
Arms Without Strings: What Buying Chinese Military Technology Really Means
The May 2025 India‑Pakistan clash and the February 2026 US‑Israel‑Iran war thrust Chinese military technology into the spotlight, showcasing the J‑10CE fighter, PL‑15 missiles and BeiDou navigation in combat. Beijing’s offer bundles low unit prices, flexible financing, minimal political licensing, joint‑production options and ready access to dual‑use components, contrasting sharply with the bureaucratic delays that have hampered Western programs such as the F‑35. While China’s share of global arms exports remains modest at 5.6 percent, its ability to supply integrated weapon systems without strings is reshaping procurement choices in South Asia and the Middle East. The article weighs these advantages against thin after‑sales support, sanctions exposure and strategic dependence on Beijing’s satellite network.

Weaponizing Supply Chains: How Iran and China Drive Strategic Food Insecurity in Modern Conflict
Iran’s coordinated mine deployment and fast‑boat attacks forced the Strait of Hormuz to close, while Beijing simultaneously imposed sweeping export bans on urea and NPK fertilizers. The dual choke‑points halted roughly one‑third of global seaborne fertilizer trade and cut up...

Inside the Islamic State Recoilless Gun Program | ARES
Armament Research Services released Special Report 6 detailing Islamic State’s home‑made light recoilless guns, including four conventional types and a newly documented fifth variant that carries a sulphur‑mustard chemical payload. The weapons share a common 89 mm barrel, folding fins and a...
A Memorandum Is Not a Strategy: What the Iran MoU Must Contain to Be More Than a Deferral
The U.S. is drafting a one‑page memorandum of understanding (MoU) with Iran following a recent de‑escalation, but Congress warned that without a clear theory of victory the agreement could merely postpone core issues. Testimony from Defense Secretary Pete Hegseth and...
Small Wars Journal and Arizona State University to Participate in SOF Week 2026
Small Wars Journal (SWJ) and multiple Arizona State University (ASU) security initiatives will attend SOF Week 2026 in Tampa, the premier gathering of the international special‑operations community. The partnership brings together academic programs, research centers, and publications such as Inter...

Intel Suggests Iran’s Missiles Aren’t Gone
U.S. intelligence reports that Iran still possesses roughly 70% of its pre‑war missile arsenal, including both ballistic and cruise systems. The data show 30 of the 33 missile sites along the Strait of Hormuz have been rebuilt, contradicting the Trump...
Persistence Over Power: A Lebanese Model of Maritime Denial
The article argues that Lebanon can secure its maritime domain by adopting a denial‑focused swarm strategy that relies on distributed unmanned systems and continuous presence rather than costly fleet expansion. Low‑cost autonomous vessels provide endurance, redundancy and legal compliance in...

AI-First Professional Military Education: Validating the Grade Chain Before the Kill Chain
The Department of War’s AI‑first strategy calls for AI agents to aid commanders in the high‑stakes kill chain, yet many Professional Military Education (PME) institutions hesitate to trust the same technology for grading student work. The article argues that the...

The Insurance Weapon: How Commercial Risk Logic Became an Irregular Warfare Tool at Hormuz
In February 2026, coordinated U.S.–Israeli airstrikes triggered a fivefold surge in war‑risk marine insurance premiums, prompting Lloyd’s Joint War Committee to label the entire Arabian Gulf a conflict zone. The resulting premium spikes—up to 1% of hull value, roughly $800,000 per...

China’s Occupation Playbook for Taiwan Is Already Written
New research from the Lowy Institute and the Irregular Warfare Center outlines a detailed playbook for how China intends to occupy Taiwan after a military seizure. The authors argue Beijing has shifted from accommodation to a phased subjugation strategy that...

The MQ-9 Gets Cheaper Teeth
General Atomics demonstrated that an Air Force MQ‑9 Reaper can shoot down aerial targets using the laser‑guided APKWS rocket, which costs $25,000‑$40,000 per round—cheaper than the $30,000 Iranian Shahed attack drone it aims to destroy. The test highlights a shift...

NATO Backs Renewables; U.S. Objects
NATO has publicly embraced renewable energy as a core element of alliance security after the Iran war disrupted fossil fuel imports, prompting concerns about jet‑fuel shortages for combat aircraft. A recent Energy Security Centre of Excellence (ESCE) report calls for...

