
Box’s Strategic Pivot From Content to Context
Box is redefining its platform by shifting from a content‑centric model to a context‑driven architecture that empowers autonomous AI agents. The company argues that traditional workflows assume users start with zero context, but agents need just‑right, surgical context to act effectively. The transcript highlights three operational challenges: data and context are scattered across unstructured files, 99% of knowledge work lacks an ‘agent.mmd’ manifest, and existing processes cannot deliver the precise context required. To address this, Box plans to reengineer workflows, embed agents as first‑class platform users, and build secure, governed pipelines for context delivery. As an executive puts it, “if you just swap the word content for context, the rest of the strategy is basically the same.” This underscores the belief that the core value proposition—helping people work with data—remains unchanged, only the consumer of that data shifts from humans to AI agents. The pivot positions Box to capture enterprise demand for generative AI assistance, promising faster decision‑making and reduced friction while demanding robust security and scalability. Companies adopting the platform could see productivity gains, but must invest in metadata hygiene and governance to realize the promised benefits.

Digital Health Unplugged: Rolling Out the FDP and AVT at Scale
The Digital Health Unplugged episode captured at Digital Health Rewired 2026 highlighted how University Hospitals Leicester (UHL) and University Hospitals Northampton (UHN) are scaling two cornerstone initiatives – a Federated Data Platform (FDP) and Ambient Voice Technology (AVT) – across...

🎙 𝗢𝘃𝗲𝗿𝘃𝗶𝗲𝘄 𝗼𝗳 𝘁𝗵𝗲 𝗘𝗥𝗣 𝗦𝗼𝗳𝘁𝘄𝗮𝗿𝗲 𝗜𝗻𝗱𝘂𝘀𝘁𝗿𝘆
Eric Kimberling hosts Kristin Valentyn, a veteran ERP executive, to dissect the current state and future trajectory of enterprise resource planning software. They highlight how cloud migration and AI integration are reshaping the market, enabling faster, subscription‑based deployments for manufacturers...

AI Hype Vs. Reality: What REALLY Works Now? #shorts
The video examines the gap between AI hype and reality as SAP, Salesforce, Oracle and other enterprise software giants rush to embed AI agents into their core platforms. It asks when “soon” becomes “now” and how buyers can separate genuine...

The Security Gap Nobody Talks About
The video highlights a critical security gap: legacy perimeter firewalls were built for three‑tier, MVC applications and cannot protect today’s hyper‑distributed workloads. Modern finance‑type applications now span on‑prem data centers, Kubernetes clusters in the cloud, and AI‑driven LLM chatbots, creating...

Handing Over The Keys to Your Kingdom: AI-Driven Security Woes
The video warns that AI agents and DevSecOps tools, despite holding extensive permissions, suffer from weak oversight, creating a "credential‑drift" crisis. Recent supply‑chain attacks have compromised popular utilities such as Trivy, Axios, LiteLLM, OpenAI Codex, and Claude Code. The speaker...

Ramsoft OmegaAI and Blume Review: A Hands-On PACS and Portal Walkthrough
The video provides a hands‑on walkthrough of Ramsoft’s OmegaAI cloud‑based radiology platform and its companion patient‑portal, Bloom. Sponsored but editorially independent, the reviewer demonstrates how a pure web, zero‑footprint solution lets users log in from any browser without installing software,...

OpenAl X Gradient Labs Founder Spotlight
The video features a founder spotlight on Gradient Labs, highlighting its partnership with OpenAI to overhaul banking customer support. The discussion centers on the inefficiencies of current human‑centric processes, where declined payments trigger a cascade of hand‑offs among transaction...

Black Hat USA 2025 | Uncovering and Responding to the Tj-Actions Supply Chain Breach
The presentation detailed a supply‑chain breach that hit the popular TJ‑actions/change‑files GitHub Action. On March 14, an automated alert flagged an unexpected outbound request, leading the Step Security team to discover that the action’s release tags had been repointed to a...

Evaluating Puppet’s Automation Capabilities I CIO Talk Network
The CIO Talk Network interview spotlights Puppet’s automation platform as a strategic lever for digital transformation. Chief Technical Strategist Nigel Kirsten frames automation not as a standalone fix but as part of a broader DevOps culture that blends measurement, sharing,...

