
Years-Old Vulnerable Apache Struts 2 Versions See 387K Weekly Downloads
Sonatype researchers reported that over 387,000 downloads of Apache Struts 2 occurred in a single week, and 98% of those were for end‑of‑life versions vulnerable to CVE‑2025‑68493. The flaw, a high‑severity (8.8) unsafe XML parsing issue affecting versions 2.0.0 through 6.1.0, was identified by the autonomous AI system Zast AI. Exploitation can trigger infinite loops that exhaust CPU and memory, effectively crashing web servers. Only about 1.8% of the downloads were for the patched Struts 6.1.1 release.

4 Outdated Habits Destroying Your SOC's MTTR in 2026
Many security operations centers still rely on outdated, manual processes that slow incident response. The article highlights four habits—manual sample review, sole reliance on static scans, fragmented toolsets, and excessive alert escalations—that inflate mean time to respond. It shows how...

Trio of Critical Bugs Spotted in Delta Industrial PLCs
Researchers from OPSWAT’s Unit 515 uncovered four serious flaws in Delta Electronics’ DVP‑12SE11T programmable logic controller, including three critical CVSS 9+ vulnerabilities. Delta issued a firmware patch just before the 2026 New Year, but many OT environments may delay updates due to...

FTC Bans GM From Selling Drivers' Location Data for Five Years
The U.S. Federal Trade Commission finalized an order against General Motors and its OnStar subsidiary for collecting and selling precise geolocation and driver‑behavior data without consent. The settlement bans GM from sharing such data with consumer reporting agencies for five...

Guarding Europe’s Hidden Lifelines: How AI Could Protect Subsea Infrastructure
The episode explores how AI can safeguard Europe’s extensive subsea cables and pipelines, focusing on the EU‑funded VIGIMARE project led by researcher Johanna Karvonen. It details how machine‑learning models will fuse satellite imagery, AIS data, radar and acoustic signals from...

Cyb3r Operations Raises $5.4M in Financing
London‑based Cyb3r Operations secured $5.4 million in a financing round led by Octopus Ventures, bringing its total capital to $6.75 million after a follow‑on from Pi Labs. The startup provides continuous, automated third‑party cyber risk visibility across tech stacks, flagging vulnerabilities, sanctions,...

AWS Flips Switch on Euro Cloud as Customers Fret About Digital Sovereignty
Amazon Web Services launched its European Sovereign Cloud to general availability, promising a fully EU‑located environment that is physically and logically separate from other AWS regions. The offering initially includes 90 services spanning compute, storage, networking, security, and AI, and...

Bitwarden Advances Passkeys and Credential Risk Controls
Bitwarden unveiled Access Intelligence, delivering application‑level visibility into weak, reused or exposed credentials and guiding remediation, cutting average resolution time from nine days. The company also expanded passkey support, adding native Windows 11 integration, cross‑platform portability via the FIDO Credential Exchange...

Arcjet Python SDK Sinks Teeth Into Application-Layer Security
Arcjet has released a Python SDK that brings its application‑layer security platform directly into Python services and APIs. The SDK provides built‑in bot protection, rate limiting, email validation and signup spam prevention, and works with both FastAPI and Flask with...

F5 Targets AI Runtime Risk with New Guardrails and Adversarial Testing Tools
F5 announced the general availability of two AI‑runtime security products—F5 AI Guardrails and F5 AI Red Team. The Guardrails solution provides model‑agnostic, real‑time protection for AI agents, while the Red Team offers automated adversarial testing using a continuously updated threat...

ICS Patch Tuesday: Vulnerabilities Fixed by Siemens, Schneider, Aveva, Phoenix Contact
Industrial control system vendors Siemens, Schneider Electric, Phoenix Contact and Aveva issued a dozen Patch Tuesday advisories on Jan. 15, 2026, addressing critical and high‑severity flaws across edge devices, process automation platforms, routers and optimization software. Siemens released five advisories,...

