
Baidam Partners with AUSCERT for Cyber Security Collab
Baidam has signed a 12‑month memorandum of understanding with the University of Queensland’s not‑for‑profit AUSCERT to strengthen Australia’s cyber security ecosystem. The partnership will focus on five pillars: cyber threat intelligence, incident response, phishing takedowns, security capability training for technical, risk and executive roles, and joint events. By combining AUSCERT’s intelligence and awareness programs with Baidam’s response expertise, the alliance aims to boost national resilience while delivering social and financial returns for First Nations peoples. The deal builds on a relationship that began in 2019 and follows Baidam’s recent MoU with Indigenous‑owned Deadly Coders.

GitLab Dedicated for Government Now GovRAMP-Authorized
GitLab announced that its Dedicated for Government offering has earned GovRAMP authorization, clearing a major procurement hurdle for state and local agencies. The single‑tenant SaaS solution provides U.S.‑only data residency, isolated infrastructure, and private networking to satisfy stringent compliance rules....

New Windows 'MiniPlasma' Zero-Day Exploit Gives SYSTEM Access, PoC Released
Researcher Chaotic Eclipse released a proof‑of‑concept for the MiniPlasma zero‑day, which escalates privileges to SYSTEM on fully patched Windows 11 systems. The exploit targets the cldflt.sys Cloud Filter driver and its HsmOsBlockPlaceholderAccess routine, a flaw originally reported as CVE‑2020‑17103 and supposedly...

Estia Health Drives Zero Trust Security Overhaul
Estia Health, Australia’s second‑largest aged‑care provider, is overhauling its security with a Zero Trust model to protect sensitive resident data. The initiative centers on three pillars—identity, data, and endpoints—leveraging Okta single sign‑on, AI‑driven data classification, and strict device controls. With...

Sysadmin Creates 'ModuleJail' To Automatically Blacklist Unused Kernel Modules
Belgian sysadmin Jasper Nuyens released ModuleJail, a GPL‑v3 shell script that scans Linux hosts and automatically blacklists kernel modules that are not in use. The tool creates a single modprobe blacklist file, preserving essential modules while disabling obscure ones that...
"Private DNS" Isn't as Private as You Think
Private DNS, typically implemented via DNS‑over‑TLS or DNS‑over‑HTTPS, encrypts only the DNS query itself. While it prevents ISPs and local Wi‑Fi from reading those lookups, the ISP still sees the destination IP and the hostname in the TLS SNI field,...

The Hidden Cost of Slow Cyber Remediation in Healthcare
Healthcare ransomware incidents are rising as hospitals struggle with slow vulnerability remediation. Nearly 90% of organizations run exploitable systems, and compliance timelines lag behind attacker speed. Governance layers, manual approvals, and siloed ownership extend exposure windows, prompting insurers and regulators...

Voice AI Systems Are Vulnerable to Hidden Audio Attacks
Researchers unveiled AudioHijack, an adversarial technique that embeds inaudible commands in audio clips to hijack large audio‑language models (LALMs). Tested on 13 open and commercial models—including Microsoft’s service—the method achieved 79‑96% success, forcing models to conduct web searches, download files,...

The Role of Zero-Knowledge Technology in Web2 Security
The article highlights how traditional Web2 security models, exemplified by the 2025 Salesforce OAuth token breach, expose massive data stores to attackers. It proposes zero‑knowledge (ZK) cryptography as a structural remedy, allowing verification without revealing raw data. Two ZK approaches...

