
G7 Sets 2034 Deadline for Finance to Adopt Quantum-Safe Systems
The G7 Cyber Expert Group has issued a recommended roadmap urging financial institutions and public entities to fully adopt post‑quantum cryptography by 2034. The plan outlines six phases—from awareness and inventory to migration, testing and validation—spanning 2025‑2035. While advisory, it stresses integrating the transition into existing risk‑management frameworks and maintaining cryptographic agility. The group also calls for cross‑jurisdictional collaboration to ensure interoperable, resilient security across the financial ecosystem.

New Research: 64% of 3rd-Party Applications Access Sensitive Data Without Justification
New research shows 64% of third‑party applications on websites access sensitive data without a clear business justification, up from 51% in 2024. Only 39% of security leaders have deployed dedicated web‑exposure solutions, despite 81% ranking web attacks as a top...

Microsoft Fixes Three Zero-Days on Busy Patch Tuesday
Microsoft released its latest Patch Tuesday update, fixing 114 CVEs including three critical zero‑day bugs. The zero‑days are CVE‑2026‑20805 (information disclosure in Desktop Window Manager), CVE‑2026‑21265 (secure‑boot certificate bypass), and CVE‑2023‑31096 (elevation of privilege in legacy Agere modem drivers). The...

Cybersecurity at the State and Local Level: Washington Has the Framework, It’s Time to Act
The March 2025 White House Executive Order calls on states, localities and tribal entities to own their cybersecurity preparedness, while the State and Local Cybersecurity Grant Program (SLCGP) allocates $1 billion over four years to fund those efforts. The bipartisan PILLAR...
%20(1).webp?ssl=1)
Spring CLI Vulnerability Allows Attackers to Execute Commands on User Systems
A command‑injection flaw (CVE‑2026‑22718) has been discovered in the Spring CLI VS Code extension, affecting all versions up to 0.9.0. The vulnerability allows an attacker with local access to execute arbitrary commands, earning a medium severity rating and a CVSS score...

Is It Time for Internet Services to Adopt Identity Verification?
Australia has enacted a law prohibiting anyone under 16 from holding a social‑media account, forcing platforms to purge non‑compliant profiles. The move positions the country as a global test case for age‑based bans and sparks a broader debate on mandatory...

Microsoft: Windows 365 Update Blocks Access to Cloud PC Sessions
Microsoft confirmed that a recent Windows 365 update is preventing users from signing into their Cloud PC sessions, causing widespread access failures that began on Tuesday at 19:00 UTC. The issue, tracked under incident WP1217671, stems from a security‑focused update that unintentionally broke...
.webp?ssl=1)
Multiple Elastic Vulnerabilities Could Lead to File Theft and DoS
Elastic has issued urgent patches for four critical Kibana vulnerabilities spanning versions 7.x through 9.2.3. The most severe, CVE‑2026‑0532, combines SSRF and file disclosure, allowing authenticated attackers to exfiltrate credentials. Three medium‑severity flaws can cause denial‑of‑service through resource exhaustion in...

Monroe University Says 2024 Data Breach Affects 320,000 People
Monroe University disclosed that a December 2024 cyberattack compromised personal, financial, and health data of more than 320,000 individuals. Attackers accessed the network for two weeks, from Dec 9 to Dec 23, before the breach was detected. The university began notifying affected...

AI in Manufacturing: The Growing Risk and Reward Dilemma Escalating Data Security
AI adoption in U.S. manufacturing is accelerating, with 55% of firms already using generative AI and many planning further expansion. Meanwhile, ransomware attacks on the sector surged 87% in 2024, making manufacturing the most targeted industry. Without enterprise‑grade security—especially through...

Scamnetic Delivers Fraud Protection Across All Payment Types
Scamnetic launched its patent‑pending IDeveryone Payment Protection solution, extending identity‑proofing to every payment channel—from push and digital payments to cryptocurrency, checks, wire transfers and ACH. The offering adds real‑time recipient verification and optional insurance, aiming to curb the $442 billion global...