Palo Alto Networks Warns of DoS Bug Letting Hackers Disable Firewalls
Palo Alto Networks disclosed a high‑severity flaw, CVE‑2026‑0227, that lets unauthenticated attackers trigger a denial‑of‑service condition on PAN‑OS firewalls and Prisma Access gateways when GlobalProtect is enabled. The bug forces the appliance into maintenance mode, effectively disabling protection. Palo Alto...

Asimily Extends Cisco ISE Integration to Turn Device Risk Into Segmentation Policy
Asimily announced new microsegmentation capabilities that add Security Group Access Control List (SGACL) support to Cisco Identity Services Engine (ISE). The integration lets organizations automatically translate device classification, behavior analysis, and risk scores into enforceable segmentation policies. By extending its...

DeFi Quietly Breaks up with Discord as Scams Overwhelm Public Channels
DeFi protocols are pulling back from public Discord servers as scam activity overwhelms community channels. Morpho announced its Discord is now read‑only and redirected users to ticket‑based tools like Intercom, while data platform DefiLlama is shifting to live chat and...

Modern Executive Protection: Digital Exposure & Physical Risk
Executive protection is expanding beyond physical guards to include digital exposure analysis. Executives and their households generate extensive online footprints that adversaries exploit to shape targeting before any physical action. The article argues that most security teams have abundant data...

Microsoft Shuts Down RedVDS Cybercrime Subscription Service Tied to Millions in Fraud Losses
Microsoft announced a coordinated legal operation in the United States and United Kingdom, backed by Europol and German authorities, to dismantle RedVDS, a subscription‑based cybercrime platform. Since March 2025, RedVDS has enabled fraudsters to rent disposable virtual machines for $24...

From Typos to Takeovers: Inside the Industrialization of Npm Supply Chain Attacks
The npm ecosystem has moved from simple typosquatting to coordinated credential‑driven attacks that compromise maintainers and CI/CD pipelines. Attackers now hijack trusted packages, inject malicious post‑install scripts, and use stolen tokens as a "master key" to reach millions of downstream...

Cyb3r Operations Raises £4M to Address Third-Party Risk Blind Spots
London‑based Cyb3r Operations secured £4 million in a round led by Octopus Ventures, bringing its total funding to £5 million. The capital will accelerate its platform that delivers continuous, automated visibility into third‑party cyber risk for large enterprises. As SaaS, cloud and...

New Cloudflare Report Warns of a ‘Technical Glass Ceiling’ Stifling AI Growth and Weakening Cybersecurity
Cloudflare’s inaugural 2026 App Innovation Report finds that organizations that modernize their application stacks are three times more likely to realize tangible AI returns, while legacy‑bound firms face heightened security exposure. The study shows 93% of leaders credit software updates...

LinkedIn Wants to Make Verification a Portable Trust Signal
LinkedIn is launching a self‑serve API that lets its Verified on LinkedIn badge be displayed on third‑party platforms, turning the verification badge into a portable trust signal. The company reports that 75 members verify each minute, now exceeding 100 million verified...

GoLogin vs MultiLogin vs VMLogin – What’s the Anti-Detect Browsers Difference?
Anti-detect browsers let users conceal fingerprints and manage multiple online identities. The article compares three leading solutions—GoLogin, MultiLogin, and VMLogin—detailing their core features, user bases, and pricing models. GoLogin distinguishes itself with cloud‑based profile storage, multilingual support, and a seven‑day...

QR Codes Are Getting Colorful, Fancy, and Dangerous
QR codes have evolved from plain black‑and‑white squares to colorful, logo‑embedded designs, making them a popular yet risky communication channel. Researchers at Deakin University identified a surge in "quishing" attacks that exploit these stylized codes to bypass traditional URL‑based security...

How the OWASP Application Security Verification Standard Helps Improve Software Security
Centraleyes recently integrated the OWASP Application Security Verification Standard (ASVS) into its cyber‑risk platform, enabling structured, repeatable assessments for web and cloud services. ASVS defines three verification levels—opportunistic, standard, and advanced—allowing organizations to match security controls to application risk. The...

