
Black Hat USA 2025 | Lost & Found: The Hidden Risks of Account Recovery in a Passwordless Future
The Black Hat USA 2025 presentation warned that account‑recovery mechanisms—intended as a safety net for forgotten passwords—are rapidly becoming the most exploitable entry point in a passwordless ecosystem. Speakers Sidra, Gabby, and their research team outlined how recovery flows rely on out‑of‑band channels such as email and SMS, which are outside the direct control of service providers and vulnerable to SIM‑swap, SS7, and phishing attacks. Their empirical study examined 22 of the most‑visited web services, mapping each site’s “account states” and testing nine recovery scenarios ranging from unverified methods to multi‑factor interactions. The data showed that four‑fifths of users forget a password within 90 days and a quarter need recovery daily, underscoring the massive scale of the problem. Design flaws surfaced, including acceptance of unverified recovery contacts, inconsistent verification steps, and the ability to hijack accounts by exploiting misspelled or compromised recovery addresses. A striking example cited was a site that allowed password resets using an unverified email address, enabling an attacker who controlled a typo‑adjacent address to seize the victim’s account without any additional checks. The researchers also introduced an adversary model—Alice, Eve, Mallory, and Chad—to illustrate how attackers can remain stealthy, lock out users, or spam recovery requests. The talk concluded that without a fundamental redesign of recovery flows, even the strongest passwordless authentication (biometrics, passkeys) will be undermined. Their open‑source Auditing Recovery Architecture (ARA) framework provides a systematic way to evaluate and harden recovery processes, and the authors issued best‑practice recommendations for the industry to adopt more robust, verified recovery channels.

Cybersecurity Standards Scorecard (2025 Edition)
The webcast, hosted by veteran SANS instructor James Troll, introduces the 2025 edition of the Cybersecurity Standards Scorecard – an annual research effort that catalogues and evaluates the growing universe of cyber‑security frameworks. Troll notes that the SANS database now...

How RBC Capital Markets Is Transforming Client Onboarding
RBC Capital Markets is re‑engineering its client onboarding to position it as a competitive advantage rather than a mere compliance exercise. Lori Messer, global head of business and client services, emphasizes that a frictionless onboarding experience showcases the bank’s service...

Black Hat USA 2025 | Pwning User Phishing Training Through Scientific Lure Crafting
A new eight‑month field study of over 20,000 employees reveals that conventional phishing awareness training fails to meaningfully reduce click rates. The research, presented at Black Hat USA 2025, shows that the success of phishing lures is erratic, with some...

How Coinbase Scaled AI to 1,000+ Engineers | Chintan Turakhia
Coinbase engineering leader Chintan Turakhia says the company has successfully scaled AI across a 1,000+ engineer organization to boost velocity and rebuild a major consumer-facing app under an aggressive six- to nine-month timeline. Adoption succeeded after leadership became hands-on with...
The MCP Security Risks You Can't Afford to Ignore
MCPTotal CTO Ariel Shiftan warned that MCP (Model Connector Protocol) servers—tools that let LLMs access private APIs and data—pose serious enterprise security risks. His team has discovered zero-day vulnerabilities in widely used MCP servers and routinely finds malicious or highly...

How to Build a Voice of the Customer Playbook? | CIO Talk Network
The CIO Talk Network episode dives into how organizations can construct a Voice of the Customer (VoC) playbook that turns raw feedback into actionable insight. Host Sanjal interviews Dwayne Lion of Vivele Data Solutions, who clarifies that VoC focuses on...
Omphile Matheolane Speaking at DDD Europe
Omphile Matheolane’s presentation at DDD Europe centered on applying domain‑driven design to large‑scale financial applications. He argued that the first step is to delineate clear bounded contexts—such as accounts and loans—so each domain owns its data and logic without over‑reaching...
Lesson 217 - Supervisor Consumer Pattern
The video introduces the Supervisor Consumer pattern, a scalability technique that lets a single service handle fluctuating loads by automatically spawning and retiring consumer threads. Mark Richards explains that a dedicated supervisor component continuously polls an event queue, assesses the...

SAP's AI Leap With NVIDIA Partnership & Future Predictions #shorts
SAP announced a strategic partnership with NVIDIA to speed up its artificial‑intelligence initiatives. The collaboration gives SAP access to NVIDIA's GPU and software stack while hinting at a longer‑term goal of developing proprietary AI technology. Executives compare this move to...
Why Is a WAF No Longer Enough?
Enterprises are discovering that traditional Web Application Firewalls (WAFs) no longer provide sufficient protection against today’s complex threat landscape. The video explains that a WAF, originally designed to filter malicious HTTP traffic, is an outdated term as application security now...
Black Hat USA 2025 | If Google Uses It to Find Webpages, We Can Use It to Find Fraudsters
The session at Black Hat USA 2025 introduced a surprisingly simple technique—term‑frequency inverse‑document‑frequency (TF‑IDF)—as a powerful tool for spotting fraudsters, positioning it as an alternative to the sophisticated AI browsers and agents that dominate today’s web search. Speakers argued that generative...

