CISA Orders Feds to Patch Windows Flaw Exploited as Zero-Day
CISA has added Windows vulnerability CVE‑2026‑32202 to its Known Exploited Vulnerabilities catalog and issued Binding Operational Directive 22‑01, requiring federal agencies to patch by May 12. The zero‑click NTLM hash‑leak flaw stems from an incomplete fix for CVE‑2026‑21510 and enables pass‑the‑hash attacks that can expose sensitive data. Russian APT28 previously exploited the related CVE‑2026‑21510 in Ukraine and EU targets, raising concerns that the new flaw may be part of a broader exploit chain. Microsoft now confirms active exploitation, urging immediate mitigation.

A Quarter of Healthcare Organizations Report Medical Device Cyber-Attacks
RunSafe Security’s 2026 Medical Device Cybersecurity Index found that 24% of healthcare organizations experienced cyber‑attacks on medical devices in the past year. In 80% of those incidents, the impact on patients was moderate or significant, ranging from delayed imaging to...

GitHub Rushed to Fix a Critical Vulnerability in Less than Six Hours
GitHub patched a critical remote code execution vulnerability in less than six hours after Wiz Research used AI to discover the flaw in its internal git infrastructure. The security team reproduced the bug within 40 minutes, deployed a fix to...
Somebody’s Watching Me: The Crackdown on Stalkerware
The podcast episode spotlights Eva Galperin’s fight against stalkerware, a hidden class of spyware used to monitor victims’ phones. After uncovering a colleague’s decades‑long abuse in 2018, Galperin founded the Coalition Against Stalkerware to coordinate researchers, advocates, and legal action....

Aviatrix Intros Platform For Agentic AI Security The ‘Containment Era’
Aviatrix has introduced AgentGuard, a platform designed to contain compromised AI agents rather than merely detect and remediate them. The solution discovers agents across VMs, Kubernetes clusters, and serverless functions, mapping their connections and enforcing zero‑trust communication governance. By limiting...

Your AI Agent Is Ready to Go. Is Your Infrastructure?
TransUnion has spent $145 million building the OneTru platform, a hybrid architecture that couples traditional expert systems with generative AI, and has already generated $200 million in cost savings. The platform powers the AI Analytics Orchestrator Agent, leveraging Google Gemini to let...

38 Vulnerabilities Found in OpenEMR Medical Software
A security audit by Aisle uncovered 38 vulnerabilities in OpenEMR, the open‑source electronic medical records platform used by more than 100,000 healthcare providers worldwide. The flaws include two critical SQL‑injection bugs (CVE‑2026‑24908 and CVE‑2026‑23627) and an authorization‑bypass issue (CVE‑2026‑24487) that...

Critical cPanel Authentication Vulnerability Identified — Update Your Server Immediately
cPanel has issued emergency security updates to fix a critical authentication bypass vulnerability (CVE‑2026‑41940) that scores 9.8 on the CVSS scale. The flaw affects all supported cPanel and WHM versions and can allow unauthenticated attackers to gain full administrative control...

Chrome 147, Firefox 150 Security Updates Rolling Out
Google and Mozilla released critical security updates for Chrome 147 and Firefox 150, addressing a total of 34 memory‑safety flaws. Chrome 147 includes 30 fixes, four of which are critical use‑after‑free bugs, while Firefox 150.0.1 patches four high‑severity vulnerabilities. Google...

AWS Leans on Prior Ingenuity to Face Future AI and Quantum Threats
AWS marks its 20‑year anniversary while confronting AI‑driven attacks and the looming quantum‑computing risk. The Nitro hardware platform gives AWS a “zero‑human” infrastructure, enabling isolated bare‑metal instances and protecting encryption keys. Early adoption of symmetric encryption means most data at...

Top AI-Powered Vendor Risk Management Platforms for SaaS Companies in 2026
Vendor risk breaches now account for roughly 30% of incidents, prompting regulators like Europe’s DORA and the SEC to tighten third‑party oversight. AI‑powered TPRM platforms promise continuous, machine‑speed visibility, turning multi‑page SOC 2 reports into concise insights and auto‑generating tickets in...

