
White House Prepares Order to Boost AI Security, Hassett Says
The White House is drafting an executive order to create a vetting system for new AI models after Anthropic’s Mythos demonstrated the ability to locate network vulnerabilities. National Economic Council Director Kevin Hassett likened the proposed safety review to the FDA drug‑approval process, signaling a possible shift toward mandatory testing. The Commerce Department simultaneously expanded a voluntary AI‑testing program that includes Google, Microsoft and xAI, while the administration negotiates broader AI policy for national‑security agencies. These moves aim to curb AI‑related cyber risks to both government and private‑sector networks.

AI Evaluation Startup Braintrust Confirms Breach, Tells Every Customer to Rotate Sensitive Keys
AI evaluation startup Braintrust disclosed an unauthorized access incident in one of its AWS accounts that exposed customer API keys. The company sent an email urging every client to revoke and rotate those keys, noting that only one customer has...

Netskope Launches AI Agents for SOC and NOC Automation
Netskope unveiled AgentSkope, an AI‑driven framework embedded in its Netskope One SASE platform, to automate security and network operations. The solution targets the chronic alert fatigue in SOCs and NOCs, where 40% of alerts go uninvestigated, by deploying six specialized...

ShinyHunters’ Instructure Canvas LMS and Vimeo Breaches Impact Millions of Users
ShinyHunters disclosed a massive data breach affecting Instructure’s Canvas learning platform and video‑hosting service Vimeo. The group claims to have exfiltrated 3.65 TB of data, including 275 million Canvas records and private messages from roughly 15,000 institutions worldwide. Vimeo’s breach stemmed from...

Pentagon Prepares F-35 for Quantum Computing Threat
The Pentagon’s F‑35 Joint Program Office issued a sole‑source presolicitation on May 6, 2026 to upgrade the fighter’s In‑Line File Encryption Device (IFED) with quantum‑resistant algorithms. Lockheed Martin Aeronautics is the only qualified contractor, with capability statements due by May 21, 2026. The contract...

The FBI Is Now Tracking AI Scams, and the Losses Are Huge
The FBI’s Internet Crime Complaint Center has, for the first time, isolated artificial‑intelligence‑related fraud as a distinct category in its 2025 cybercrime report. Americans reported nearly $21 billion in total cybercrime losses, with AI‑linked scams accounting for about $893 million across more...

DeFi Protocol Kelp DAO Pivots to Chainlink CCIP for Stronger Cross-Chain Security
Kelp DAO announced it will replace LayerZero with Chainlink’s Cross‑Chain Interoperability Protocol (CCIP) as the backbone for its rsETH bridge. The move follows an April 18 exploit that drained about 116,500 rsETH, roughly $292 million, highlighting vulnerabilities in LayerZero’s messaging layer. CCIP’s...

OpenAI Violated Canadian Privacy Laws, Federal and Provincial Watchdogs Say
Four Canadian privacy commissioners concluded that OpenAI breached federal and provincial privacy statutes while gathering data to train early ChatGPT models. The agency said the company scraped personal and sensitive information from social media, blogs and news sites without obtaining...
Chrome Downloads a 4GB AI File without User Consent, Researcher Alleges
Google’s Chrome browser silently downloaded a 4 GB Gemini Nano model file to users’ machines without prompting. Researchers confirmed the weights.bin file appears after Chrome 148.0.7778.97 updates on macOS and Windows, and re‑downloads after deletion unless AI features are disabled via...
MSPs Get AI Workforce to Scale Managed Security
WatchGuard unveiled Rai, an agentic AI digital workforce for managed service providers that automates detection, investigation and response tasks. Positioned as a shift from assistive to autonomous AI, Rai operates continuously, taking pre‑authorized actions and logging them via the WatchGuard...

Kubernetes Finally Lands User Namespace Support, but Shared Kernel Problem Remains
Kubernetes 1.36 introduces general‑availability user namespace support, allowing pods to remap root to an unprivileged host UID. This mitigates several high‑severity CVEs by limiting the impact of container escapes and lateral movement. However, all containers still share the same Linux...

Charities Must Avoid Damaging Public Trust when Using Soft Opt-In, Regulator Warns
Britain’s Fundraising Regulator has released updated data‑privacy guidance to reflect the Data (Use and Access) Act 2025, which introduces a soft‑opt‑in provision allowing charities to send direct marketing without explicit consent. The regulator cautions that misuse of this power could...

Breaches in Cybersecurity Could Disrupt, Affect Patient Care: Tarun Sondhi
Accenture’s cybersecurity lead Tarun Sondhi warned that the growing reliance on electronic devices and interconnected vendor platforms is expanding the attack surface in health care. Breaches can cripple systems, delay access to patient records, and disrupt scheduling, directly affecting treatment...

