
Open CTI Retirement Guide: Moving Salesforce Contact Centers Toward Agentforce
Salesforce will retire its Open CTI telephony integration on February 28 2028, prompting contact centers to replace the legacy bridge with a modern solution. The recommended path centers on Salesforce Voice combined with the Agentforce AI engine, either as a fully native platform or through a hybrid BYOT layer that preserves existing telecom hardware. Integrated AI is reported to save 93% of agents time and cut routine task effort by 20%, with Agentforce already handling over two million conversations. A detailed migration playbook outlines auditing, architecture selection, piloting, parallel runs, and full rollout to ensure a seamless transition.

CIO Playbook: From IT Strategy to Business Outcomes — What It Really Takes
Senior IT leaders at a Digital Boardrooms session highlighted why massive cloud, data and AI spend still yields limited business impact. They argued that AI and analytics fail when layered on fragmented processes, with 85‑95% of initiatives not moving the...

86% of Phishing Attacks Are AI Driven, KnowBe4 Research Finds
KnowBe4’s seventh Phishing Threat Trends Report reveals that 86% of phishing attacks now leverage AI, marking a dramatic shift from traditional email‑only scams. The study documents a 49% rise in calendar‑invite phishing, a 139% surge in reverse‑proxy techniques targeting Microsoft...

The AI-Native Enterprise: Rearchitecting Your GTM Stack for Agent-Driven Operations
The article warns that traditional GTM stacks—built for human‑keyboard interaction—cannot safely support autonomous AI agents without a structural overhaul. It pinpoints three architectural layers—integration, identity, and governance—that must be re‑engineered, and proposes four production‑tested patterns (Tool Gateway, Identity as Context,...

Fortifying Organizational Fragility (Part 1)
The author warns that growing reliance on SaaS, cloud services and AI has turned modern enterprises into fragile constructs, likening today’s digital dependency to the 24 U.S. Navy vessels that became paperweights during a Starlink outage. Recent disruptions—such as a...

ILTA Just-In-Time: Preparing for Cloud Outages
A joint blog by legal‑industry IT leaders warns that cloud‑based services remain vulnerable to outages. The authors outline a "just‑in‑time" framework that emphasizes proactive monitoring, multi‑region redundancy, and clear client communication. They share practical steps firms can adopt to minimize...

From Query Builder to Knowledge Engineer: The Architecture of Generative AI in Enterprise ERP
The article argues that enterprise ERP architects must evolve from query builders to knowledge engineers, a shift enabled by upgrading to Oracle EBS 12.2.14. This release provides native REST services and a secure data layer that lets large language models...

Beyond the Perimeter: Why Identity and Cyber Security Are One Single Story
Identity and cyber security are converging as cloud adoption, distributed workforces, and third‑party integrations dissolve traditional network perimeters. Continuous authentication and contextual monitoring replace static, gate‑based controls, requiring a shared risk model across users, devices, and environments. The article outlines...

DORA and the Practical Test of Operational Resilience
The EU’s Digital Operational Resilience Act (DORA), in force since January 2025, obliges financial‑service firms to manage IT risk, conduct realistic stress tests, and govern third‑party providers at board level. A recent Censuswide survey shows 96% of EMEA institutions still lack...

AWS Security Digest #258 - Vercel of Secrets
Vercel disclosed a security incident on April 19, 2026 after an attacker leveraged a compromised third‑party AI productivity tool, Context.ai, to hijack an employee’s Google Workspace account and pivot into Vercel. The breach allowed the threat actor to enumerate and...

You Can’t Mature Enterprise Architecture Until You Decide What “Better” Means
Enterprise architects struggle to agree on what a mature architecture looks like, with definitions ranging from fixing brittle platforms to delivering CFO‑friendly financial metrics. Forrester argues that without a shared definition of “better,” EA initiatives remain fragmented and fail to...