Part 1: The U.S. Munitions Problem
The Center for Strategic and International Studies (CSIS) report released in late April finds that the 39‑day air campaign against Iran depleted seven critical U.S. missile stockpiles, deepening a pre‑existing shortfall for near‑peer war readiness. These weapons—Tomahawk, JASSM, PrSM, SM‑3,...

SOF Weekly Update – May 11, 2026
The SOF Weekly Update for May 11, 2026 highlights several key developments across special operations and global security. The joint Flintlock exercise in Africa concluded, while the African Lion drill suffered a fatality and a missing U.S. soldier. U.S. forces are expanding...

Legos at War: Iranian Information Operations
Iran has escalated its information operations amid U.S. military actions, deploying fast‑produced Lego‑style animation and AI‑generated memes that mock American leaders and highlight geopolitical grievances. The small firm Explosive Media released about ten videos in 24‑hour cycles, while Iranian embassies...

Delegated Violence: Jihadist Organizations and the Strategic Logic of Small Wars
The article argues that modern great‑power strategy increasingly relies on delegating violence to non‑state proxies, turning “small wars” into a technology of indirect confrontation. It traces this logic from Cold‑War U.S. support for Afghan mujahideen, through the rise of Turkish...

Can China Stop Its Demographic Slide? Can the United States?
China’s fertility rate continues to fall despite the shift from a one‑child policy to two‑ and three‑child allowances, leaving the nation on track for a loss of roughly 786 million people by 2100. RAND researchers warn that a shrinking, aging workforce...

5/8/26 National Security and Korean News and Commentary
The Small Wars Journal roundup bundles a dozen national‑security commentaries and a parallel set of Korean‑focused briefs. Highlights include Iran’s internal stalemate and its anti‑Trump video campaign, Anthropic’s Mythos model rattling the White House AI strategy, and demographic forecasts warning...

A Battle of Wits, Not Metal: How Irregular Warfare Is Preempting Convergence in the Indo-Pacific
The Indo‑Pacific is witnessing a strategic "battle of wits" where irregular warfare campaigns are deliberately shaping the environment before any kinetic conflict. By contesting sustainment, weaponizing controlled escalation, reshaping political geometry, and creating decision‑making friction, adversaries are eroding the pre‑conditions...

Subnational Diplomacy in a Fragmenting World
The essay highlights the rise of subnational diplomacy as a response to a fragmented global governance system shaped by intensified U.S.-China rivalry. It traces the structural shift toward great‑power contestation, noting how both Washington and Beijing have rewired their economies...

Davos, Munich, Nashville: Taking the National Security Conversation Beyond the Beltway
The fifth Asness Summit in Nashville, hosted by Vanderbilt’s Institute of National Security, gathered senior military leaders, policymakers, and industry innovators to rethink U.S. defense strategy. Speakers urged shared‑risk contracts, rapid scaling of drone production, and a shift from deterrence...

