
Black Hat USA 2025 | Breaking Out of The AI Cage: Pwning AI Providers with NVIDIA Vulnerabilities
Researchers from Wiz uncovered a critical vulnerability in the NVIDIA Container Toolkit, the software that isolates AI workloads on NVIDIA hardware. The flaw permits a container escape to the host OS, potentially compromising entire Kubernetes clusters and exposing cross‑tenant data. Tests on leading AI platforms, including Replicate and DigitalOcean, confirmed the exploit works across major providers. The discovery underscores a systemic risk for AI services that rely on NVIDIA’s container stack.

Software Earnings Vs. AI Disruption
The segment’s focus is the widening gap between robust software earnings and mounting fears that generative‑AI agents could render traditional enterprise applications obsolete. A viral investment‑newsletter essay titled "The 2028 Global Intelligence Crisis" sparked the conversation, prompting analysts to compare...

Find and Replace Users in HubSpot #shorts
HubSpot has introduced a Find and Replace Users tool that scans the entire CRM for references to a departing employee and swaps them with a new owner in just a few clicks. Previously, admins had to manually edit workflows, meeting...

Executive Interview: How Costa Rica Could Solve Healthcare IT's Staffing Crisis with Scott Gildea
Optimum Healthcare IT announced a major expansion of its managed‑services operation into Costa Rica, positioning the Central American nation as a new hub to alleviate the chronic staffing shortage plaguing U.S. healthcare IT departments. The company cites Costa Rica’s growing pool...