Critical Node.js Vulnerability Can Cause Server Crashes via Async_hooks Stack Overflow
Node.js released security updates fixing a critical vulnerability (CVE‑2025‑59466) that causes the runtime to terminate with exit code 7 when a stack overflow occurs while async_hooks is enabled. The bug affects all versions from 8.x through 18.x and impacts major frameworks...

CISO Assistant: Open-Source Cybersecurity Management and GRC
CISO Assistant’s community edition is an open‑source governance, risk, and compliance (GRC) platform that lets security teams document assets, risks, controls, and framework alignment in a single, self‑hosted system. The tool ships with built‑in mappings to ISO 27001, NIST CSF, and...

US Cybersecurity Weakened by Congressional Delays Despite Plankey Renomination
The White House renominated seasoned cyber veteran Sean Plankey as CISA director after his initial nomination lapsed, but Senate holds tied to a Coast Guard issue and a pending telecom security report are delaying confirmation. Simultaneously, deep budget cuts have...
Firmware Scanning Time, Cost, and Where Teams Run EMBA
A new research paper compares the EMBA firmware analysis tool on a local workstation and an Azure virtual machine, measuring execution time, repeatability, and cost. Identical configurations and a common firmware set were used, revealing that scan duration depends more...

Nicole Ozer Joins CPPA to Drive Privacy and Digital Security Initiatives
California Privacy Protection Agency appointed Nicole Ozer to its board, reinforcing the state’s privacy agenda. Ozer, former ACLU tech director and executive at UC Law San Francisco, brings extensive experience in privacy law, AI, and digital civil liberties. Her appointment...

How AI Image Tools Can Be Tricked Into Making Political Propaganda
A new study shows that commercial text‑to‑image models can be coaxed into generating political propaganda by replacing explicit names with descriptive profiles and fragmenting prompts across multiple low‑risk languages. Researchers tested GPT‑4o, GPT‑5 and GPT‑5.1, achieving bypass rates up to...

Taiwan Endures Greater Cyber Pressure From China
Taiwan’s National Security Bureau reported an average of 2.63 million cyber attacks per day in 2025, a 6 percent rise from the prior year. Energy utilities faced a ten‑fold surge in malicious traffic while hospitals and emergency services saw attacks climb 54 percent....

Personal Details of Thousands of Border Patrol and ICE Agents Allegedly Leaked in Huge Data Breach
A whistleblower allegedly released personal data on roughly 4,500 ICE and Border Patrol employees, including about 2,000 frontline agents, after the Jan. 7 shooting of Renee Nicole Good. The leak, posted on the volunteer‑run ICE List site, contains names, work emails,...

AI Scraping in Mobile Apps: How It Works and How to Stop It
Scraping has migrated from web sites to mobile apps as AI‑driven bots target richer, structured API data. Attackers decompile Android APKs, extract endpoints and credentials, then replay authenticated requests without using the UI. Traditional defenses—rate limits, CAPTCHAs, and token‑based authentication—fail...

CISO Succession Crisis Highlights How Turnover Amplifies Security Risks
Chief Information Security Officers are facing unprecedented turnover, with average tenure now 18‑26 months. Rapid M&A activity forces CISOs to juggle integration, risk, board advising, and crisis management, leading to burnout and a 66% report of excessive expectations. Surveys show...

Ukraine's Army Targeted in New Charity-Themed Malware Campaign
Ukraine’s Defense Forces were hit by a charity‑themed malware campaign from October to December 2025 that delivered the PluggyApe backdoor. The attacks arrived via Signal or WhatsApp messages promising charitable documents, but instead provided password‑protected PIF archives containing malicious payloads. Ukrainian...

NY: Southold Laserfiche Access Remains Suspended After Cyberattack
Southold, New York, has kept its Laserfiche online record‑keeping system offline for more than six weeks after a cyberattack on Nov. 24 compromised its servers. The town announced that public access will remain suspended with no clear restoration timeline. To remediate,...

Central Maine Healthcare Breach Exposed Data of over 145,000 People
Central Maine Healthcare suffered a cyber intrusion that lasted from March 19 to June 1, 2024, exposing the personal and health information of 145,381 individuals. The breach affected patients, current and former employees, revealing names, dates of birth, treatment details,...

