This New Malware Calls Gemini AI Mid-Attack to Decide What to Do Next
A newly discovered malware family now contacts Google’s Gemini AI mid‑infection to decide its next actions. By feeding contextual data to the large language model, the code receives real‑time instructions on payload selection, lateral movement, and data exfiltration. The technique leverages the publicly accessible Gemini API, allowing attackers to offload decision logic to an external AI service. Security researchers say this marks a shift from static code to adaptive, AI‑driven threat behavior.
Unseen Devices in Your Network
The video highlights how organizations routinely overlook a significant portion of devices on their networks, exposing a blind spot in cybersecurity defenses. Speakers reveal that roughly 10‑12% of assets are completely unknown, and among the known inventory, about 12% lack endpoint...

🔴 Feb 23's Top Cyber News NOW! - Ep 1074
Episode 1074 delivers a concise roundup of the most pressing cyber‑security headlines for February 23, targeting analysts, CISOs, and business leaders. It spotlights ThreatLocker’s Zero Trust platform as a ransomware‑prevention solution and promotes free educational resources such as Flare.io Academy and Antisyphon...

Black Hat USA 2025 | Breaking Out of The AI Cage: Pwning AI Providers with NVIDIA Vulnerabilities
Researchers from Wiz uncovered a critical vulnerability in the NVIDIA Container Toolkit, the software that isolates AI workloads on NVIDIA hardware. The flaw permits a container escape to the host OS, potentially compromising entire Kubernetes clusters and exposing cross‑tenant data....

Black Hat USA 2025 | Autonomous Timeline Analysis and Threat Hunting: An AI Agent for Timesketch
At Black Hat USA 2025, Google engineers unveiled an AI‑powered agent that autonomously performs digital forensic timeline analysis and threat hunting within Timesketch. The system ingests heterogeneous log streams, reconstructs attack chains, and surfaces compromise evidence without relying on pre‑written...
AI Is Only as Good as Your Data
The video stresses that AI’s value in asset intelligence is directly tied to the quality of the data feeding it. While AI hype dominates headlines, the speaker reminds viewers that without clean, current data, even the most sophisticated models will...

Payment Spayce and Sagicor Bank: Innovating Fintech for the Caribbean Market
Payment Spayce and Sagicor Bank highlighted how wallet‑to‑wallet transfers abstract ACH, SWIFT and card networks, delivering instant, auditable payments. They emphasized that compliance—KYC, KYB, OFAC, PEP screening—is embedded directly into the transaction flow, turning regulation into an accelerator rather than...

MechaCon: PS2s Unbreakable Gatekeeper ...Until It Wasn't
The video explains how the MechaCon processor, hidden inside every PlayStation 2, served as the console’s ultimate gatekeeper—verifying disc legitimacy, memory‑card authenticity, and executable signatures. Two hardware generations existed: the early SPC970 chip with a fixed mask‑ROM firmware, and the later...