Gen. Larry D. Welch Deterrence Writing Award (Due 6/1/26) | Strategic Command Academic Alliance
The United States Strategic Command (USSTRATCOM) is sponsoring the Gen. Larry D. Welch Deterrence Writing Award, with submissions due June 1 2026. The competition accepts papers from junior (undergraduate and master’s) and senior (doctoral, post‑doc and professional) researchers on any strategic deterrence...
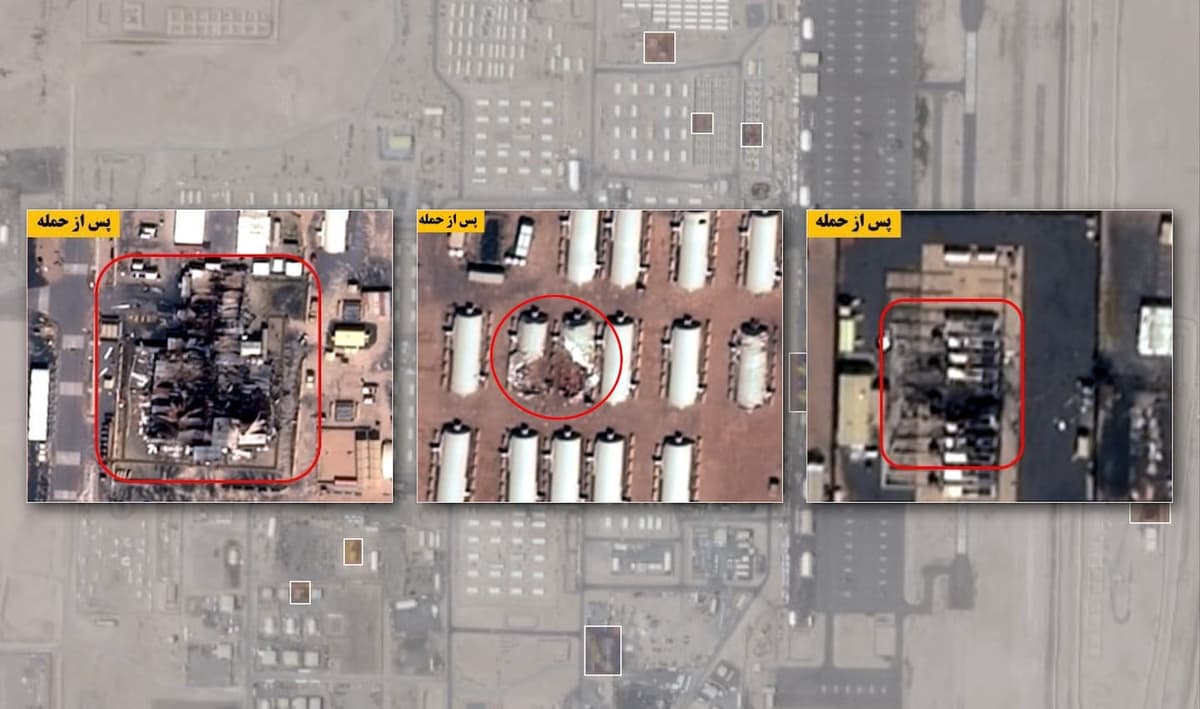
The American Military Base: Untouchable No More?
Satellite imagery reviewed by the Washington Post identified at least 228 damaged structures across 15 U.S. facilities in the Middle East during the Iran‑U.S. war. The strikes hit fuel depots, barracks, radars, communications nodes, Patriot batteries and aircraft, showing a...

2026 Counterterrorism Strategy | The White House
President Trump signed the 2026 U.S. Counterterrorism Strategy, the first formal CT blueprint of his second term. The document places hemispheric narcoterrorism—cartel‑linked drug trafficking that fuels terror—at the top of the priority list, followed by five external‑operation Islamist groups such...

How America’s Adversaries Learned to Weaponize Reality
The article argues that Russia, China and Iran have mastered narrative warfare, using reflexive control, discourse power and revolutionary ideology to shape perceptions and sustain political influence despite military setbacks. Russia fragments adversary views, China conditions long‑term discourse, and Iran...

Testing “On An Equal Basis” Or a Three-Way Arms Control Agreement
U.S. Under Secretary Thomas DiNanno claimed China conducted a yield‑producing nuclear test on June 22, 2020, using a decoupling technique to mask seismic signals. The CTBTO refuted the claim, stating the detected events were far below the treaty’s detection threshold....

5/6/26 National Security and Korean News and Commentary
The June 5 roundup by retired Special Forces Colonel David Maxwell surveys escalating security challenges across the Middle East and Northeast Asia. It highlights Iran’s deepening ties with China and Russia on drone production, a surge in Iranian attacks on U.S. assets,...