Why Ransomware Attacks Succeed Even when Backups Exist
Ransomware attackers are now deliberately compromising backup systems, turning what should be a safety net into a single point of failure. The Acronis Cyberthreats Report shows a 50 % rise in attacks last year, exposing common weaknesses such as shared credentials,...

SecureIQLab Opens Post-Quantum Validation of Cloud-Native Firewalls
SecureIQLab released the first AMTSO‑registered validation methodology that tests cloud‑native firewalls against NIST post‑quantum cryptography (PQC) standards, including ML‑DSA, ML‑KEM and SHA‑384/512. The framework, Cloud Native Firewall CyberRisk Validation v1.0, evaluates up to 16 vendors across multi‑cloud, Kubernetes and serverless...

Some Kids Are Bypassing Age-Verification Checks with a Fake Mustache
Governments in the U.S. and U.K. are tightening age‑verification laws to keep minors off adult sites, forcing platforms to adopt document uploads or biometric checks. A survey by Internet Matters found half of 1,000 children could easily bypass these controls,...

Devicie Is Building Endpoint Security for an AI-Driven World
Devicie, an Australian‑origin startup, delivers a zero‑touch, AI‑enhanced endpoint security platform built on Microsoft Intune, automating patching, compliance and policy enforcement for laptops, tablets and phones. The solution addresses the fact that up to 90% of cyberattacks start at endpoints...

MFA Misconfiguration Is the Costliest Point of Failure in Manufacturing Cyber Claims
Manufacturing has been the world’s most targeted industry for cyberattacks for five straight years, yet its security spending lags behind exposure. Resilience’s five‑year claims analysis shows ransomware accounts for 90% of losses while representing only 12% of claim volume. The...

MuddyWater Uses Microsoft Teams to Steal Credentials in False Flag Ransomware Attack
Iranian‑backed MuddyWater disguised a ransomware campaign as a Chaos RaaS attack, using Microsoft Teams screen‑sharing to steal credentials and bypass MFA. The group focused on data exfiltration and persistence via DWAgent and AnyDesk rather than encrypting files. A code‑signing certificate...

Iranian APT Intrusion Masquerades as Chaos Ransomware Attack
Iran‑linked APT MuddyWater staged a sophisticated intrusion in early 2026 that masqueraded as a Chaos ransomware attack. The group used Microsoft Teams screen‑sharing to harvest credentials, deployed remote‑access tools such as AnyDesk and its own DWAgent, and installed a custom...

Webinar: Why Network Incidents Escalate and How to Fix Response Gaps
On June 2, 2026 BleepingComputer will host a live webinar titled “From alert to containment: Fixing the gaps in network incident response,” featuring Edgar Ortiz of Tines. The session examines why incident response falters—particularly during triage, enrichment, and routing—and demonstrates how intelligent,...

Chinese Chamber of Commerce Puts a $432bn Price Tag on the EU’s Cybersecurity Overhaul
The China Chamber of Commerce in the EU commissioned KPMG to estimate the cost of the European Commission’s revised Cybersecurity Act, which would force the removal of Chinese suppliers from 18 critical sectors. The study puts the price tag at...
Hackers Compromise Daemon Tools in Global Supply-Chain Attack, Researchers Say
Researchers at Kaspersky discovered that hackers compromised the installer files for Daemon Tools Lite, a popular disk‑image mounting program, by injecting backdoors into versions 12.5.0.2421 through 12.5.0.2434. The malicious installers were distributed via the official website and reached users in...

UK High Court Dismisses Facial-Recognition Judicial Review Case
The UK High Court dismissed a judicial review brought by anti‑knife activist Shaun Thompson and privacy advocate Silkie Carlo, finding that the Metropolitan Police’s live facial‑recognition (LFR) policy contains sufficient legal constraints. The court rejected claims that the policy is...

Study Says AI Has yet to Transform Cybercrime
A peer‑reviewed study of over 100 million posts from underground cybercrime forums finds that artificial intelligence has not yet revolutionized illicit activity. While criminals experiment with tools like ChatGPT, AI mainly helps skilled actors hide malicious patterns and run automated harassment...

From Stuxnet to ChatGPT: 20 News Events That Shaped Cyber
Dark Reading commemorates its 20th anniversary by cataloguing 20 pivotal cyber events—from the Stuxnet worm that shattered the myth of air‑gapped safety to the rise of AI‑driven threats like ChatGPT. The piece traces how early viruses evolved into nation‑state sabotage,...