Enterprise-Ready MCP // Jiquan Ngiam
The Coding Agents Conference on March 3 will feature Jiquan Ngiam discussing the rapid enterprise adoption of agents and Model Context Protocols (MCPs). Over 80 % of professional developers now use AI tools daily, and agentic coding platforms such as Claude Code...

Techstrong TV - February 27, 2026
Techstrong TV featured Nikquille Hondigal, co‑founder and Chief AI Officer of Forward Networks, to discuss the company’s evolution from a software‑defined networking (SDN) startup to an AI‑enabled network operations provider. Founded twelve years ago by Stanford PhDs, Forward Networks has...

Anthropic Vs. The Pentagon + AI Agents Are Rewriting Software | TSG Ep. 1029
The episode centers on a high‑stakes standoff between Anthropic and the U.S. Department of Defense over a $200 million contract to supply the Claude model. The Pentagon seeks fewer guardrails, while Anthropic insists on a strict human‑in‑the‑loop policy for any weaponized...

Identify, Scope, and Build an Agentic Workflow in N8n with Max Tkacz
The video walks viewers through building an AI‑driven, agentic workflow in n8n, starting with a live demo that automates a repetitive competitor‑monitoring task. Max Tkacz emphasizes a disciplined triage process—evaluating potential automations on time saved, feasibility, risk of damage, and...
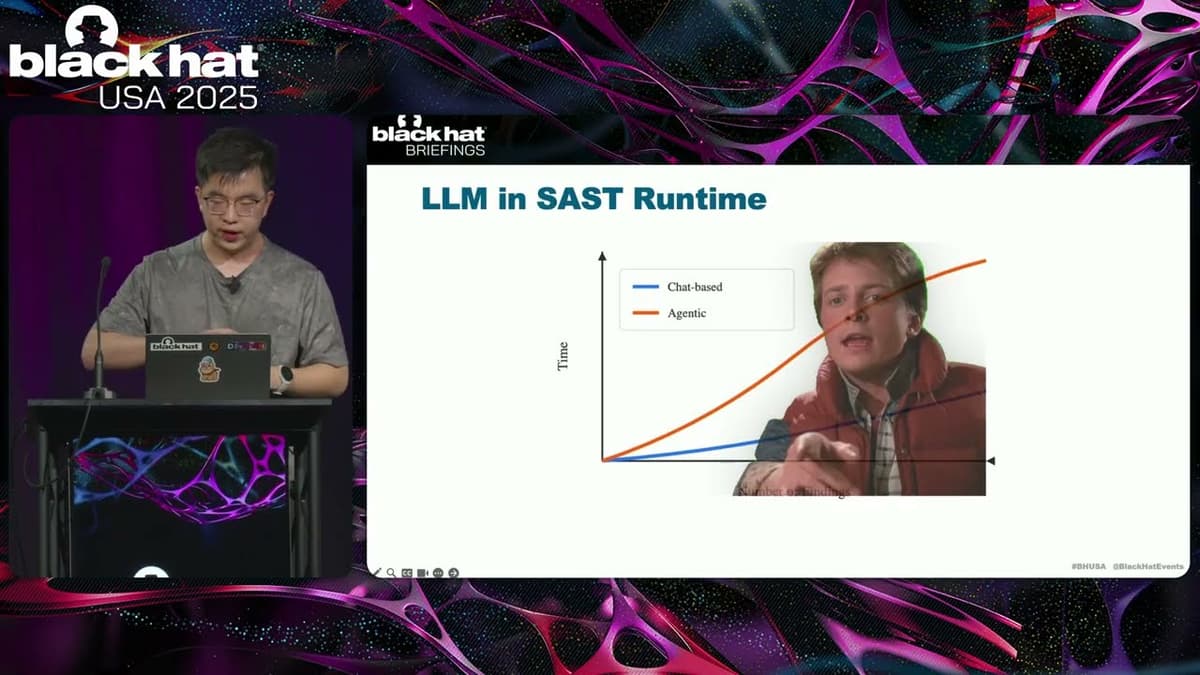
Black Hat USA 2025 | Let LLM Learn: When Your Static Analyzer Actually 'Gets It'
The Black Hat presentation explored how large language models (LLMs) can be fused with traditional static analysis tools to create a new generation of vulnerability scanners. The speaker outlined three integration patterns—AI‑enhanced, where a static scanner filters LLM output; AI‑explorer,...