Cybersecurity Spending Keeps Rising, so Why Is Business Impact Still Hard to Explain?
Cybersecurity budgets are set to increase again, yet security leaders still struggle to demonstrate clear business value. Finance executives express uneven trust in security teams’ ability to translate risk mitigation into financial outcomes, creating friction in budget approvals. Divergent definitions...

The NSA Lays Out the First Steps for Zero Trust Adoption
The National Security Agency has published the first two documents in its Zero Trust Implementation Guidelines series—a Primer and a Discovery Phase guide. The Primer explains the structure and principles of the series, while the Discovery Phase directs organizations to...

Microsoft, Law Enforcement Disrupt RedVDS Global Cybercrime Service
Microsoft and international law‑enforcement agencies, including Europol, dismantled RedVDS, a cybercrime‑as‑a‑service platform that has stolen roughly $40 million since March 2025. The operation seized the service’s marketplace, customer portal, and associated domains, cutting off access to cheap virtual dedicated servers rented for...

Depthfirst Secures $40M to Expand Agentic Approach to Software Security
Depthfirst Inc. announced a $40 million Series A round led by Accel to accelerate its AI‑native security platform. The startup’s General Security Intelligence platform deploys custom AI agents that continuously analyze code, infrastructure and workflows, delivering context‑aware vulnerability detection. In its first...

Aikido Security Raises $60M Series B at $1B Valuation to Unify Application Security
Belgian cybersecurity firm Aikido Security announced a $60 million Series B round that values the company at $1 billion, making it Europe’s fastest unicorn in the sector. The funding will accelerate its unified application security platform, which combines static and dynamic testing, software...

How to Build a Stateless, Secure, and Asynchronous MCP-Style Protocol for Scalable Agent Workflows
The tutorial demonstrates how to construct a Minimal Communication Protocol (MCP) that is stateless, cryptographically signed, and capable of handling asynchronous, long‑running tasks. Using Python, Pydantic models enforce strict schema validation for every request and response, while HMAC signatures guarantee...

Project Eleven Scores $20M Series A
Project Eleven, a post‑quantum security and digital‑asset migration startup, announced a $20 million Series A financing round. The round was led by Castle Island Ventures and included investors such as Coinbase Ventures, Balaji Srinivasan, Fin Capital, Variant, and several other venture funds....

Secure Your Spot at RSAC 2026 Conference
The RSA Conference (RSAC) will convene cybersecurity leaders in San Francisco from March 23‑26, 2026, offering a platform to explore emerging strategies and bold technologies. Simultaneously, GISEC GLOBAL 2026 will gather CISOs, government officials, and ethical hackers across the Middle East and Africa...

NDSS 2025 – PolicyPulse:Precision Semantic Role Extraction For Enhanced Privacy Policy Comprehension
Researchers from the University of Denver introduced PolicyPulse, an information‑extraction pipeline that converts natural‑language privacy policies into structured, machine‑readable formats. The system combines a specialized XLNet classifier with a BERT‑based semantic role labeler, processing sentences to preserve predicate‑argument relationships. Trained...

