
TeamPCP Ups the Game, Releases Shai-Hulud Worm’s Source Code
TeamPCP, a prolific hacking group, has publicly released the source code for its Shai‑Hulud supply‑chain worm on GitHub, prompting immediate forks before the repositories were taken down. The code reveals a modular framework with loaders, secret‑harvesting modules, encryption, and a random‑passphrase anti‑signature mechanism that thwarts traditional YARA detection. Simultaneously, the group launched a “supply‑chain challenge” on BreachForums, offering monetary rewards for successful deployments of the worm. Security firms warn that the open‑source release will lower the barrier for copy‑cat attacks and likely trigger a surge in supply‑chain compromises.

Rocky Linux Launches Opt-In Security Repository for Urgent Fixes
Rocky Linux has added an optional Security Repository that delivers urgent patches ahead of the upstream Enterprise Linux release when a vulnerability is publicly exploitable and no official fix exists. The repository is disabled by default and can be enabled...

AI-Hacking Threat Pushes $130 Billion Crypto Sector to the Brink
In April 2026, two AI‑enhanced crypto hacks siphoned roughly $600 million, accounting for about 76% of all cryptocurrency thefts that year. The attacks, attributed to North Korea‑linked groups, leveraged artificial intelligence to pinpoint vulnerable targets and craft custom exploits. The fallout...

The Economics of Ransomware 3.0
Ransomware 3.0 has shifted from pure encryption to a triple‑extortion play that combines system lock‑out, data exfiltration, and pressure on customers, regulators and shareholders. The model, used by groups such as ALPHV and Cl0p, forces organizations to confront threats that...

Keycard Helps Developers Secure Autonomous AI Agents with Scoped Access
Keycard unveiled “Keycard for Multi‑Agent Apps,” a platform that gives each autonomous AI agent its own verifiable identity and session‑based, scoped access. The solution replaces static API keys with runtime‑issued tokens, enabling fine‑grained delegation and full auditability across agent‑to‑agent workflows....

On-Prem Microsoft Exchange Server CVE-2026-42897 Exploited via Crafted Email
Microsoft disclosed CVE‑2026‑42897, an 8.1‑rated cross‑site scripting flaw in on‑premise Exchange Server that is already being exploited via crafted emails. The vulnerability allows arbitrary JavaScript to run in Outlook Web Access when a malicious message is opened. Microsoft’s temporary countermeasure...

OpenAI Confirms Limited Impact From TanStack Npm Supply Chain Attack, Urges macOS App Updates
OpenAI disclosed that a recent TanStack npm supply‑chain attack compromised two employee devices but did not expose customer data or production systems. The breach, linked to the Mini Shai‑Hulud malware campaign, prompted immediate isolation, credential rotation, and a temporary halt...

Taiwan Incident Highlights Cybersecurity Gaps in Rail Systems
On April 5 a 23‑year‑old rail enthusiast spoofed Taiwan High Speed Rail’s emergency radio, triggering emergency brakes on three bullet trains and causing a 48‑minute service disruption. The hack leveraged the Terrestrial Trunked Radio (TETRA) system, which can be secure but...

Hackers Exploit Auth Bypass Flaw in Burst Statistics WordPress Plugin
Hackers are exploiting a critical authentication bypass vulnerability (CVE‑2026‑8181) in the Burst Statistics WordPress plugin, which is installed on roughly 200,000 sites. The flaw, introduced in versions 3.4.0 and 3.4.1, lets unauthenticated attackers impersonate any known admin user or create...
Meet Fragnesia, the Third Linux Kernel Vulnerability in a Month
A new Linux kernel flaw named Fragnesia (CVE‑2026‑46300) has been disclosed, targeting the XFRM ESP‑in‑TCP subsystem to achieve local privilege escalation. The vulnerability provides an in‑memory write primitive that bypasses traditional file‑system permissions, allowing unprivileged users to corrupt security‑sensitive files...

