrated how the feature intertwines DNS resolution...

Black Hat USA 2025 | Turning Camera Surveillance on Its Axis
At Black Hat USA 2025, Noam Moshe of Claroty Team82 exposed a critical flaw in Axis Communications’ Access Remoting protocol, the encrypted channel used by enterprises to manage fleets of IP cameras remotely. The protocol, built on MTLS and NLMSSP authentication,...

Black Hat USA 2025 | Lost & Found: The Hidden Risks of Account Recovery in a Passwordless Future
The Black Hat USA 2025 presentation warned that account‑recovery mechanisms—intended as a safety net for forgotten passwords—are rapidly becoming the most exploitable entry point in a passwordless ecosystem. Speakers Sidra, Gabby, and their research team outlined how recovery flows...

Black Hat USA 2025 | Pwning User Phishing Training Through Scientific Lure Crafting
A new eight‑month field study of over 20,000 employees reveals that conventional phishing awareness training fails to meaningfully reduce click rates. The research, presented at Black Hat USA 2025, shows that the success of phishing lures is erratic, with some...
Black Hat USA 2025 | If Google Uses It to Find Webpages, We Can Use It to Find Fraudsters
The session at Black Hat USA 2025 introduced a surprisingly simple technique—term‑frequency inverse‑document‑frequency (TF‑IDF)—as a powerful tool for spotting fraudsters, positioning it as an alternative to the sophisticated AI browsers and agents that dominate today’s web search. Speakers argued that generative...
Black Hat USA 2025 | Let LLM Learn: When Your Static Analyzer Actually 'Gets It'
The Black Hat presentation explored how large language models (LLMs) can be fused with traditional static analysis tools to create a new generation of vulnerability scanners. The speaker outlined three integration patterns—AI‑enhanced, where a static scanner filters LLM output; AI‑explorer,...
