ARTESCA+ Veeam Gets Easier, Smarter, and Highly Available
The video showcases the Artresca+ Veeam unified software appliance, highlighting the upcoming 4.3 release that expands the solution from a single‑node box to a three‑node, highly available cluster. The presenter and Scality engineer Thomas walk through the new features, emphasizing how the appliance bundles Veeam backup software directly alongside storage for a single‑pane‑of‑glass experience. Key updates include a reshaped dashboard that surfaces backup job status, capacity trends, and alerts; native support for Veeam 13, both Windows and Linux flavors, with the Linux version enabling true high‑availability. Scalability jumps dramatically—from 400 TB on a single node to an initial 2.5 PB and a roadmap toward 10 PB across the multi‑node cluster. Automation is deepened with one‑click repository creation, automatic immutability settings, and hidden credential handling, reducing manual steps and error risk. Thomas notes, “We’re adding a lot of improvements around our Artis scale plus Veeam unified software appliance,” and demonstrates how the UI now links directly to the Veeam web console. He also points out that the appliance can host backups for Veeam’s broader portfolio—Office 365, Kasten containers—allowing heterogeneous environments to converge on a single platform. For IT leaders, the upgrade means faster deployments, lower operational overhead, and a path to enterprise‑grade backup without juggling separate storage and software stacks. The high‑availability cluster and expanded capacity also future‑proof organizations as data volumes surge and workloads migrate to containers.
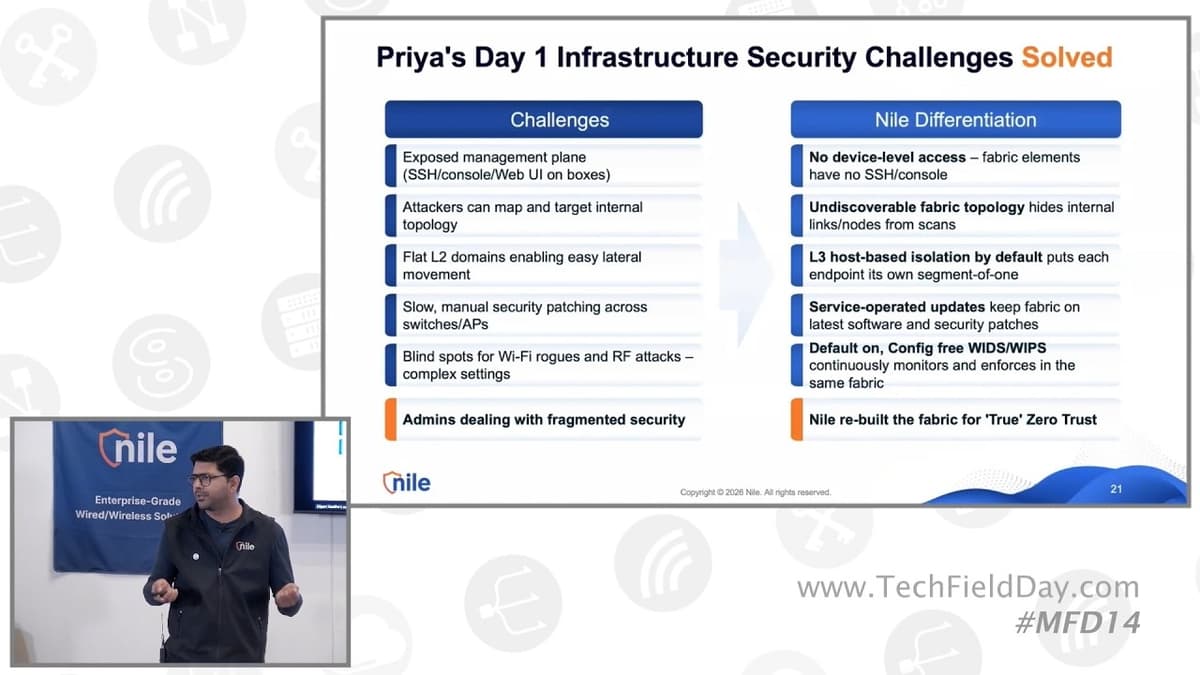
Nile Built-In Zero Trust Not Bolted-On
The presentation showcases Nile’s built‑in zero‑trust architecture, stressing that every security function—from infrastructure hardening to access control—resides inside a single, cloud‑driven portal, eliminating the need for disparate tools. Nile structures security into three layers—infra, access, policy—and differentiates itself with a...
Building AI Agents Is Easy—Transforming Enterprise Workflows Is the Hard Part
In this Techstrong.AI interview, Core.ai CEO Raj Conru argues that while constructing AI agents has become relatively straightforward, the real challenge lies in embedding them within existing enterprise workflows. He frames the conversation around three primary ROI‑driven use‑cases—customer‑experience automation, employee‑experience...
Inventory Management 101: What Every Growing Brand Needs To Know with Cin7 | Startup CPG Webinar
The Startup CPG webinar introduced inventory management fundamentals for fast‑growing consumer brands, with Cin7 demonstrating how a unified platform can replace ad‑hoc spreadsheets. Kenny outlined why inventory is essentially cash, emphasizing that excess stock ties up capital and inflates 3PL...