Anonymous Nigeria Attacks South Africa
Nullsec Nigeria, also known as Anonymous Nigeria, announced it breached the South African Department of Correctional Services and threatened to leak roughly 11 GB of sensitive data unless xenophobic attacks on Nigerians cease. The group also claimed responsibility for hacking the...
NGINX CVE-2026-42945 Exploited in the Wild, Causing Worker Crashes and Possible RCE
A heap‑buffer overflow in NGINX’s rewrite module (CVE‑2026‑42945) has been actively exploited just days after disclosure, allowing unauthenticated attackers to crash worker processes and, on systems with ASLR disabled, execute remote code. The flaw spans NGINX versions 0.6.27 through 1.30.0...
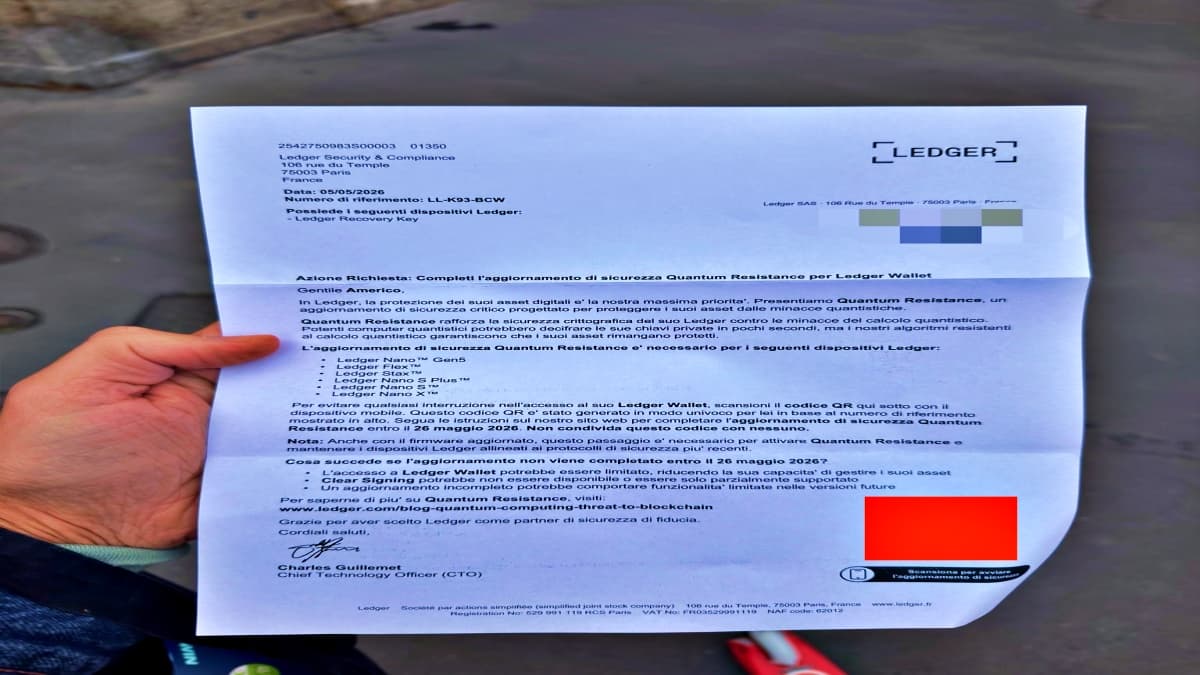
Scammers Send Physical Phishing Letters to Steal Ledger Wallet Seed Phrases
Scammers are sending forged Ledger‑branded letters that include QR codes to trick hardware‑wallet owners into revealing their 24‑word seed phrases. The campaign is localized, with versions in Italian and other languages, indicating attackers may have accessed customer shipping data from...

Grafana Says It Rejected Ransom Demand After Source Code Theft
Grafana Labs reported that a threat actor accessed its GitHub repository using a compromised token, downloading parts of the company’s open‑source codebase. The investigation found no evidence of customer data exposure or impact on client systems. Grafana publicly refused the...

OCR Studio Expands KYC Fraud Detection for AI-Generated Identity Documents
OCR Studio has upgraded its document‑verification platform with an anti‑fraud engine that can spot AI‑generated and morphed identity documents, including forgeries created by tools such as ChatGPT, Midjourney, Grok and NanoBanana. The technology examines the underlying image structure to detect...

Cybersecurity Experts Warn: This Common Email Habit Is a Gift to Hackers
Cybersecurity experts warn that using an email address as the sole username and relying on one‑click logins creates a single point of failure. If a hacker gains access to that inbox, they can reset passwords, intercept verification codes, and hijack...

The Mythos Stress Test: Can Indian Fintechs, Banks Fend Off AI-Native Cyber Threats?
Anthropic’s Mythos AI model has demonstrated the ability to autonomously uncover long‑standing software vulnerabilities, prompting alarm across the global security community. In India, the finance ministry convened senior bank leaders after Mythos’ release, forming a panel headed by SBI chairman...

FCA, Bank of England and Treasury Joint Statement on Frontier AI Models and Cyber Resilience
The FCA, Bank of England and Treasury issued a joint statement warning that frontier AI models are already capable of automating cyber attacks at scale, creating new threats to the safety and soundness of UK financial firms. Regulators outlined five...

The Cyber Resilience Standard Every Hospital CIO Must Meet
Hospital CIOs now face a minimum standard to deliver safe patient care for at least 30 days without core technology, driven by the Joint Commission and American Hospital Association's Cyber Resilience Readiness (CRR) program. The average healthcare breach costs $7.42 million,...