I Gave Our Developers an AI Coding Assistant. The Security Team Nearly Mutinied
A technology leader approved an AI coding assistant to relieve developers from repetitive tasks, but the security team reacted strongly, fearing uncontrolled code generation. The tool can draft tests, explain legacy code, and suggest refactors, yet it raises questions about...
Romanian Man Extradited to US for Role in Hacking Scheme 17 Years Ago
Romanian national Gavril Sandu was extradited to the United States after being arrested in Romania in January 2026. Sandu faces charges for a 2009‑2010 vishing scheme that compromised small‑business VoIP systems, stole payment‑card data and acted as a money mule. The...

Construction ‘Least Prepared’ Industry for Cyber Threats, Poll Finds
A Beazley survey of over 3,500 leaders finds construction firms are the least prepared for cyber threats, with only 74% confident in their defenses and 32% citing security as their top concern. AI‑driven phishing and a 410% YoY rise in...

US Firms Could Face Exclusion Under New EU Cyber Bill, Lead Lawmaker Says
The European Parliament is revising its Cybersecurity Act to address non‑technical risks from third‑country vendors, a move that could label U.S. technology firms as high‑risk suppliers. Lead negotiator Markéta Gregorová warned that American companies may face exclusion if they fail...

The Creation of the Credential Protection Register; More than 750,000 Fraudulent Verification Requests Blocked
Australia’s Albanese Government has launched the Credential Protection Register, a national database designed to stop identity‑theft fraud in digital government services. Since its rollout, the register has blocked more than 750,000 fraudulent verification requests, averaging 18,000 per month. An investment...

Build the Agentic SOC to Combat AI-Powered Attackers
Splunk, now a Cisco subsidiary, is urging firms to replace fragmented security tools with an AI‑powered SecOps platform that unifies SIEM, SOAR and UEBA. At the ITWeb Security Summit 2026 in Johannesburg, VP Ahmed El Saadi will detail how this integrated...

White House App Is a Terrifying Security Mess
A security analysis of the new White House Android app uncovered a suite of privacy‑and‑security flaws. The app continuously polls GPS coordinates—every 4.5 minutes in the foreground and 9.5 minutes in the background—and sends them to OneSignal’s servers, even though...

Telenor to Have Another Go at Weaning Itself Off US Hyperscalers
Telenor will launch Telenor Sovereign Cloud in the first half of 2025 as a distinct unit within Telenor Infrastructure. The service will operate from Norwegian‑controlled data centres, fully isolated from commercial global cloud providers, to satisfy strict security and data‑sovereignty...

South Africa’s Patching Problem Is About to Get Worse
South African enterprises are already missing patch windows for traditional software, and the rollout of autonomous AI agents threatens to widen that gap. TrendAI’s Zaheer Ebrahim warns that AI agents can be hijacked through hidden email instructions, bypassing malware defenses....
4 Things Apple Should Let Android Users Do on iPhone (and One Is Actually Happening)
Apple is rolling out encrypted RCS messaging that lets iPhone and Android users exchange native, end‑to‑end‑encrypted texts, currently available in beta with a toggle in Settings. The same beta adds EU‑only features such as one‑tap pairing for Android earbuds, smartwatches,...

Why Europe Must Refuse the Data-Sharing Deal with the US
The European Commission is weighing a deal that would let U.S. authorities access personal data of 450 million Europeans in exchange for preserving the visa‑waiver program. Critics, led by the European Data Protection Supervisor, argue the arrangement lacks reciprocity and undermines...

Application Security Strategies Are Changing as AI-Generated Code Floods the SDLC
AI coding assistants have shifted from experimental tools to daily development aids, accelerating function drafting, test generation, and repetitive changes. However, security teams now grapple with how much AI‑generated code reaches pull requests without proper validation, as 46% of developers...

Daon Launches Workforce Identity Fraud Prevention Tool
Daon announced a Workforce Identity Fraud Prevention solution that unifies its TrustX, xProof, xAuth and xFace technologies into a single framework. The platform verifies candidate identities during hiring, issues phishing‑resistant passkey authentication, and provides step‑up and continuous re‑verification throughout employment....
Google's Android Apps Get Public Verification to Stop Supply Chain Attacks
Google announced that its Binary Transparency system will cover all production Android applications and Mainline modules starting May 1, 2026. The public, cryptographic ledger records metadata for each released binary, allowing anyone to confirm that the software matches Google’s intended build. By...

Poisoned Truth: The Quiet Security Threat Inside Enterprise AI
Enterprises are rapidly deploying internal LLMs, copilots, and autonomous agents, but security teams are overlooking a silent threat: AI data poisoning. The risk arises when models ingest corrupted, stale, or low‑quality data, causing them to produce plausible yet wrong outputs...

Financial Services Industry Collaborates to Test Real-World Cyber Readiness
Lloyds Banking Group, Hack The Box, and Google Cloud Security hosted the first UK Financial Services Security Hackathon on April 27‑28, drawing 33 teams from 16 firms. The competition tested real‑world cyber readiness across web exploitation, forensics, OSINT, cryptography and...