ThreatLocker Enforces Zero Trust With Strict Application Control (Sponsored)
The Packet Protector podcast, sponsored by ThreatLocker, spotlights the company’s zero‑trust platform that moves security from a “trust‑but‑verify” model to a “deny‑by‑default, permit‑by‑exception” approach. Rob Allen explains that ThreatLocker combines traditional allow‑listing with “ring‑fencing,” which not only decides which binaries may...

Navy’s Ashley Elizabeth Evans Talks Future-Ready Automation
In a UiPath Fusion public‑sector interview, Deputy Director Ashley Elizabeth Evans outlined the Navy’s roadmap for scaling automation from isolated pilots to enterprise‑wide, mission‑driven solutions. The service has run a six‑year robotic process automation (RPA) program, deploying more than 500 bots...

Supply Chain LIVE - US Summit 2026 | Yaniv Butel on AI Agents Solving Logistics Spend Leakage
At the Supply Chain LIVE US Summit 2026, Yaniv Butel, CRO of Pixify’s Fixify platform, outlined how agentic AI can curb logistics spend leakage for manufacturers that outsource freight to numerous carriers. Butel explained that procurement teams are hampered by fragmented...

Big 4 Consultant Reveals: SAP Recommendation Was Set From Day 1! #shorts
In a short interview, a former Big‑Four consultant recounts his first software‑evaluation engagement for a Fortune 500 client, revealing that the firm entered the project with SAP already chosen as the answer. The consulting team billed the client roughly $1 million to $1.5 million...

The Part of Email Security Nobody Is Talking About (Until It's Too Late)
The video spotlights a fundamental shift in email security, arguing that legacy secure email gateways (SEGs) are no longer sufficient against sophisticated business‑email‑compromise (BEC) and insider threats. While SEGs sit at the perimeter and rely on signatures, they only see...
Datasite CEO: How AI Agents Are Rewiring M&A — 55,000 Deals, 3.5B Pages, One Operating System
Datasite CEO Rusty Wiley explains how the company has transformed from a paper‑based data‑room provider into an AI‑native, end‑to‑end M&A operating system. Over the past 12 years, the firm migrated legacy customers, was acquired by CapVest, and added several strategic...
Ensuring a Successful Epic Go-Live with Real-Time Training Dashboards & Personalization
Care New England’s recent Epic go‑live was anchored in a three‑phase strategy—pre‑go‑live personalization, live‑day support, and post‑go‑live optimization. The organization set an ambitious target: 90% of providers personalized before launch, leveraging expert‑led labs and workflow‑based training to make the experience...