World Bank, African DPAs Outline Formula for Trusted Digital Identity, DPI
At the ID4Africa 2026 AGM, the World Bank warned that trust is the linchpin of digital public infrastructure. It highlighted six technical and governance risks that have undermined Kenya, India, Uganda and other nations’ digital ID programs. A panel of...

AI Could Steal Fingerprints From High-Resolution Selfies, Experts Warn
Experts warn that modern smartphone cameras can capture enough ridge detail in high‑resolution selfies to reconstruct fingerprints, reviving concerns about biometric security. Recent reports from China suggest images taken from about five feet away, especially with the popular peace‑hand gesture,...

Common Azure Privilege Escalation Paths Attackers Exploit
Azure privilege escalation typically follows a chain of modest misconfigurations rather than a single dramatic exploit. Attackers often start with a user who owns an application registration, add a client secret, and leverage the app’s permissions to read directory data...

ESET Details New Ghostwriter Activity Targeting Ukrainian Government
ESET researchers have identified a new Ghostwriter (FrostyNeighbor) campaign targeting Ukrainian government agencies, active since March 2026. The operation begins with a spear‑phishing PDF masquerading as an Ukrtelecom notice, using geofencing to deliver a decoy to non‑Ukrainian IPs and a malicious...

Android 16 Bug Allows Apps to Ignore VPNs and Leak IP Addresses
A newly disclosed vulnerability in Android 16’s ConnectivityManager lets malicious apps bypass VPN tunnels and expose the device’s real IP address. The bug, reported through Google’s Vulnerability Reward Program, was deemed “infeasible” to fix by Google’s security team, leaving it...

Did Iran Hack Tank Readers at US Gas Stations? Security Leaders Discuss
U.S. officials suspect Iranian hackers breached unsecured automatic tank gauge (ATG) systems at gas stations, altering fuel‑level displays without affecting actual storage. The intrusion, reported by CNN, highlighted that the ATG devices were online without password protection, enabling remote manipulation....

Exchange Server Zero-Day Vulnerability Can Be Triggered by Opening a Malicious Email
Microsoft disclosed a zero‑day cross‑site scripting vulnerability (CVE‑2026‑42897) in on‑premises Exchange Server 2016, 2019 and Server Subscription Edition that can be exploited by simply opening a crafted email in Outlook Web Access. The flaw is already being used in the...

AI Agents Show They Can Create Exploits, Not Just Find Vulns
Researchers from leading universities and AI firms introduced ExploitGym, a benchmark that evaluates whether frontier AI agents can turn software bugs into functional exploits. The suite contains 898 real‑world vulnerabilities from Google’s V8 engine and the Linux kernel. In two‑hour...

Funnel Builder WordPress Plugin Bug Exploited to Steal Credit Cards
A critical, unauthenticated vulnerability in FunnelKit's Funnel Builder WordPress plugin is being actively exploited to inject malicious JavaScript into WooCommerce checkout pages. The flaw, affecting all versions prior to 3.15.0.3, lets attackers add a skimmer script that steals credit‑card numbers,...

A Hotel Check-In System Left a Million Passports and Driver’s Licenses Open for Anyone to See
A misconfigured Amazon S3 bucket used by Tabiq, the hotel check‑in platform from Japan’s startup Reqrea, exposed over 1 million passports, driver’s licenses and selfie verification photos to the public web. Security researcher Anurag Sen discovered the open bucket and alerted...

For May, Patch Tuesday Means 139 Updates — but No Zero-Days
Microsoft’s May 2026 Patch Tuesday released 139 updates covering Windows, Office, .NET and SQL Server, but no zero‑day exploits. The rollout includes three unauthenticated remote‑code‑execution flaws in Netlogon, DNS Client and a SSO plugin, plus four Word Preview Pane RCEs...

How AI Adoption Is Driving Investment Into Cybersecurity Basics: Blackwood Execs
Blackwood executives say the rush to adopt AI is prompting organizations to double‑down on core cybersecurity fundamentals such as endpoint visibility, identity security, and data protection. As AI agents integrate deeper into corporate IT environments, traditional security gaps become more...

Lombard Joins LayerZero Exodus as $4 Billion in Assets Switch to Chainlink's Bridge
Lombard, a DeFi protocol that issues bitcoin‑backed tokens, announced it will move more than $1 billion in assets from LayerZero to Chainlink’s Cross‑Chain Interoperability Protocol (CCIP). The migration follows a broader exodus of roughly $4 billion in crypto assets shifting to Chainlink...