Secret Management in Production: Vault, KMS, and Rotation Strategies
The post outlines a three‑layer secret‑management model that separates key management (KMS), secret storage (Vault or cloud secret managers), and application consumption. It explains envelope encryption, showing how KMS protects data‑encryption keys while Vault handles lifecycle tasks such as rotation,...

Your Data Platform Costs More Than It Should
A Snowflake migration revealed unexpectedly high cloud spend, prompting a deep dive into data platform economics. The author demonstrates how simple SQL queries can surface the most credit‑hungry warehouses and queries, exposing idle compute and full‑table scans. By adjusting auto‑suspend...

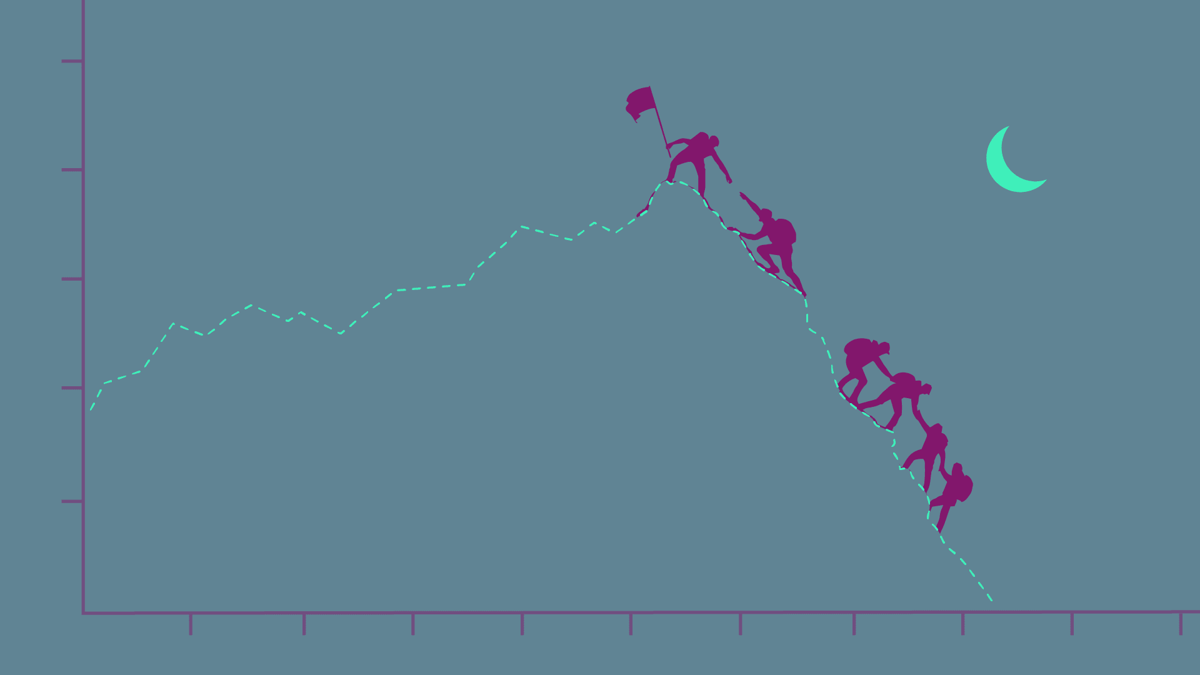
The New Software Economics: Earn the Right to Invest Again, in 90-Day Cycles
Leonard Greski argues that traditional CapEx vs OpEx debates are obsolete for software development. Decades of accounting standards, from SFAS 86 to ASC 350‑40, allowed capitalization, but cloud and SaaS have shifted 70% of IT spend to the income statement. Agile sprint...

From the Microsoft Dynamics GP Blogs: Cost of Not Investing in GP Now; Myths of GP to BC Migration; Migrating...
Recent Microsoft Dynamics GP blog round‑up warns SMBs that delaying investment in GP drives rising maintenance and upgrade costs, outlines five common myths surrounding migration to Dynamics 365 Business Central, and highlights an often‑overlooked gap in moving GP reporting tools....