AI, Big 4 Consulting & Leadership
The video is a candid discussion about the intersection of AI adoption, Big Four consulting firms, and leadership responsibility, framed by a recent legal warning over a social‑media post. The speakers argue that brands face heightened risk when social platforms amplify...

FireMon Brings Clarity to Firewall Rule Chaos (Sponsored)
The sponsored episode of Packet Protector spotlights FireMon, a policy‑control platform that aims to tame the growing chaos of firewall rules across on‑prem, cloud and micro‑segmentation environments. Jody Brazil explains that while firewalls have evolved—from ACLs to application‑aware and native cloud...

𝗧𝗵𝗲 𝗦𝘁𝗮𝘁𝗲 𝗼𝗳 𝗘𝗥𝗣 𝗶𝗻 𝟮𝟬𝟮𝟲: 𝗔 𝗟𝗶𝘃𝗲 𝗗𝗶𝘀𝗰𝘂𝘀𝘀𝗶𝗼𝗻
The podcast examines the current state of ERP in 2026, highlighting a decisive shift from generic, horizontal suites toward industry‑specific vertical applications. Host Erica and Diginomica’s Jonathan Reed explore how vendors are re‑architecting their platforms to embed vertical functionality, effectively...

How DayAI Automates Every Department and How to Agentify Your Operations
The Research to Runtime session featured Christopher O'Donnell of DayAI, who outlined how the startup is re‑imagining every department through AI‑driven agents. Drawing on his experience at HubSpot, O'Donnell described a new operating model where autonomous agents function like hired...

Agentic AI for Enterprise: How Globant Is Scaling AI Innovation in APAC & Middle East
Fernando, a 15‑year veteran at Globant, outlines how the firm is scaling agentic AI across its Middle East and APAC operations. The company moves beyond traditional product‑centric AI by deploying autonomous agents that orchestrate workflows, while keeping a technology‑agnostic layer...

For WBD’s Steinhauser, Agentic AI Is Now, A Unified Ecosystem Is Not-Yet
Warner Bros. Discovery’s senior ad‑tech leader, Steinhauser, outlined the company’s current foray into agentic artificial intelligence and its broader vision for a more open, API‑driven advertising stack. He emphasized that the pilot projects are already stripping low‑value, repetitive tasks from...

Cyber Week 2026 Wrap Up with Palo Alto Networks: Agents, Prisma AIRS and NGTS (Sponsored)
The podcast recaps Palo Alto Networks’ RSA 2026 announcements, spotlighting AI‑security guidance and the launch of Next‑Gen Trust Security (NGTS). Executives Ian Swanson and Rich Kana explain why enterprises must secure AI models, agents, and skills throughout the supply chain and...

CDW ERP Modernization Case Study | Workday & Deloitte
CDW, a Fortune 500 IT solutions provider with more than $20 billion in revenue, announced a comprehensive ERP modernization driven by Workday and Deloitte. The company sought a cloud‑based platform to replace a legacy system riddled with manual data extraction and...

SAP S/4HANA Integrator Secrets Revealed! 🚀 #shorts
The short video distills veteran consultant Eric’s reflections on working with SAP system integrators, emphasizing that every integration engagement is fundamentally a business transaction. Eric stresses that consultancies operate under the same profit imperatives as any other firm—revenue generation, gross margin...

When AI Starts Acting on Its Own...
At RSA, Cisco senior vice president Peter Bailey explained that zero‑trust security must evolve when the "identity" is an autonomous AI agent rather than a human user. He noted traditional zero‑trust assumes breach and relies on static credentials, but agents act at...
Legacy Software: Stuck or Savvy? Rethink Your Next Move! #shorts
The video addresses a common dilemma for enterprises running legacy ERP platforms such as SAP or older Oracle suites: whether to rely on third‑party support to prolong the system’s life or to embark on a costly, high‑risk transformation. It highlights...