What’s Next for Chinese Cyber Strategy? In Conversation with Adam Segal
Adam Segal and Ciaran Martin discussed China’s evolving cyber strategy amid great‑power competition. They examined how sanctions, economic strain, and the AI arms race could reshape Beijing’s digital tactics over the next three to five years. The conversation highlighted internal...
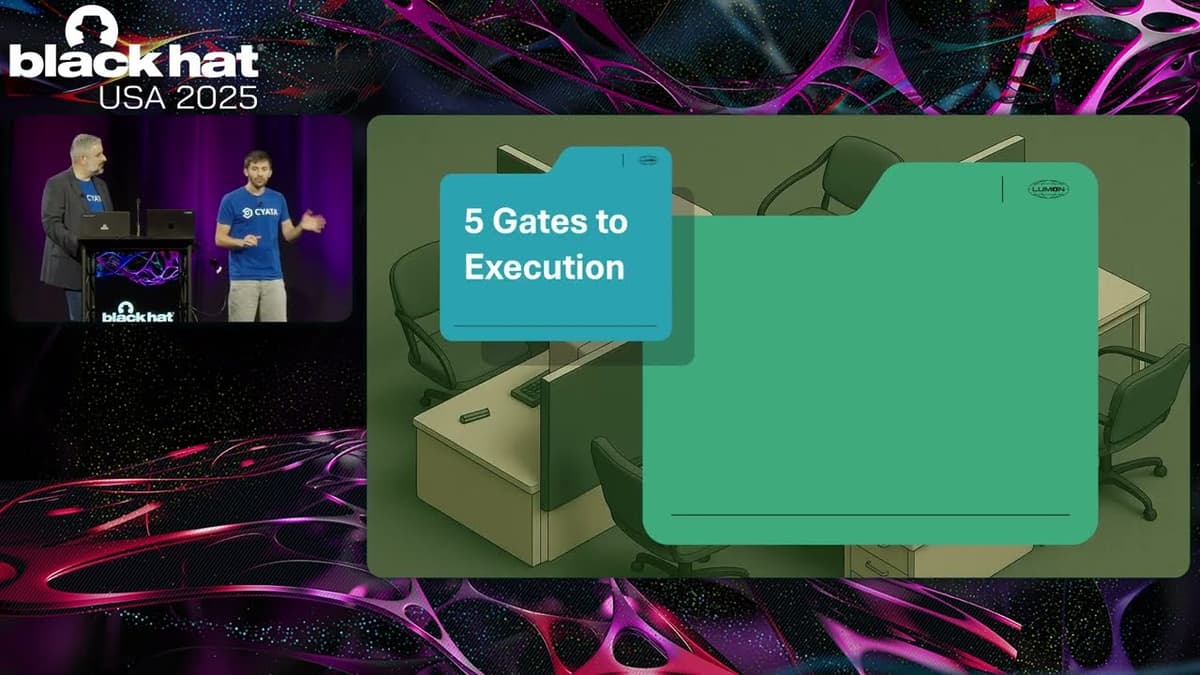
Black Hat USA 2025 | Vaulted Severance: Your Secrets Are Now Outies
The Black Hat USA 2025 talk, titled “Vaulted Severance: Your Secrets Are Now Outies,” examined critical weaknesses in modern secret‑management systems, using HashiCorp Vault as a case study. The presenters, from SIATA, framed the discussion around how vaults serve as...

100+ Trackers Are Watching You Right Now (Here's How to Stop Them)
The video explains that modern web pages fire hundreds of hidden tracking requests, turning a simple visit into a data‑harvesting operation. It outlines three defensive layers: browser extensions that expose and block trackers (Ghostery, uBlock Origin, AdGuard); privacy‑first browsers that enforce...
BBC Reporter Hacked via AI Vibe Coding Platform - Do You Trust These Platforms?
The video spotlights a recent incident in which a BBC reporter’s laptop was compromised after he downloaded the desktop version of Orchards, an AI‑driven “vibe” coding platform that lets users generate applications by describing them in natural language. According to the...