The Digital Insurgency: Cyber Operations and the Future of Resistance
In the fourth episode of the SOF Professional Podcast, irregular‑warfare scholar Tom Johansmeyer examines how cyber operations intersect with reinsurance, parametric insurance and economic security. He argues that the true metric of a cyber catastrophe is the economic damage it...
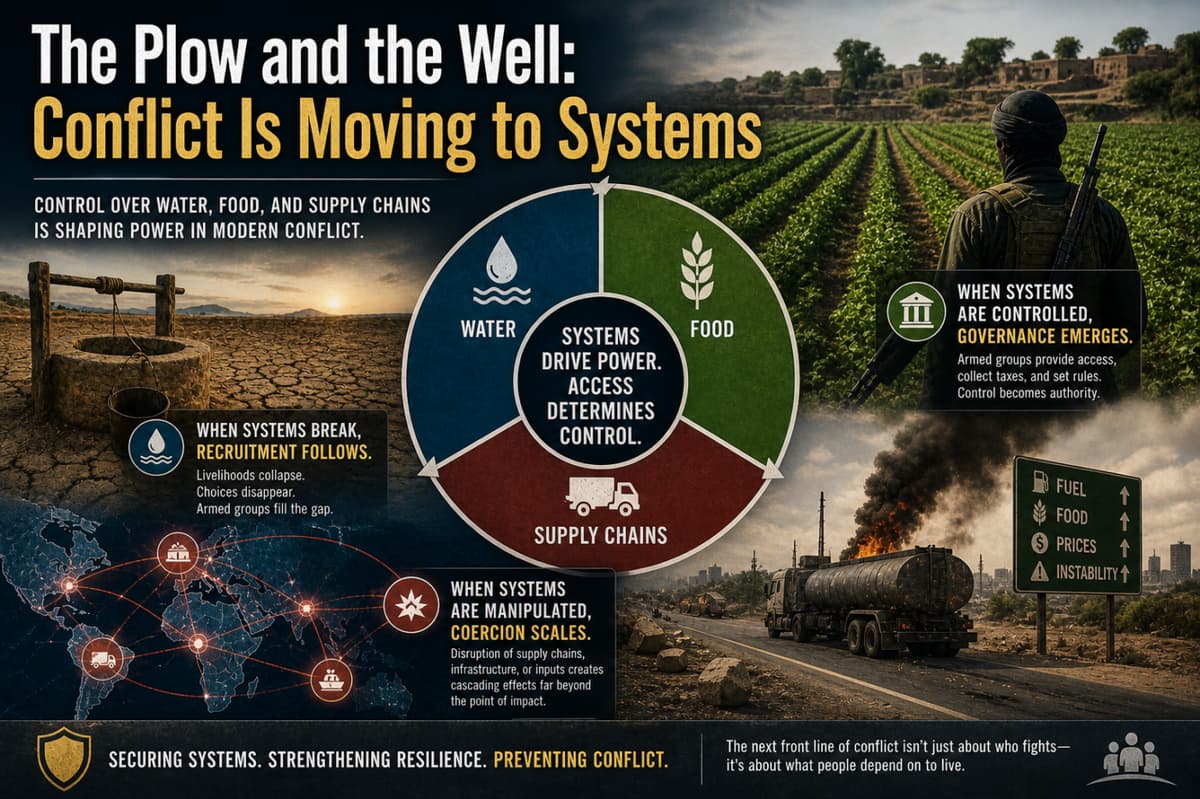
The Plow and the Well: Conflict Is Moving to Systems
The article argues that modern insurgencies derive power from controlling or disrupting essential systems—water, food, and supply chains—rather than solely from ideology or territorial gains. It cites the Lake Chad Basin’s shrinkage, ISIS’s agricultural dominance, and JNIM’s 2025 fuel blockade...

Irregular Warfare, Part One: Updating the Term and the Toolkit
The article by Jocelyn Garcia and Dr. James Giordano calls for redefining irregular warfare based on state stewardship rather than traditional asymmetry. It argues that a stewardship‑centric doctrine clarifies authority, entitlement, and responsibility, enabling the Joint Force to better classify...