Black Hat USA 2025 | Autonomous Timeline Analysis and Threat Hunting: An AI Agent for Timesketch
At Black Hat USA 2025, Google engineers unveiled an AI‑powered agent that autonomously performs digital forensic timeline analysis and threat hunting within Timesketch. The system ingests heterogeneous log streams, reconstructs attack chains, and surfaces compromise evidence without relying on pre‑written...
How to Make Money With OpenClaw (Real Business Use Cases)
The video demonstrates how a customized OpenClaw AI instance can generate real revenue by automating outreach, resurrecting stalled deals, and surfacing better contacts from CRM and sales call data. The creator shows it drafting personalized re-engagement emails, finding alternative decision-makers...
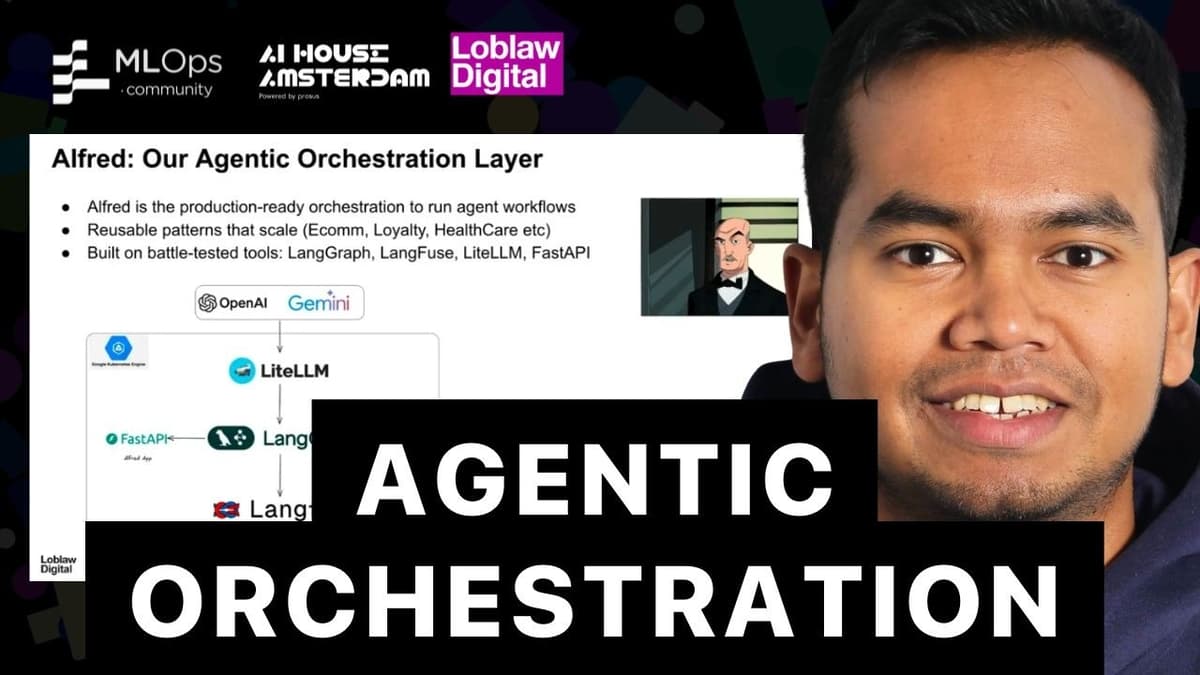
Building an Orchestration Layer for Agentic Commerce at Loblaws
The talk introduced Alfred, Loblaws’ production‑grade orchestration layer designed to power agentic commerce across its massive retail ecosystem. Built on Google Kubernetes Engine with a FastAPI gateway, Alfred abstracts LLM providers, leverages LangChain‑style execution graphs, and connects to over fifty...
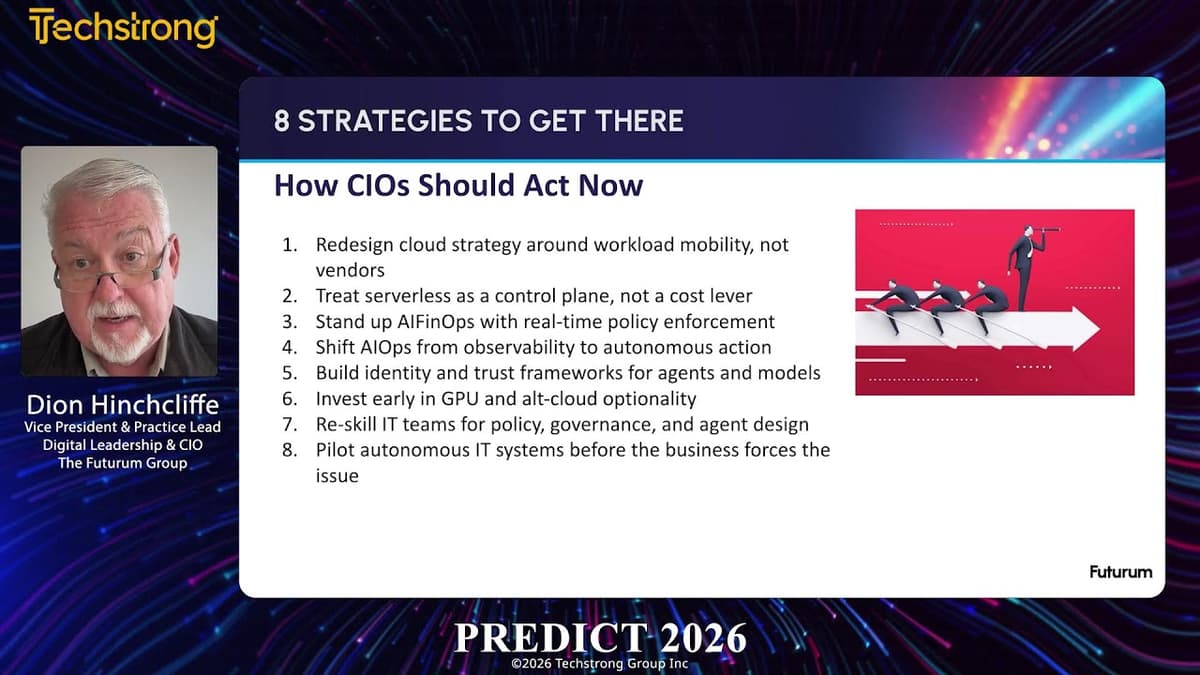
Techstrong TV - February 23, 2026
RSAC’s Innovation Sandbox Contest showcased over $18.1 billion in follow‑on funding, more than 100 acquisitions, and AI‑centric finalists, backed by a $5 million Crosspoint grant and expanded early‑stage programs. OpenTelemetry’s growing adoption is prompting the creation of unified observability warehouses that combine...