Microchip Launches PQC-Ready Root of Trust Controllers for Secure Platforms
Microchip Technology unveiled the TS1800 root‑of‑trust controller and the TS50x secure‑boot family, both engineered to run post‑quantum cryptography (PQC) algorithms. The TS1800 provides external root‑of‑trust functions with hardware acceleration for NIST‑standard PQC schemes such as ML‑DSA, LMS and ML‑KEM, while...
Met Police Federation Decries ‘Outrageous’ Palantir AI System
The Metropolitan Police Federation is threatening legal action over the force’s new Palantir AI system, which it says breaches officers’ privacy and GDPR rules. The pilot, launched last week, has already led to two arrests and two suspensions while hundreds...

CERT-In Warns of AI-Driven Cyber Threat Surge, MSMEs at Highest Risk
India’s cyber‑security agency CERT‑In warned that frontier AI is reshaping cyber threats, making attacks faster, more scalable and accessible to low‑skill actors. The advisory highlights that AI can scan code, spot zero‑day vulnerabilities and launch coordinated multi‑stage attacks in seconds....

Malaysian Indians Least Likely to Be Scammed as They Ask Too Many Questions: Police
Malaysians suffered an estimated 2.7 billion ringgit (about US $684 million) loss to online scams in 2024, a 76% jump from the prior year. The Penang Commercial Crime Department reported that only 7% of the 5,090 scam cases in the state involved Indian...

ClickUp Discloses Feature Flag Misconfiguration That Exposed 893 Customer Email Addresses and a Live API Token
ClickUp disclosed that a misconfigured feature‑flag setup exposed 893 customer email addresses and a live API token. The emails were embedded in Split.io flag targeting rules and became publicly queryable through the client‑side SDK key, which is intentionally exposed in...

Privacy Watchdog Clears Jollibee’s Christmas Ads
The National Privacy Commission (NPC) cleared Jollibee Foods Corp. and Rakuten Viber of violating the Philippines’ Data Privacy Act after a probe into the 2025 Holiday Gems Christmas campaign. The investigation found the stickers were delivered via on‑device keyword matching, with...

Router (Home Network): OWE Authentication Question
A home‑network user in NYC noticed their router reporting OWE (Opportunistic Wireless Encryption) instead of the expected WPA2. The moderator explained that when a router is set to WPA3/WPA2 mode it operates in an OWE transition mode, causing compatible devices...

BlueAPACHE Partners with NinjaOne to Strengthen Services Delivery
blueAPACHE announced a strategic partnership with NinjaOne, embedding the latter’s unified IT operations platform into its managed‑services framework. The integration will enable remote monitoring, automated patching, secure access and proactive remediation across client environments. blueAPACHE will first run NinjaOne‑enabled services...

Smart Firms Treat Vendor Risk Like Their Own
Artificial intelligence is accelerating the discovery of third‑party software flaws, turning vendor risk into a frontline concern for enterprises. Microsoft’s April 14, 2026 patch cycle addressed 167 Windows vulnerabilities, illustrating how quickly weaknesses can surface. Mid‑market firms, heavily reliant on cloud and...

New Report From the MPA’s Content Security Initiative Links Control Failures to Content Security Incidents Across the Entertainment Industry
The Motion Picture Association’s Trusted Partner Network released the TPN STAR Report, the first industry‑wide study linking security‑assessment data to real‑world content‑security incidents. The report finds that while most studios have basic policies, inconsistent execution of technical controls—especially MFA, vulnerability management,...

Why Backing Up Your Microsoft 365 Data Is Only Half the Job
Microsoft 365 has transformed from a suite of web apps into the enterprise’s central control plane, intertwining identity, collaboration, security, and workflow. While Microsoft secures the underlying platform, customers now shoulder configuration, access delegation, and governance responsibilities. A breach at a...