Quests, Token Leaderboards, and a Skills Marketplace: The Elite AI Adoption Playbook | John Kim
John Kim, CEO of Sunbird, outlines an "AI adoption playbook" that turns internal ideas into production‑ready tools through AI‑driven quests, a token consumption leaderboard, and a skills marketplace. The approach treats AI as a product, empowering marketers, salespeople, and...
Exciting Future for Businesses & Teams
The conversation centers on the evolving role of enterprise‑resource‑planning (ERP) systems amid rapid AI adoption and the strategic plans of the ERP Perspective community to broaden its educational reach. Speakers argue that AI will serve as an efficiency tool rather than...

Podcast Ep271: 'Best Practice' Is Not Best for You, Global SAP Lessons, More Technology Isn't Better
The episode of Transformation Ground Control tackles the grim reality that ERP initiatives routinely flop, citing an 80% failure rate and emphasizing that only a tiny fraction of value—about 3%—comes from the software itself. Host Eric Kimberling and guest Karm...

Prep for Sales Meetings Faster with Codex
The video showcases Codex, an AI‑driven assistant, streamlining sales‑meeting preparation by orchestrating data from Google Calendar, Salesforce, Google Drive, Slack, and Gmail in a single conversational thread. Codex first reads the calendar entry, extracts attendees and agenda, then queries Salesforce for...
HousingStack On-Demand: The Empower Loan Origination System (LOS) by Dark Matter
The HousingStack On‑Demand demo showcased Dark Matter Technologies’ Empower loan‑origination system, a cloud‑native platform that embeds artificial‑intelligence and a developer‑friendly API layer to automate the end‑to‑end mortgage workflow. Key features highlighted include persona‑driven borrower and loan‑officer interfaces, real‑time orchestration of credit...
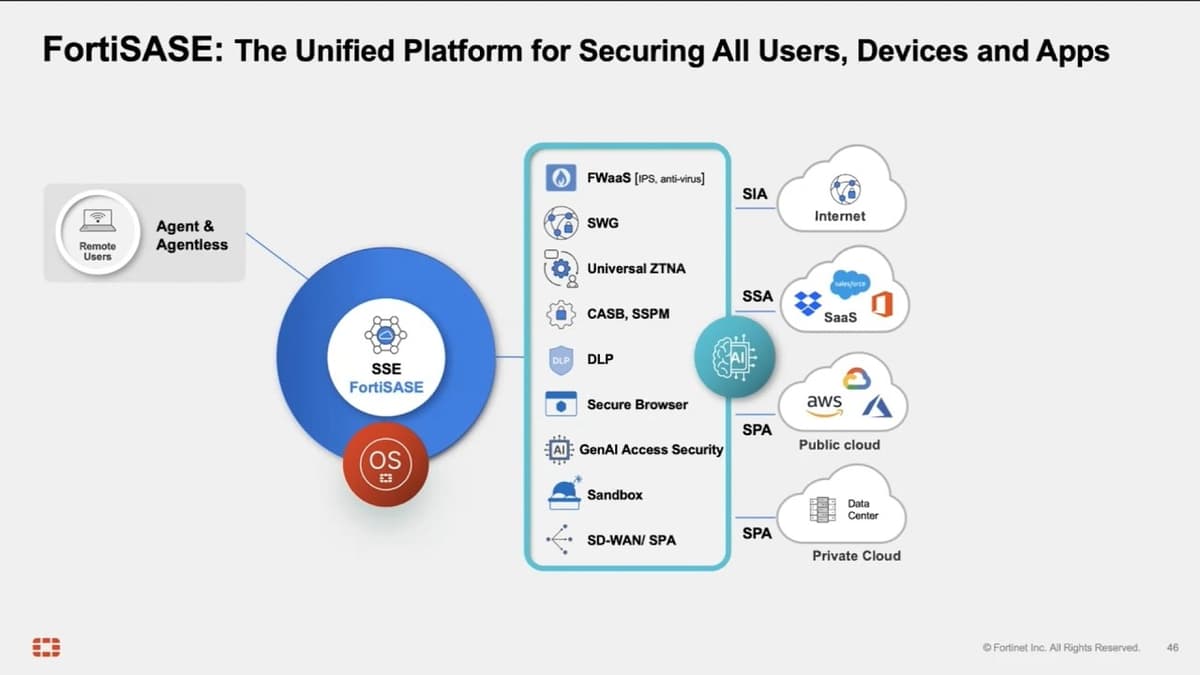
Secure Every Device, Everywhere with FortiSASE
FortiSASE’s latest briefing highlighted the rollout of a Secure Browser plug‑in designed to protect BYOD environments while extending the broader 4D SASE platform. Director Ramnat Chennai walked through the architecture, noting more than 200 globally distributed POPs, each running on...