Congress Puts Heat on Instructure After Canvas Outage
Congressional committees are pressing Instructure after its Canvas learning‑management system suffered two separate breaches within a week, attributed to the ShinyHunters cybercrime group. The attacks exposed more than 3 TB of data from over 9,000 educational institutions, including student IDs, emails,...
NSCC Information for the Confirmation of a Cybersecurity Program / Compliance to Rule File: SR-NSCC-2019-003
The National Securities Clearing Corporation (NSCC) has reminded all members that under Rule SR‑NSCC‑2019‑003 they must submit a complete Cybersecurity Confirmation every two years. An electronic form will be sent to each institution’s designated Control Officer on May 20, 2026, with a...

Synack’s Analysis of 11,000+ Vulnerabilities Reveals Top Weaknesses Attackers Are Weaponizing Today
Synack’s 2026 State of Vulnerabilities Report, based on over 11,000 exploitable flaws discovered in 2025, shows a 42‑day reduction in mean time to remediate high‑severity issues and a 47% overall MTTR drop. The threat landscape intensified, with CVE disclosures up...

Windows 11 and Microsoft Edge Hacked at Pwn2Own Berlin 2026
The first day of Pwn2Own Berlin 2026 saw researchers claim $523,000 in cash by exploiting 24 zero‑day vulnerabilities. Orange Tsai secured $175,000 for chaining four logic bugs to escape Microsoft Edge’s sandbox, while three teams each earned $30,000 for privilege‑escalation flaws in...

ODNI Taps Officials to Coordinate Response to Foreign Election Threats
The Office of the Director of National Intelligence has appointed Dave Mastro and James Cangialosi to serve as the intelligence community’s election‑threat executives, overseeing coordination across U.S. spy agencies for the 2026 midterm elections. The role, originally created during the...

Christophe Pettus: Eleven CVEs Walk Into a Release
PostgreSQL released versions 18.4, 17.10, 16.14, 15.18 and 14.23 on May 14, 2026, fixing eleven CVEs and over sixty bugs. Three of the CVEs carry a CVSS score of 8.8, exposing critical server‑side and client‑side vulnerabilities in core components like...

The "Zombie API" Attack: Why Your Old Integrations Are Your Biggest Security Risk
The article warns that forgotten, still‑active endpoints—dubbed “zombie APIs”—pose a hidden security threat. When teams deprecate an integration without formally shutting it down, the old API remains reachable, often using outdated protocols and weak authentication. Recent breaches at Optus, Honda...

ServiceNow’s Amit Zavery On Delivering An ‘End-To-End’ Security Platform For OT And IT
ServiceNow announced that its $7.75 billion acquisition of Armis is accelerating the company’s roadmap for a unified security platform that spans both IT and operational technology (OT). By integrating Armis’s asset‑intelligence engine with ServiceNow’s workflow suite, the firm aims to deliver...
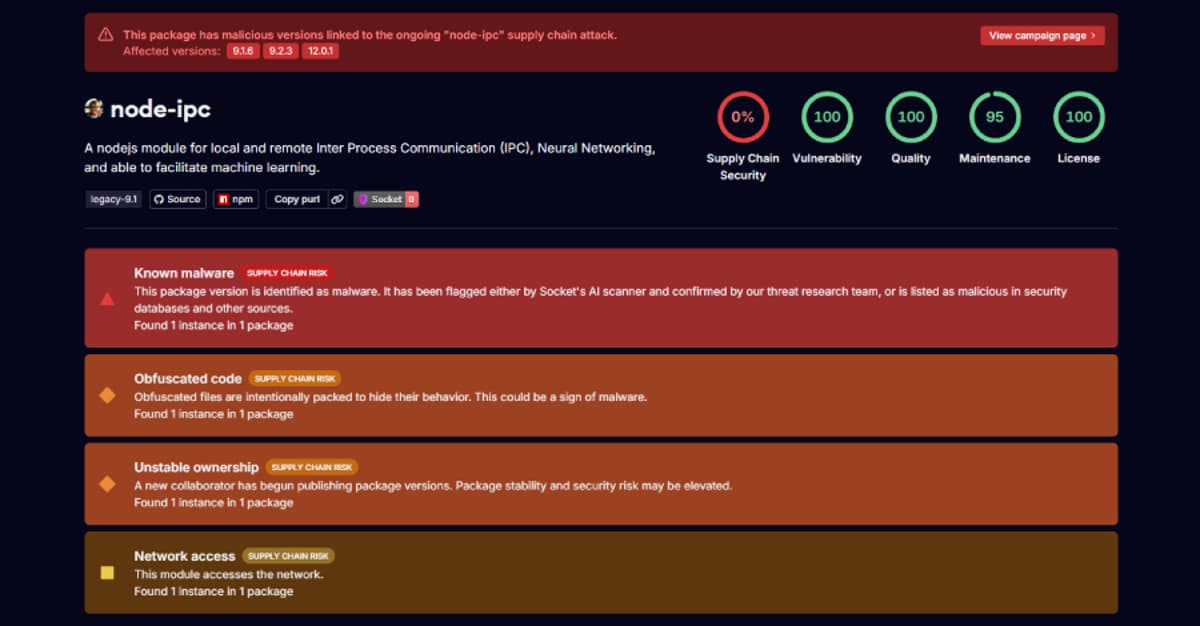
Stealer Backdoor Found in 3 Node-IPC Versions Targeting Developer Secrets
Security researchers have identified three compromised releases of the popular npm package node‑ipc (versions 9.1.6, 9.2.3 and 12.0.1) that embed a stealthy stealer/backdoor. The malicious code executes whenever the module is required, bypassing standard npm lifecycle hooks, and harvests roughly...