How GFT & Mambu Are Replacing Legacy Core Banking Systems
The video outlines how GFT, a global banking‑technology integrator, and Mambu, a cloud‑native composable core platform, have joined forces to replace legacy mainframe systems. Their joint offering combines Mambu’s standardized code base with GFT’s regulatory and implementation expertise, promising a...

End-to-End Supply Chain Excellence: AI, Visibility & Warehousing
Supply chain leaders are grappling with mounting returns, unsynced omnichannel data, and manual reconciliations that erode margins and customer loyalty. The upcoming Softeon‑hosted LinkedIn Live on April 2 will address these pain points by showing how to eliminate data silos...

NEW: Inside ServiceNow’s $10B Go-to-Market Engine with Paul Fipps
ServiceNow’s president of global customer operations, Paul Fipps, walked viewers through the company’s $10 billion go‑to‑market engine, a platform that has driven more than 20% annual growth for five straight years. The firm expects its customers to run roughly $80 billion in workflows...

ERP Extensibility - D365 vs SAP 🚀 #shorts
The video tackles a core dilemma for ERP buyers: how much functionality should reside inside the ERP platform versus external extensions, focusing on Microsoft Dynamics 365 (D365) and SAP S/4HANA. It frames the discussion as a trade‑off between built‑in capabilities...

RevOpsAF Podcast Episode 84: Your CRM Has an Identity Crisis (and What You Can Do About It)
The RevOps AF podcast episode tackles the "CRM identity crisis" – how flawed entity records in CRMs cripple AI‑driven revenue operations and data enrichment. Host Matthew Vaughn and Kernel CEO Anders Cone explain that the root problem lies not in missing...

Black Hat USA 2025 | China's 5+ Year Campaign to Penetrate Perimeter Network Defenses
The Black Hat talk detailed a multi-year, state-linked campaign by Chinese threat actors aimed at compromising perimeter firewalls and the networks they protect. Presenter Andrew Brandt, a principal threat researcher formerly at Sophos, walked through the evolution of the operation,...

From AI Hype to Execution: The Future of Supply Chain Planning
At Manifest 2026, OMP’s Andrew Driscoll discussed the shift from AI hype to tangible supply‑chain execution. He highlighted how integrated planning platforms, digital twins, and connected data ecosystems are accelerating decision‑making and disruption response. The conversation underscored the critical challenge...

Why Most CRM Systems Fail (And How to Fix Them)
The video argues that most CRM implementations collapse because users abandon the system once they fall behind, opting for fresh prospecting instead of leveraging existing records. It highlights that dormant contacts often represent higher lifetime value than newly sourced leads, and...

LSEG World-Check Verify
The video introduces LSEG World-Check Verify, a cloud‑native name‑screening API designed to embed directly into payment and onboarding pipelines. Built on Amazon Web Services, the solution promises real‑time, privacy‑first checks that keep compliance from slowing down instant‑payment ecosystems. Key features highlighted...

Solution Showcase: The Freeing Power of Testing Automation with Phillip Furukawa and Chris Paravate
The episode spotlights SH Test’s testing‑automation platform and its deployment at Northeast Georgia Health System (NGHS), a 1,000‑bed, multi‑hospital network running Epic across acute, long‑term and rehab care. The discussion centers on how automated regression testing reshapes the traditionally labor‑intensive...

Hollywood Drama, Sales Secrets, & SAP's $172M Failure
The conversation weaves together a Hollywood‑style intrigue about leaked texts with a deep dive into sales ethics and a high‑profile ERP disaster. Host Eric and his guest use the Zimmer Biomet saga—where a $172 million SAP S/4HANA rollout was sold as...

How Profile Software Is Modernising Banks Worldwide
Profile Software, a publicly listed Greek fintech firm, is positioning itself as a catalyst for banks’ digital transformation. The company focuses on two growth pillars—API‑driven core banking modernization and embedded finance—helping institutions replace legacy systems with modular, cloud‑ready platforms...

Vision, Communication, & Leadership Secrets
The discussion centers on three pillars of effective change management—vision, communication, and leadership—while also probing the strategic risks of emerging technologies like SAP’s AI‑enhanced master data governance. Speakers argue that a clear, purpose‑driven vision aligns teams, but without two‑way dialogue...