NDSS 2025 – A Comprehensive Memory Safety Analysis Of Bootloaders
Researchers at NDSS 2025 presented the first systematic memory‑safety study of bootloaders, revealing a growing attack surface as these low‑level programs add features. By surveying prior vulnerabilities and building a dedicated fuzzing framework, the team examined nine popular bootloaders and...

New Windows Updates Replace Expiring Secure Boot Certificates
Microsoft has begun automatically replacing expiring Secure Boot certificates on eligible Windows 11 24H2 and 25H2 devices. The certificates, which protect the pre‑boot environment, are set to expire in June 2026, prompting a phased rollout through Windows quality updates. High‑confidence devices receive the...

FortiOS Vulnerability Allows Remote Code Execution Without Login
Fortinet disclosed a heap‑based buffer overflow in the cw_acd daemon of FortiOS and FortiSwitchManager that allows unauthenticated remote code execution. The flaw can be triggered via crafted network requests, especially on exposed fabric interfaces, and affects versions from 6.4.17 up...

Man to Plead Guilty to Hacking US Supreme Court Filing System
Nicholas Moore, a 24‑year‑old from Springfield, Tennessee, is set to plead guilty to unauthorized access of the U.S. Supreme Court’s electronic filing system on 25 separate days between August and October 2023. Prosecutors allege he obtained information from a protected...

Windows 11 KB5074109 & KB5073455 Cumulative Updates Released
Microsoft released the Windows 11 KB5074109 and KB5073455 cumulative updates for 25H2/24H2 and 23H2, delivering the January 2026 Patch Tuesday security patches. The updates raise build numbers to 26200.7623 (or 26100.7462) and 226x1.6050, and they address a range of vulnerabilities, driver compatibility,...

Microsoft January 2026 Patch Tuesday Fixes 3 Zero-Days, 114 Flaws
Microsoft released its January 2026 Patch Tuesday update, addressing 114 security flaws across Windows and related services. The bundle includes eight critical vulnerabilities—six remote code execution and two elevation‑of‑privilege bugs—plus one actively exploited information‑disclosure flaw in Desktop Window Manager. Two publicly...

What Is a DNS Attack? Understanding the Risks and Threats
The Domain Name System (DNS) remains a critical yet vulnerable internet backbone, with 88% of organizations reporting at least one DNS attack in 2023. Attacks such as hijacking, cache poisoning, and DDoS floods can redirect users, cause service outages, and...

After Goldman, JPMorgan Discloses Law Firm Data Breach
JPMorgan Chase disclosed to the Maine Attorney General that a data breach at law firm Fried Frank exposed personal information of 659 investors in a private‑equity fund. The breach involved unauthorized copying of files containing names, contact details, account numbers,...

Identity Under Siege: What the Salt Typhoon Campaign Reveals About Trusted Access Risks
The Salt Typhoon espionage campaign compromised email accounts of U.S. congressional staff by exploiting stolen credentials rather than deploying malware. Attackers blended into normal email and cloud traffic, maintaining persistent, low‑noise access to sensitive communications. The breach underscores that identity systems...

GitGuardian Closes 2025 with Strong Enterprise Momentum, Protecting Millions of Developers Worldwide
GitGuardian reported record ARR growth in 2025, fueled by rapid enterprise adoption across North America and Europe. The platform now safeguards over 115,000 developers, monitors more than 610,000 repositories and 210,000 collaboration‑tool sources, a seven‑fold increase from the prior year....

Convincing LinkedIn Comment-Reply Tactic Used in New Phishing
Scammers are posting fake LinkedIn reply comments that mimic official policy‑violation notices and direct users to malicious links. The fraudsters leverage LinkedIn’s own lnkd.in URL shortener, making the phishing URLs appear legitimate. Impersonated company pages also use the LinkedIn logo...

Antwerp’s AZ Monica Hospital Hit by Cyber Attack
AZ Monica hospital in Antwerp suffered a cyber attack on Tuesday, forcing a shutdown of computer systems at its Deurne and Harmonie campuses. The breach was detected at 6:30 am, prompting staff to power down servers and initiate an investigation by...