The Two-Year Window: Russia’s Readiness Clock and Europe’s Strike Gap
Estonian Defense Forces commander Andrus Merilo predicts Russia will regain full combat readiness by 2027 after retooling its economy for war and consolidating battlefield experience in Ukraine. Analysts note that while Russia’s offensive capacity remains tied to the Ukrainian front,...
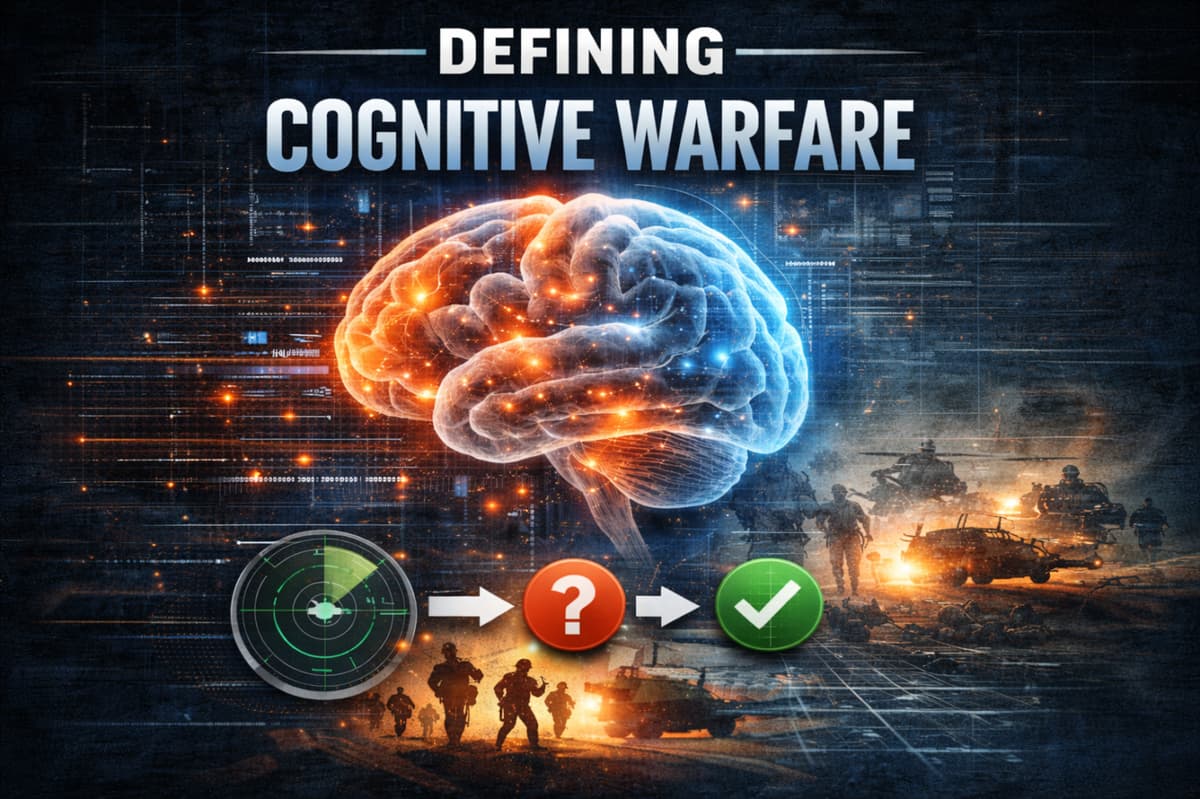
Defining Cognitive Warfare: A NDAA Mandate Response
The 2026 National Defense Authorization Act (NDAA) requires the Department of War to produce a precise definition of cognitive warfare and its relationship to narrative intelligence. Responding to this mandate, the article proposes a decision‑centric definition that frames cognitive warfare...

Why Xi’s Search for Loyalty Is Strangling the PLA’s Effectiveness
Xi Jinping’s latest anti‑corruption campaign has removed more than 100 senior PLA officers, effectively halving the service’s top leadership. The reforms re‑impose the Chairman Responsibility System, routing strategic, operational and even tactical decisions directly through Xi. While intended to tighten...

Cognitive Warfare and the Changing Character of Engagement: A Neurostrategic Perspective
Dr. James Giordano’s Strategic Insights piece frames cognitive warfare as the systematic use of neuroscience to shape perception, judgment, and emotion. By targeting the brain’s neural processes rather than merely the content of ideas, adversaries can degrade reasoning, morale, and...

Taipei Is ‘Fiddling While Rome Burns’
Retired U.S. Admiral Mark Montgomery warned Taiwan’s defense reforms are lagging during a tabletop exercise on Chinese pressure. He outlined three operational steps: enlist 200,000 citizens for regular reserve training, compel companies to support those cycles, and reassign two active...

Iranian Kurds as a Strategic Lever in a Changing Republic | Irregular Warfare Center
The Irregular Warfare Center’s perspective argues that Iranian Kurds are an underused strategic lever for Western policy toward Tehran. Decades of security‑first governance have left Kurdish provinces politically excluded, fueling cycles of unrest that escalated during the 2022‑2023 “Woman, Life,...