From the Microsoft Dynamics 365 Business Central Blogs: Cloud Migration; External Storage; Better Reporting; Critical Security Practices
Microsoft’s Dynamics 365 Business Central blog series highlights four critical topics for ERP users: cloud migration, external storage for attachments, reporting evolution, and essential security practices. Author Stefano Demiliani warns partners not to reuse the same self‑hosted Azure Integration Runtime during...

The Infrastructure You Need for the Solutions You Want, with Tyler Hochman of FORE Enterprise
Tyler Hochman founded FORE Enterprise's workforce turnover prediction platform five years ago, gaining solid market traction. However, customers repeatedly hit a roadblock: they lacked the data infrastructure needed to feed the tool. To address this, FORE built a turnkey data...

Enterprise Architecture in the Age of AI: More Critical Than Ever
Enterprise Architecture (EA) is becoming indispensable as organizations embed artificial intelligence across their tech stacks. The article argues that AI cannot replace the strategic oversight EA provides, especially when coordinating disparate SaaS solutions and ensuring data governance. It highlights how...

Router Security Hardening Steps for 2026: From Default Credential Audits to Automated Firmware Risk Monitoring
Network edge devices, especially routers, have overtaken PCs as the primary cyber‑attack vector, a trend accelerated by hybrid work in the Netherlands. Threat actors exploit default credentials, unpatched firmware, and exposed management interfaces, making routers the weakest link in many...

Portworx by Everpure Is Redefining Modern Virtualization for Customers with Proven, Enterprise-Ready Solutions
Portworx by Everpure unveiled new Enterprise capabilities that let organizations run both virtual machines and containers on Kubernetes at scale. The platform now supports over 100,000 VM volumes across on‑prem, hybrid, and multi‑cloud environments, offering unified storage, data‑management, and built‑in...

Modernising the Legacy Estate: Reducing Technical Debt without Starting From Scratch
Made Tech argues that public‑safety agencies should modernise legacy IT by evolving existing platforms rather than replacing them wholesale. Technical debt manifests as fragmented, hard‑to‑maintain code that forces caseworkers to juggle multiple systems and spreadsheets. By combining user research, service...

Heineken’s Schilperoord Talks About Being a Chief Architect and His Involvement with Iasa Global
Arno Schilperoord, Heineken’s Director of Global Architecture & Innovation, explains how enterprise architecture drives the brewer’s massive digital transformation. He stresses that architecture must provide intentional, value‑driven direction, linking processes, data, and technology across regions. Schilperoord highlights the need for...
When Personal Tools Become Enterprise Systems
The article explains how low‑code, SaaS, and AI tools enable individuals to create solutions that quickly address unmet needs, turning personal productivity hacks into de‑facto enterprise systems. As these shadow‑IT solutions scale, they begin to store shared data, support recurring...
OpenClaw AI Deployment on Dedicated Servers: A Practical Infrastructure Guide
OpenClaw AI agents require dedicated server infrastructure to meet their persistent, memory‑intensive workloads. Shared or virtual environments cause CPU throttling, I/O latency, and unreliable context handling, forcing costly migrations later. The guide outlines hardware baselines—32 GB RAM, NVMe storage, and dedicated...

Declaring Independence: Why We Are Starting the “Free Your IT” Movement
Ardoq announced the “Free Your IT” movement, a campaign aimed at breaking the traditional Big Tech lock‑in model that forces enterprises to surrender data control and roadmap autonomy. The initiative promotes open standards, interoperable architectures, and a community‑driven approach to...

The Architecture of Trust: How Enterprises Can Safely Deploy PII in LLMs
Enterprises can now safely process personally identifiable information (PII) within large language models by embedding the models in a purpose‑built protective architecture. The approach combines a fine‑grained entitlement layer that classifies and enforces access rules, end‑to‑end encryption that keeps data...