The Now Generation: Teaching Supply Chain with Simulations, Stories, and Systems
Supply Chain Now’s ‘Now Generation’ episode spotlights Texas Christian University’s approach to preparing students for rapid entry into supply‑chain roles, featuring TCU adjunct Ryan Goodwin—senior director of supply chain technology at Trinity Industries and co‑founder of the Texas Tabletop Society—and...

Avoid Vendor Lock in & Project Failure
The video warns that vendor lock‑in is a leading cause of digital‑transformation project failure, especially in large ERP rollouts. It stresses the need for modular, API‑first architectures and early negotiation of exit clauses. By applying rigorous vendor due diligence and...

S/4HANA Journey and Fortune-Telling Your Business Success #shorts
The video offers practical closing advice for firms embarking on, or already deep into, an SAP S/4HANA transformation. The speaker emphasizes that the initiative must be business‑led, with clear ownership from the line side rather than being relegated solely to...
Black Hat USA 2025 | Vaulted Severance: Your Secrets Are Now Outies
The Black Hat USA 2025 talk, titled “Vaulted Severance: Your Secrets Are Now Outies,” examined critical weaknesses in modern secret‑management systems, using HashiCorp Vault as a case study. The presenters, from SIATA, framed the discussion around how vaults serve as...

IT Operations Are Not Ready for AI Agents: How to Respond Today
The Gartner ThinkCast preview warns that IT operations are ill‑prepared for the surge of AI agents and that CIOs are pressing for AI‑driven cost reductions. Speakers Autumn Stanish and Paul Delori cite that 52% of CIO priorities for 2026 are cost‑cutting,...
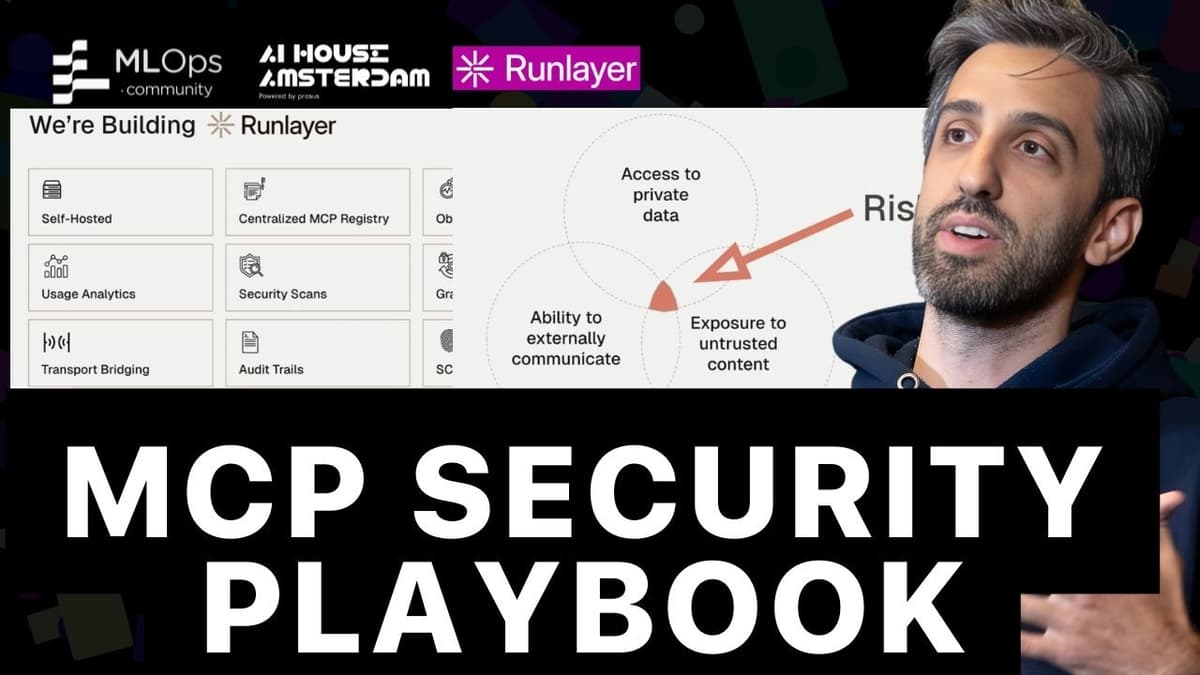
MCP Security: The Exploit Playbook (And How to Stop Them)
The video spotlights the rapid rise of the MCP (Model‑Centered Programming) standard since its November 2024 launch and the stark security lag that now threatens its expanding ecosystem. While major platforms are racing to support MCP, developers are left scrambling to...