New Nginx Exploit
Depthfirst's automated analysis system uncovered a critical heap buffer overflow in NGINX’s ngx_http_rewrite_module, cataloged as CVE‑2026‑42945. The flaw allows unauthenticated remote code execution on servers that use rewrite or set directives, and it was disclosed alongside three related memory‑corruption issues....
'FrostyNeighbor' APT Carefully Targets Govt Orgs in Poland, Ukraine
Belarus‑linked APT group FrostyNeighbor, also known as Ghostwriter, has launched a new spear‑phishing campaign targeting government and military entities in Poland and Ukraine. The operation, active since March, uses deceptive PDFs that impersonate Ukrainian telecom provider Ukrtelecom and delivers a...

ThreatsDay Bulletin: PAN-OS RCE, Mythos cURL Bug, AI Tokenizer Attacks, and 10+ Stories
The ThreatsDay bulletin highlights a surge of active exploits, starting with Palo Alto Networks confirming limited attacks against its PAN‑OS CVE‑2026‑0300 buffer overflow, which grants root‑level code execution. Meta introduced Incognito Chat, a private AI interface that runs inference inside...

When Encryption Meets Quantum
Quantum computers will soon invalidate RSA and elliptic‑curve cryptography, exposing every system that relies on them—from IoT sensors to cloud services. A "harvest now, decrypt later" threat means encrypted data captured today can be broken once quantum hardware matures. U.S....

Cyber-Enabled Cargo Crime: How Cybercrime Tradecraft Is Used to Steal Freight
Cyber‑enabled cargo crime is borrowing ransomware playbooks to hijack freight, turning phishing attacks into fraudulent load pickups and rerouted shipments. In 2025 Verisk CargoNet estimated $725 million in cargo‑theft losses, while the FBI’s IC3 logged roughly $21 billion in broader cybercrime losses....

Druva Provides Integration with Dell PowerProtect Data Domain to Boost Cyber Resilience
Druva announced a new integration with Dell PowerProtect Data Domain that lets enterprises blend on‑prem Data Domain appliances with Druva’s cloud‑native SaaS platform. The joint solution offers fast local recovery from Data Domain and an immutable, air‑gapped copy in the...

A Spyware Investigator Exposed Russian Government Hackers Trying to Hijack Signal Accounts
Security researcher Donncha Ó Cearbhaill, who leads Amnesty International’s Security Lab, was targeted by a sophisticated phishing campaign that pretended to be Signal support. The attack was part of a larger operation that has affected more than 13,500 Signal users, using...
Ghostwriter Targets Ukrainian Government With Geofenced PDF Phishing, Cobalt Strike
The Belarus‑aligned threat group Ghostwriter has launched a new campaign against Ukrainian government entities, using geofenced PDF attachments that only deliver a malicious RAR archive when the victim’s IP originates from Ukraine. The archive drops a JavaScript version of PicassoLoader,...