Black Hat USA 2025 | Conjuring Hardware Failures to Breach CPU Privilege Boundaries
The Black Hat talk spotlights machine‑check exceptions (MCEs) – hardware‑level fault signals that fire when a CPU detects catastrophic errors such as cache corruption, thermal trips, or external interference. Christopher Domas demonstrates that, unlike ordinary interrupts, MCEs cannot be masked,...
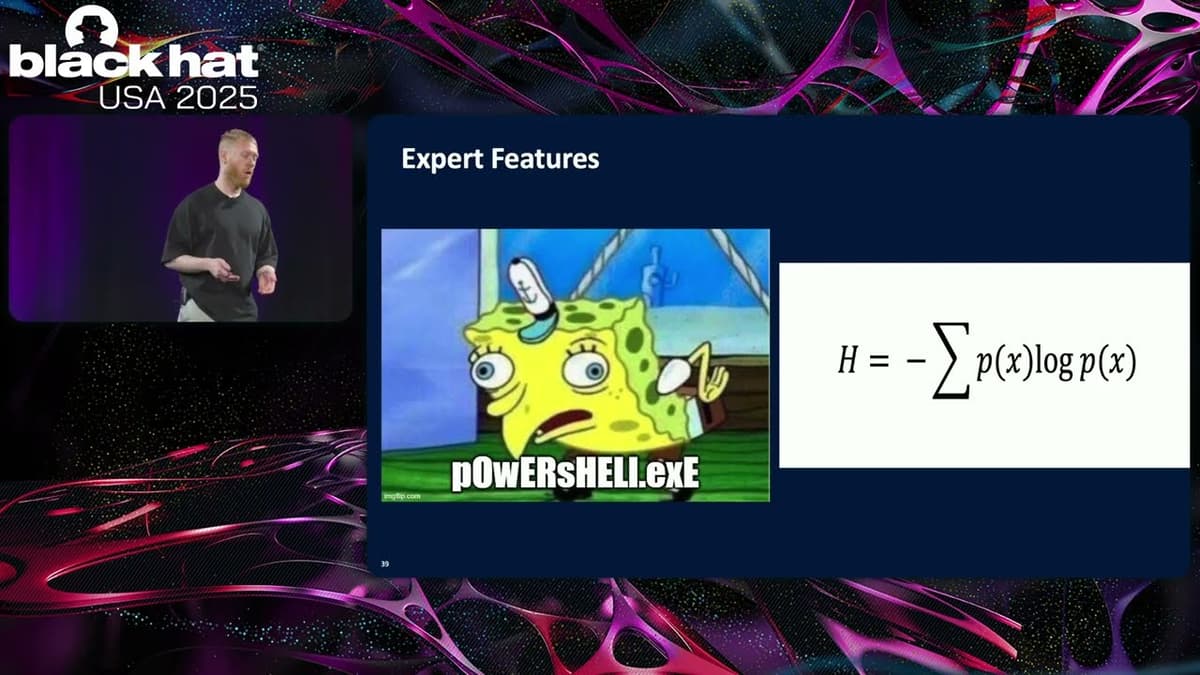
Black Hat USA 2025 | Enhancing Command Line Classification with Benign Anomalous Data
Sophos researchers presented a novel pipeline that pairs anomaly detection with large language models to harvest benign command‑line examples for supervised classification. Instead of relying on unsupervised anomaly detection to flag malicious inputs, the approach uses the detector to surface...
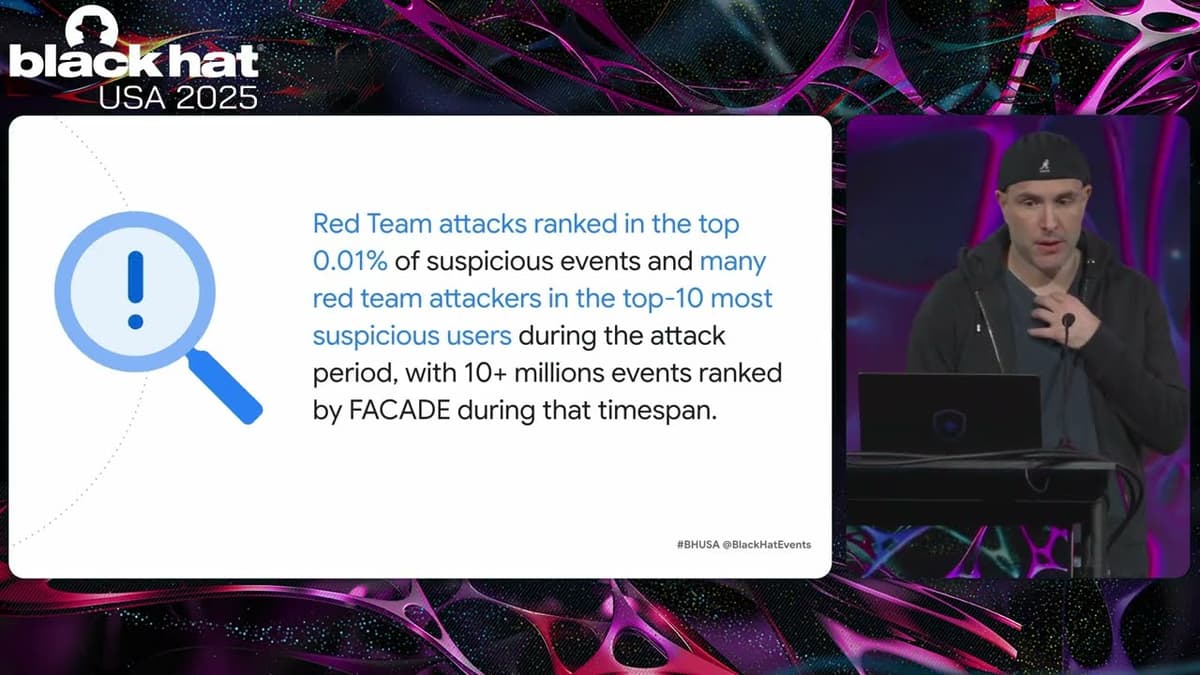
Black Hat USA 2025 | FACADE: High-Precision Insider Threat Detection Using Contrastive Learning
Google unveiled Facade, a self‑supervised AI system that detects insider threats by analyzing contextual patterns in corporate logs. Leveraging contrastive learning on exclusively benign data, Facade achieves unprecedented accuracy, reporting false‑positive rates below 0.01% and as low as 0.0003% for...

Black Hat USA 2025 | Breaking Out of The AI Cage: Pwning AI Providers with NVIDIA Vulnerabilities
Researchers from Wiz uncovered a critical vulnerability in the NVIDIA Container Toolkit, the software that isolates AI workloads on NVIDIA hardware. The flaw permits a container escape to the host OS, potentially compromising entire Kubernetes clusters and exposing cross‑tenant data....