Fortinet Unified Endpoint Security
Fortinet’s Hari Krishnan introduced the 4D Endpoint platform, a unified solution that merges traditional endpoint protection, EDR, VPN/ZTNA, and emerging data‑loss‑prevention capabilities into a single agent and console. The presentation emphasized the growing demand from enterprises to replace fragmented security...

Cloud-Enabled Security Strategy | Larry Biagini, GE
In this CIO Talk Radio interview, GE’s chief technology and security officer Larry Biagini explains how enterprises can turn cloud adoption into a security advantage. He argues that the old “inside‑versus‑outside” mindset no longer applies; instead, organizations must prioritize risk,...
Autonomous Software Development at Enterprise Scale: Inside a 1,000-Developer Pilot (with Blitzy)
GNP, Mexico’s largest insurer, ran a four‑month pilot of Blitzy, an autonomous software‑development platform, involving roughly a thousand developers to test whether AI could replace traditional coding. The pilot covered four scenarios – migrating a legacy Java 8 backend to Java 21, upgrading...
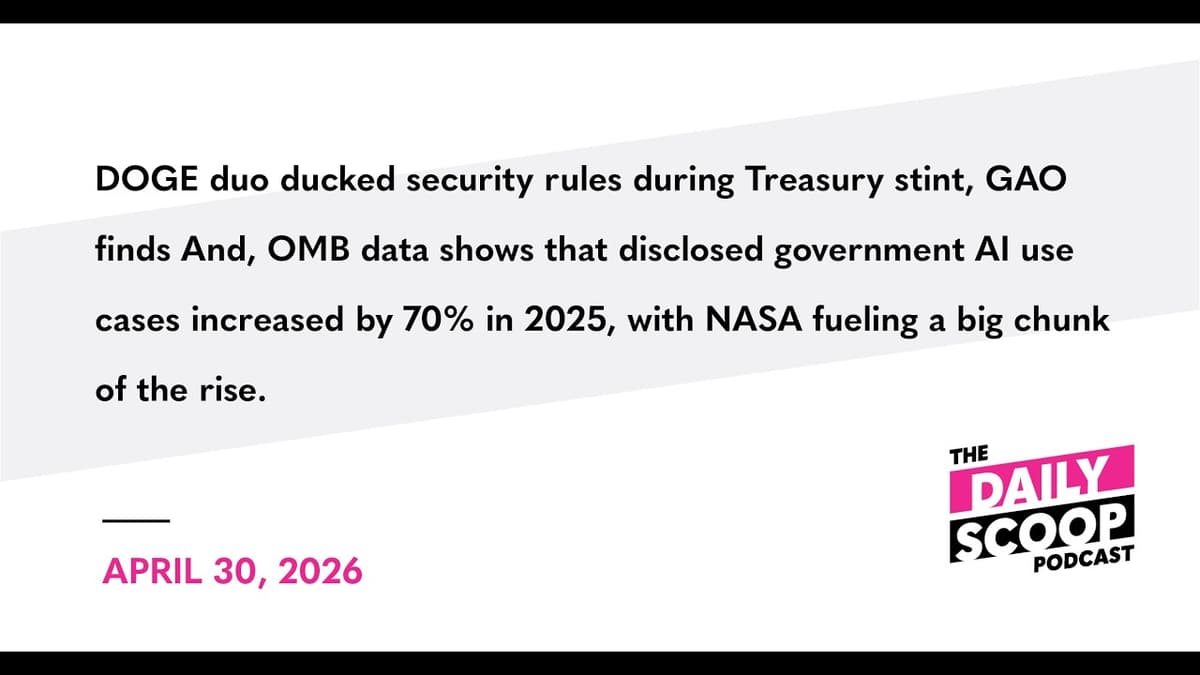
DOGE Duo Ducked Security Rules During Treasury Stint, GAO Finds
The Government Accountability Office released a report exposing serious IT security lapses by two Dogecoin‑affiliated staffers who were temporarily assigned to the Treasury Department’s Bureau of the Fiscal Service (BFS) during early 2025. The watchdog examined their access to three...