Modernizing Systems, Streamlining Processes & Delivering Services
Acting CIO Debbie Stephens of the U.S. Patent and Trademark Office joined Scoop News Group’s Billy Mitchell at a GDIT Emerge session to discuss modernizing legacy systems. She emphasized moving beyond mere technology deployment to achieve genuine adoption, highlighting artificial...

How Finastra Is Redefining the Operating Model in Trade Finance
The video outlines how Finastra is reshaping the operating model for trade finance amid sweeping regulatory reforms that now recognize electronic documents as legally equivalent to paper. Banks across Europe, the United States, the Middle East and Southeast Asia...

Government eDiscovery Needs and Challenges I CIO Talk Network
The CIO Talk Network interview spotlights the growing complexity of eDiscovery within the U.S. Department of Justice’s Civil Division. Host Sanjok speaks with Allison Stanton, the newly created Director of eDiscovery, to explore how the federal government tackles both affirmative...

AI Success Is About Learning Not Output | Platform Engineering Meetup Highlight
The Platform Engineering meetup highlighted a shift in AI strategy: success hinges on continuous learning rather than sheer output volume. Speakers warned that the industry’s rush to “move at AI speed” must be tempered by robust safety and security practices,...
Expert Witness Reveals Lessons
The live discussion centered on the anatomy of ERP failures, with Eric Kimberling of Third Stage Consulting introducing Fred Hler, director of the firm’s expert‑witness practice. The conversation highlighted that ERP implementations fail at alarming rates—often quoted above 80%—and that...

Komed Health: Hospital Coordination Made Easy Like WhatsApp | MedTech World Middle East 2026
Komed Health, a Swiss startup led by CEO Louisa Dober, has built an orchestration “coordination execution” layer that links hospitals’ EMRs and clinical systems to a WhatsApp-like mobile interface for clinicians. Deployed in 29 hospitals across Switzerland and Germany with...

Founder Shares His RevOps #AI Stack
Founder Peter Fuller of The Workflow Academy disclosed the AI stack powering his RevOps practice, promising a 20‑30% efficiency lift. The toolkit combines Cerebro Analytics for dashboards, Lovable for app development, Moon Knox as a ChatGPT wrapper, and Anthropic’s Claude...

Disconnects Cost More than Discounts.
Future Finance hosts Paul Barnhurst and Glenn Hopper discuss with Riya Grover, CEO of Sequence, how unifying Configure‑Price‑Quote (CPQ) and billing eliminates revenue leakage between CRM and ERP systems. The episode highlights that contract details often get lost when sales...

Consulting Vs. Software: Who Wins the IT Budget War? #shorts
The IT spending landscape is rapidly shifting, with organizations allocating more budget to software solutions than to traditional consulting services. Automation and artificial intelligence are accelerating this transition, enabling enterprises to implement scalable tools without extensive human advisory. As AI-driven...

How He Built a €1.1B Giant - Interview with Enrico Giacomelli, the Founder of Namirial
The EU Startups podcast features Enrico Giacomelli, founder of Italy’s digital‑trust specialist Namirial, which has grown into a €1.1 billion enterprise. Giacomelli walks through the company’s 30‑year journey from a modest paper‑selling venture in 1991 to a market‑leading platform for electronic...

The 229 Podcast: AI Governance Webinar with Dr. James McCabe, Dr. Ben Hohmuth, and Kristen Myers
The 229 Podcast episode convened senior clinicians from Jefferson Health, Geisinger and Northwell Health to map an enterprise‑wide AI governance playbook. Panelists described how their CEOs have elevated artificial intelligence to a strategic imperative, linking it to cost reduction,...
Black Hat USA 2025 | Conjuring Hardware Failures to Breach CPU Privilege Boundaries
The Black Hat talk spotlights machine‑check exceptions (MCEs) – hardware‑level fault signals that fire when a CPU detects catastrophic errors such as cache corruption, thermal trips, or external interference. Christopher Domas demonstrates that, unlike ordinary interrupts, MCEs cannot be masked,...

Patch THIS Vulnerability in 10 Seconds
A critical Chrome zero‑day vulnerability is being actively exploited in the wild, and Google has released an emergency patch. The flaw, a use‑after‑free bug in Chrome’s rendering engine, allows attackers to execute arbitrary code simply by getting a user to...