The Future of Coding: AI Agents & the Next Tech Revolution // Ricky Doar
The conversation centers on Cursor, an AI‑driven coding assistant, and how developers are adapting to a new paradigm where large language models act as pair programmers or autonomous agents. Ricky Doar and his guest discuss the rapid adoption of Cursor...

This Isn't Event Sourcing
The video clarifies that not every state change qualifies as an event; creating a shipment is merely CRUD, while actions like order dispatched, shipment loaded, arrived, or delivered are true events. It argues that event sourcing can become over‑engineering if...

Turning Every Service Call Into Opportunity: Human + AI Performance at Scale
The video outlines Intel’s initiative to transform inbound service calls into revenue‑generating interactions by layering artificial intelligence onto traditional call‑center operations. By teaming with McKinsey and Google, Intel built a platform that automatically transcribes, categorizes, and analyzes calls, delivering real‑time insights...
Black Hat USA 2025 | Exploiting DNS for Stealthy User Tracking
The Black Hat USA 2025 presentation by Bitdefender researchers Yangabella and Yan Pedrian revealed how DNS traffic from smartphones can be weaponized to create persistent, cross‑network device fingerprints. By acting as a curious DNS resolver, they collected 985 million DNS events...
Techstrong TV - February 20, 2026
TechStrongTV’s February 20 episode spotlights Kevin Green, co‑founder and chief marketing officer of Hapix, a startup building AI‑driven solutions for community banks and credit unions. Green explains that beyond product features, controlling the narrative around AI adoption is critical in a...

Avoid Costly Mistakes & Vendor Traps
Third Stage Consulting released a video highlighting a suite of free resources designed to help enterprises avoid costly mistakes and vendor traps during digital transformation initiatives. The offering includes the 2026 Digital Transformation Report, 2025 reports on AI strategy and...
Why Real-Time Data and ERP Now Matter for Builder Decision-Making
Constellation HomeBuilder Systems executives Bob Swainhart and Chris Graham argue that real‑time data, integrated ERP platforms, and practical AI are no longer optional for homebuilders. They cite rising consumer hesitancy and rapidly shifting market conditions as catalysts for adopting these...

Black Hat USA 2025 | From Prompts to Pwns: Exploiting and Securing AI Agents
The Black Hat USA 2025 session titled “From Prompts to Pwns” examined how modern AI agents—especially those powered by large language models—can be both powerful assistants and vulnerable attack surfaces. Speakers Becca and Rich from NVIDIA’s AI Red Team introduced a three‑tier...

N8n Hostinger Setup 2026 - Step by Step
The video walks viewers through a step‑by‑step deployment of the n8n workflow automation platform on a Hostinger virtual private server, emphasizing a low‑cost, one‑click installation that becomes production‑ready by the end. Dan begins by urging users to sign up through an...