When the Marketing Graph Becomes the Target Map
A Wired investigation uncovered that Google’s ad service hosted audience segments tied to highly sensitive groups, allowing marketers and potential adversaries to target mobile devices linked to government employees and executives. The article warns that modern ad‑tech pipelines collect granular...

F5 NGINXaaS for Google Cloud Protects Cloud-Native Applications
F5 has introduced F5 NGINXaaS for Google Cloud, a managed, cloud‑native application delivery‑as‑a‑service that unifies load balancing, security and observability. Developed with Google Cloud, the service is available through the Marketplace and targets containerized, AI‑enabled workloads. It offers programmable traffic...

Widespread Magecart Campaign Targets Users of All Major Credit Cards
Silent Push researchers have uncovered a global Magecart campaign that has been skimming credit‑card data from all major networks since 2022. The attackers host malicious JavaScript on innocuous domains such as cdn‑cookie.com and erase the code when a WordPress admin bar...

Concentric AI Releases Private Scan Manager for AWS GovCloud (US)
Concentric AI has added Private Scan Manager support for AWS GovCloud (US), allowing federal agencies, contractors, and partners to run its Semantic Intelligence platform within isolated, U.S.-only cloud regions. The extension follows earlier 2025 announcements of private‑cloud scanning for Azure...
![[Webinar] Securing Agentic AI: From MCPs and Tool Access to Shadow API Key Sprawl](/cdn-cgi/image/width=1200,quality=75,format=auto,fit=cover/https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEi2N9qZuwkcslheNUOsWaTDrMYeXiBUfw1y-hItTvuGo71srarOm7AWzq3o7ro9E0x_CnC7XmJGXKl1tfkc6gTMK288y6M_zN6Yg1FATduXSQmMlp_jnHESxVYZDuJnNozO_Ff-r-lWIyG5AikC8AwrOckeYVYcCQv2RjeLof2bxV_TrcbvRvZqrTIcjD0/s2600/ai-agent.jpg)
[Webinar] Securing Agentic AI: From MCPs and Tool Access to Shadow API Key Sprawl
The Hacker News webinar spotlights the emerging security gap as agentic AI tools like Copilot, Claude Code, and Codex move from code generation to full‑cycle software deployment. Central to the risk are Machine Control Protocols (MCPs), which dictate which tools,...

PowerShell-Driven Multi-Stage Windows Malware Using Text Payloads
Researchers have uncovered the SHADOW#REACTOR campaign, a multi‑stage Windows malware chain that starts with an obfuscated VBS script and escalates through a PowerShell stager, text‑only payloads, and a .NET Reactor‑protected loader. The loader reflectively injects a Remcos RAT payload entirely...
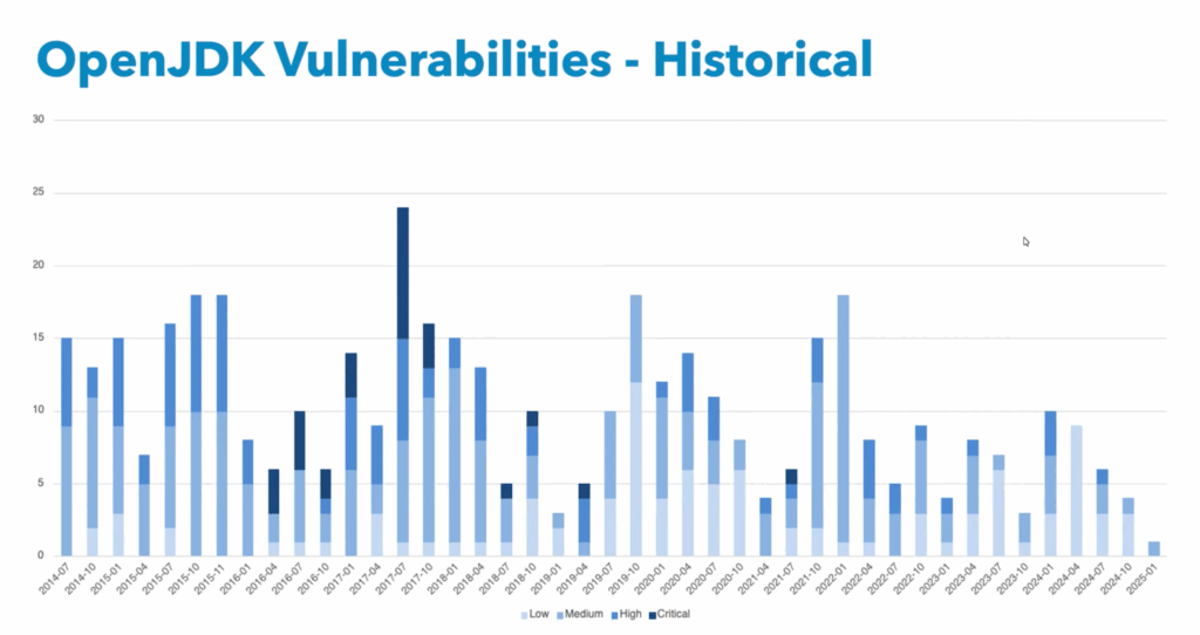
Can You Afford the Total Cost of Free Java?
Running Java on a free, unsupported JVM carries hidden risks as exploit timelines have accelerated dramatically. In 2023, attackers began leveraging newly disclosed Java flaws within five days, and some incidents occurred in under an hour. Without commercial support, organizations...