Indiana Rolls Out GenAI for All State Staff — and Leadership
The Indiana state government announced a statewide deployment of Microsoft’s Generative AI platform, Co‑Pilot, extending access to every employee and senior leader. After an eight‑week pilot that involved dozens of agencies, officials reviewed data‑access patterns and uncovered unexpected risks. Over the...
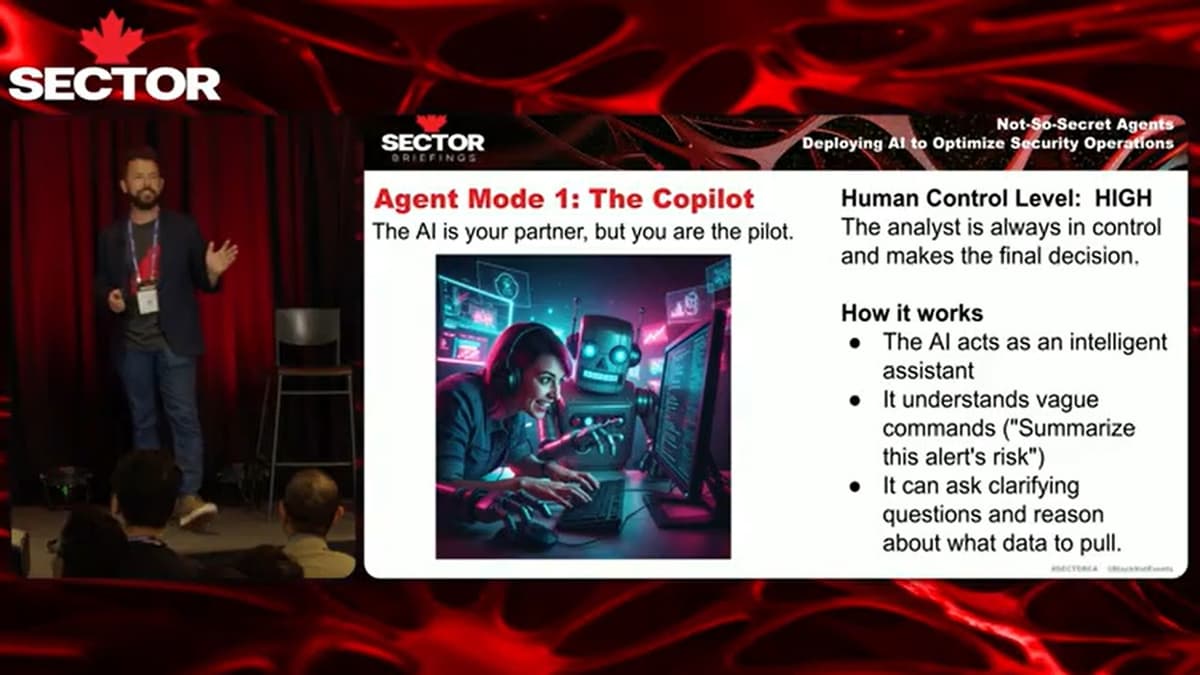
SecTor 2025 | Not-So-Secret Agents: Deploying AI to Optimize Security Operations
The SecTor 2025 talk, led by Red Canary’s data‑science head, detailed how the company deploys AI agents to streamline security‑operations centre (SOC) workflows. By integrating large‑language‑model agents into their managed detection and response (MDR) platform, Red Canary processes roughly 350,000...