How Encompass Is Transforming Corporate KYC and Digital Identity
The video features an interview with Alex, a senior executive at Encompass, recorded at day four of CybOS Frankfurt 2025. He outlines how the Australian‑born fintech is reshaping corporate know‑your‑customer (KYC) processes and digital identity solutions for institutional clients. Encompass began...
Gemara: GRC Engineering Model for Automated Risk Assessment | OpenSSF Project Spotlight
Jamara, the GRC Engineering Model for Automated Risk Assessment, is an OpenSSF‑hosted open‑source project that defines a multi‑layer logical model for integrating governance, risk, and compliance (GRC) directly into software engineering pipelines. Its purpose is to replace fragmented, tool‑specific data...

590 - From Patient Flow to Operational Efficiency: Optimising Workflows at the Enterprise Level
Talking Health Tech’s latest episode spotlights Roland’s enterprise‑level Concentric Care platform, designed to streamline patient flow and boost operational efficiency across hospitals. Executive Director Steve Gomes explains how a 25‑person engineering team in Victoria has built a middleware layer that...

Why Smartstream Is Doubling Down on AI and Customer Success
SmartStream CEO Ak Jaffa announced a strategic push to double down on artificial intelligence and customer‑success initiatives, positioning the firm’s brand to reflect a blend of AI and human intelligence delivering measurable value. The company will continue heavy R&D spending, rebranding...

Best Practices Badge for Free/Libre and Open Source Software | OpenSSF Project Spotlight
David Wheeler, director of open‑source supply‑chain security at the OpenSSF, introduced the OpenSSF Best Practices Badge – a three‑tier (passing, silver, gold) certification that evaluates open‑source projects against a curated set of security‑focused criteria drawn from well‑run repositories. The badge...

Turning Threat Intelligence Into Real-World Action | 2 Cyber Chicks S8 E1
In the latest 2 Cyber Chicks episode, Karla Reffold, Chief Insights Officer at Surefire Cyber, explains how threat intelligence can move from static data to actionable insight during high‑pressure incidents. She emphasizes the need for concise, context‑rich intel that aligns...

EDiscovery Best Practices and Trends I CIO Talk Network
The CIO Talk Network episode reframes eDiscovery as a strategic data‑governance and risk‑management function rather than a purely reactive legal task. Vivian Tero of IDC and host Sanjog Aul discuss enterprise confidence gaps, the surge of AI‑driven automation, and the...

The #1 Executive Blind Spot
Executives routinely underestimate how consuming enterprise resource planning (ERP) implementations are, treating them like routine IT upgrades instead of operational overhauls that demand sustained senior and key-user engagement. Consultants say clients must participate deeply—defining requirements, testing, making rapid decisions and...
Black Hat USA 2025 | Enhancing Command Line Classification with Benign Anomalous Data
Sophos researchers presented a novel pipeline that pairs anomaly detection with large language models to harvest benign command‑line examples for supervised classification. Instead of relying on unsupervised anomaly detection to flag malicious inputs, the approach uses the detector to surface...

Podcast Ep262: Microsoft’s Bundling Regulatory Issues, Best SI's In the Market, SAP RISE
Episode 262 of the Transformation Ground Control podcast dives into three core topics: Microsoft’s ongoing bundling regulatory challenges, a discussion on the top system integrators in the market, and an overview of SAP’s RISE offering. Host Eric Kimberling and guest...
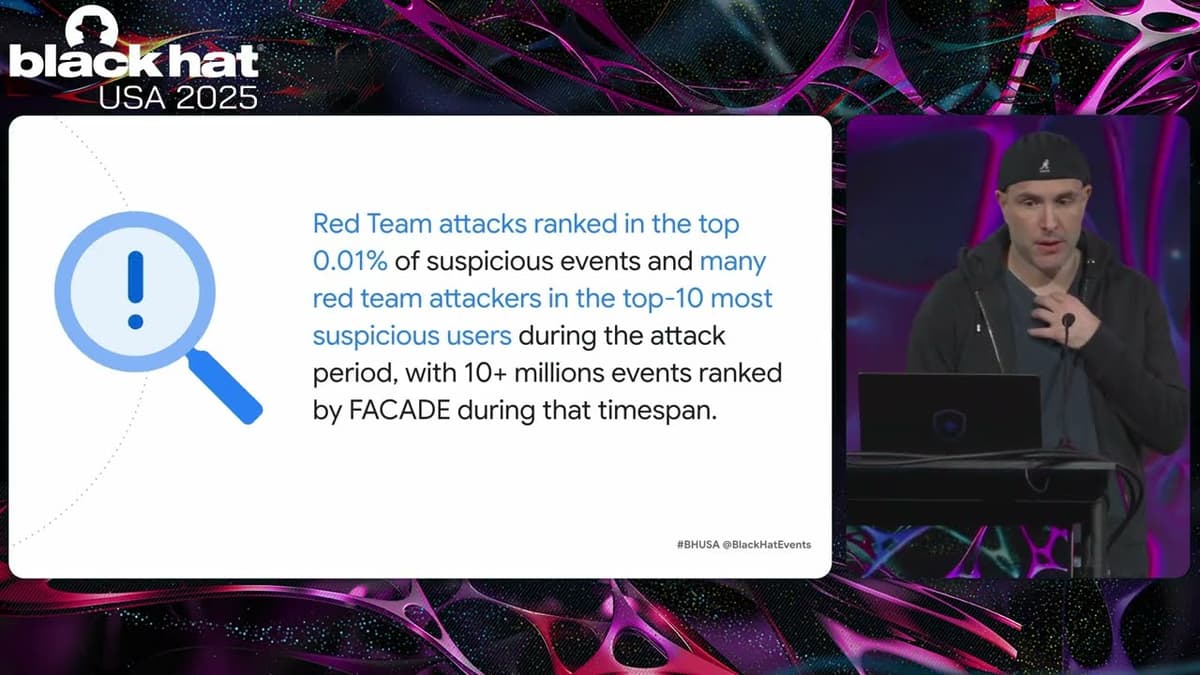
Black Hat USA 2025 | FACADE: High-Precision Insider Threat Detection Using Contrastive Learning
Google unveiled Facade, a self‑supervised AI system that detects insider threats by analyzing contextual patterns in corporate logs. Leveraging contrastive learning on exclusively benign data, Facade achieves unprecedented accuracy, reporting false‑positive rates below 0.01% and as low as 0.0003% for...