HackTheBox - GiveBack
The video walks through the Hack The Box “GiveBack” challenge, showing how a seemingly ordinary WordPress site can be leveraged to gain full control of a Kubernetes‑hosted environment. The presenter first discovers that the site runs an outdated Give plugin (v3.14.0)...
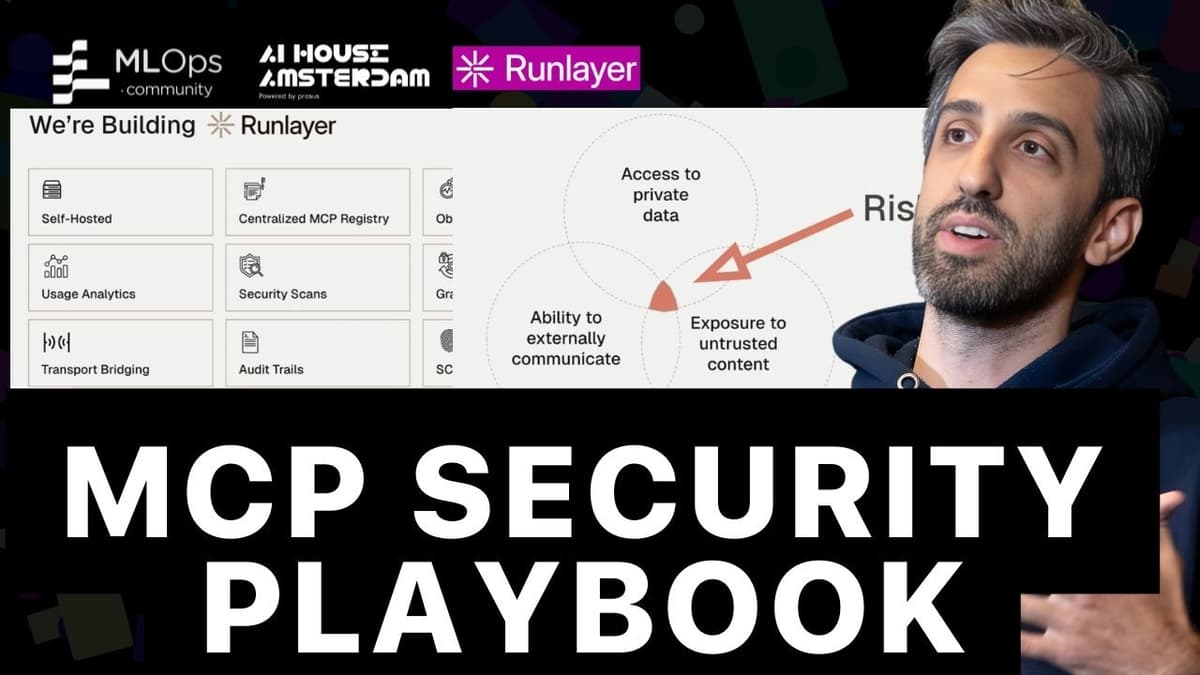
MCP Security: The Exploit Playbook (And How to Stop Them)
The video spotlights the rapid rise of the MCP (Model‑Centered Programming) standard since its November 2024 launch and the stark security lag that now threatens its expanding ecosystem. While major platforms are racing to support MCP, developers are left scrambling to...
Should You Scan that QR Code?
QR codes have become a ubiquitous bridge between physical media and digital content, appearing on restaurant menus, retail signage, television screens, newspapers and magazines. The video asks a simple but critical question: should consumers scan these codes without hesitation? The presenter...
Operation Winter SHIELD: FBI Philadelphia Safeguards the Energy Sector
Operation Winter Shield, the FBI’s weekly cyber‑security outreach, spotlighted the energy sector, emphasizing that power plants, grids and distribution networks are critical public‑safety infrastructure requiring heightened protection. The briefing outlined five practical defenses: segmenting critical networks to contain breaches; accelerating patch...
3 Reasons Your GRC Program Is Failing You in 2026
The video warns that traditional GRC programs are falling short in 2026, highlighting three critical failure points: third‑party risk, browser‑based attacks, and the rapid rise of AI. First, the explosion of SaaS services has multiplied third‑party exposure, exemplified by the Snowflake...
Black Hat USA 2025 | Exploiting DNS for Stealthy User Tracking
The Black Hat USA 2025 presentation by Bitdefender researchers Yangabella and Yan Pedrian revealed how DNS traffic from smartphones can be weaponized to create persistent, cross‑network device fingerprints. By acting as a curious DNS resolver, they collected 985 million DNS events...
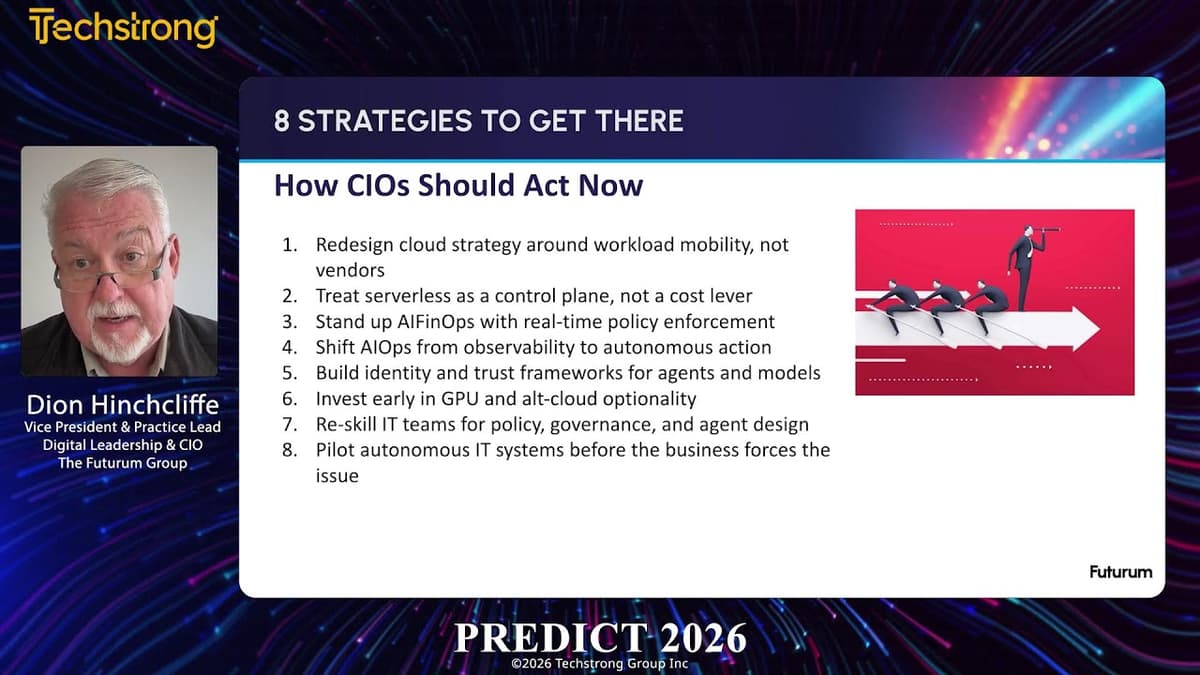
Techstrong TV - February 20, 2026
TechStrongTV’s February 20 episode spotlights Kevin Green, co‑founder and chief marketing officer of Hapix, a startup building AI‑driven solutions for community banks and credit unions. Green explains that beyond product features, controlling the narrative around AI adoption is critical in a...