MSPs Need AI to Fight AI-Fueled Cyberthreats: Guardz
Guardz’s latest research shows AI is turbo‑charging cyberattacks on small and midsize businesses, letting threat actors exploit classic weaknesses—identity gaps, weak authentication, and cloud misconfigurations—at unprecedented speed. Over a six‑month window, nearly nine‑in‑ten SMBs experienced at least one credential compromise,...
Critical Infrastructure Under Siege
A joint advisory from six U.S. federal agencies on April 7, 2026 warns that Iranian‑linked actors, operating as CyberAv3ngers, are actively exploiting internet‑connected Rockwell Automation/Allen‑Bradley PLCs across water, energy and government facilities. The advisory cites real‑world disruptions and financial losses, tracing the...

Gremlin Stealer Evolves Into Modular Threat with Advanced Evasion Capabilities
Palo Alto Networks’ Unit 42 reports that the Gremlin stealer has transformed from a simple credential harvester into a modular toolkit within a year. The latest build hides its malicious payload in the .NET resource section and applies XOR encoding to...
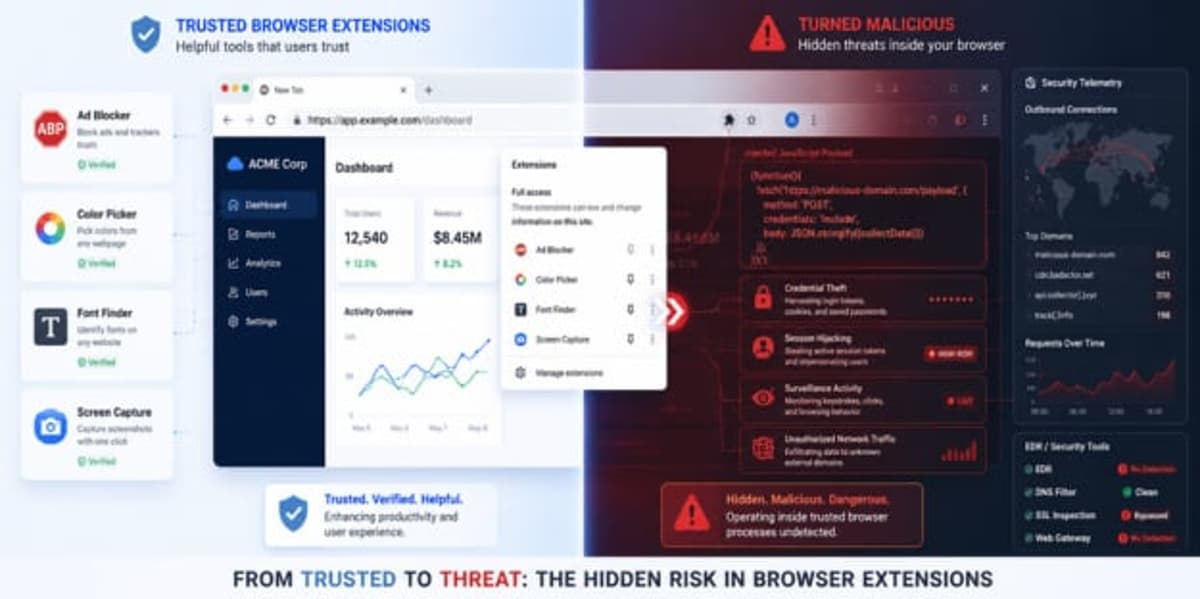
7AI Uncovers Browser Extension Campaign Evading EDR Defenses
7AI researchers identified a large‑scale malicious browser‑extension campaign called CRXfiltrate that injects remote JavaScript into authenticated Chrome sessions, bypassing EDR, SSL inspection and other traditional defenses. The operation uses a network of 22 extensions with over 85,000 installs and 60+...

AI Exploits, Ransomware Breaches, and Cloud Security Gaps Define This Week in May 2026
The week’s headlines were dominated by a Foxconn ransomware breach that stole 11 million files, exposing critical engineering data across its supply‑chain partners. Microsoft’s May Patch Tuesday delivered fixes for 120 vulnerabilities while cPanel patched three high‑risk flaws, underscoring the urgency...

Welcome to BlackFile: Inside a Vishing Extortion Operation
Google Threat Intelligence Group reports UNC6671, operating under the BlackFile brand, running a vishing‑based extortion campaign that targets Microsoft 365 and Okta environments. The group uses real‑time adversary‑in‑the‑middle attacks to capture MFA credentials, then registers attacker‑controlled devices for persistence. Automated...

THORChain Reports $10.7M Loss From Compromised Asgard Vault
THORChain announced that one of its six Asgard vaults was compromised, resulting in an estimated loss of $10.7 million. The network’s automated monitoring detected unauthorized outbound transactions and stopped signing activity, averting additional outflows. In response, THORChain paused churn operations, delaying...