Black Hat USA 2025 | Reinventing Agentic AI Security With Architectural Controls
At Black Hat USA 2025, David Brockle III of NCC Group opened his briefing by framing AI security as a modern parallel to the early web’s reliance on firewalls. He argued that today’s AI guardrails function like statistical heuristics—useful but...
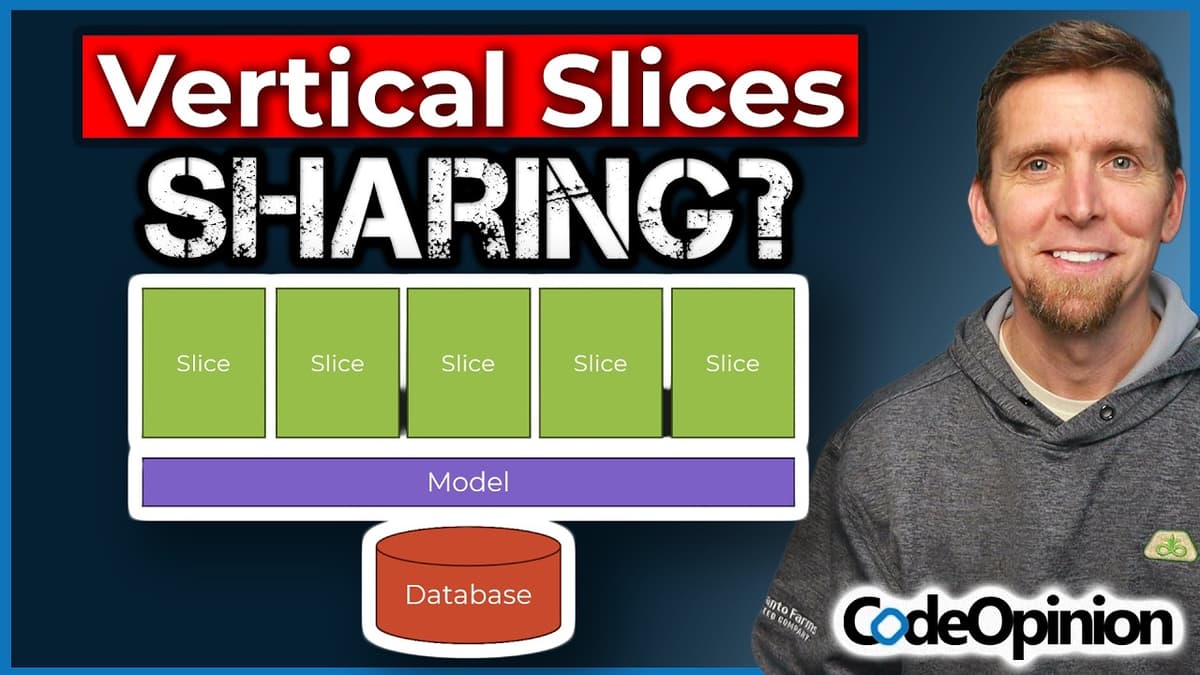
Vertical Slice Architecture Doesn't Mean “Share Nothing”
Dererick Martin clarifies a common misconception about vertical‑slice architecture: it does not mandate absolute code isolation, but rather the selective sharing of appropriate concerns. He distinguishes between technical plumbing—error handling, logging, outbox/event‑bus utilities—and domain data, which each slice owns. The slice...

Data Security in the Age of AI: Proactive Strategies to Protect Your Most Valuable Assets
The webcast, led by Peter Sleven, senior information‑security manager at Bank of Ireland, examined how enterprises can safeguard data as AI adoption accelerates. Sleven framed data security as a prerequisite for successful AI projects and outlined a roadmap that spans...

ThreatLocker CEO Told Me the Codename... Project Elephant
The video features ThreatLocker’s CEO previewing an upcoming product reveal, internally dubbed “Project Elephant.” The initiative follows the company’s recent success with zero‑trust endpoint protection, which now operates without generating alerts unless left in monitor mode. Key insights include the realization...

Delivering Higher Value in Lesser Time I CIO Talk Network
The CIO Talk Network episode focuses on how the U.S. Department of Energy’s CIO, Ann Duncan, is rethinking government IT to deliver higher value in less time. She frames the challenge as an “infinite game” where public expectations now mirror...