Iran’s Partial Internet Shutdown May Be a Windfall for Cybersecurity Intel
Iran’s near‑total internet blackout, begun Jan 8, has stripped millions of residential users offline, leaving only government‑controlled networks visible. Cybersecurity analysts say this creates a rare window to fingerprint Iranian state‑linked IPs and map their digital infrastructure. Vendors like Whisper Security...
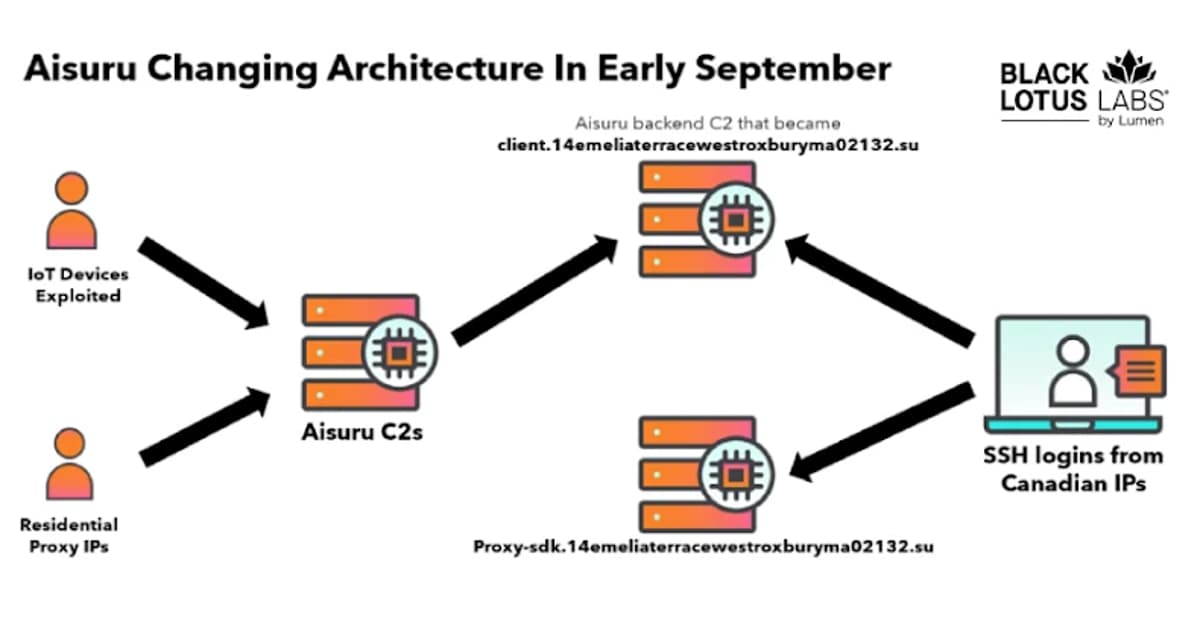
Researchers Null-Route Over 550 Kimwolf and Aisuru Botnet Command Servers
Black Lotus Labs at Lumen Technologies announced that it has null‑routed traffic to more than 550 command‑and‑control nodes used by the AISURU/Kimwolf botnet since early October 2025. The botnet now controls over two million Android devices, primarily unsecured TV boxes, and...

Structure and Reliability in E-Commerce Platforms
E‑commerce platforms depend on a robust technical foundation that goes beyond aesthetics. Scalability, security, speed, and continuous uptime are essential to handle traffic spikes, protect customer data, and maintain conversion rates. Managed hosting and automated backups simplify maintenance while platform‑specific...

From Backup to Business Resilience: Inside Cognizant and Rubrik’s New BRaaS Model
Cognizant and Rubrik have launched a Business Resilience as a Service (BRaaS) platform that merges Rubrik’s cyber‑resilience technology with Cognizant’s delivery expertise. The service addresses modern threats such as ransomware, cloud‑infrastructure attacks, and AI‑driven disruptions by providing unified data protection,...

Microsoft Updates Windows DLL that Triggered Security Alerts
Microsoft released a service alert confirming that the WinSqlite3.dll library, a core Windows component, was mistakenly flagged by third‑party security tools as vulnerable to CVE‑2025‑6965. The false‑positive affected Windows 10, Windows 11, and Windows Server 2012‑2025 systems for several months. Microsoft updated...

US Cargo Tech Company Publicly Exposed Its Shipping Systems and Customer Data to the Web
Bluspark Global, a U.S. shipping‑tech firm behind the Bluvoyix platform, left its API and customer data exposed to the public internet. Researchers discovered unauthenticated endpoints, plaintext passwords, and the ability to create admin accounts, granting access to decades‑old shipment records....

From Bot Noise to Real Insights: How Jobrapido Achieved True Marketing ROI
Jobrapido, a global recruitment‑marketing platform, partnered with DataDome to combat bot‑driven traffic that was inflating costs and skewing performance metrics. The AI‑powered solution filtered out roughly 15% of invalid visits, giving the company a clean, real‑time view of genuine user...