Can SAP HANA Hold Up To Scrutiny? I CIO Talk Network
The CIO Talk Network episode examines whether SAP HANA can withstand rigorous scrutiny, featuring SAP’s VP of product strategy Jeff W. and HP’s CTO Chris Ninwit. They frame HANA as a purpose‑built, in‑memory platform that unifies transactional (OLTP) and analytical...
Do AI Agents Need to Be Intelligent to Do Their Job? | Shimmy Says Ep. 47
The episode questions whether AI agents must be truly intelligent or simply effective at completing tasks. It highlights the ongoing debate over AI’s “understanding” versus its role as a practical workflow engine in enterprises. Real‑world use cases—document drafting, ticket routing,...
How Temenos Is Powering the Future of Global Money Movement
Temenos is positioning its Money Movement and Management platform as the backbone for the accelerating global payments ecosystem, promising banks, fintechs and non‑bank payment service providers a unified solution to handle everything from instant domestic transfers to complex cross‑border settlements. The...

🔴 Feb 25's Top Cyber News NOW! - Ep 1076
Episode 1076 of the "Top Cyber News NOW!" series provides a concise roundup of the day’s most relevant cybersecurity developments for professionals. The episode spotlights ThreatLocker’s Zero Trust platform as a ransomware mitigation tool and promotes educational resources such as...
Why Half of All Kubernetes Clusters Are About to Become Vulnerable | Kat Cosgrove & Tabitha Sable
The Kubernetes Steering Committee announced that the Ingress NGINX controller – a core ingress solution for roughly half of cloud‑native deployments – will be officially retired at the end of March, six weeks from the announcement. After that date the...

This FREE Tool Can Help You Backup and Restore Anything at Enterprise Level.
Plakar is an open‑source backup solution aimed at DevOps engineers who need enterprise‑level data resilience. The video explains how traditional object storage like S3 lacks point‑in‑time recovery and built‑in encryption, leaving critical workloads exposed to accidental deletion, ransomware, or corruption. Plakar...

Transparency in Security Controls
Vanta uses a public trust center that displays real-time security control status with green check marks tied directly to internal continuous monitoring. Simple configuration checks—such as whether encryption is enabled—are automatically run and reflected on the external site so prospects...

How Google Supports Fintech Builders
Google casts itself as an agnostic ecosystem enabler for fintechs, supplying cloud infrastructure and developer tools so firms can focus on product rather than core operations. Its Google Cloud Marketplace helps B2B fintechs onboard and gain access to tier‑1 through...
Read Replicas Are NOT CQRS (Stop Confusing This)
In the video, Derek Lamartin dismantles the blanket claim that the outbox pattern, CQRS, and event sourcing are inherently over‑engineered solutions. He argues that the real question is whether these patterns address a concrete business need, not whether they belong...
DEF CON 33 - DisguiseDelimit: Exploiting Synology NAS with Delimiters and Novel Tricks - Ryan Emmon
Ryan Emmens presented at DEF CON 33 a case study on discovering and weaponising an unauthenticated vulnerability in Synology’s DiskStation Manager (DSM) operating system, culminating in a $40,000 Pwn2Own win. By instrumenting the login flow with eBPF tracing and inotify, he...
RevOps Is the Glue of Scalable #marketing
The speaker argues that Revenue Operations (RevOps) is the central function that enables scalable, strategic marketing by ensuring data integrity, compliance, segmentation, and automated orchestration without sacrificing brand authenticity. At their company, a marketing manager doubles as the RevOps specialist,...
How to Build Reliable AI at Scale: Insights From Addy Osmani
Addy Osmani, working to bridge Google DeepMind research with product and developer teams, urges builders to move beyond one-off demos toward production-ready AI systems. He frames development on a spectrum from “wild west” solo experiments to enterprise-grade setups with quality...