João Moura on Multi-Agent Systems, Autonomous Workflows & AI Entrepreneurship | Ep 09
In this episode, João Moura (Joe Mora), founder and CEO of Crew AI, discusses the company’s mission to deliver end‑to‑end multi‑agent workflows for large enterprises. He explains how the startup grew from an open‑source library into a platform that handles everything...

Cybersecurity Careers: Cloud Security Engineer (7 of 9 Careers)
The video spotlights the cloud security engineer track, emphasizing its distinct importance amid soaring demand for cloud expertise. Host Joe South outlines three career tiers—junior, senior, and lead—each with escalating responsibilities within an organization’s cloud defense posture. Junior engineers primarily monitor...

Learn MLOps with MLflow and Databricks – Full Course for Machine Learning Engineers
The new free course offers an end‑to‑end deep dive into MLflow, the industry‑standard platform for managing the full machine‑learning lifecycle. It guides learners through experiment tracking, model versioning, prompt management, and systematic evaluation, then demonstrates professional integration with Databricks and...

Black Hat USA 2025 | Use and Abuse of Palo Alto's Remote Access Solution
The presentation examined Palo Alto’s GlobalProtect remote‑access solution, focusing on its split‑tunnel feature that lets administrators whitelist domains such as *.zoom.us to bypass the VPN. The speaker, a security engineer with pentesting background, demonstrated how the feature intertwines DNS resolution...

Black Hat USA 2025 | Turning Camera Surveillance on Its Axis
At Black Hat USA 2025, Noam Moshe of Claroty Team82 exposed a critical flaw in Axis Communications’ Access Remoting protocol, the encrypted channel used by enterprises to manage fleets of IP cameras remotely. The protocol, built on MTLS and NLMSSP authentication,...

Cloud Strategy, The Future of Infrastructure, and Of Course AI at Cloud Field Day 25
Cloud Field Day 25, held March 11‑12, focuses on cloud strategy, future infrastructure, and AI, featuring live sessions streamed on LinkedIn, YouTube, and partner sites. The agenda includes Hammerspace’s demonstration of a global namespace and policy‑based data management for AI workloads,...

Sam Jenkins Interview | Turning Data Into Better Business Decisions
Sam Jenkins, managing partner at Punchcard Systems, discusses how organizations can turn raw data into decision‑making products that drive better business outcomes. His upcoming talk focuses on building high‑performing digital enterprises by treating data strategically, designing tools around specific decision...

João Moura on Multi-Agent Systems, Autonomous Workflows & AI Entrepreneurship | Teaser
João Moura, reflecting on building CREI, argued that startups often must build complete systems in-house because partial solutions fail to reach production—teams expose the wrong data, lack deployment and monitoring, and ultimately don’t trust their models. He advised first-time AI...

𝗧𝗵𝗶𝗿𝗱-𝗣𝗮𝗿𝘁𝘆 𝗠𝗮𝗶𝗻𝘁𝗲𝗻𝗮𝗻𝗰𝗲: Regaining Control of Your Technology Roadmap
Eric Helmer of Rimini Street discusses third‑party maintenance for legacy enterprise systems such as SAP ECC, JD Edwards, Salesforce, and VMware. He explains how TPM can slash support fees, keep stable platforms running longer, and sidestep mandatory cloud migrations. The...

Minder: Policy-Based Control of Software Security | OpenSSF Project Spotlight
Minder, an OpenSSF initiative, provides continuous policy enforcement for software supply chains, monitoring repositories, releases and pull requests to maintain security compliance with minimal friction. The service defines policies, uses webhooks to detect drift, and automatically remediates violations via patches, comments...

Black Hat USA 2025 | Lost & Found: The Hidden Risks of Account Recovery in a Passwordless Future
The Black Hat USA 2025 presentation warned that account‑recovery mechanisms—intended as a safety net for forgotten passwords—are rapidly becoming the most exploitable entry point in a passwordless ecosystem. Speakers Sidra, Gabby, and their research team outlined how recovery flows...