SOF Weekly Update – May 4, 2026
The SOF Weekly Update for May 4, 2026 highlights a series of geopolitical and defense developments. Iran has submitted a new phased nuclear‑deal proposal, while President Trump is reportedly considering pulling U.S. troops out of Germany. The acting U.S. ambassador to Ukraine...

Analysis: ISKP’s Exploitation of the Af-Pak Border War
The Islamic State‑Khorasan Province (ISKP) has shifted from a peripheral threat to an active combatant in Pakistan’s Balochistan, openly declaring war on the Baloch Liberation Army (BLA) after a May 2025 propaganda video. Pakistan’s defense minister announced an "open war" with...

The AI Battlespace: Artificial Intelligence, Civil Stability, and the Weaponization of Trust
Artificial intelligence is increasingly embedded in military, cyber and civilian systems, offering speed and analytical power but also creating new vulnerabilities. The article explains how adversaries can weaponize AI by poisoning data, manipulating trusted outputs, and automating cyber attacks, citing...

5/1/26 National Security and Korean News and Commentary
The Small Wars Journal roundup highlights a surge of strategic developments across U.S., Chinese, Iranian, and Korean security arenas. The Pentagon has secured new AI contracts for classified work while China pushes stablecoins and lithium dominance to reshape financial warfare....

South Africa’s Crime War and the Global Challenge of Criminal Insurgency
South Africa has launched Operation Prosper, deploying the South African National Defence Force (SANDF) alongside police to confront a surge in murders and organized crime. Officials cite 26,000‑30,000 annual homicides, framing the military’s role as a temporary stabilizer that provides...
Ghaleb Krame on Cartels, Drones, and Mexico’s Response
Ghaleb Krame, former Lebanese war child and Mexican security advisor, warned that Mexican drug cartels are operating as decentralized irregular warfare forces. He highlighted their rapid adoption of drones, now moving toward AI‑enabled targeting, aided by expertise flowing from the...

The Structural Biases That Undermine US Irregular Warfare | Modern War Institute
Andrew Rolander argues that the U.S. defense establishment’s failure in irregular warfare stems from three entrenched structural biases—measurability, temporal mismatch, and conventional primacy—rather than doctrine or funding. These biases push the Pentagon to chase countable metrics, short‑term cycles, and high‑intensity...

The Limits of China’s NCO Corps and Future Warfare
China’s People’s Liberation Army has dramatically upgraded its noncommissioned officer (NCO) corps, expanding technical training and professional pathways to support sophisticated weapons systems. Yet decision‑making authority remains tightly held by officers and embedded party structures, preserving a centralized command culture....

How China’s Fear of Secondary Sanctions Pushed Moscow Into Leveraging Stablecoins to Reshape Financial Warfare
Russia’s central bank plans to launch a digital ruble in September 2026, but private stablecoins have already become the primary tool for evading Western sanctions. The A7A5 stablecoin, launched in January 2025 and pegged to the ruble, has processed over...

The Hidden Subsidy of the Citizen Soldier
The article argues that the U.S. National Guard and Reserve—often called citizen soldiers—are the hidden subsidy financing today’s wars, shouldering a disproportionate share of deployments, combat casualties and community costs. Data show they comprised roughly 45% of the deployed force...

Arizona State University Wins Federal Contract to Offer War and Strategy Degree to Government Leaders
Arizona State University secured a Department of Defense contract to launch a master’s degree in war and strategy, beginning this fall in Washington, D.C. The program will admit up to 24 students annually, all nominated by the DoD, and targets...

Time to Damn the Iron River
Washington’s anti‑cartel strategy focuses on designations and strike authority, but the real leverage point is the steady flow of U.S.-sourced firearms into Mexico. Data consistently trace large volumes of recovered rifles and .50‑caliber weapons to American origin points, fueling cartel...

Monthly Drone Report – April 30, 2026
The April 30 2026 Monthly Drone Report notes a rapid surge in low‑cost unmanned aerial systems that is compressing operational depth and expanding contested rear areas. It highlights how traditional assumptions about medical evacuation, rear‑area security, and force protection are eroding in...

The Grievance Economy
Jack Dorsey’s Block announced a 40% workforce cut, blaming AI, echoing similar moves at IBM, UPS and Klarna. President Trump ordered a federal ban on Anthropic after the AI firm resisted Pentagon requests for surveillance‑type use. The article argues that...