Enhancing Data Center Security Without Sacrificing Performance
Data center operators are confronting a persistent trade‑off between security agents that consume CPU cycles and the need for peak performance, especially in AI‑focused facilities. Recent hypervisor‑level breaches, such as Broadcom’s March 2025 VMware ESXi zero‑day patches, highlighted that host‑based agents...

Aligning State and Local AI Security Investments with the Cyber Strategy for America
The White House’s Cyber Strategy for America outlines six pillars that can guide state and local cybersecurity, especially pillars four and five focused on critical infrastructure and emerging technologies. A 2025 Center for Internet Security report shows 68% of state,...

New Linux Kernel Vulnerability Fragnesia Allows Root Privilege Escalation
A new Linux kernel flaw, designated CVE‑2026‑46300 and nicknamed Fragnesia, lets an unprivileged user gain root access by corrupting files through the XFRM ESP‑in‑TCP subsystem. The vulnerability enables a memory‑write primitive that can overwrite binaries such as /usr/bin/su or even...

HYCU Adds Agentic Backup Data Intelligence Layer to Find and Fill Risk Gaps
HYCU has launched aiR, an AI‑agent layer that queries backup data across more than 100 workloads, from on‑premises servers to major cloud SaaS applications. The platform provides natural‑language search, letting admins ask plain‑language questions that surface PII, insider‑risk signals, configuration...

TeamPCP, BreachForums Launch $1K Supply-Chain Attack Contest
TeamPCP and BreachForums have launched a $1,000 Monero‑rewarded contest that challenges hackers to compromise open‑source packages using the Shai‑Hulud tool. Participants submit proof of access and compete on a leaderboard that scores based on download volume of the infected packages....

FlowerStorm Phishing Gang Adopts Virtual-Machine Obfuscation to Evade Email Defenses
Security researchers have identified that the FlowerStorm phishing-as-a-service operation is now employing KrakVM, an open‑source JavaScript virtual machine, to obfuscate credential‑stealing code delivered via HTML attachments. The VM‑based payload encrypts malicious bytecode, evading static analysis and traditional email‑security tools while...

Akamai to Acquire AI and Browser Security Firm LayerX for $205 Million
Akamai announced an all‑cash acquisition of LayerX for roughly $205 million. LayerX, a startup focused on AI‑driven browser security, brings a platform that monitors user and agentic activity across browsers, apps, and IDEs. The deal, expected to close in Q3 2026, adds...

Chinese APT Exploits Microsoft Exchange to Breach Energy Sector Network
Chinese state‑aligned APT group FamousSparrow breached a major Azerbaijani energy firm by exploiting the ProxyNotShell chain on an unpatched Microsoft Exchange server on Dec. 25, 2025. The attackers deployed the Deed RAT via a LogMeIn Hamachi DLL sideloading technique and later attempted a...

Chinese APTs Expand Targets, Update Backdoors in Recent Campaigns
Chinese state‑sponsored groups Salt Typhoon and Twill Typhoon have broadened their target sets and refreshed their malware toolkits. Salt Typhoon used the ProxyNotShell exploit chain to breach Microsoft Exchange servers, deploying Deed RAT via DLL sideloading and later re‑introducing the TernDoor backdoor. Twill Typhoon...

Foxconn Attack Highlights Manufacturing's Cyber Crisis
Foxconn confirmed a cyberattack at several North American factories, with the Nitrogen ransomware gang claiming responsibility. The gang alleges it exfiltrated over 11 million files, roughly 8 TB of data, including confidential designs for clients such as Apple, Nvidia and Google. While...

New Malware Framework Enables Screen Control and UAC Bypass
Researchers uncovered TencShell, a sophisticated malware framework built on the open‑source Rshell C2 tool and repurposed for stealthy post‑exploitation. In April 2026, Cato CTRL blocked an attack on a global manufacturing firm in India after the implant delivered Donut shellcode hidden...