Mastering Transitions & Continuous Improvement
The discussion centers on how enterprises should rethink ERP projects, treating them as ongoing transformations rather than one‑off implementations. Guests highlighted that true change management involves guiding cultural shifts when moving from legacy platforms like Lawson to modern suites such...

Data Liberation, Tech Debt, and the Road to AI Ready | Executive Interview with Jim Jacobs
In this executive interview, Jim Jacobs, CEO of Metaquant, explains how the company’s active‑data archiving platform helps health systems untangle legacy systems, cut operational costs and lay the groundwork for artificial‑intelligence initiatives. By extracting and preserving data from outgoing EHRs...

Podcast Ep270: The ERP Industry & the Mafia?, The Machine Is Rigged, The Safe Choice Is the Riskiest
In Episode 270 of Transformation Ground Control, Eric Kimberling likens the ERP ecosystem to an organized‑crime syndicate, arguing that vendors, system integrators and analysts act as a well‑oiled machine that extracts value at the customer’s expense. He frames the dynamic...

TSAM London : NeoXam's Blueprint for Taming Private Market Complexity with AI
NeoXam presented a roadmap for applying artificial intelligence to tame the growing complexity of private‑market data, focusing on private equity and credit portfolios that are increasingly adopted by institutional investors. The firm’s approach combines AI‑driven extraction of structured information from unstructured...

Why ERP Talent Is Vanishing!
The conversation centers on the growing scarcity of ERP consultants and the launch of the "ERP Perspective" podcast as a remedy. Host George explains that firms struggle to locate skilled talent, many of whom are nearing retirement, and that traditional...

Build Vs. Buy Apps: Avoid Salesforce & Workday Nightmares #shorts
The video tackles the classic build‑versus‑buy dilemma for enterprise applications, using Salesforce and Workday as cautionary examples, and warns that purchasing a SaaS solution does not eliminate maintenance headaches. Speakers cite real‑world incidents where preview instances suffered database failures, causing downtime...
Agentic AI and the Future of Enterprise Software in 2026
Agentic AI is reshaping enterprise software as large language models gain reasoning capabilities, a shift sparked by GPT‑4’s 2024 release. The conversation highlights how models have moved from chat‑only interfaces to true agents that can plan, access tools, and retain...

Why Enterprise AI Demands More Platform Engineering, Not Less | Weave Intelligence
Boyan, CTO at Sixt, says the company’s product and engineering organization totals about 800 people and builds over 95% of its core software in-house across hundreds of countries. Over the past decade Sixt has invested in broad platform engineering—MLOps, developer...
Hyatt Is Quietly Rebuilding With AI
Hyatt is quietly rolling out ChatGPT Enterprise across marketing, finance, customer experience and other core functions, marking one of the first large‑scale AI deployments in the hospitality sector. The initiative reflects a broader industry trend where hotels, cruises and airlines...

How Modern Systems Power Financial Stewardship in Rural Healthcare
The interview at the HIMS conference spotlights how modern ERP platforms are reshaping financial stewardship in rural health systems. CFO Brent Ray of Montgomery County Memorial Hospital and Multiview ERP CEO Mike Johnson discuss the chronic challenges of fragmented payers,...

Podcast Ep269: Hidden Cost of Agile, 20 Perspectives From ERP Lessons, Agentic AI Landscape in 2026
Episode 269 of Transformation Ground Control tackles three intertwined themes: the hidden costs of applying agile methods to ERP projects, insights gathered from twenty ERP‑implementation interviews, and Oracle’s launch of agentic AI‑driven Fusion applications that signal a shift toward autonomous...

The Factory Operating System Revolution
The video explores the emerging "factory operating system" – a unified platform that merges real‑time operational data, artificial intelligence, and modern IT architectures to reshape manufacturing. The speaker argues that after a decade of digitizing machines, the industry is finally...
Real Customers React to Chloe — Close's AI Sales Teammate
The video introduces Chloe, Close’s AI sales teammate that functions as a conversational power‑dialer, calling prospects on behalf of users. Demonstrations show Chloe can be configured in under two hours, instantly learn product details, and qualify complex mortgage and tax offerings,...