AI Reshapes Public Safety, Privacy, and the Government Workforce #GovTech #AI #Cybersecurity #Shorts
The GovTech weekly roundup spotlights how artificial intelligence is reshaping public‑sector operations, from correctional facilities to state workplaces. Officials see AI as a tool to offload routine prison tasks, allowing staff to focus on safety and rehabilitation, while a Massachusetts...

Black Hat USA 2025 | From Prompts to Pwns: Exploiting and Securing AI Agents
The Black Hat USA 2025 session titled “From Prompts to Pwns” examined how modern AI agents—especially those powered by large language models—can be both powerful assistants and vulnerable attack surfaces. Speakers Becca and Rich from NVIDIA’s AI Red Team introduced a three‑tier...
1.2M Exposed: WHY Port 23 Is a Nightmare
The video highlights that more than 1.2 million internet‑connected devices still run Telnet on port 23, a legacy protocol widely considered insecure. Using the Showdan scanning platform, the creator demonstrates how easily these exposed services can be discovered, underscoring a gap between...

🔴 Feb 20's Top Cyber News NOW! - Ep 1073
The February 20 2026 episode of Simply Cyber’s Daily Cyber Threat Brief opened with host Dr. Gerald Oer reminding listeners that CISA has issued an urgent three‑day patch mandate for Dell’s RecoverPoint backup solution. The vulnerability, tracked as a hard‑coded credential CVE, has...

Quantum Vs. Bitcoin: Is a Crypto Security Collapse Coming? | Scott Stornetta Weighs In
The video features cryptography veteran Scott Stornetta discussing whether quantum computing threatens Bitcoin and other blockchain systems. He explains that blockchain security rests on mathematical problems that are easy to compute in one direction but infeasible to reverse, creating a...

Techstrong TV - February 19, 2026
Datadog’s CISO Emilio Escobar urged security teams to adopt AI proactively, linking observability with threat detection ahead of RSA. Bill Mulligan highlighted eBPF’s rise as enterprises embed observability, networking, and security directly into the Linux kernel for lower latency and...

Your Mac Is Under Attack From 3 Directions Right Now
The Techlore Surveillance Report warns macOS users that they are currently facing three distinct attack campaigns, ranging from state‑backed AI‑driven phishing to supply‑chain malware and malicious advertising. While the episode also touches on Discord’s age‑verification rollout and other tech news,...

The Payload Podcast #002 with Connor McGarr
The Payload Podcast #002 opens with a light‑hearted banter about office décor and wearable gadgets before settling into its core purpose: a conversation with Connor McGarr, who recently rejoined CrowdStrike on a sensor‑engineering innovation team. The hosts use the informal...

Hidden Risk of Expired Support Contracts
The video highlights a hidden security risk: devices operating on expired or nonexistent support contracts cannot receive the latest firmware updates, leaving them vulnerable to exploitation. This issue is especially acute for organizations that purchase second‑hand networking equipment, which often...

How AI Weapons Are Trained on Your Private Data
The video warns that the next generation of warfare will be powered not by nuclear arsenals but by autonomous weapons trained on the digital footprints of billions. It argues that private data harvested from social media, browsing habits and photos...

🔴 Feb 25's Top Cyber News NOW! - Ep 1076
Episode 1076 of the "Top Cyber News NOW!" series provides a concise roundup of the day’s most relevant cybersecurity developments for professionals. The episode spotlights ThreatLocker’s Zero Trust platform as a ransomware mitigation tool and promotes educational resources such as...