The AI Divide Global Politics Agent Identity and Kubernetes | TSG Ep. 1026
The Techstrong Gang dissected a new AI innovation pledge signed by 88 nations that emphasizes market expansion while omitting enforceable safety standards. The hosts debated how this signals a fragmented global governance landscape and reshapes competitive dynamics among superpowers. They...

AI Agent Sandboxes: Securing Memory, GPUs, and Model Access
AI agents expand the attack surface beyond traditional microservices by accessing models, memory, GPUs, and external tools, making conventional container isolation inadequate. Industry leaders discussed how lightweight VM‑based sandboxes, such as those built on Kata, can provide stronger isolation, limit...

Techstrong TV - February 24, 2026
Techstrong TV’s February 24 2026 episode spotlighted the rapid convergence of AI and enterprise infrastructure. RUCKUS President Bart Giordano explained how AI‑driven applications and edge workloads are forcing a rewrite of wireless performance, reliability, and security. Microsoft’s Tiffany Treacy and Keith Kirkpatrick...
Cybersecurity Careers: Penetration Tester (4 of 9 Careers)
The video introduces penetration testing as the offensive counterpart to defensive security roles, highlighting its focus on discovering and exploiting weaknesses across hardware, software, networks, policies, and people. Kean Evans explains that entry‑level testers start with automated scans, then progress to...

How Red Hat Is Using Open Source to Power the Future of Banking
Red Hat is positioning open‑source technologies as the backbone of modern banking infrastructure, offering secure, compliant platforms for cloud‑native transformation. The company showcases its enterprise‑grade Red Hat Enterprise Linux and OpenShift solutions, which bridge community innovation with strict financial regulations....

Episode 2: From CIO Initiative to C-Suite Priority: Governing AI for Enterprise Impact
Leaders from Skyward, Nationwide and veteran CIOs warned that while AI's potential is real, most pilots stall without C‑suite and board alignment, clear governance and a scalable operating model. Skyward’s CEO described moving from experimental proofs to enterprise deployment by...
AI Chips, Software Profit & Atlassian's Growth HACK! #shorts
The short‑form video stitches together a rapid‑fire commentary on the current state of SaaS growth, AI‑chip economics and Atlassian’s latest earnings, highlighting how profit and revenue stacks are being reshuffled amid the AI boom. Atlassian reported a 23 % year‑over‑year revenue increase...

Could IBM's Software-and-AI Pivot Re-Rate Its Stock?
IBM has repositioned itself as a software‑led, platform business centered on hybrid cloud, artificial intelligence and quantum computing. Over the past three years the pivot delivered roughly 1,000 basis points of operating‑margin expansion and about $5 billion of incremental free cash...
Unseen Devices in Your Network
The video highlights how organizations routinely overlook a significant portion of devices on their networks, exposing a blind spot in cybersecurity defenses. Speakers reveal that roughly 10‑12% of assets are completely unknown, and among the known inventory, about 12% lack endpoint...