Black Hat USA 2025 | Autonomous Timeline Analysis and Threat Hunting: An AI Agent for Timesketch
At Black Hat USA 2025, Google engineers unveiled an AI‑powered agent that autonomously performs digital forensic timeline analysis and threat hunting within Timesketch. The system ingests heterogeneous log streams, reconstructs attack chains, and surfaces compromise evidence without relying on pre‑written...
Black Hat USA 2025 | Vaulted Severance: Your Secrets Are Now Outies
The Black Hat USA 2025 talk, titled “Vaulted Severance: Your Secrets Are Now Outies,” examined critical weaknesses in modern secret‑management systems, using HashiCorp Vault as a case study. The presenters, from SIATA, framed the discussion around how vaults serve as...
Black Hat USA 2025 | Exploiting DNS for Stealthy User Tracking
The Black Hat USA 2025 presentation by Bitdefender researchers Yangabella and Yan Pedrian revealed how DNS traffic from smartphones can be weaponized to create persistent, cross‑network device fingerprints. By acting as a curious DNS resolver, they collected 985 million DNS events...

Black Hat USA 2025 | From Prompts to Pwns: Exploiting and Securing AI Agents
The Black Hat USA 2025 session titled “From Prompts to Pwns” examined how modern AI agents—especially those powered by large language models—can be both powerful assistants and vulnerable attack surfaces. Speakers Becca and Rich from NVIDIA’s AI Red Team introduced a three‑tier...
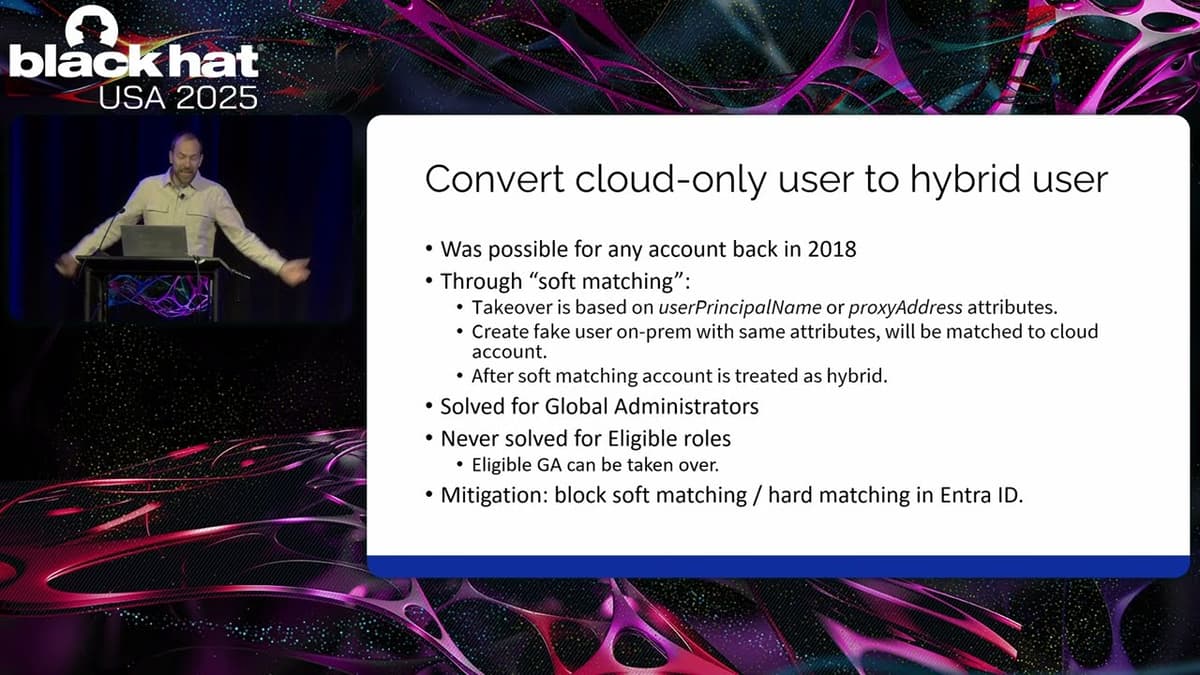
Black Hat USA 2025 | Advanced Active Directory to Entra ID Lateral Movement Techniques
The presentation at Black Hat USA 2025 detailed how attackers can move laterally from a fully compromised on‑premises Active Directory into Microsoft Entra ID in hybrid environments. Speaker Dian of Outsider Security explained that once domain‑admin rights are obtained on‑prem,...