🔴 Feb 24's Top Cyber News NOW! - Ep 1075
The Simply Cyber Daily Threat Brief episode 1075, recorded on February 24, 2026, opened with the host’s usual community banter before diving into the day’s headline: a ransomware attack by the Everest group that compromised nearly 140,000 records at V‑Core...

Password Managers Are Swiss Cheese - Threat Wire
The latest Threatwire episode delivers a packed cyber‑security briefing, spotlighting three headline stories: a critical flaw in Windows 11’s revamped Notepad, Discord’s upcoming facial‑age verification system, and a new academic analysis exposing weaknesses in leading password managers. Microsoft’s Notepad now parses...
Why Half of All Kubernetes Clusters Are About to Become Vulnerable | Kat Cosgrove & Tabitha Sable
The Kubernetes Steering Committee announced that the Ingress NGINX controller – a core ingress solution for roughly half of cloud‑native deployments – will be officially retired at the end of March, six weeks from the announcement. After that date the...

This FREE Tool Can Help You Backup and Restore Anything at Enterprise Level.
Plakar is an open‑source backup solution aimed at DevOps engineers who need enterprise‑level data resilience. The video explains how traditional object storage like S3 lacks point‑in‑time recovery and built‑in encryption, leaving critical workloads exposed to accidental deletion, ransomware, or corruption. Plakar...

Transparency in Security Controls
Vanta uses a public trust center that displays real-time security control status with green check marks tied directly to internal continuous monitoring. Simple configuration checks—such as whether encryption is enabled—are automatically run and reflected on the external site so prospects...

Bad Bot Problem - Computerphile
The video explains how social media ‘botnets’—operator-controlled networks of fake accounts—are increasingly using large language and image models to mimic human behavior, generate original posts, images and tailored comments, and coordinate narratives. Using a local demo platform, the presenter shows...
Techstrong TV - February 18, 2026
TechStrong TV featured Mike Manos, chief technology officer of Dun & Bradstreet, discussing how the 186‑year‑old firm is reinventing itself through cloud migration and artificial‑intelligence initiatives. Manos outlined a five‑year transformation that moved D&B from legacy data centers to a...

PANW Platformization Strategy: Long-Term Tailwind Amid Short-Term Headaches
After reporting a double‑beat earnings quarter, Palo Alto Networks saw its stock slide about 7.5%, prompting analysts to dissect the firm’s long‑term platformization strategy. The company highlighted a $210 billion cybersecurity addressable market and emphasized its move toward a unified, AI‑driven...
DEF CON 33 - DisguiseDelimit: Exploiting Synology NAS with Delimiters and Novel Tricks - Ryan Emmon
Ryan Emmens presented at DEF CON 33 a case study on discovering and weaponising an unauthenticated vulnerability in Synology’s DiskStation Manager (DSM) operating system, culminating in a $40,000 Pwn2Own win. By instrumenting the login flow with eBPF tracing and inotify, he...
DEF CON 33 - Browser Extension Clickjacking: One Click and Your Credit Card Is Stolen - Marek Tóth
The DEF CON presentation by Marek Tóth exposed a new class of browser‑extension clickjacking that lets attackers harvest credit‑card and password data with a handful of user clicks. By targeting the manual‑autofill feature of popular password‑manager extensions, the researcher demonstrated...
China and Latin America, Explained: A Conversation with Brian Fonseca
The video features Dr. Brian Fonseca discussing how China’s expanding economic, technological, and security footprint in Latin America and the Caribbean is reshaping U.S. hemispheric strategy. He frames the issue within the latest U.S. National Security Strategy, which labels Beijing...

Ahead of the Threat Podcast: Season 2, Episode 1 — John Hultquist
Season two of the FBI’s Ahead of the Threat podcast opens with Assistant Director Brett Leatherman framing the agency’s dual mission: impose costs on hostile actors while safeguarding privacy and constitutional rights. The episode spotlights the Cybersecurity Information Sharing Act...

Cloud Password Vault Weakness
A team of security researchers at ETH Zurich examined the resilience of popular cloud‑based password managers by modeling an extreme threat: a server that is entirely malicious. Using this worst‑case assumption, they evaluated Bitwarden, LastPass and Dashlane. The tests showed a...