RedVDS Cybercrime Service Disrupted by Microsoft and Law Enforcement
Microsoft announced a joint operation with international law enforcement to dismantle RedVDS, a cybercrime‑as‑a‑service platform that provides disposable Windows VMs for phishing, BEC and financial fraud. Launched in 2019, RedVDS charged as little as $24 per month and is tied...

Hacker Claims Full Breach of Russia’s Max Messenger, Threatens Public Leak
A hacker using the alias CamelliaBtw posted on DarkForums claiming a full breach of Russia’s Max Messenger, exfiltrating roughly 142 GB of data that includes 15.4 million user records, authentication tokens, passwords, communication metadata, source code, and internal infrastructure assets. The alleged...

AppOmni Surfaces BodySnatcher AI Agent Security Flaw Affecting ServiceNow Apps
AppOmni, a SaaS security platform vendor, has disclosed a critical vulnerability in ServiceNow identified as CVE‑2025‑12420, nicknamed BodySnatcher. The flaw enables an unauthenticated attacker to impersonate any ServiceNow user and spawn a malicious AI agent within the platform. Because ServiceNow...

Webinar: Beyond the Quadrant: An Analyst’s Guide to Evaluating Email Security in 2026
Former Gartner analyst Ravisha Chugh and Abnormal’s Director of Product Marketing Lane Billings will host a webinar on January 20 2026, revealing how email‑security vendors will be evaluated in 2026. The session outlines Gartner’s evaluation criteria, essential vendor questions, red‑flags, and a proven shortlisting...

Survey: Rapid AI Adoption Causes Major Cyber Risk Visibility Gaps
Panorays’ survey of 200 U.S. CISOs reveals that 60% consider AI vendors uniquely risky, yet only 22% have formal vetting processes. The rapid rollout of chat‑bots and AI agents is outpacing traditional third‑party risk controls, leaving most organizations with limited...

Predator Spyware Turns Failed Attacks Into Intelligence for Future Exploits
New research by Jamf uncovers that the Predator spyware, sold by Intellexa, includes a self‑diagnostic system that reports detailed error codes when attacks fail. These codes convey why deployments were aborted—such as detection of developer mode, proxies, or analysis tools—allowing...
Reprompt Attack Let Hackers Hijack Microsoft Copilot Sessions
Researchers at Varonis uncovered a “Reprompt” attack that lets hackers hijack Microsoft Copilot Personal sessions by embedding malicious prompts in the URL’s `q` parameter. After a victim clicks a crafted link, the attacker can issue follow‑up commands that bypass Copilot’s...

EasyDMARC Expands Executive Team with Armen Najarian as Chief Commercial Officer
EasyDMARC announced the appointment of Armen Najarian as its new Chief Commercial Officer. Najarian brings over 25 years of experience in email security, fraud prevention, and AI‑driven analytics, previously leading go‑to‑market roles at ThreatMetrix, Agari, Outseer and Sift. He will...

Data Protection Agency Tells Coupang to Stop Publishing Unconfirmed Information About Data Breach
South Korea’s Personal Information Protection Commission (PIPC) has ordered e‑commerce giant Coupang to stop publishing its own findings about a recent data breach that exposed personal information of millions of users. The regulator warned that unverified disclosures could mislead consumers...

Eurail Passengers Taken for a Ride as Data Breach Spills Passports, Bank Details
Eurail confirmed a data breach that exposed personal information of customers, particularly those who received passes through the EU‑funded DiscoverEU programme. The breach potentially includes passport numbers, issuance details, and bank information, though direct‑purchase customers’ passports were not stored visually....

Airia Adds AI Governance for Compliance, Accountability, and Control
Airia has launched an AI Governance product, completing its three‑pillar enterprise AI management ecosystem alongside AI Security and Agent Orchestration. The new suite offers a governance dashboard, model and agent registries, compliance automation, and risk assessment tools to provide end‑to‑end...