Four OpenClaw Flaws Enable Data Theft, Privilege Escalation, and Persistence
Cybersecurity firm Cyera disclosed four linked vulnerabilities in the OpenClaw agent platform, dubbed the Claw Chain, that enable sandbox escape, credential theft, privilege escalation, and persistent backdoors. The flaws—CVE‑2026‑44112, ‑44113, ‑44115, and ‑44118—combine TOCTOU race conditions, heredoc injection, and a spoofable...

Gunra Ransomware Expands RaaS After Conti Locker Shift
Gunra ransomware has transitioned from a Conti‑derived locker to a standalone Ransomware‑as‑a‑Service platform, expanding its operational reach. The shift, announced after its initial 2025 attacks on South Korean firms, now powers an affiliate network that can brand the payload and...

Google Lets Workspace Admins Apply One Policy Across All SAML Apps
Google has upgraded Context‑Aware Access in Workspace with a default policy for SAML applications, establishing a universal security baseline for any SAML‑based app lacking a specific rule. Administrators can manually enable the feature at the organizational‑unit or group level, eliminating...

UAE Cyber Security Council, Siemens Sign OT Security MoU
The UAE Cyber Security Council and Siemens have signed a memorandum of understanding to deepen cooperation on operational technology (OT) cybersecurity across the UAE’s critical infrastructure. The pact creates a Joint Innovation Center of Excellence for OT research, workforce development,...

2025 Saw a Surge in Wireless Vulnerabilities
Security firm Bastille Networks reported a dramatic rise in wireless vulnerabilities in 2025, with 937 new CVEs—about 2.5 per day—recorded across Wi‑Fi, Bluetooth, cellular and Zigbee. Wireless flaws grew 20 times faster than traditional threats over the past 15 years,...

Illicit Enterprise: An Anatomy of the Modern Underground Phishing Marketplace
The phishing underground has transformed from a chaotic marketplace into a sophisticated criminal ecosystem offering tools, labor and phishing‑as‑a‑service (PhaaS). Intel 471’s 2026 Phishing Outlook, based on analysis of nearly 200 offers, reveals recruitment now accounts for 31 % of activity, with...

Patch Time for Cisco SD-WAN Admins as Vendor Drops yet Another Make-Me-Admin Zero-Day
Cisco has issued emergency patches for a critical zero‑day vulnerability (CVE‑2026‑20182) affecting its Catalyst SD‑WAN Controller and Manager, formerly known as vSmart and vManage. The flaw allows unauthenticated remote attackers to bypass authentication and obtain admin privileges, enabling arbitrary NETCONF...

What 45 Days of Watching Your Own Tools Will Tell You About Your Real Attack Surface
Bitdefender reports that 84% of 700,000 high‑severity incidents involve abuse of trusted Windows utilities, underscoring the living‑off‑the‑land (LOLBin) threat. To counter this, the firm offers a complimentary 45‑day Internal Attack Surface Assessment for organizations with 250+ employees, leveraging GravityZone PHASR to...
TanStack Supply Chain Attack Hits Two OpenAI Employee Devices, Forces macOS Updates
OpenAI disclosed that two employee devices were compromised in a supply‑chain attack targeting the TanStack library, part of the Mini Shai‑Hulud campaign. The breach resulted in limited credential exfiltration from internal source‑code repositories, but no intellectual property or production systems...

OrBit Rootkit Targets Linux to Steal SSH and Sudo Credentials
The OrBit Linux rootkit, first identified in 2022, has been quietly evolving while remaining active in the wild. Built on the open‑source Medusa LD_PRELOAD framework, attackers now deploy two main variants—Lineage A with full credential‑stealing and network‑hiding features, and a slimmer...

CalPhishing Scam Uses EvilTokens Kit, Outlook Invites to Steal M365 Sessions
Cybercriminals are leveraging a new CalPhishing technique that embeds malicious iCalendar (.ics) files into Outlook invites, automatically adding tentative meetings to victims' calendars. The campaign, identified by Fortra Intelligence and Research Experts, uses the EvilTokens phishing kit sold on Telegram...

Thorchain Halts Trading After $10 Million Cross-Chain Exploit, RUNE Token Drops 12%
Thorchain, the decentralized cross‑chain liquidity protocol, suffered a $10.8 million exploit spanning Bitcoin, Ethereum, BSC and Base, prompting an immediate halt to all trading and signing operations. The attacker’s wallets now hold roughly 3,443 ETH (about $7.8 million), 36.85 BTC (around $3.0 million) and 96.6 BNB...