They’ve Scamming with AI Clones of YOUR Voice
The video warns that AI‑generated voice clones are being weaponised in the United Kingdom to bypass bank authentication and steal money from vulnerable consumers. Criminal groups first conduct seemingly innocuous lifestyle surveys, harvesting health, financial and personal details. Using that data...
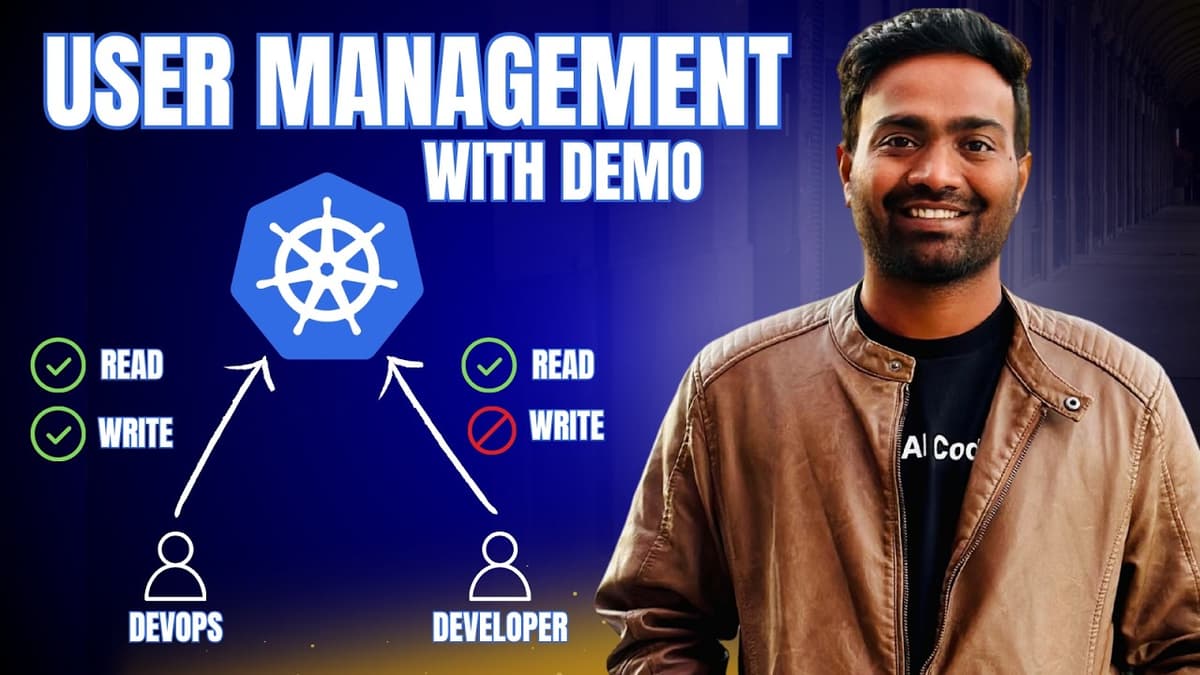
Realtime Kubernetes User Management with Demo | Must Watch
The video tackles the persistent pain points of Kubernetes user management, highlighting how authentication (kubeconfig) and authorization (RBAC) become unwieldy at scale. It explains that distributed kubeconfig files expose cluster IPs, certificates, and tokens, while the native RBAC model forces...

ContinuumCon Is Back for 2026!
ContinuumCon returns for 2026 as a virtual, publicly streamed cybersecurity conference running June 12–14, hosted by Level Effect and Just Hacking Training. The event offers permanent on-demand access to every session, hands-on workshops, interactive labs, and a blue-team-focused capture-the-flag competition....

Remote Work Is Here to Stay I CIO Talk Network
The CIO Talk Network episode spotlights the permanence of remote work and the need for scalable, reliable, and secure operations. Host Sanjal interviews Sisha Mandawa, CIO of Greenpath Financial Wellness, a nonprofit that has navigated the shift to a distributed workforce...
DNS Click Fix Threat
The video discusses a newly reported threat – the first known DNS ClickFix attack – in which cyber‑criminals use a seemingly innocuous nslookup command to deliver malicious payloads. Microsoft’s security team identified the technique, marking a shift from traditional email‑based...
Blue Team | Intelligence-Driven Defense for the Real World
The video outlines an intelligence‑driven approach to blue‑team operations, arguing that modern cyber‑threat intelligence (CTI) must evolve from static reports into an operational pipeline that turns external threat feeds and internal telemetry into concrete defensive actions. The speaker, who credits...

Red Team | Weaponizing LLM Fine-Tuning for Stealthy C2
Researchers from Palo Alto Networks' Cortex team demonstrated how attackers can weaponize fine-tuning of large language models to build stealthy command-and-control channels that live inside popular AI models. They show attackers already using LLMs for reconnaissance, social engineering and coding,...