Train Like You Fight: Why Cyber Operations Teams Need No-Notice Drills
Cybersecurity detection has improved, yet response readiness still lags behind. The article contends that scheduled tabletop exercises cannot mimic the physiological stress of real incidents and recommends no‑notice drills to build instinctive, resilient response capabilities. Citing medical, military and psychological...

EU Cyber Plan Barring Chinese Suppliers Will Cost US$430 Billion: Report
The European Union is set to adopt a new Cybersecurity Act that would bar Chinese hardware from critical infrastructure such as telecoms, energy grids, and transport networks. A recent study estimates the required replacement of Chinese equipment will cost the...

One in Eight Workers Has Sold Their Corporate Logins
According to Cifas’ Workplace Fraud Trends report, 13 % of UK employees either sold their corporate logins or knew a colleague who did in the past year. Acceptance of the practice spikes among senior staff, with 81 % of business owners deeming...

Heartbot AI Partners with Zyxel Networks to Bring Secure GenAI Access to SMBs Worldwide
Heartbot AI announced a strategic partnership with Zyxel Networks to embed its AnyInsight.ai platform into Zyxel’s USG FLEX H series firewalls, delivering a secure, governed gateway for generative AI to SMBs and managed service providers. The integration offers unified access...
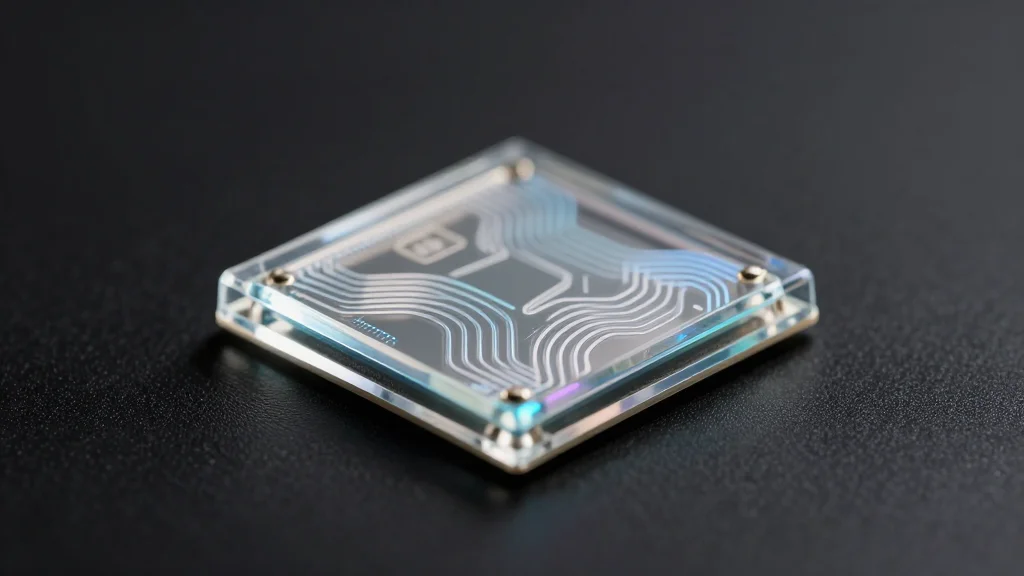
How Spain’s ICFO Helped Build a Quantum Security Startup for the AI Era
Quside, a Barcelona startup spun out of the Institute of Photonic Sciences (ICFO), sells photonic quantum random number generator (QRNG) chips that deliver high‑quality, verifiable entropy for cryptographic keys. The firm has shipped to 50‑60 customers worldwide and expects to...
Massive “Low and Slow” DDoS Attack Hits Platform With 2.45 Billion in 5 Hours
Cybercriminals launched a fragmented "low and slow" DDoS campaign that flooded a major user‑generated content platform with 2.45 billion requests over five hours. The attack leveraged more than 1.2 million unique IP addresses across 16,402 autonomous systems, peaking at 205,344 requests per...

EnforceAuth Open-Sources Zift — A Code Scanner Built to Close the Authorization Gap in Enterprise and AI Systems
EnforceAuth has released Zift, an Apache‑2.0 open‑source scanner that automatically discovers authorization decisions across multi‑language codebases and generates Open Policy Agent (OPA)‑ready Rego policy stubs. In an internal benchmark of a financial app, Zift found only 20% of enforcement points...

‘We’re Not Investing as Much as We Should in Their Skills and Development’: Skills Shortages Remain a Key Factor in...
Fortinet’s 2026 Global Cybersecurity Skills Gap Report finds human factors remain the top cause of breaches, with 56% of leaders pointing to employee security‑awareness gaps and 54% to a shortage of trained staff. Traditional attacks—malware (39%), phishing (36%), web (31%)...