Sponsored Session: Installing OpenTelemetry, Today and Tomorrow - Ted Young, Grafana
In a sponsored session at the conference, Grafana Labs’ Developer Programs Director Ted Young—also a co‑founder of the OpenTelemetry project—outlined the current state of installing OpenTelemetry and previewed the roadmap for simplifying the process. He emphasized that the guidance applies...

Techstrong TV - February 18, 2026
Mike Manos, CTO of Dun & Bradstreet, described a five-year modernization push to transform the 186-year-old data company into a cloud-first, AI-enabled enterprise. He said D&B now ingests and processes north of five exabytes of data nightly across more than...

Remote Work Is Here to Stay I CIO Talk Network
The CIO Talk Network episode spotlights the permanence of remote work and the need for scalable, reliable, and secure operations. Host Sanjal interviews Sisha Mandawa, CIO of Greenpath Financial Wellness, a nonprofit that has navigated the shift to a distributed workforce...
Domain-Driven Platform Engineering Is the Future | Weave Intelligence
The video explores how domain‑driven design (DDD) is reshaping platform engineering, arguing that future internal developer platforms must be built around business domains rather than generic infrastructure abstractions. AJ Chunkermath explains that traditional platform teams often deliver one‑size‑fits‑all services, which...

Mauricio Monroy - Equisoft - ITC LATAM 2023
Mauricio Monroy, senior executive at Equisoft, spoke at ITC LATAM 2023 in Miami, highlighting the Canadian firm’s end‑to‑end software solutions tailored for the insurance sector. Equisoft’s portfolio spans CRM, illustration and quoting engines, electronic applications, policy‑admin systems, customer portals and a...

The Hidden Cost of Cloud Upgrades
Speakers warned that cloud upgrade projects often promise “fit‑to‑standard” implementations but fail because vendors and integrators do not adequately engage frontline staff to redesign work, leading teams to re‑create legacy processes in new systems and negate expected benefits. Poor requirements...

𝗦𝗬𝗦𝗧𝗘𝗠𝗦 𝗜𝗡𝗧𝗘𝗚𝗥𝗔𝗧𝗢𝗥 𝗔𝗪𝗔𝗥𝗗 𝗦𝗛𝗢𝗪
The video features Eric Kimberling interviewing Bonnie Tinder of Raven Intelligence about the critical role of system integrators in digital transformations and Raven’s data-driven, peer-review platform for rating integrators. Tinder explains that while buyers obsess over consumer reviews for small...
Blue Team | Intelligence-Driven Defense for the Real World
The video outlines an intelligence‑driven approach to blue‑team operations, arguing that modern cyber‑threat intelligence (CTI) must evolve from static reports into an operational pipeline that turns external threat feeds and internal telemetry into concrete defensive actions. The speaker, who credits...

Red Team | Weaponizing LLM Fine-Tuning for Stealthy C2
Researchers from Palo Alto Networks' Cortex team demonstrated how attackers can weaponize fine-tuning of large language models to build stealthy command-and-control channels that live inside popular AI models. They show attackers already using LLMs for reconnaissance, social engineering and coding,...

Blue Team | From Exploit to Risk: Scaling Purple Team Insights
Anthony Switzer argues for “first-principle purple teaming,” a methodology that converts red-team and pentest findings into actionable business risk and mission impact. He stresses translating technical detections (e.g., Active Directory exploits, MITRE mappings) into language executives and auditors understand, and...

Blue Team | Hunting Cloud Persistence Without Malware
The talk explains how modern attackers achieve long-term cloud persistence without malware by abusing legitimate cloud-native features—OAuth app consent, stolen or replayed tokens, mismanaged service principal credentials, long-lived API keys, mailbox rules and automated connectors. These malicious activities blend into...

EU Bans AI over Cybersecurity and Privacy Fears on Parliament Devices
The European Parliament has ordered the disabling of built‑in artificial‑intelligence functions on corporate tablets and other work devices used by members and staff, citing unresolved privacy and cybersecurity risks. An internal email obtained by Politico explains that many AI features...