Building Cyber Resilience Through Zero Trust in the Public Sector
Public sector agencies are prime cyber‑crime targets, prompting governments to replace perimeter defenses with identity‑led Zero Trust models. In Australia, Zero Trust is codified in the 2025 Protective Security Policy Framework and reinforced by state strategies such as NSW’s 2026‑2028...

U.S. Ends Investigation Into Claims WhatsApp Chats Aren’t Private
The U.S. Commerce Department abruptly ended a 10‑month investigation into allegations that Meta Platforms can access and store unencrypted WhatsApp messages. The probe, led by an export‑control agent who claimed Meta viewed all content, was shut down at senior agency...
CyberHeed Pushes Beyond Checkbox Compliance with SmartPrep
CyberHeed, a Melbourne startup, is expanding its SmartPrep platform to serve as a foundational "compliance brain" for organizations at any maturity level. The tool reuses up to 60% of work across different GRC frameworks, shifting focus from certificate‑driven compliance to...

Federal Drawdown of Election Support ‘Destroyed’ Ongoing Relationships, Experts Say
Federal efforts under President Trump to scale back the Cybersecurity and Infrastructure Security Agency (CISA) have stripped election‑security staff, halted disinformation teams and eliminated the agency’s election program in the FY 2027 budget proposal. State officials in Michigan and Georgia testified...

Always-On Defence Becomes Critical as AI Accelerates Cyber Threats: Infotrust
Cybersecurity leaders warn that AI‑driven automation is accelerating attack speed, forcing organisations to shift from periodic checks to an always‑on defence model. Infotrust CEO Simon McKay notes attackers now have access to the same AI tools used by defenders, enabling larger‑scale...

Exclusive: OpenAI, Anthropic Meet with House Homeland Security Behind Closed Doors on Cyber Threats
OpenAI and Anthropic briefed the House Homeland Security Committee staff in classified sessions about their new cyber‑capable AI models—OpenAI’s tiered‑release GPT‑5.4‑Cyber and Anthropic’s Mythos Preview, which remains unreleased due to exploit risks. Both firms are granting federal agencies direct access...

Broken VECT 2.0 Ransomware Acts as a Data Wiper for Large Files
Researchers have identified a critical flaw in the VECT 2.0 ransomware that causes it to act as a data wiper for files larger than 128 KB. The ransomware, promoted on BreachForums and linked to the TeamPCP threat group, targets victims of recent...

Shift to SSI Could Preserve Security of India’s Digital Ecosystem at Scale
The Data Security Council of India and the Digi Yatra Foundation released a joint paper urging a shift to self‑sovereign identity (SSI) for India’s digital ecosystem. It argues that centralized identity systems like Aadhaar are straining under scale, privacy expectations,...

Hackers Are Exploiting a Critical LiteLLM Pre-Auth SQLi Flaw
Researchers have identified a critical pre‑authentication SQL injection flaw (CVE‑2026‑42208) in the open‑source LiteLLM gateway, which routes LLM API calls. The vulnerability lets attackers send a crafted Authorization header to read or modify the proxy’s database, exposing stored API keys,...

Treasury Missed Security Controls in Giving DOGE System Access, GAO Finds
The Government Accountability Office (GAO) released a report revealing that the Treasury Department granted a Department of Government Efficiency (DOGE) associate access to its three payment systems without adhering to required security controls. The associate, identified by GAO as matching...

The Founder of Scholly Sold His Scholarship App to Sallie Mae. He Says They Fired Him for Asking Why They...
Sallie Mae bought scholarship‑matching app Scholly in 2023, gaining access to its five million users. Founder Christopher Gray has filed a Delaware lawsuit and an SEC whistleblower complaint, alleging he was fired after warning the acquirer about selling users' personal...

Google and Mastercard Contribute Agentic Commerce Standards to FIDO Alliance
The FIDO Alliance announced two new technical working groups to create open standards for AI‑agent authentication and commerce. Google donated its Agent Payments Protocol (AP2) and Mastercard contributed its Verifiable Intent framework to the Payments Working Group. The Agentic Authentication...