PraisonAI Vulnerability Gets Scanned Within 4 Hours of Disclosure
A critical authentication bypass in the open‑source AI orchestration framework PraisonAI was actively scanned less than four hours after a GitHub advisory disclosed it. The flaw, tracked as CVE‑2026‑44338, disables authentication by default in a legacy Flask API server and...

Industrial Organizations Under Increasing Fire as Attackers Target Operational Technology
Industrial organizations faced a surge in ransomware, with 2,073 attacks representing 30% of all incidents in the year to March 2026. Capital‑goods manufacturers were hardest hit, recording 1,192 attacks, and the machinery sub‑sector alone suffered 442 incidents. Regulators in the...

Cybersecurity Awareness Rises—And Shifts
Cybersecurity consulting demand is accelerating, especially among mid‑market firms and small businesses, as the focus shifts from compliance to risk mitigation, revenue protection, and business continuity. Mid‑market companies are adopting hybrid models that blend lighter internal teams with external experts,...

170 Npm Packages Hijacked to Steal GitHub, AWS & Kubernetes Secrets
Hackers compromised more than 170 npm packages and two PyPI libraries, which together see over 200 million weekly downloads, to harvest developer and cloud credentials. The malicious packages embed pre‑install scripts that download obfuscated payloads, extract GitHub Actions tokens, npm publishing...

F5 Patches Over 50 Vulnerabilities
F5 Networks announced patches for more than 50 vulnerabilities affecting its BIG‑IP, BIG‑IQ and NGINX platforms, including 19 high‑severity and 32 medium‑severity flaws. The most critical issue, CVE‑2026‑42945, scores 9.2 and can cause a denial‑of‑service or code execution if ASLR...

China-Linked Twill Typhoon Uses Fake Apple and Yahoo Sites for Espionage
Security firm Darktrace has identified a new wave of espionage attacks across Japan and the broader Asia‑Pacific region, attributed to the China‑linked group Twill Typhoon. The actors disguise malicious payloads as legitimate software and host them on counterfeit Apple and...

Most Organizations Now Use AI Agents for Sensitive Security Tasks
A new Semperis study finds that 93% of global enterprises already use or plan to deploy AI agents for sensitive security functions such as password resets and VPN access. At the same time, 92% have these agents installed on machines...
Mistral Pitches Security-Focused Model As Mythos Alternative
Mistral AI, a French startup, is promoting a security‑focused generative model as a European alternative to Anthropic’s Claude Mythos. The company says its AI can scan code for vulnerabilities in high‑risk sectors such as banking and the military, and it...

ICO Publishes Five-Step Plan to Counter Emerging AI-Powered Attacks
The UK Information Commissioner’s Office (ICO) has issued a five‑step guide to counter the surge in AI‑driven cyber attacks, urging organisations to adopt multi‑layered defenses and align with the National Cyber Security Centre’s updated Cyber Assessment Framework. The guidance highlights...

Using Continuous Purple Teaming to Protect Fast-Paced Enterprise Environments
Enterprise security teams face ever‑changing attack surfaces as cloud adoption, infrastructure‑as‑code, and continuous delivery accelerate system turnover. Traditional periodic pen tests no longer reflect the current state, prompting a shift to continuous purple teaming, which fuses offensive (red) and defensive...

Exim BDAT Vulnerability Exposes Email Servers to Remote Attacks
A critical remote use‑after‑free flaw (CVE‑2026‑45185) was discovered in Exim mail servers that use GnuTLS, earning a CVSS score of 9.8. The vulnerability surfaces when a TLS close_notify alert interrupts an active BDAT transfer, allowing memory corruption and potential code...

AI Cyberattacks Are Escalating Across the Americas. This Webinar Explains Why
In the first quarter of 2026 the Americas saw a sharp rise in AI‑powered cyberattacks, ransomware bursts, and assaults on critical infrastructure. Threat actors leveraged generative AI to automate phishing, deepfake creation, and rapid exploitation, making detection harder. Nation‑state groups...