Cloud Security Maturity at the GovExperience Summit
The Carahsoft GovExperience Summit 2026 highlighted a growing awareness of cloud‑security challenges in the federal government, but revealed significant architectural gaps. Two panels showed that while some officials can articulate multi‑cloud governance, many still treat security as a procurement decision...
Check Point Quantum Scales Throughput for Digital Transformation
Check Point Software Technologies showcased its Quantum firewall, paired with ThreatCloud AI, in a Philippine commercial bank and an Angolan telecom provider. Frost & Sullivan’s report finds the solution delivers higher throughput, automated threat prevention, and unified policy management, overcoming...

Veeam Report Reveals a Market-Wide Shift From Recovery Confidence to Proven Data Resilience Amid Ransomware Threats and AI Adoption
Veeam’s Data Trust and Resilience Report 2026, based on more than 900 senior IT and security leaders, shows a stark gap between confidence and reality: while 90% of organizations believe they can recover from a cyber incident, only 28% fully recover...

Oracle and AWS Collaborate to Expand Multicloud Networking
Oracle announced a new multicloud networking link that directly connects its Oracle Interconnect with AWS Interconnect‑multicloud, delivering a private, high‑performance bridge between Oracle Cloud Infrastructure (OCI) and Amazon Web Services. The service will launch later this year in the AWS...

What to Do When Your AI Guardrails Fail
Microsoft 365 Copilot inadvertently processed confidential emails in users’ Sent Items and Drafts, bypassing sensitivity labels and Data Loss Prevention policies due to a code bug (CW1226324). The incident exposed a fundamental architectural flaw: all AI governance controls reside within...

Lentech Names Mike Majarov Chief Innovation, IT Officer
Lentech has created a new Chief Innovation and Information Technology Officer role and appointed long‑time executive Mike Majarov to fill it. Majarov will oversee enterprise architecture, infrastructure and emerging technologies, including mission‑specific AI capabilities. The move underscores Lentech’s push into...

The New Ardoq Experience: Why We Redesigned the Platform
Ardoq unveiled a redesigned platform on April 8, introducing a fresh user experience tailored for enterprise architecture teams. The new interface emphasizes visual modeling, drag‑and‑drop workflows, and real‑time collaboration across the organization. Underlying performance upgrades enable faster processing of large, complex...

98% of Buyers Will Ask About Your AI Agents at Renewal
Okta announced the general availability of its AI Agent solution on April 30, giving enterprises a reference implementation for discovering, governing, and revoking autonomous AI agents. A survey of 150 IT decision makers revealed that 98% will factor agent‑governance controls...

Echeverry Shares Insights About Her Career in Architecture
Viviana Echeverry, an enterprise architect at IKEA, drives the company’s global digital transformation by shaping data platforms, integration frameworks, and governance models. Her career progressed from hands‑on development to designing the "invisible layer" that enables faster, more consistent product delivery....

Digitisation Is Not Optional – It’s National Strategy
Datuk Syahril Aziz, Group CEO of Dataprep, argues that digitisation is no longer optional for Malaysia but a core component of its national strategy. He urges CIOs to expand their remit beyond corporate walls, shaping ethical, human‑centric digital ecosystems that...

From CIO to Community Leader : Why Collaboration Is the New Power
Emmanuel Morka, Access Bank Ghana’s regional CIO, argues that today’s CIO must evolve from a traditional IT manager to a strategic architect of intelligence‑driven enterprises. He stresses that collaboration, community participation, and shared wisdom are essential for building competitive advantage....

Arch Insurance Promotes Fernández and Losada to Heads of Cyber for Europe & Iberia
Arch Insurance promoted Jose Carlos Jiménez Fernández to Head of Cyber for Europe and Rafael Ortiz Losada to Head of Cyber for Iberia, both effective immediately and based in Madrid. They will lead underwriting, product development and distribution of cyber...