Podcast Ep261: Oracle’s Supply Chain Capabilities, Industry 4.0, Best Practices Do Not Exist
In Episode 261 of Transformation Ground Control, hosts Eric Kimberling and Darian Fiacusky discuss practical guidance for digital transformations, urging annual roadmap reviews and the need to pivot mid-implementation when business realities change. They advocate measured, pilot-based adoption of AI...
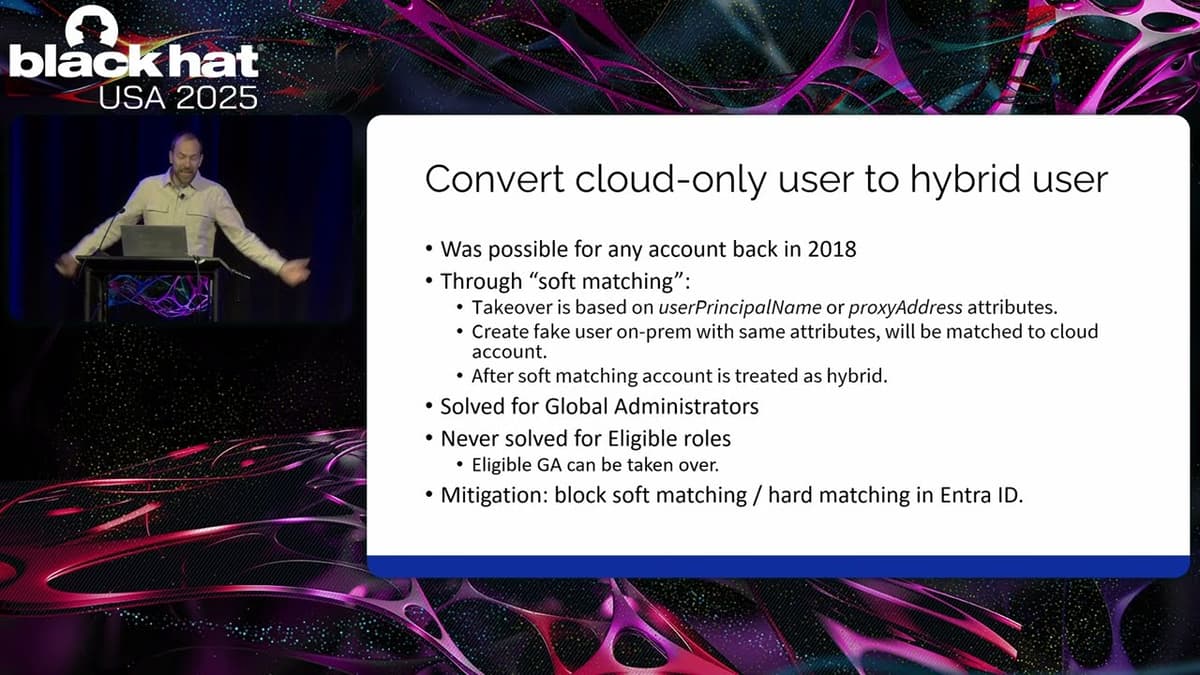
Black Hat USA 2025 | Advanced Active Directory to Entra ID Lateral Movement Techniques
The presentation at Black Hat USA 2025 detailed how attackers can move laterally from a fully compromised on‑premises Active Directory into Microsoft Entra ID in hybrid environments. Speaker Dian of Outsider Security explained that once domain‑admin rights are obtained on‑prem,...
How Fortune 100 Companies Adopt Knowledge Graphs in Practice | Emil Eifrem X Data Science Dojo
The discussion centers on how Fortune 100 enterprises are actually implementing knowledge graphs, contrasting idealized, organization‑wide visions with the pragmatic routes companies are taking today. Two adoption patterns emerge. Large firms often build an “enterprise knowledge graph” that mirrors portions of their...