NSA Chief During Snowden Affair Shares Regrets, Reflections 13 Years Later
Former NSA Deputy Director Chris Inglis reflects on the 2013 Snowden disclosures, emphasizing that investigations found no illegal abuse of authority but that the fallout still damaged public trust. He argues Snowden bypassed internal reporting channels, highlighting systemic contractor‑management flaws...

One Year After CVE-2025-31324: Lessons for ERP Security Leaders
One year after SAP disclosed CVE-2025-31324, the flaw continues to be exploited long after the vendor released a patch. Onapsis reports the vulnerability ranked among the three most frequently abused weaknesses of 2025, alongside Oracle E‑Business Suite and Microsoft SharePoint....

Federal CIO Cautious on Anthropic’s Mythos Despite Planned Rollout
Federal CIO Greg Barbaccia said the government will proceed with a measured rollout of Anthropic’s Mythos AI model, noting its promise for bolstering cyber defenses while emphasizing lingering uncertainties about real‑world performance. He has only seen lab‑based evaluations and no...
Elsight’s Halo, Its BLOS (Beyond Line-of-Sight) Connectivity Platform, Is Now Certified on the U.S. DCMA Blue UAS List, Enabling Faster...
Elsight's Halo beyond‑line‑of‑sight (BLOS) connectivity platform has been certified on the U.S. Defense Contract Management Agency (DCMA) Blue UAS List, confirming it meets the department’s rigorous supply‑chain and cybersecurity standards. The certification lets U.S. military units procure Halo directly through...

US Bill Would Require Warrants for Digital Surveillance, Biometric Searches
The House introduced the Surveillance Accountability Act (H.R. 8470), a bipartisan bill that would require a warrant for virtually all government searches of digital and biometric data, including facial recognition, license‑plate readers, cloud storage, and data‑broker records. The legislation amends...
Vidar Rises to Top of Chaotic Infostealer Market
Credential‑stealing malware Vidar has surged to become the most used infostealer on the Russian Market, overtaking Lumma and Rhadamanthys after law‑enforcement takedowns in 2025. Intrinsec’s report attributes the rise to a major upgrade and expanded distribution network, including phishing, fake...

Cyber Insurance Data Gives CISOs New Ammo for Budget Talks
Resilience’s new cyber‑insurance analysis translates technical threats into monetary loss, giving CISOs a data‑driven script for board budget discussions. The study of manufacturing claims from March 2021‑February 2026 shows ransomware responsible for 90% of incurred loss while representing only 12% of claims....
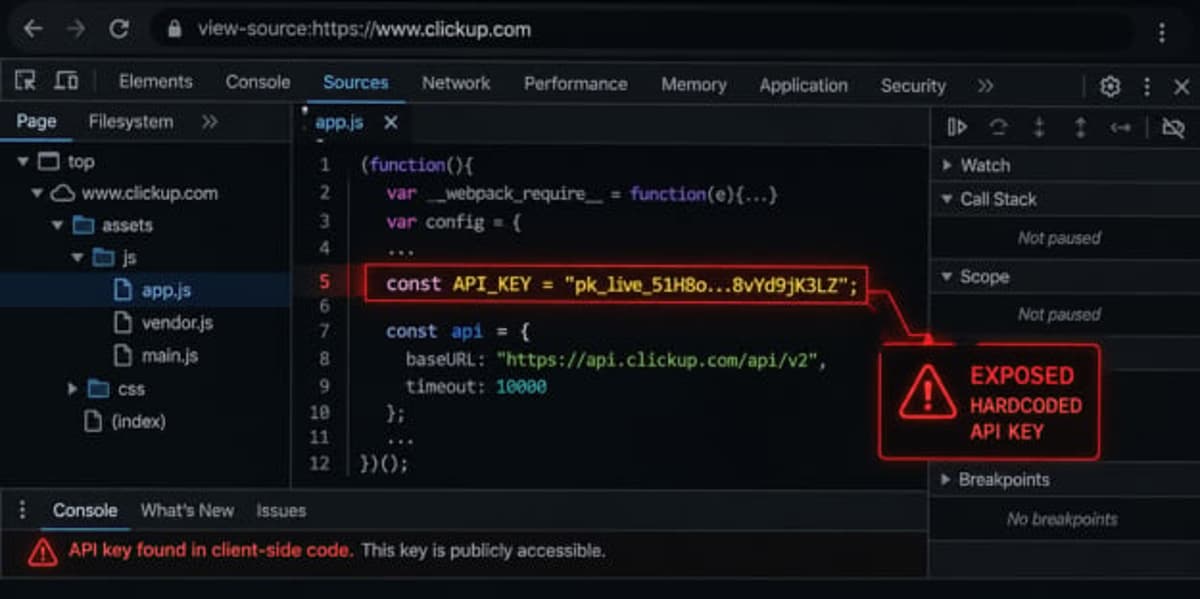
ClickUp Data Leak Exposes Enterprise Emails for Over a Year
A hardcoded API key embedded in ClickUp’s public website allowed anyone to retrieve 959 corporate and government email addresses and 3,165 internal feature flags without authentication. The flaw, first reported in early 2025, remained active through April 2026, exposing sensitive...