𝗧𝗵𝗲 𝗠𝗮𝗰𝗵𝗶𝗻𝗲 𝗜𝘀 𝗥𝗶𝗴𝗴𝗲𝗱 — 𝗛𝗲𝗿𝗲'𝘀 𝗛𝗼𝘄 𝘁𝗼 𝗙𝗶𝗴𝗵𝘁 𝗕𝗮𝗰𝗸
Digital transformation has become a trillion‑dollar industry, yet more than 70% of initiatives miss their targets, often due to a self‑reinforcing ecosystem of vendors, consultants, and analysts. In a live session, author Eric Kimberling explains how this "Machine" locks enterprises...
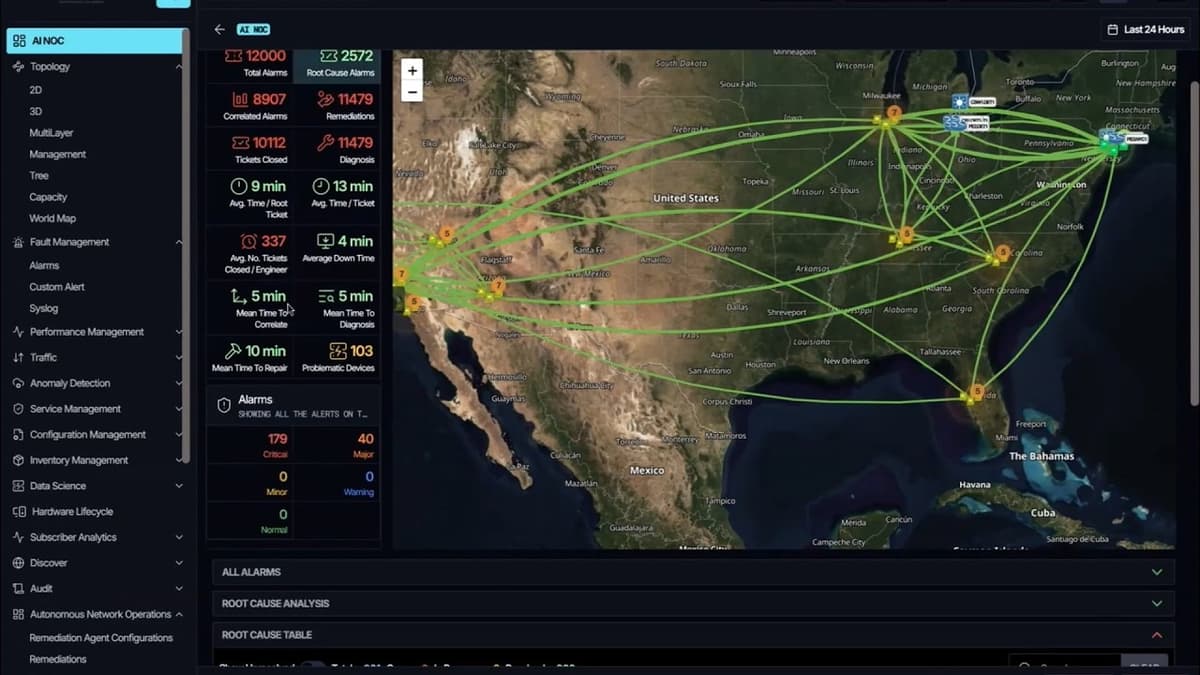
NetAI GraphIQ Demo with Irfan Lateef
The video showcases NetAI’s GraphIQ platform, a next‑generation AI‑ops solution that stitches together device‑level data—CLI configs, SNMP traps, gNMI streams, and even cloud telemetry—into a unified graph model. Van Latif walks through the functional architecture, highlighting how the platform builds...