No Digital Economy without Digital Infrastructure
The piece stresses that reliable connectivity, cloud access, and cybersecurity form the backbone of modern economic growth. It urges CIOs to move beyond day‑to‑day IT operations and become strategic leaders of infrastructure transformation. Resilience, ethical governance, and participation in a...

Black Duck Names Dom Glavach as CISO to Bolster Supply Chain and AI Security Push
Application security firm Black Duck has appointed Dom Glavach as its chief information security officer. Glavach arrives from CyberSN and a two‑decade tenure at defense contractor CTC, where he managed FedRAMP, DFARS and CMMC compliance and nation‑state incident response. His...

From Task Automation to Enterprise Orchestration: A Shift CIOs Can No Longer Ignore
Enterprises have invested heavily in RPA, AI pilots, and low‑code tools, yet many see only fragmented efficiency gains. The missing piece is orchestration—a coordination layer that links people, systems, data, and intelligent technologies across the organization. By shifting focus from...

Certes Launches V7 Platform with Quantum-Safe Encryption Across Hybrid Cloud and Edge Environments
Certes has unveiled version 7 of its Data Protection and Risk Mitigation platform, extending post‑quantum cryptography to hybrid‑cloud, edge and AI workloads. The update introduces per‑flow quantum‑safe encryption and cryptographic micro‑segmentation that can be deployed in days without rewriting legacy applications....
We Ditched Our Vendor and Built Our Own Destiny
Facing chronic delays and firmware bugs from a third‑party NIC vendor, the company chose to design and produce its own network interface card for hyperscale deployment. A cross‑functional team of software and production engineers was assembled, emphasizing operational experience over...
Low Code in Financial Services, Part 1: Addressing Six Recurring IT Pain Points
Financial institutions boast robust, highly governed core systems, yet everyday requests—such as intake forms and dashboards—still slog through centralized engineering backlogs, taking weeks to deliver. This creates fragmented workflow ecosystems, duplicate effort, and limited traceability. Low‑code solutions like Microsoft Power...

Inside View: Stewart Crane on Withers’ Technology Priorities and AI in Practice
In a recent Inside View interview, Stewart Crane, global IT director at Withers, outlined the firm’s technology agenda and its pragmatic AI rollout. Withers was an early adopter of Microsoft Copilot, deploying it firm‑wide to build internal AI expertise before...

Windows 11 Is Phasing Out Old Kernel Drivers: Microsoft Will Permanently End Cross-Signing in April
Microsoft announced that, starting with the April 2026 security update, Windows 11 will permanently stop trusting kernel drivers signed under the old Cross‑Signed Program. The change applies to Windows 11 24H2, 25H2, 26H1 and Windows Server 2025, allowing only drivers vetted through the Windows...

The Integrated Enterprise: Why Architecture Must Connect Product, Data, Execution, and Experience
The article argues that Gartner’s domain‑specific conferences deliver deep insight but leave enterprise architecture fragmented. It introduces Enterprise Experience Architecture (EXA) as a new layer that connects product, data, supply‑chain, and application domains to the human experience. EXA makes systems...

Oracle APEX and Artificial Intelligence: How a Low-Code Platform Is Arguably Changing the Rules of Enterprise Development
Oracle APEX now bundles artificial‑intelligence features directly within Oracle Database 23ai and APEX 24.1, letting developers add semantic search, generative AI, and predictive analytics through ordinary SQL without middleware. The platform’s low‑code approach reduces prototype cycles to a few days and...

Webinar: High Availability, Simplified
DH2i is hosting a webinar on April 16 at 12:00 pm EDT to demonstrate its newest high‑availability solution for Microsoft SQL Server across Windows, Linux and Kubernetes. The session will walk IT teams through automated scale‑up and scale‑down of SQL Server...

How Banks Are Modernising Legacy Systems
Banks are confronting decades‑old core systems that limit speed, integration and security. To stay competitive, they are adopting modular architectures that let them upgrade components piece‑by‑piece rather than a full replacement. Cloud‑based core banking, open‑banking APIs and AI‑driven automation are...