Paragon Is Not Collaborating with Italian Authorities Probing Spyware Attacks, Report Says
Paragon Solutions, the Israeli‑American maker of Graphite spyware, has failed to answer a formal information request from Italian prosecutors investigating a 2024 hacking campaign that targeted journalists and activists. The company previously promised to assist the probe but instead cancelled...

Brazilian LofyGang Resurfaces After Three Years With Minecraft LofyStealer Campaign
Brazilian cybercrime group LofyGang has resurfaced after a three‑year hiatus, launching a new Minecraft‑targeted campaign that distributes the LofyStealer (aka GrabBot) malware. The stealer is disguised as a popular Minecraft hack called "Slinky" and uses the game’s official icon to...

Cyber Command, NSA Chief Warns Foreign Adversaries Likely to Target Midterms
U.S. Cyber Command head Gen. Joshua Rudd told the Senate that foreign adversaries are likely to attempt interference in the 2024 midterm elections. He noted uncertainty about whether the Election Security Group, the joint task force used since 2018, has...

Police Arrest 10 Suspected Members of Black Axe Cybercrime Gang
Swiss police, in coordination with Europol, arrested ten suspected members of the Black Axe criminal network on 28 April 2026. The raids across multiple cantons captured the group’s Southern Europe regional head and several individuals of Nigerian origin accused of romance scams,...

IAM’s Adaptation for AI Agents Drives M&A Deals for Silverfort, iC Consult
Silverfort, a digital identity security firm, has acquired AI‑native provider Fabrix Security to embed Fabrix’s real‑time AI decision engine into its Runtime Access Protection platform. The combined solution aims to protect human, non‑human and agentic identities at runtime, addressing the...

US FMCSA Tightens ID Checks for Driver Database, Taps Idemia
The Federal Motor Carrier Safety Administration (FMCSA) announced stricter identity‑verification requirements for users of its Drug and Alcohol Clearinghouse, a database that flags commercial drivers barred for substance‑related offenses. The new rules target medical review officers, substance‑abuse professionals, third‑party administrators...

How Identity, Geopolitics and Data Integrity Define Cyber Resilience
The article argues that cyber resilience now hinges on three intertwined forces—identity, geopolitics, and data integrity. Identity weaknesses trigger roughly 90% of breaches, while fragmented global regulations leave 69% of firms scrambling. Data poisoning and unmanaged "shadow AI" expose 63%...

Turning Secret Detection Into Measurable Risk Reduction
HashiCorp’s Vault Radar extends secret detection beyond visibility by adding correlation, automated workflow integration, and reporting. The platform matches discovered secrets with Vault or AWS Secrets Manager, enabling teams to see which exposures are already managed and which represent governance...