BodySnatcher (CVE-2025-12420): A Broken Authentication and Agentic Hijacking Vulnerability in ServiceNow
ServiceNow’s Virtual Agent API and Now Assist AI Agents contain a critical broken‑authentication flaw (CVE‑2025‑12420) that lets unauthenticated attackers impersonate any user using only an email address. The vulnerability exploits a static provider secret and email‑only auto‑linking to bypass MFA...

HoneyTrap: Outsmarting Jailbreak Attacks on Large Language Models
Researchers from Shanghai Jiao Tong University, UIUC and Zhejiang University introduced HoneyTrap, a deceptive‑defense framework that counters multi‑turn jailbreak attacks on large language models. The system employs four specialized defensive agents to mislead attackers, prolong interactions, and drain computational resources...

Armenia Probes Alleged Sale of 8 Million Government Records on Hacker Forum
Armenian authorities have launched a probe after a hacker identified as dk0m claimed to be selling eight million government records on a dark‑web forum. The data allegedly originates from a state notification system that distributes legal and administrative notices. Officials...

Massive Cyberattack on Polish Power System in December Failed, Minister Says
Poland’s power grid endured its biggest cyberattack in years during the last week of December, according to Energy Minister Milosz Motyka. The operation attempted to sever communication links between renewable energy installations and distribution operators, but was ultimately thwarted with...

Noction Adds Automatic Anomaly Detection to IRP v4.3 for Faster DDoS Mitigation
Noction launched Intelligent Routing Platform (IRP) v4.3, adding Automatic Anomaly Detection (AAD) that spots abnormal traffic and triggers edge‑level DDoS mitigation. The system can automatically apply BGP FlowSpec filters or blackhole traffic, with optional operator review. IRP v4.3 also upgrades Commit Control...
Android Banking Malware deVixor Actively Targeting Users with Ransomware Capabilities.
Android banking trojan deVixor, active since October 2025, is distributing through counterfeit automotive‑sale websites targeting Iranian users. The malware harvests SMS OTPs, banking credentials, and cryptocurrency exchange data, and can remotely lock devices with a ransomware command demanding 50 TRX. Its...

Q4 2025 Malware Trends: Telegram Backdoor, Banking Trojans Surge, Joker Returns to Google Play
Doctor Web’s Q4 2025 mobile‑malware report reveals a modified Telegram X app delivering the Android.Backdoor.Baohuo.1.origin backdoor, compromising roughly 58,000 Android devices across phones, tablets, smart TVs and in‑car systems. The same period saw a 65% surge in Android banking trojans and the re‑appearance...