Podcast Ep268: 40% of Agentic AI Canceled, ERP Industry Changing & Evolving, Why ERP Projects Fail
The Transformation Ground Control podcast highlights three critical trends shaping digital initiatives. Gartner predicts that 40% of agentic AI projects will be canceled by 2027, underscoring rising complexity and budget pressures. The episode also maps the ERP software industry’s shift...

Aviz Network Copilot Demo with Cody McCain
The video demonstrates Aviz Network Copilot, an AI‑powered platform that brings large language models into network operations, showing how it can automate troubleshooting, configuration, and security tasks across multi‑vendor environments. The presenter explains that AI in NetOps evolves from manual configuration...
InsurTech NY: Data Logistics on Automating Inbound Documents and Simplifying Claims
At InsurTech NY, a data‑logistics startup showcased its configurable platform that automates the intake of inbound claim documents for insurers and risk‑management firms. The solution captures submissions from PO boxes, email and text, normalizes the data, and delivers a clean,...

𝟮𝟬 𝗟𝗲𝘀𝘀𝗼𝗻𝘀 𝗳𝗿𝗼𝗺 𝟮𝟬 𝗘𝗥𝗣 𝗣𝗲𝗿𝘀𝗽𝗲𝗰𝘁𝗶𝘃𝗲𝘀
George Collier, founder of the ERP Perspective podcast, sat down for a live LinkedIn session to dissect the biggest themes emerging from his first 20 episodes. He highlighted recurring trends across SAP and Infor ecosystems, the rise of AI agents...
Can AI Decisions Be Tracked Like Humans? ERP Has The Answer! #shorts
The video examines whether AI decision‑making can be audited like human approvals, and argues ERP systems may provide the needed traceability. Oracle touts built‑in governance, but the speaker notes that auditability depends on the specific AI tool. Core ERP suites from...

ServiceNow’s AI-First Shift | Agent Trap Alarms | Nutanix X NetApp Field Trip
The panel dissected ServiceNow’s announcement that its platform will become "AI‑first," meaning artificial‑intelligence capabilities are baked into the core product rather than sold as separate add‑ons. Executives debated whether this signals a genuine cost‑saving strategy for customers or a...

AI Agents Fail in Production. Here's Why State Management Matters | Mark Fussell, Dapr
The video announces the general availability of Dapr Agent 1.0, a CNCF‑graduated project that extends Dapr’s durable workflow engine to run AI agents in production on Kubernetes. Mark Fussell explains that the core problem for production‑grade agents is state management, failure recovery...

What If Your ERP Could Do Your Accounting Team's Manual Work? | Meet Campfire
The discussion centers on Campfire, an AI‑native enterprise resource planning platform that reimagines the general ledger for midsize tech firms. Co‑founder John Glasco, a former CFO at Adobe and other public companies, launched Campfire after experiencing the limitations of legacy...

How Lightpath Is Optimising Revenue Management Processes with Oracle Solutions
The video details Lightpath’s partnership with Oracle to modernize its revenue‑management and back‑office operations. After a 2025 carve‑out from its primary investor, Lightpath embarked on a heavy‑lift transformation, standing up independent finance, supply‑chain, and billing platforms to gain autonomy and...

Digital Transformation's Dark Side
The live discussion tackled the often‑unseen backlash that digital‑transformation commentators face when platforms enforce copyright claims. Host Eric Kimberling and guest Emma Roloff used a recent Instagram takedown of Emma’s satirical ERP‑failure video to illustrate how a crisis‑PR firm can...

How WiseTech Is Compounding Advantages Across Global Trade
WiseTech, a leading logistics software platform, is embedding artificial intelligence directly into the core workflows that power global trade. CEO Zubin Appoo explained how the company’s AI strategy differs from superficial add‑ons, focusing on deep integration across freight, customs, and...

Podcast Ep267: SAP Partnering With Open Data, State of ERP in 2026, ERP Vendor Blame
Podcast episode 267 explores SAP’s new partnership with the Open Data Institute, examines predictions for ERP in 2026, and critiques the tendency of ERP vendors to blame customers for implementation failures. The SAP‑ODI collaboration aims to create open data standards...